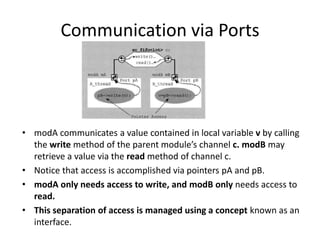
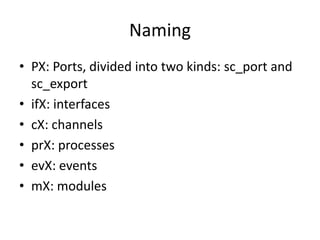
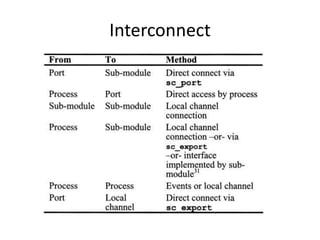
1. Ports in SystemC allow modules to communicate through channels inserted between them. A port is a pointer to an external channel.
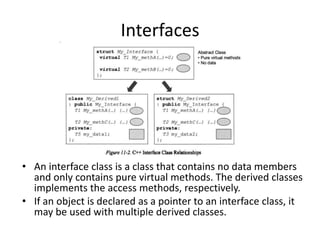
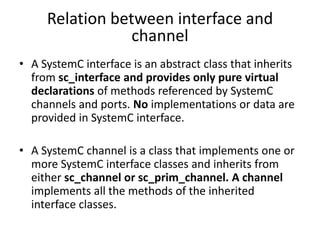
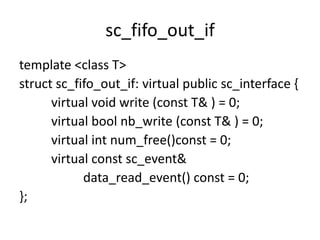
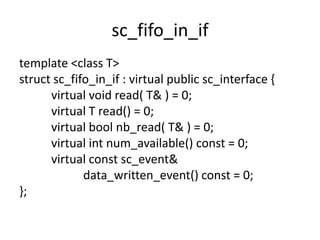
2. Interfaces define the methods that ports and channels use to communicate without specifying data or implementations. Channels implement the interface methods.
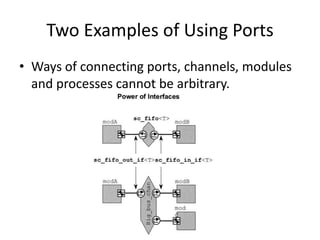
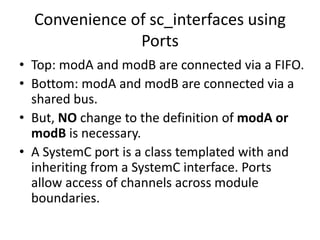
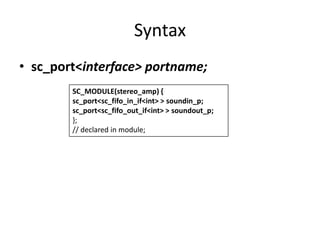
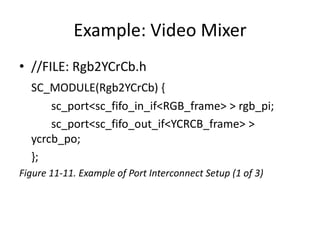
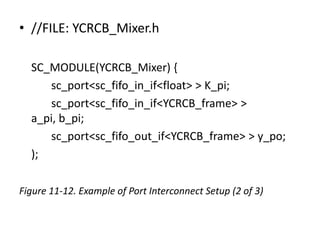
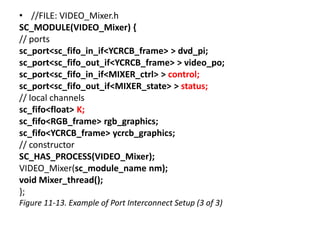
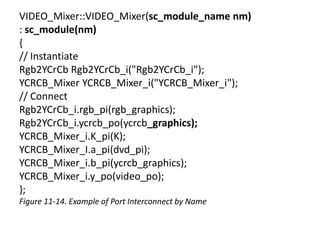
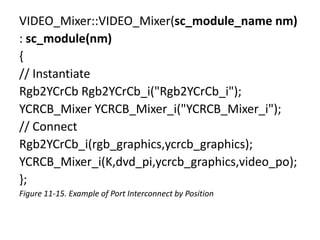
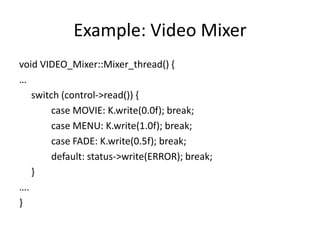
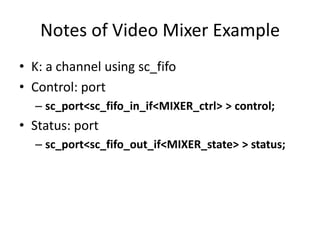
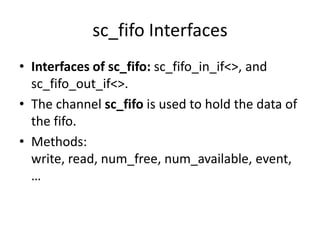
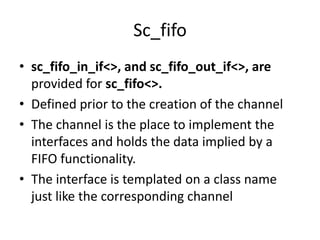
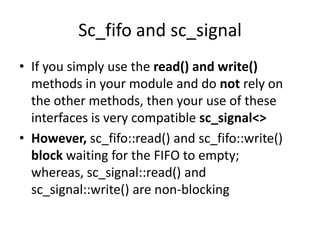
3. In the video mixer example, modules are connected through ports and channels with interfaces like sc_fifo_in_if and sc_fifo_out_if. Processes can access ports and call channel methods to communicate between modules.

![sc_port array
• Provide multi-port or port array of liked
defined.
• Syntax:
– sc_port <interface[ ,N]> portname;
– // N=0..MAX Default N=1](https://image.slidesharecdn.com/ports2010-131223114824-phpapp01/85/SystemC-Ports-38-320.jpg)


![Memory Model
//FILE: mem_arch.h
#include "CPU_if.h"
struct mem: public sc_channel, CPU_if {
// Constructors & destructor
explicit mem(sc_module_name nm,
unsigned long ba, unsigned sz)
: sc_channel(nm), m_base(ba), m_size(sz)
{ m_mem = new long[m_size]; }
~mem() { delete [] m_mem; }
// Interface implementations
virtual void write(unsigned long addr, long data) {
if (m_start <= addr && addr < m_base+m_size) {
m_mem[addr–m_base] = data;
}
}
virtual long read(unsigned long addr) {
if (m_start <= addr && addr < m_base+m_size) {
return m_mem[addr–m_base];
} else {
cout <<
"ERROR:"<<name()<<"@"<<sc_time_stamp
()
<< ": Illegal address: " << addr << endl;
sc_stop(); return 0;
}
}
private:
unsigned long m_base;
unsigned m_size;
long m_mem[];
mem(const mem&); // Disable
};](https://image.slidesharecdn.com/ports2010-131223114824-phpapp01/85/SystemC-Ports-53-320.jpg)