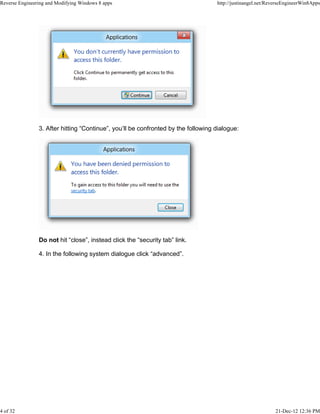
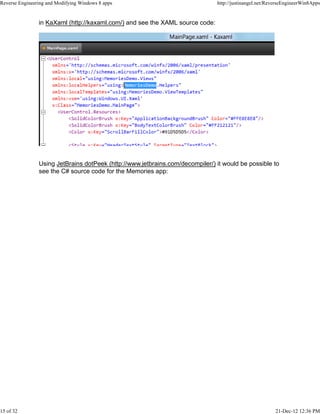
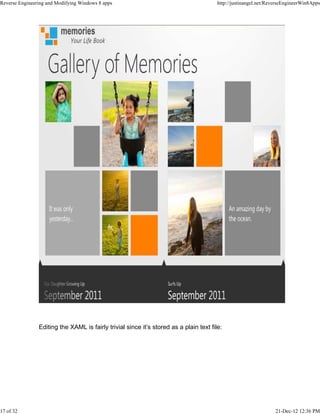
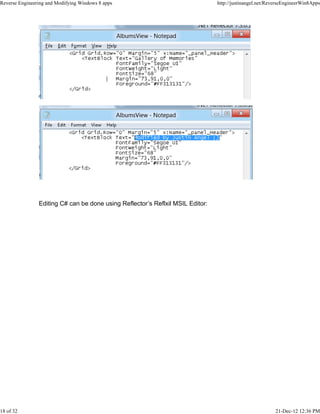
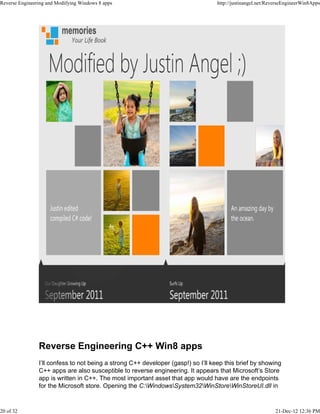
The document discusses security vulnerabilities in Windows 8 apps that allow for reverse engineering and modification. It describes how apps' source code is stored openly on users' machines, allowing easy access and editing of HTML, JavaScript, CSS, XAML, and .NET code. This could enable new viruses, app piracy through modification, and extraction of intellectual property. The author provides steps to access and modify sample apps as proofs of concept and suggests mitigation strategies for Microsoft.