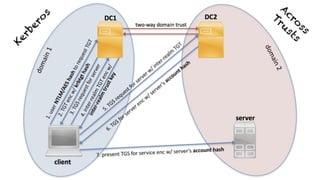
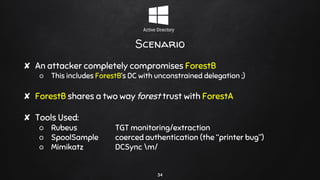
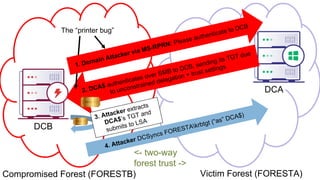
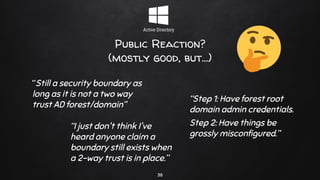
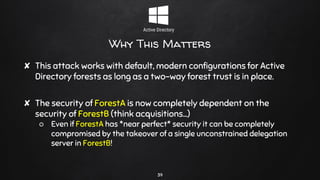
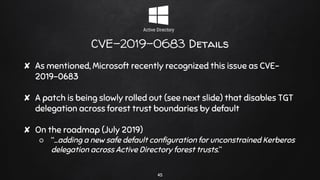
1. The document discusses breaking trusts between Active Directory forests by leveraging compromised unconstrained delegation and the "printer bug" to coerce authentication across forest boundaries.
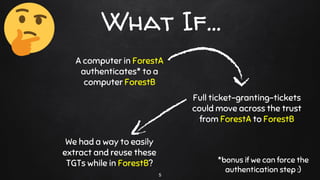
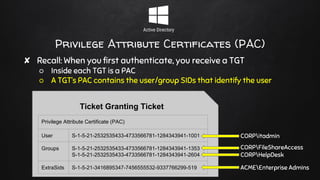
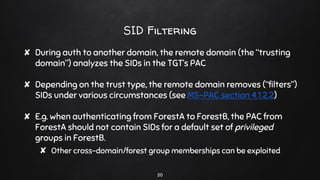
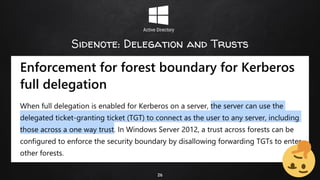
2. It explains how a compromised server with unconstrained delegation in one forest can be used to extract ticket granting tickets (TGTs) that can then be reused to access resources in a separate, trusting forest.
3. The "printer bug" allows remotely forcing authentication and is used to extract TGTs from the separate forest to circumvent typical cross-forest security restrictions. This bypasses the assumption that forests provide a security boundary when two-way trusts exist between them.












![CVE-2019-0683 Timeline
46
✘ March 12, 2019
○ Kerberos full delegation block is backported to Server 2008[R2]
✘ May 14, 2019
○ A new trust flag will be introduced in case you need full delegation
across trusts
○ "EnableTGTDelegation” set to “no” for all new trusts
✘ July 9, 2019
○ Start of enforcement of new trust flag
○ "EnableTGTDelegation” ignored from this point forward](https://image.slidesharecdn.com/notasecurityboundary-190321093533/85/Not-a-Security-Boundary-46-320.jpg)
![thanks!
Any questions?
[will | lee]@specterops.io
@harmj0y | @tifkin_
47](https://image.slidesharecdn.com/notasecurityboundary-190321093533/85/Not-a-Security-Boundary-47-320.jpg)
