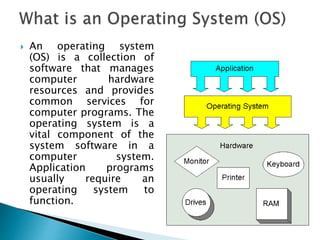
The document discusses operating systems, including their functions, components, and types. It provides details on single-user single-tasking operating systems, single-user multi-tasking operating systems, and multi-user multi-tasking operating systems. Examples of commonly used operating systems like Windows and MacOS are described. Key aspects of operating systems that are covered include process management, memory management, I/O device management, and providing a user interface.