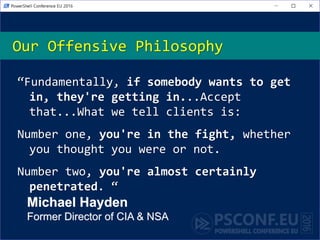
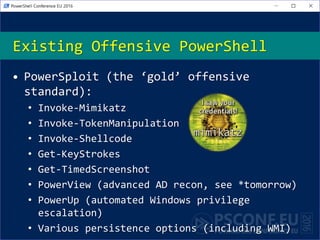
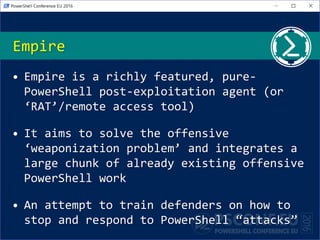
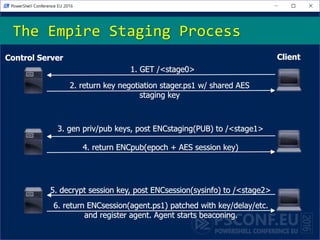
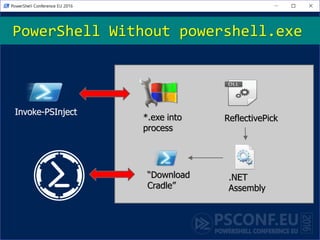
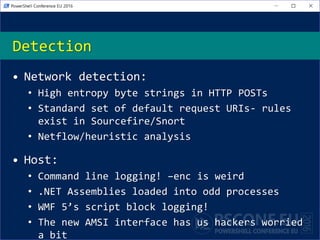
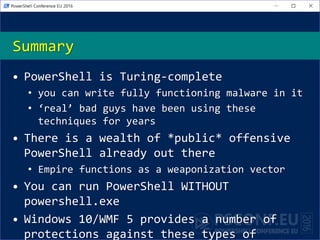
The document discusses the development and use of Empire, a PowerShell-based post-exploitation tool designed to simulate advanced threats and aid in defensive measures against them. It emphasizes the necessity of acknowledging the reality of cybersecurity threats and the existence of sophisticated offensive PowerShell techniques for both attackers and defenders. The presentation outlines the architecture, modules, and detection methods associated with Empire, highlighting its functionalities and the challenges it presents to network defense strategies.
![• Will Schroeder (@harmj0y)
• http://blog.harmj0y.net | will [at]
harmj0y.net
• Security researcher and red teamer for
Veris Group‘s Adaptive Threat Division
• Offensive open-source developer:
• Veil-Evasion, Empire, PowerSploit
• Recent Microsoft CDM/PowerShell MVP
About_Author](https://image.slidesharecdn.com/psconfeuempire-160422094830/85/PSConfEU-Building-an-Empire-with-PowerShell-13-320.jpg)