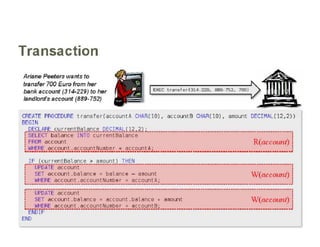
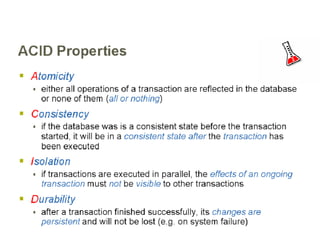
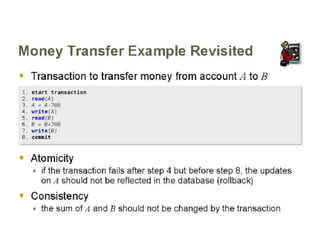
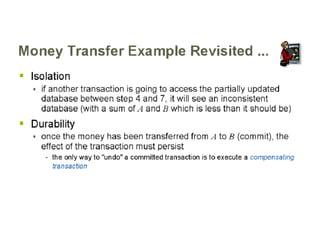
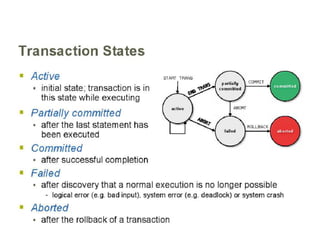
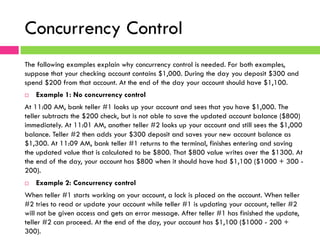
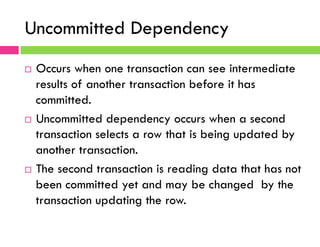
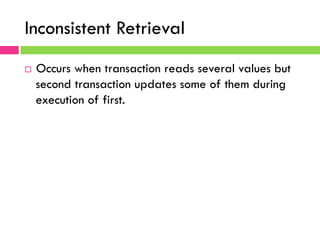
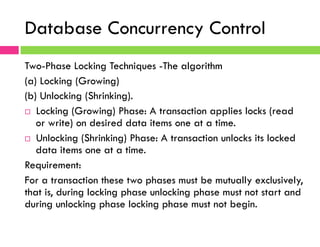
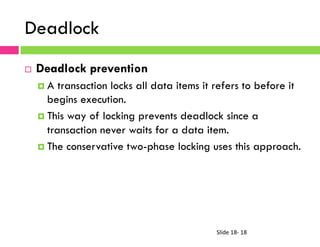
This document discusses database transaction management and concurrency control. It describes the properties of transactions, interference problems that can arise from simultaneous database access like lost updates, and tools used by DBMS to prevent these issues like locks and two-phase locking. Recovery tools are also covered, including transaction logs, checkpoints, and database backups that allow recovering data after failures.