Embed presentation
Download to read offline


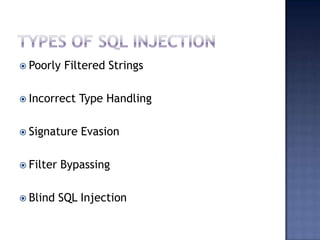
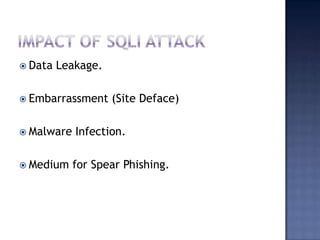





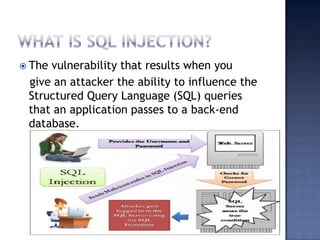
Ashish Gharti and Bijay Limbu Senihang are founders of Nep Security and IT security researchers who consult for Entrust Solution Nepal. SQL injection occurs when an attacker can influence SQL queries an application passes to a database, potentially allowing data leakage, site defacement, malware infection, or spear phishing. Defenses include addslashes(), mysql_real_escape_string(), is_numeric(), sprintf(), and htmlentities().