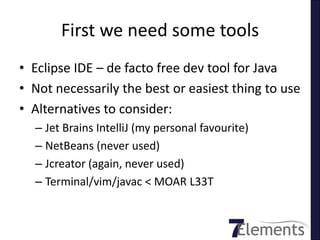
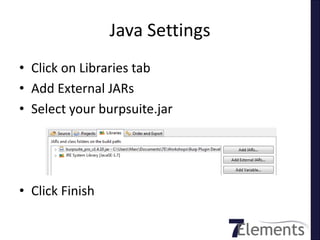
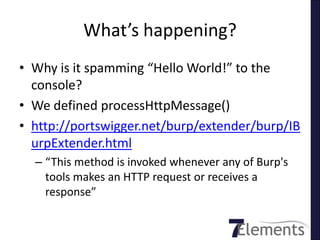
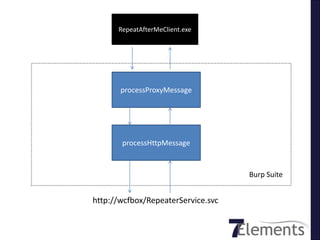
The document provides a comprehensive guide on developing Burp Suite plugins using Java for beginners. It covers essential topics such as setting up the Eclipse IDE, writing a simple plugin that interfaces with Burp's runtime data, and the limitations of Burp Extender. Furthermore, it includes practical examples, additional resources, and humorous asides to engage readers.

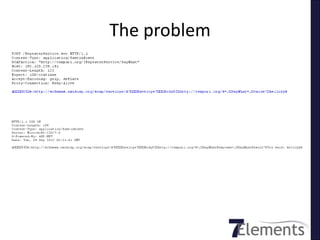



![First: we get it wrong
• Burp returns message body as byte[]
• Hmm, bytes are hard, let’s convert to String
• Split on rnrn](https://image.slidesharecdn.com/burpplugindevelopmentforjavan00bs44con-120913043528-phpapp01/85/Burp-plugin-development-for-java-n00bs-44-con-53-320.jpg)