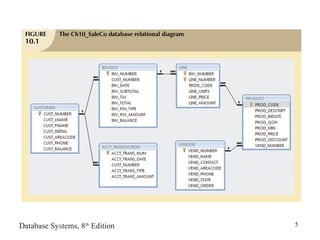
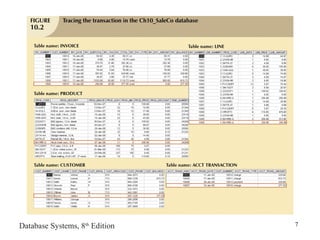
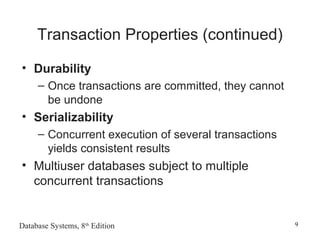
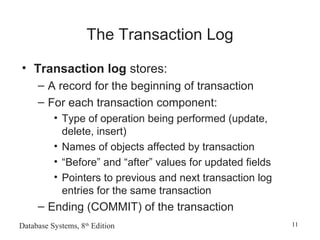
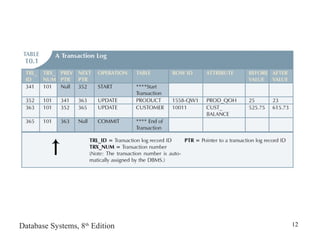
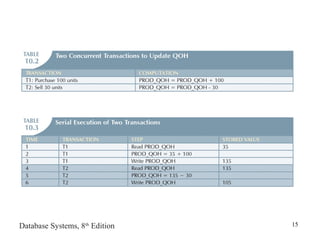
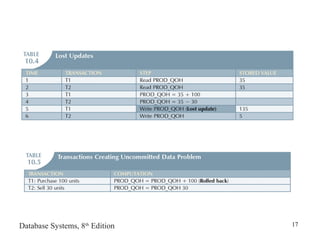
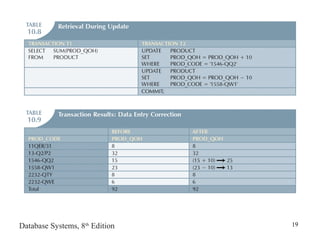
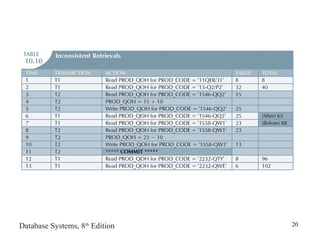
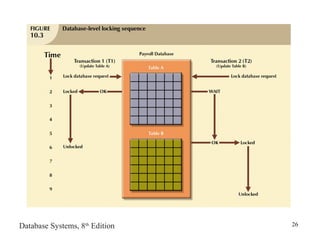
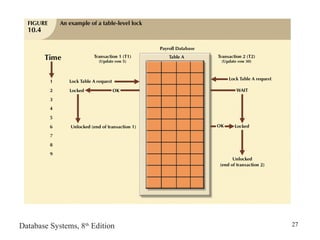
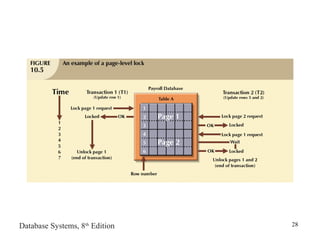
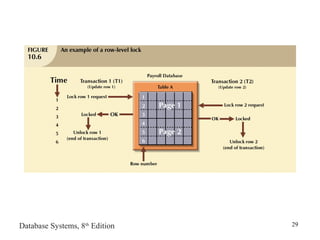
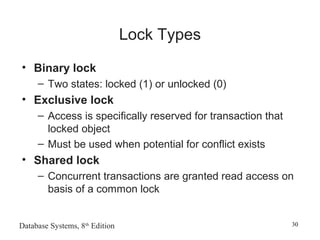
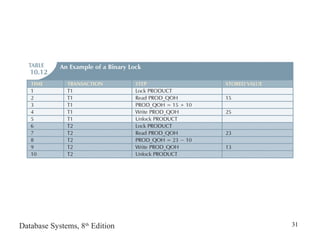
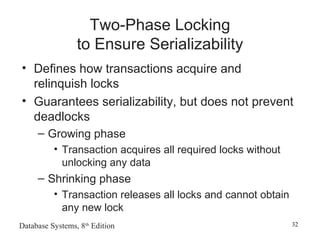
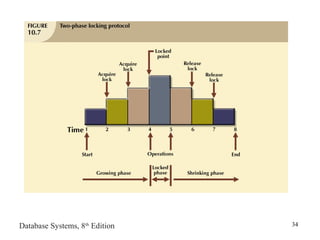
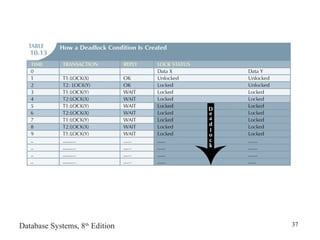
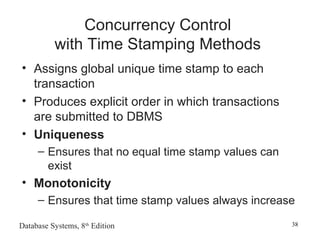
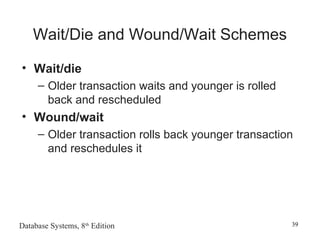
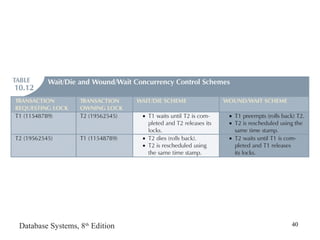
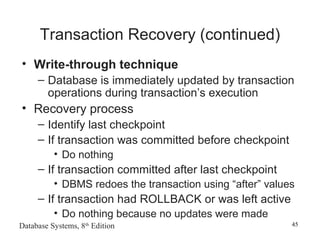
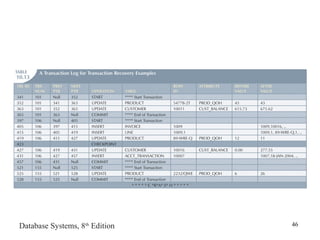
The document discusses transaction management and concurrency control in database systems. It covers topics such as transactions and their properties, concurrency control methods like locking, time stamping and optimistic control, and database recovery management. The goal of these techniques is to coordinate simultaneous transaction execution while maintaining data consistency and integrity in multi-user database environments.