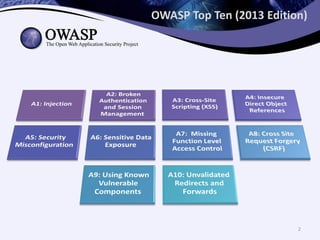
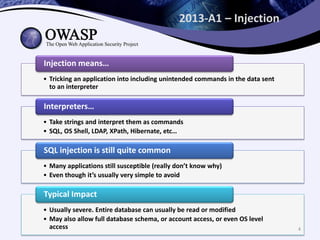
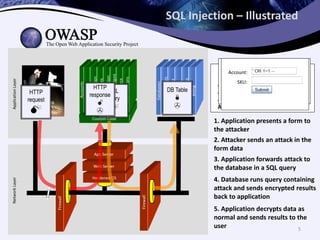
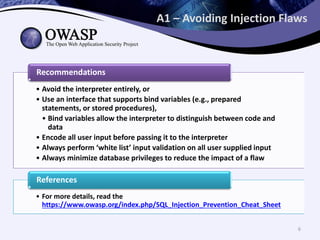
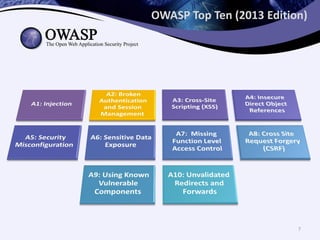
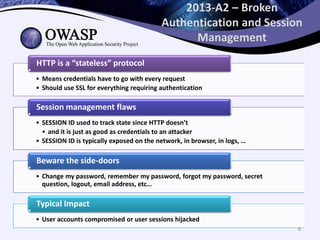
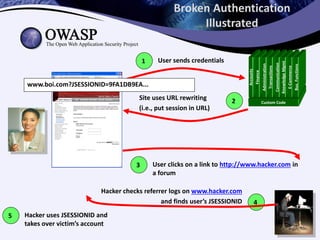
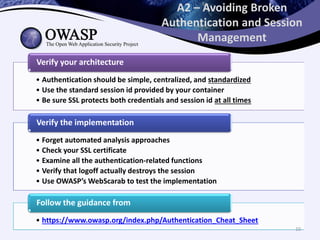
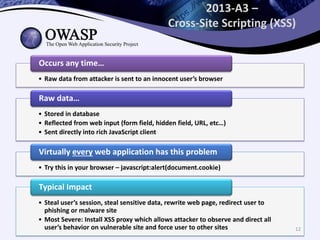
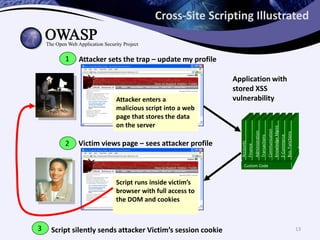
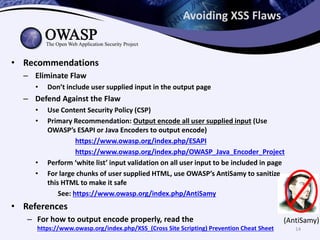
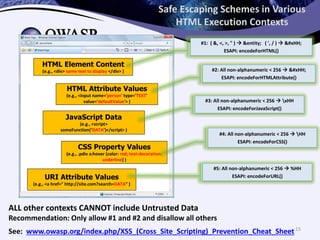
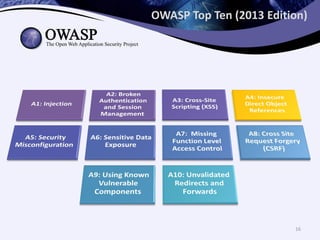
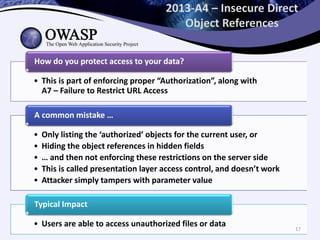
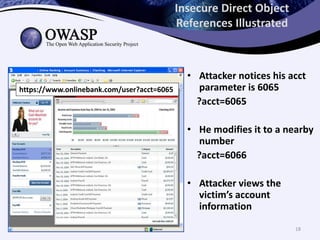
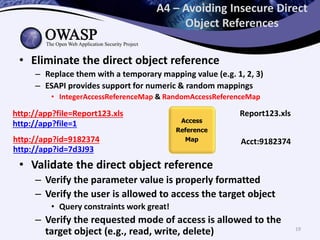
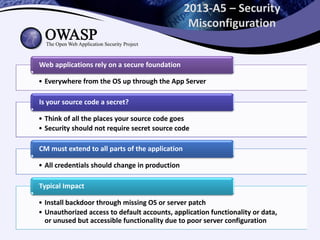
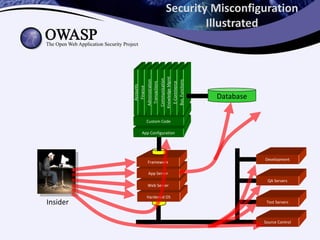
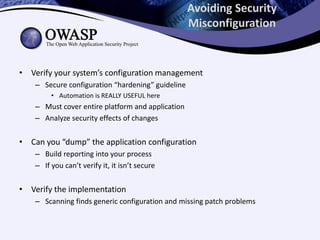
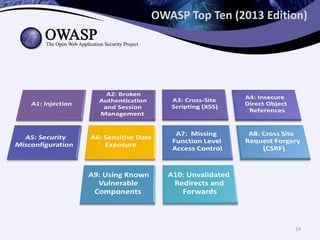
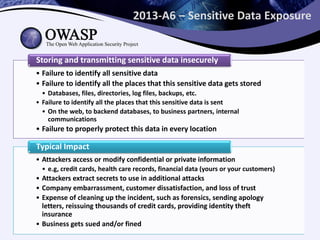
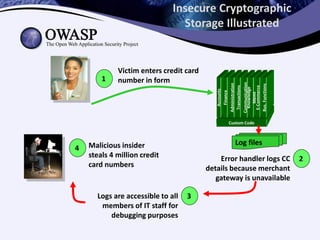
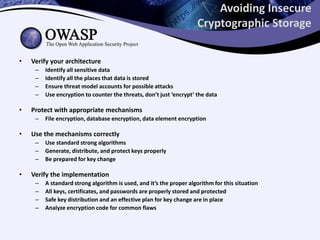
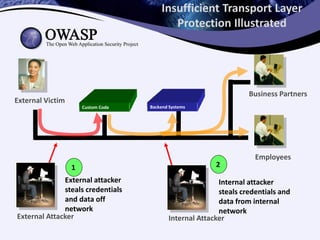
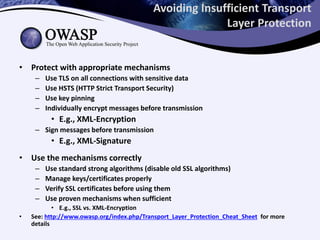
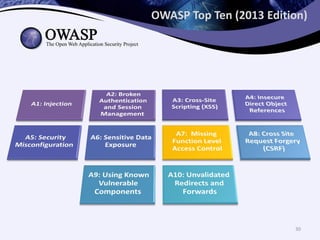
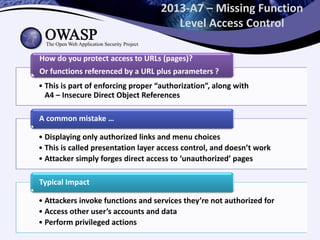
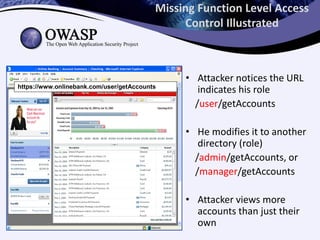
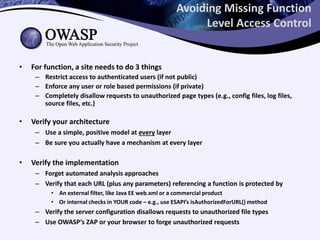
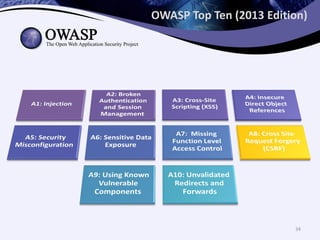
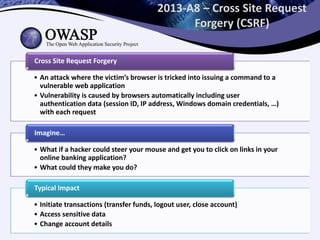
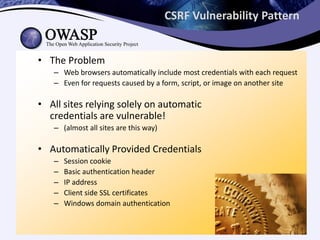
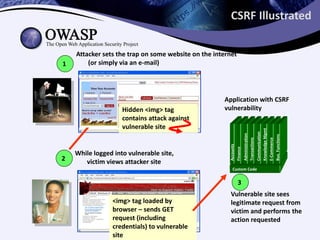
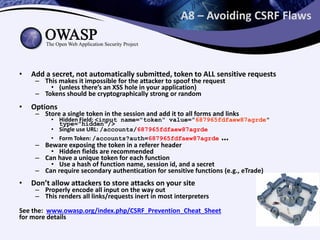
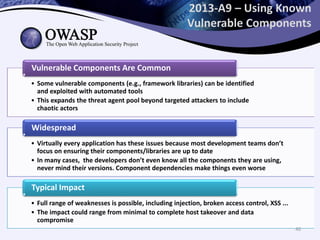
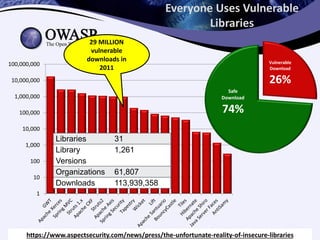
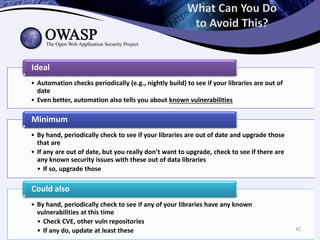
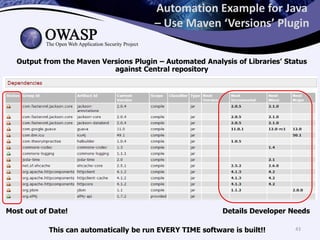
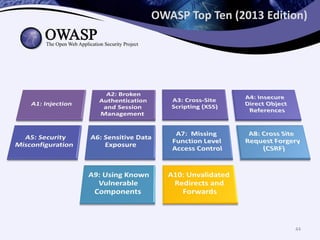
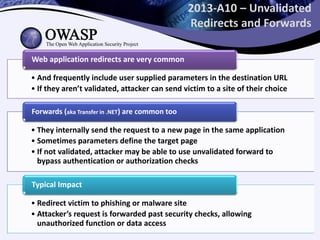
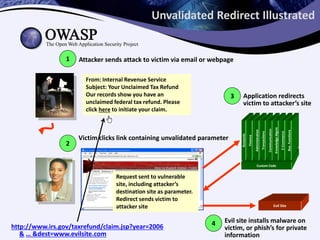
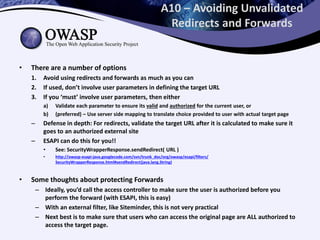
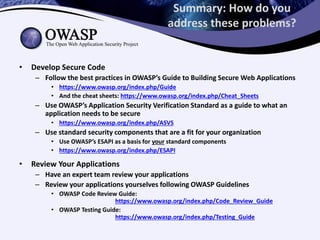
The 2013 OWASP Top Ten document outlines the most critical web application security risks, including issues like injection flaws, broken authentication, and cross-site scripting. It details the vulnerabilities, typical attack patterns, and provides recommendations for avoiding these security risks. The document emphasizes the importance of secure coding practices, proper session management, and regular updates to components to mitigate potential threats.