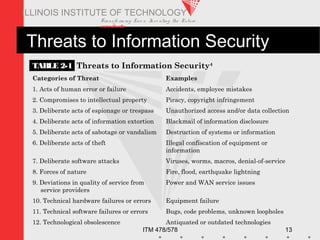
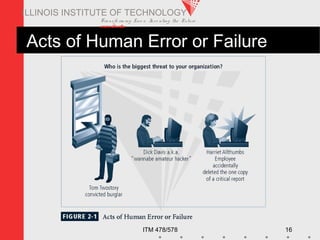
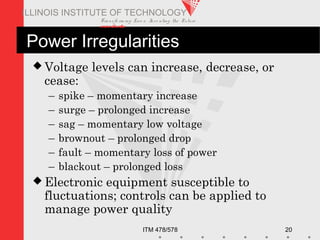
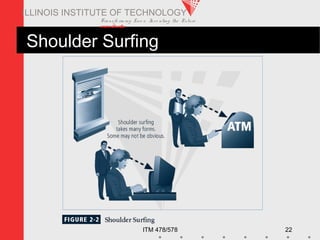
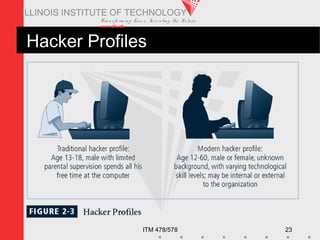
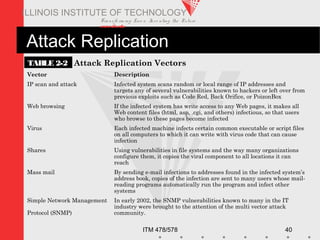
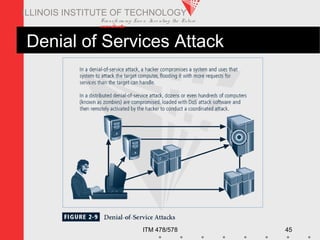
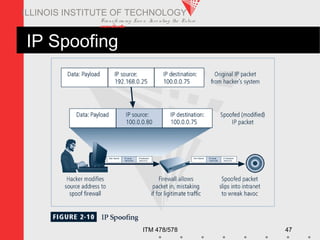
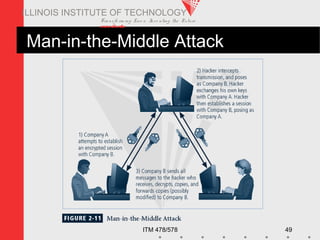
This document discusses the need for information security. It covers threats to information security like human error, hackers, malware attacks, and natural disasters. The document is from an Illinois Institute of Technology course on information security and outlines objectives, threats, and examples of common threats like software attacks, intellectual property theft, and power outages. It aims to explain the business need for security and describe common information security threats.