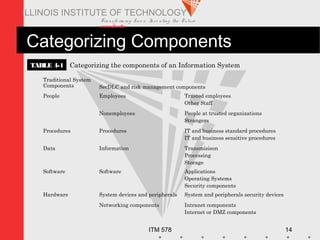
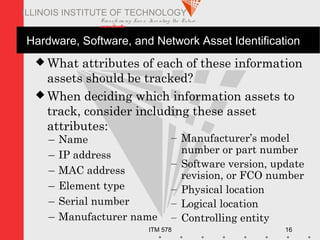
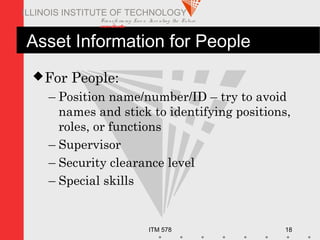
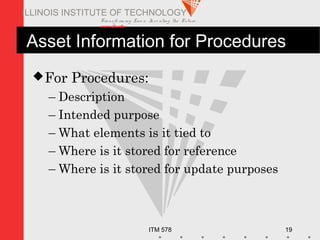
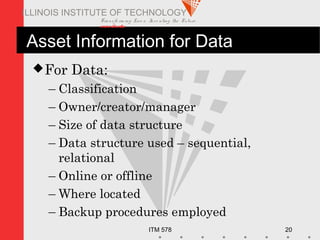
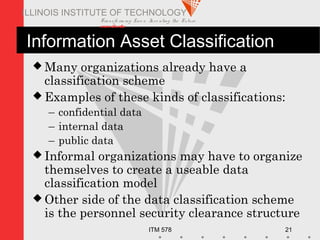
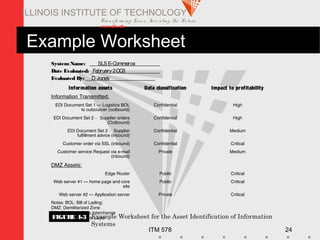
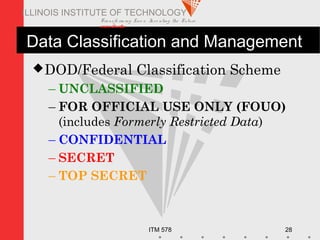
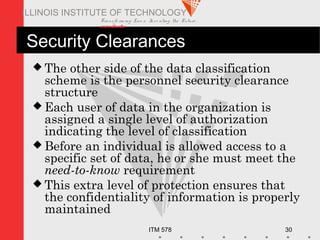
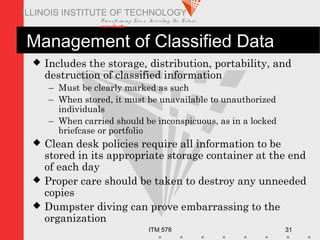
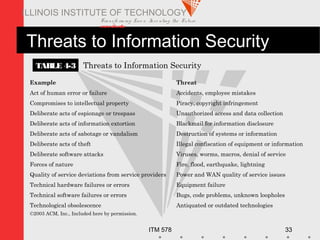
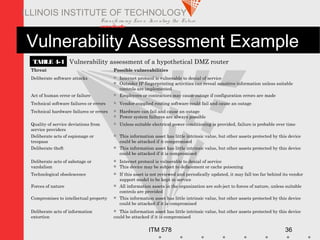
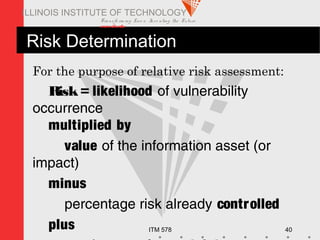
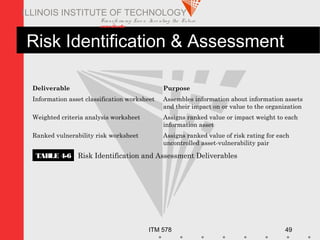
This document provides an overview of risk management concepts and the risk management process as it relates to information security. It discusses defining risk management and its role in the secure software development lifecycle. It also describes identifying risks through asset identification, classification, and valuation. Additionally, it covers identifying threats, assessing risks based on likelihood and impact, and documenting the risk identification and assessment process. The overall purpose is to teach students the fundamentals of risk management for information security.