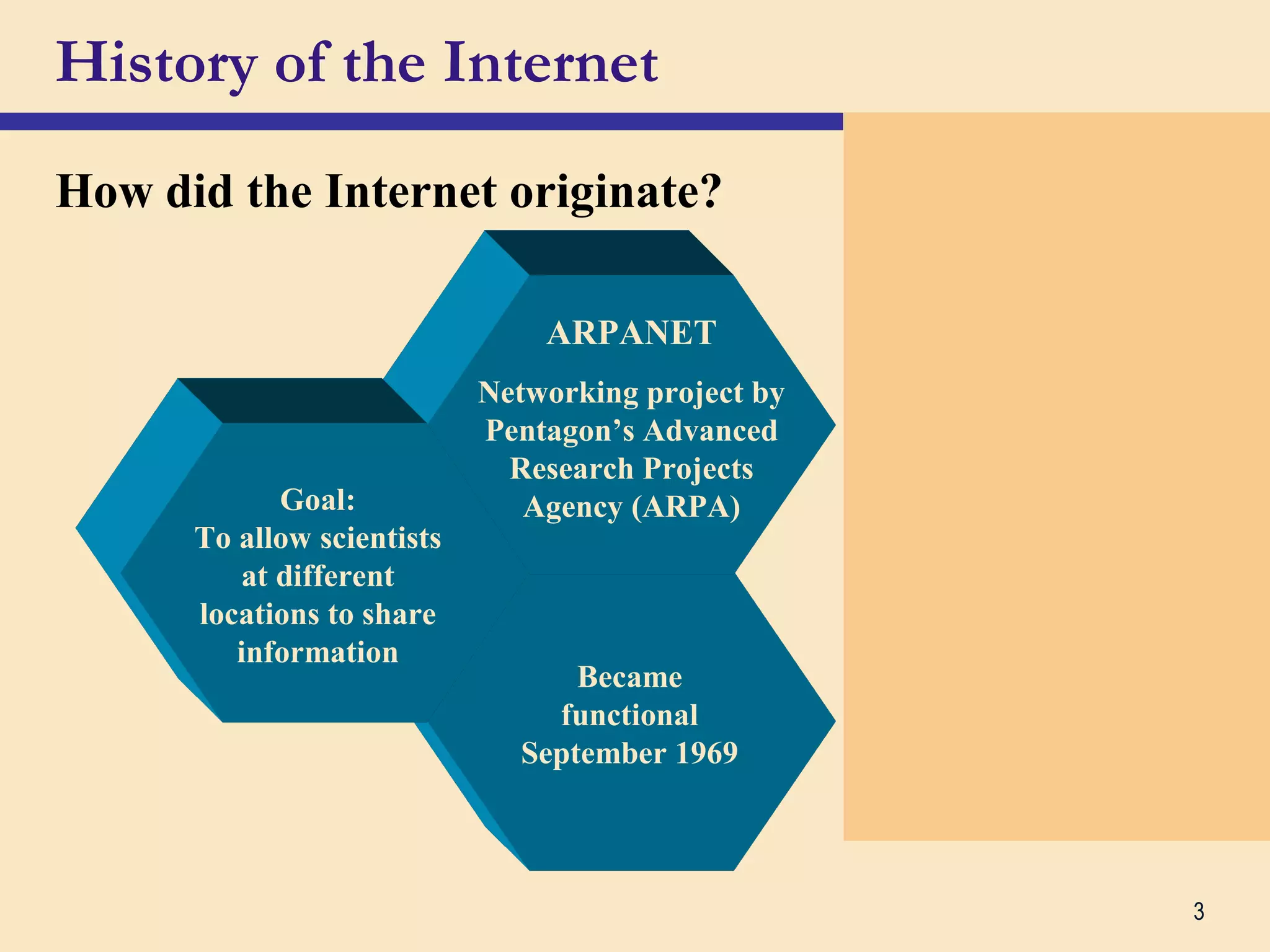
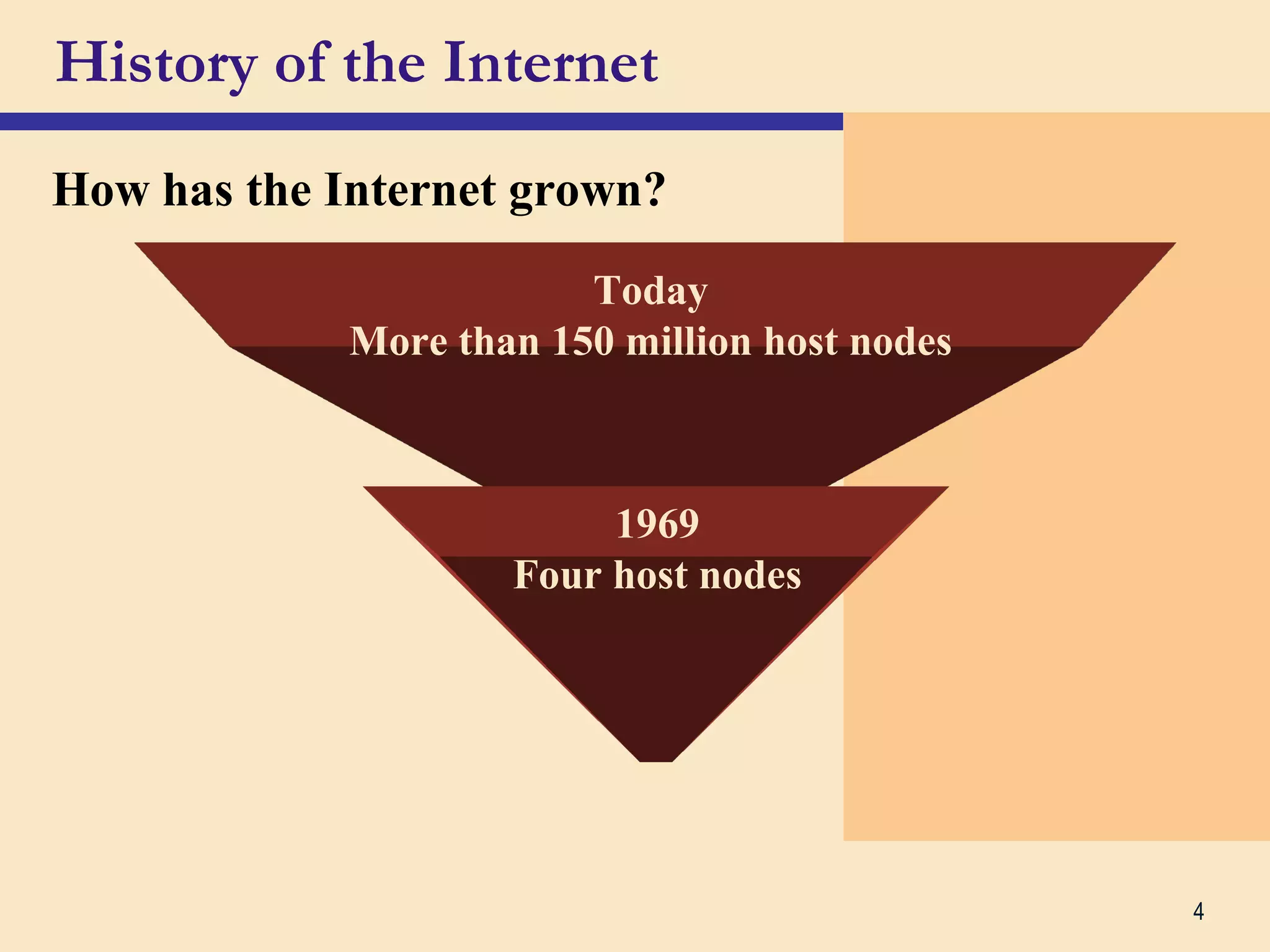
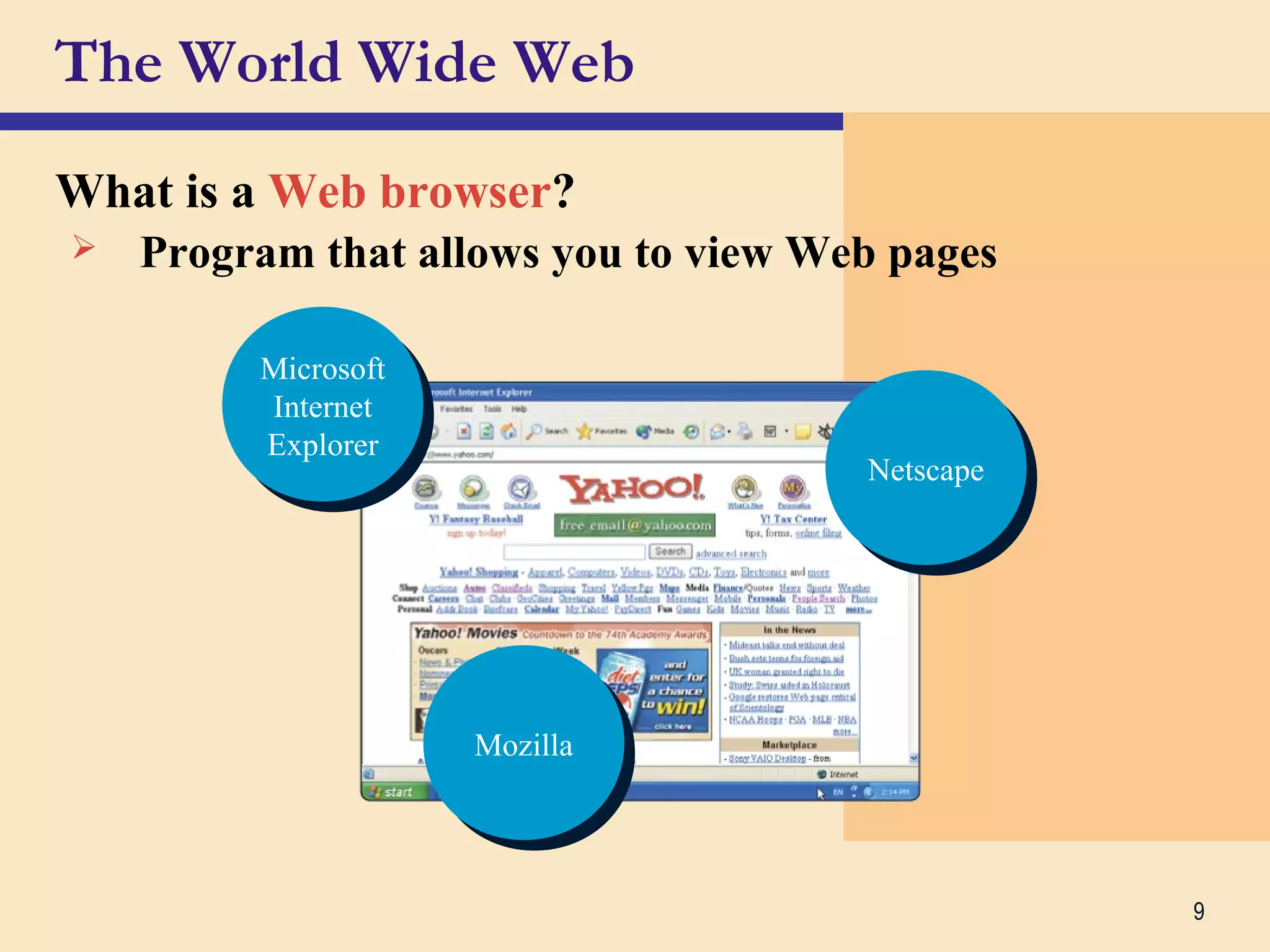
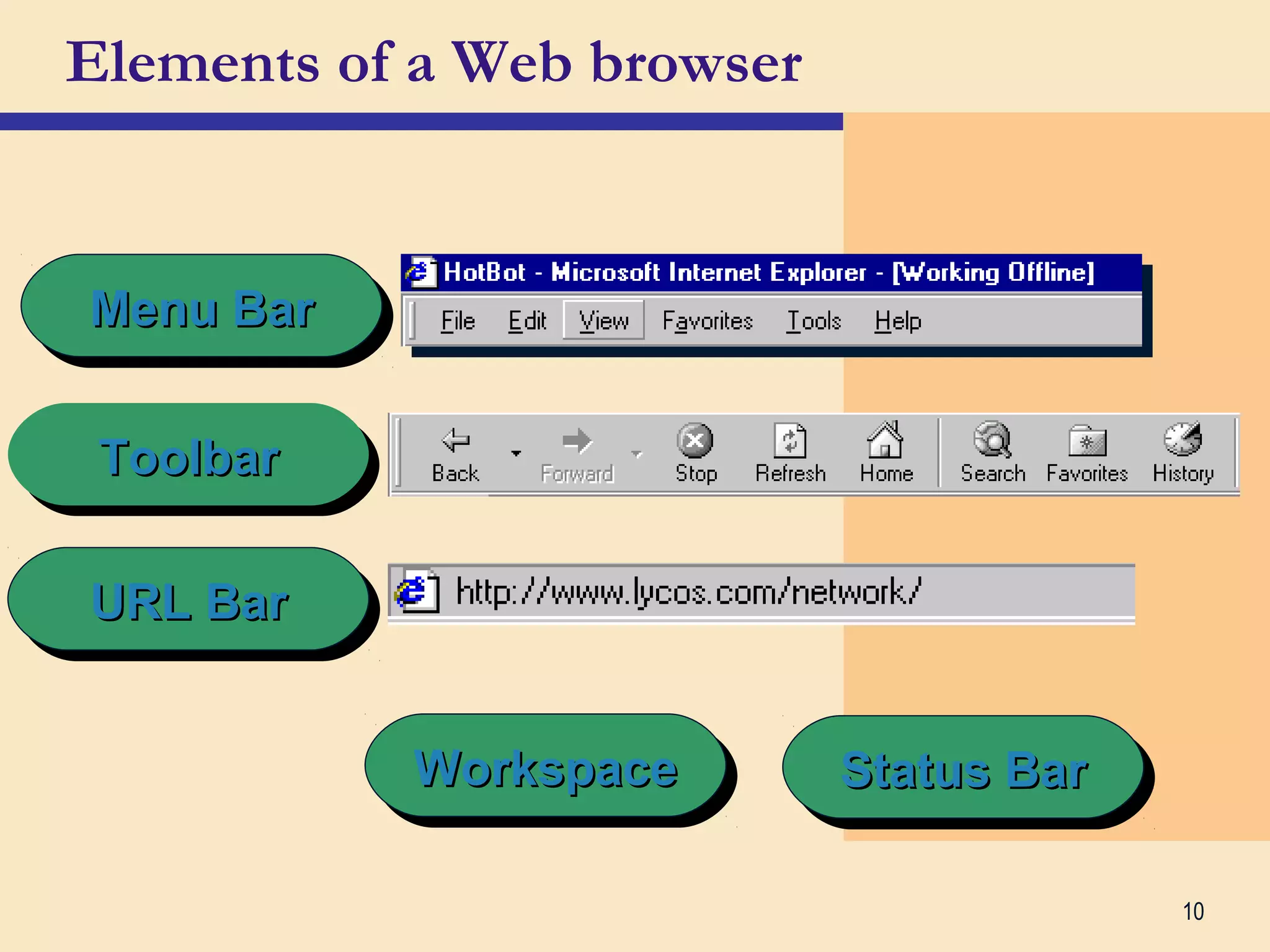
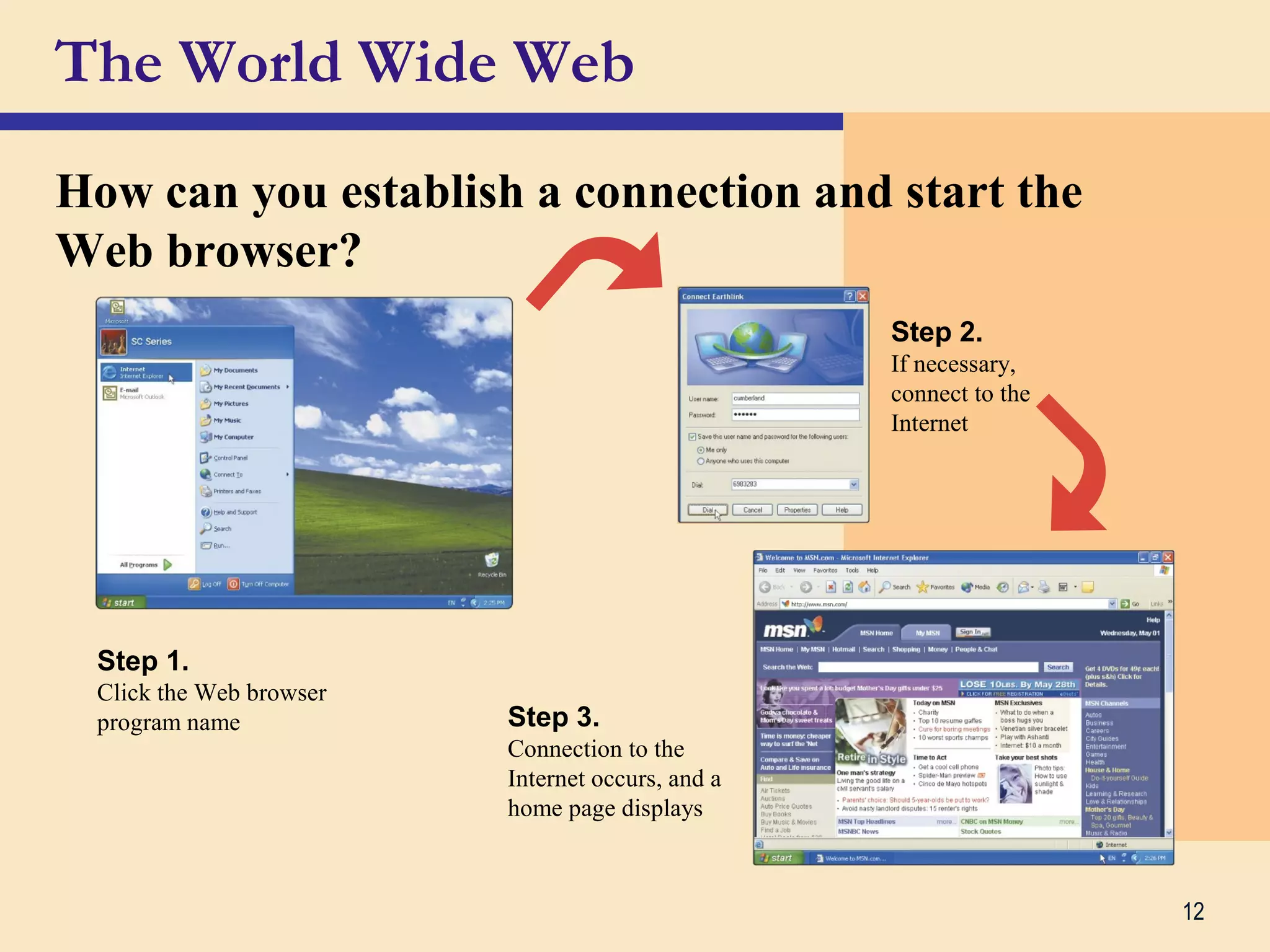
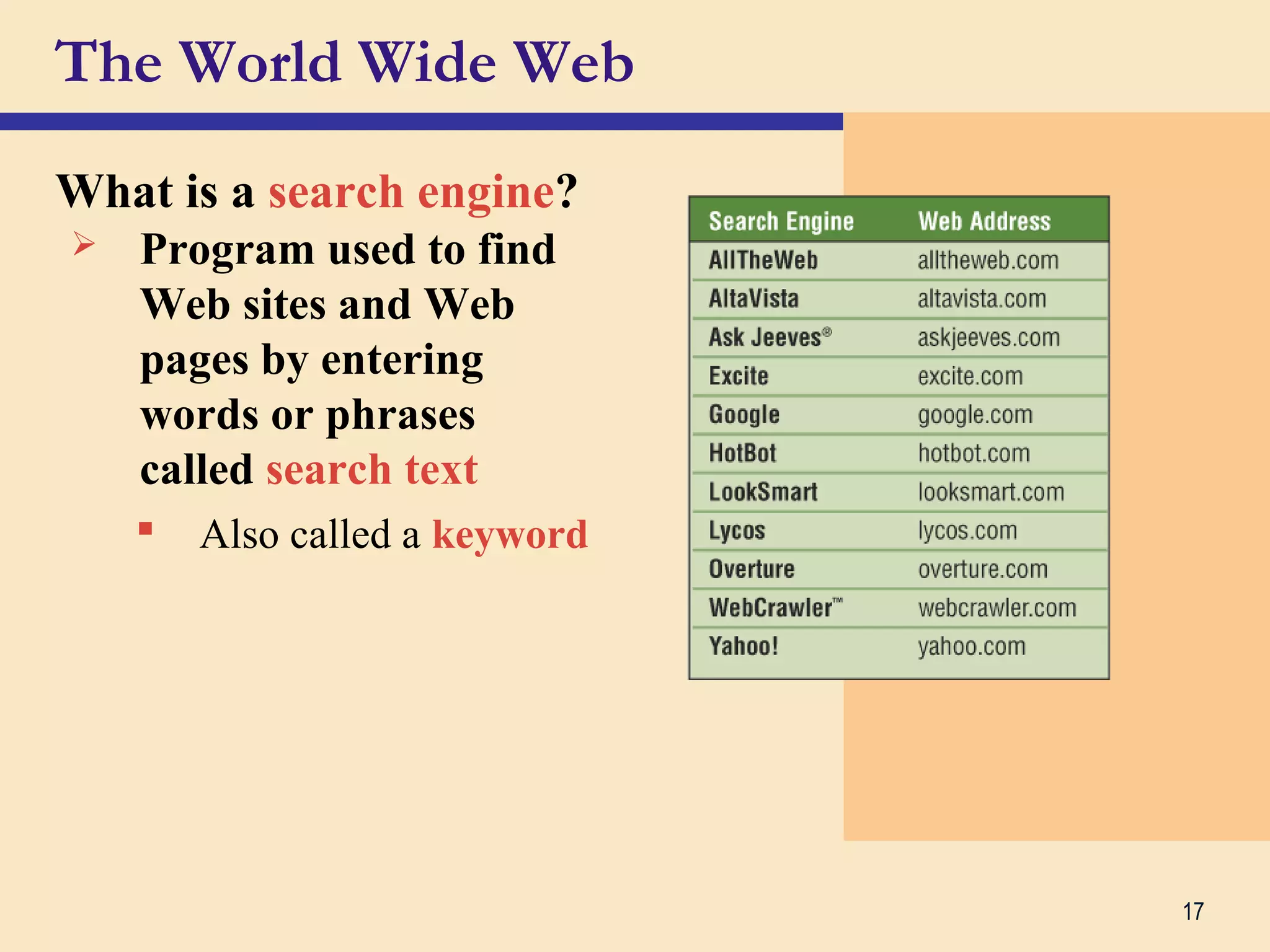
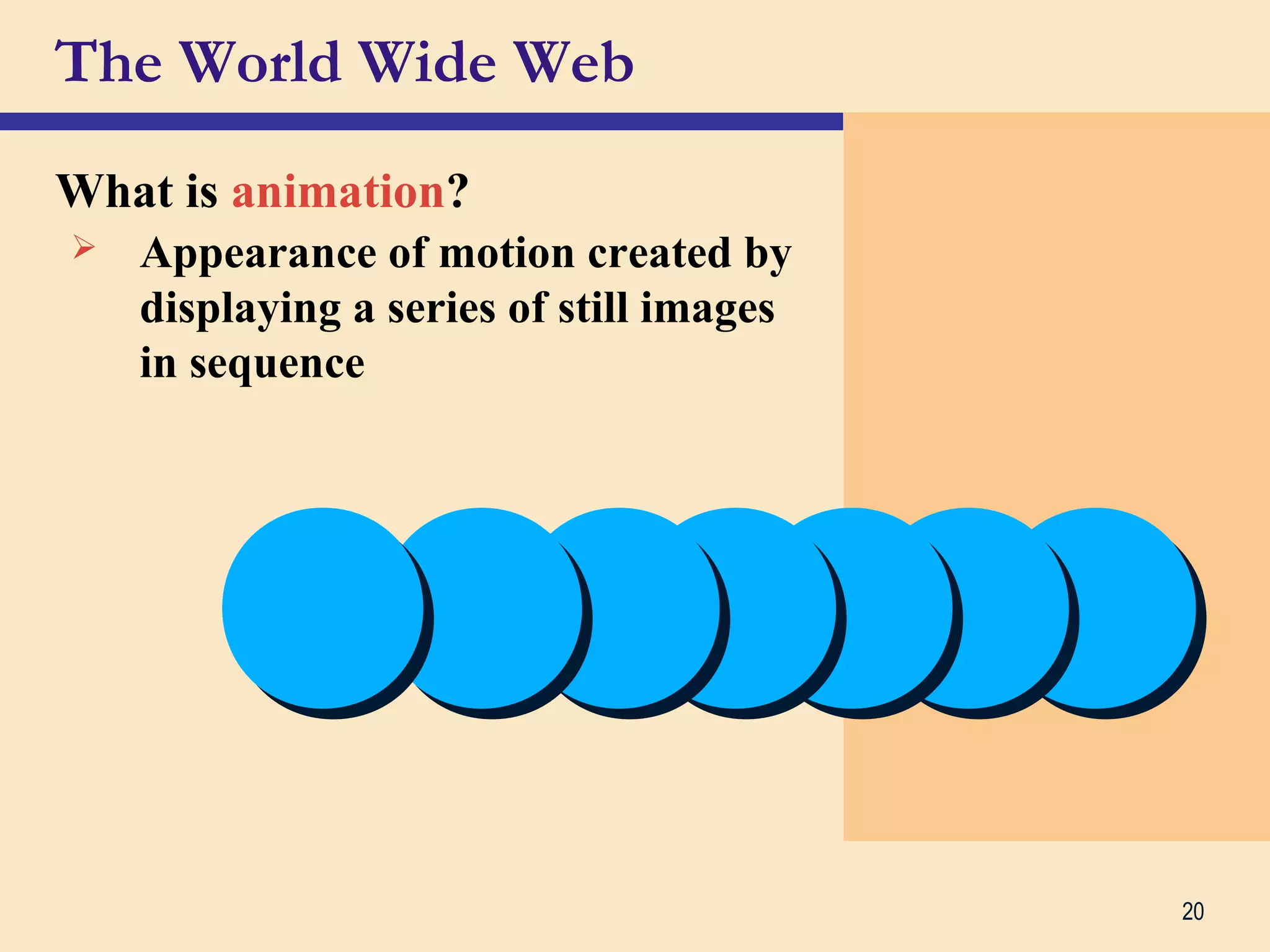
The document provides a comprehensive overview of the internet and World Wide Web, covering their history, functionality, and various components. It explains how users connect to the internet, the role of web browsers and service providers, and introduces key concepts such as URLs, hyperlinks, multimedia, and e-commerce. Additionally, it profiles Dr. Kamal Gulati, outlining his academic qualifications and contributions to the field of computer science and information technology.

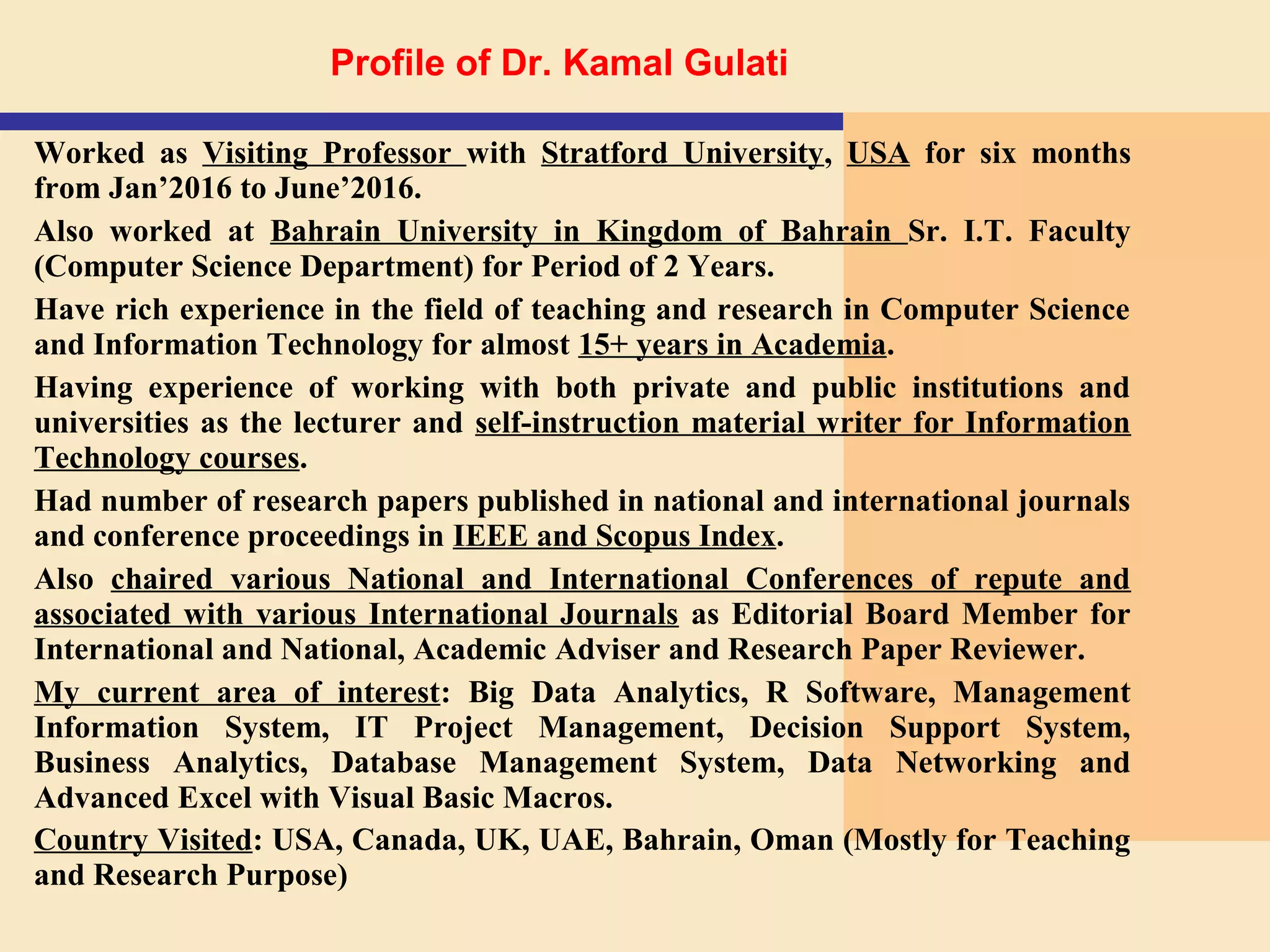
![Dr. Kamal Gulati
Associate Professor |
University Quality Support Head |
Mentoring Programme Coordinator
[Ph. D., M.Sc. (Computer Science), M.C.A., M.B.A]
Professional Certifications:
Certified Microsoft Innovative Educator
Data Science 101 Certification from Big Data University
R Language 101 Certification from Big Data University
SQL Certification from SOLOLEARN.com
Certified IBM Big Data 101 from Big Data University
R Program & Python Certified from DataCamp
Wiley Certified Big Data Analyst [WCBDA]
Certification on DBMS from IIT Mumbai
Certified Cisco Certified Network Associate [CCNA]
Certified Microsoft Certified Professional [MCP]
Certified Brainbench in Computer Fundamentals, Microsoft Access, MySQL 5.7 Administration &
Microsoft Project](https://image.slidesharecdn.com/theinternetandworldwideweb-171208050457/75/The-Internet-WWW-Basic-Understanding-34-2048.jpg)