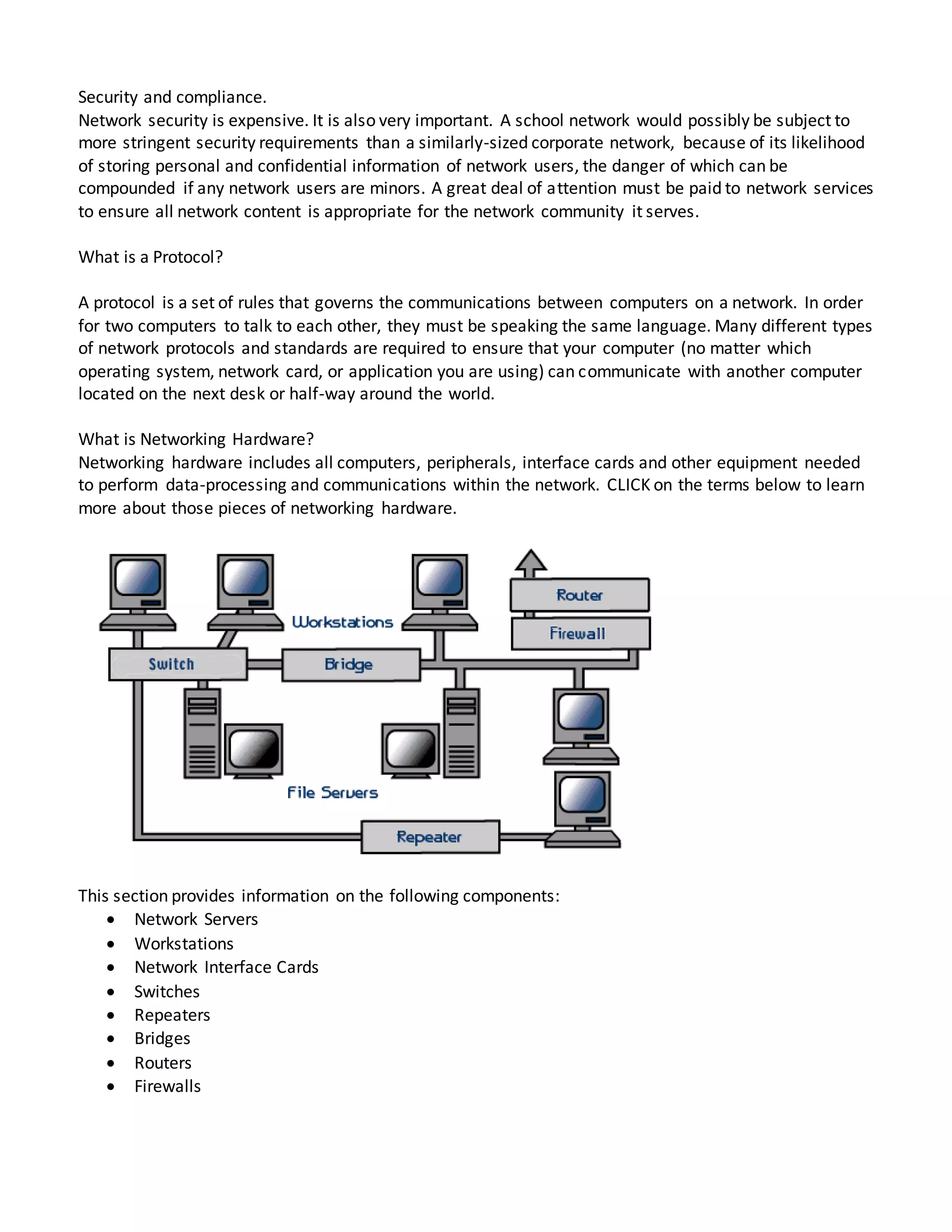
A network connects computers to share resources and exchange files. Common types of networks include local area networks (LANs), which connect computers in a small area like a building, and wide area networks (WANs), which connect larger geographic areas like countries. LANs use servers to provide services to connected workstations, while WANs can connect LANs across long distances using technologies like cables or satellites. Installing a school network provides benefits like centralized user access control, information sharing, internet access, and flexible access for students, but also has disadvantages such as high installation costs and needing administrative support.