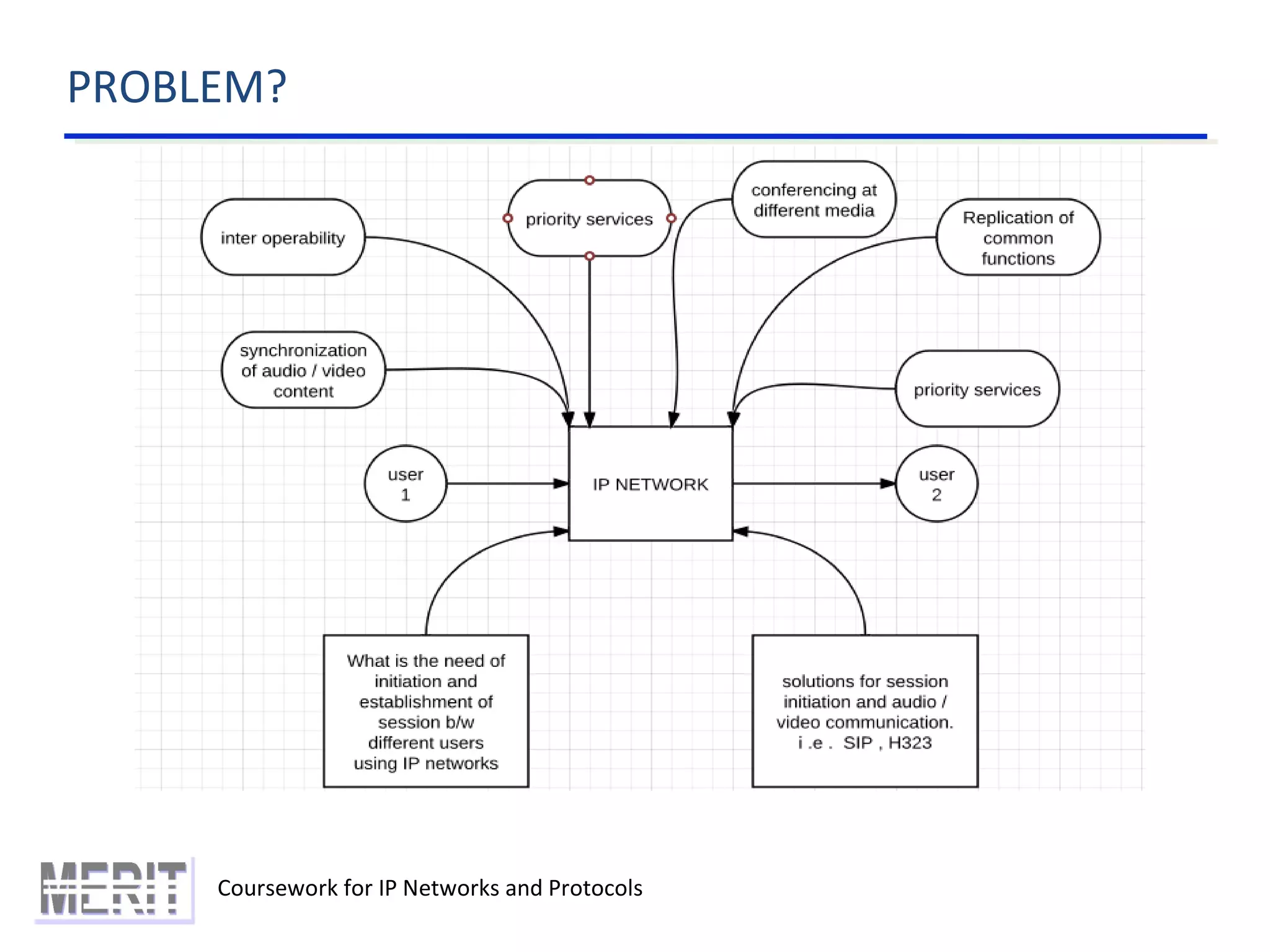
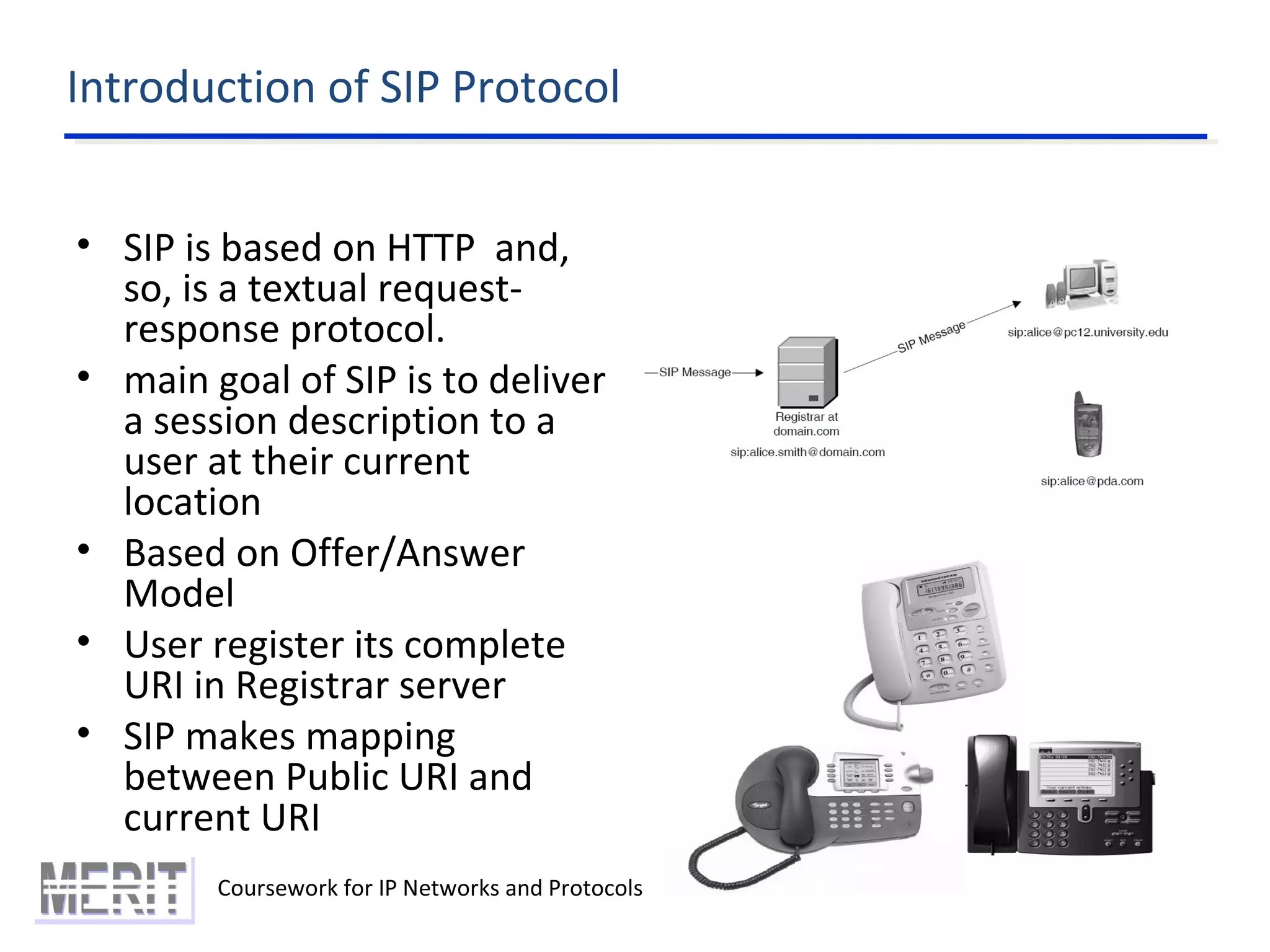
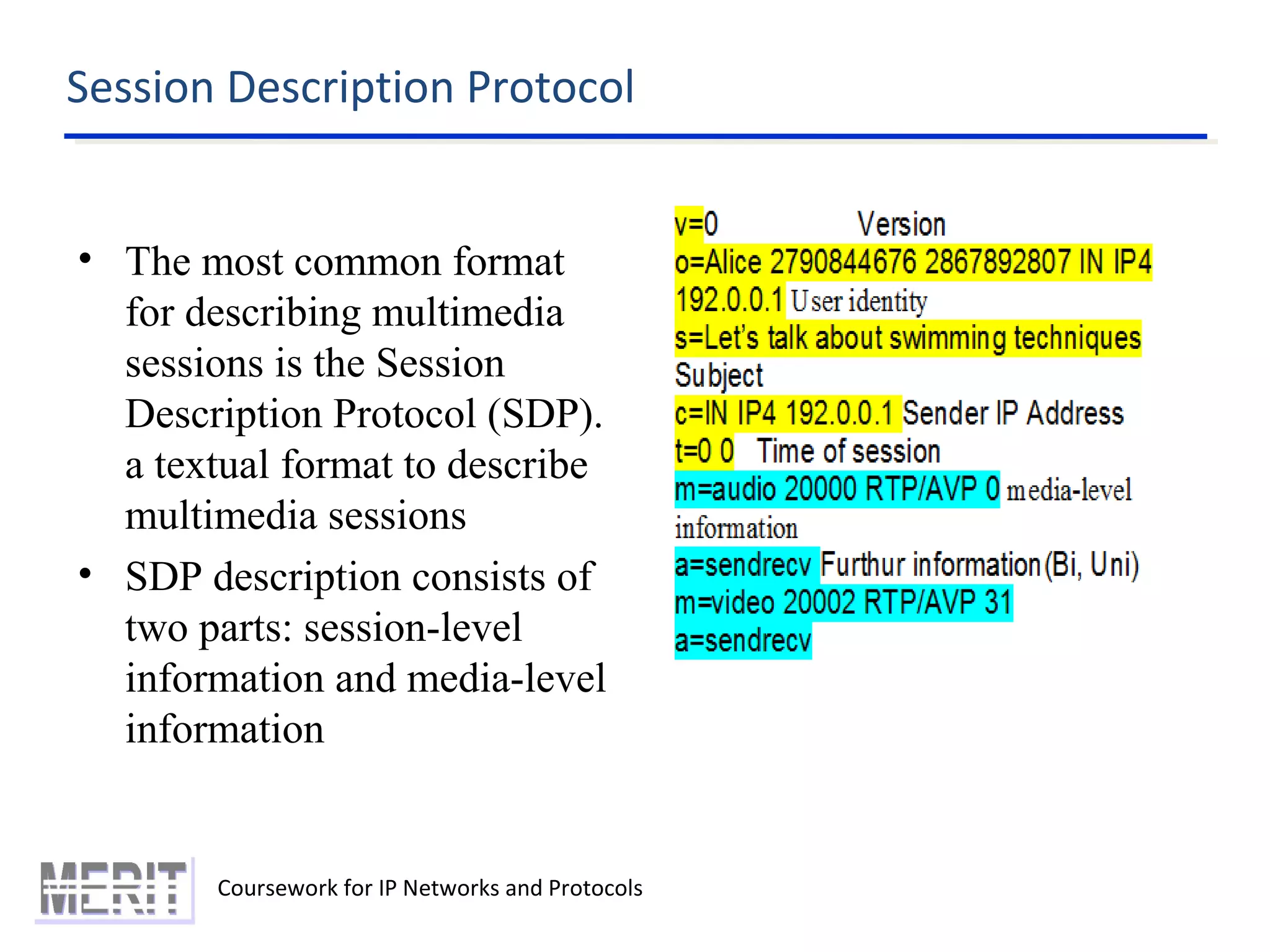
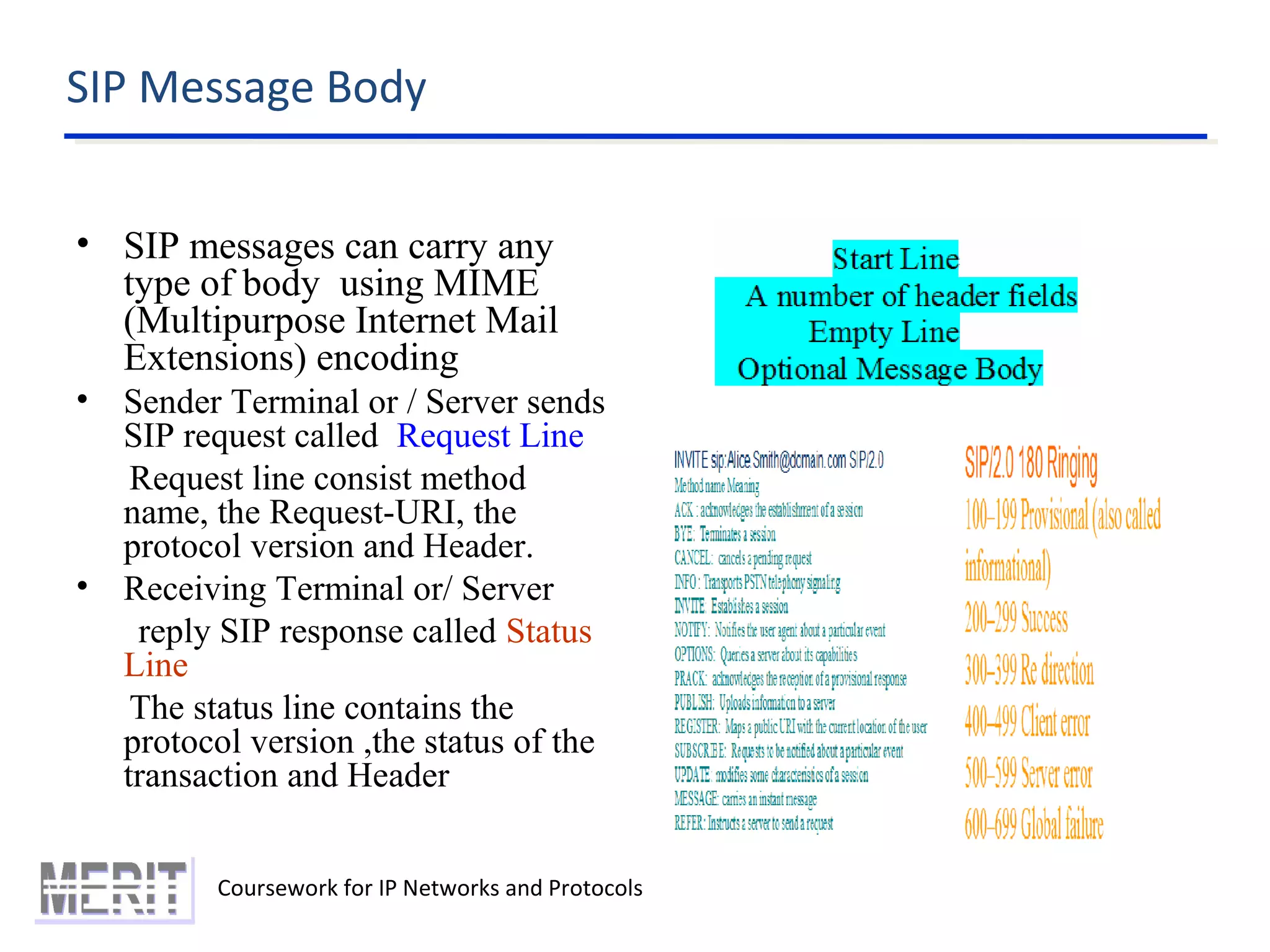
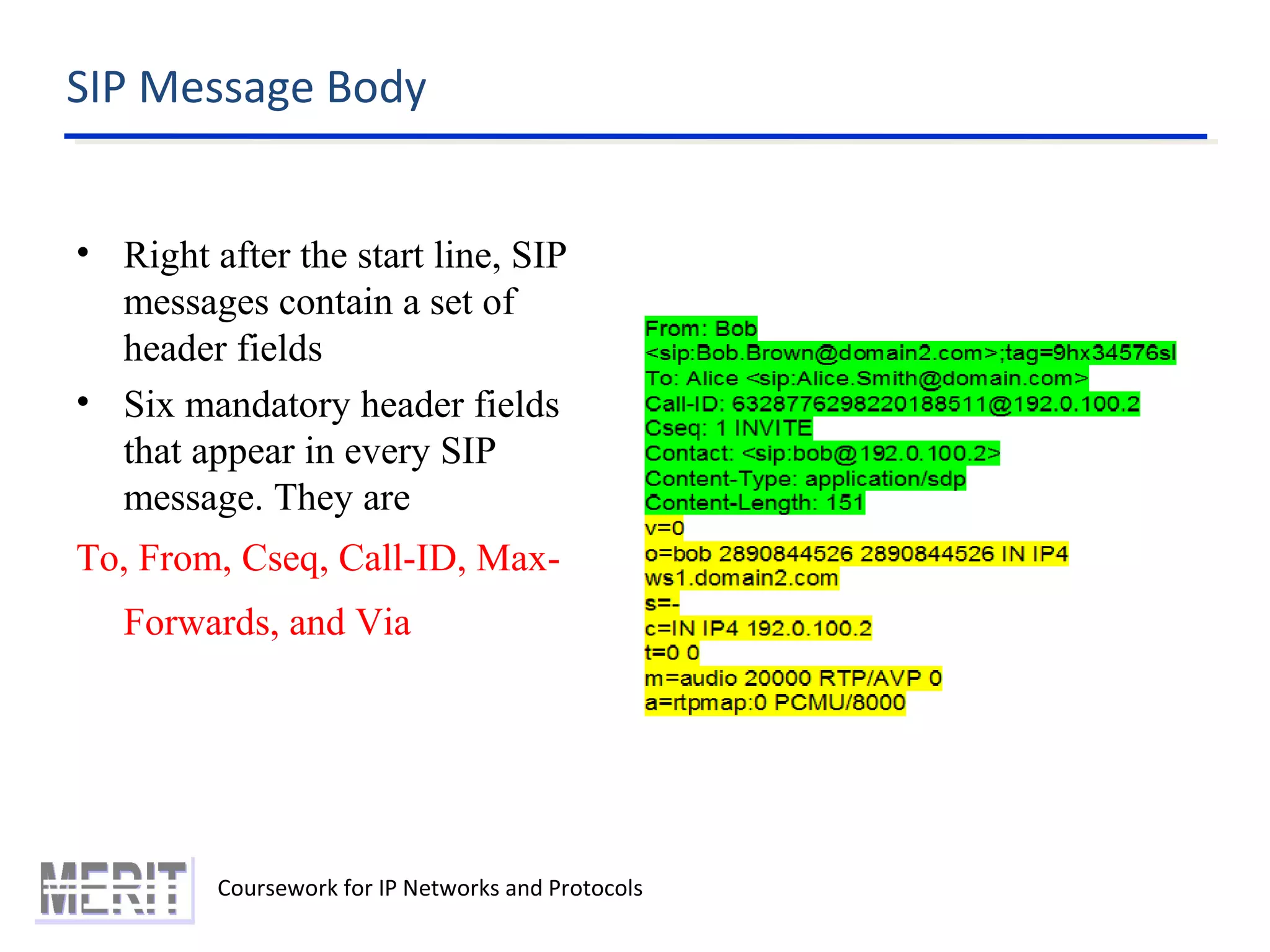
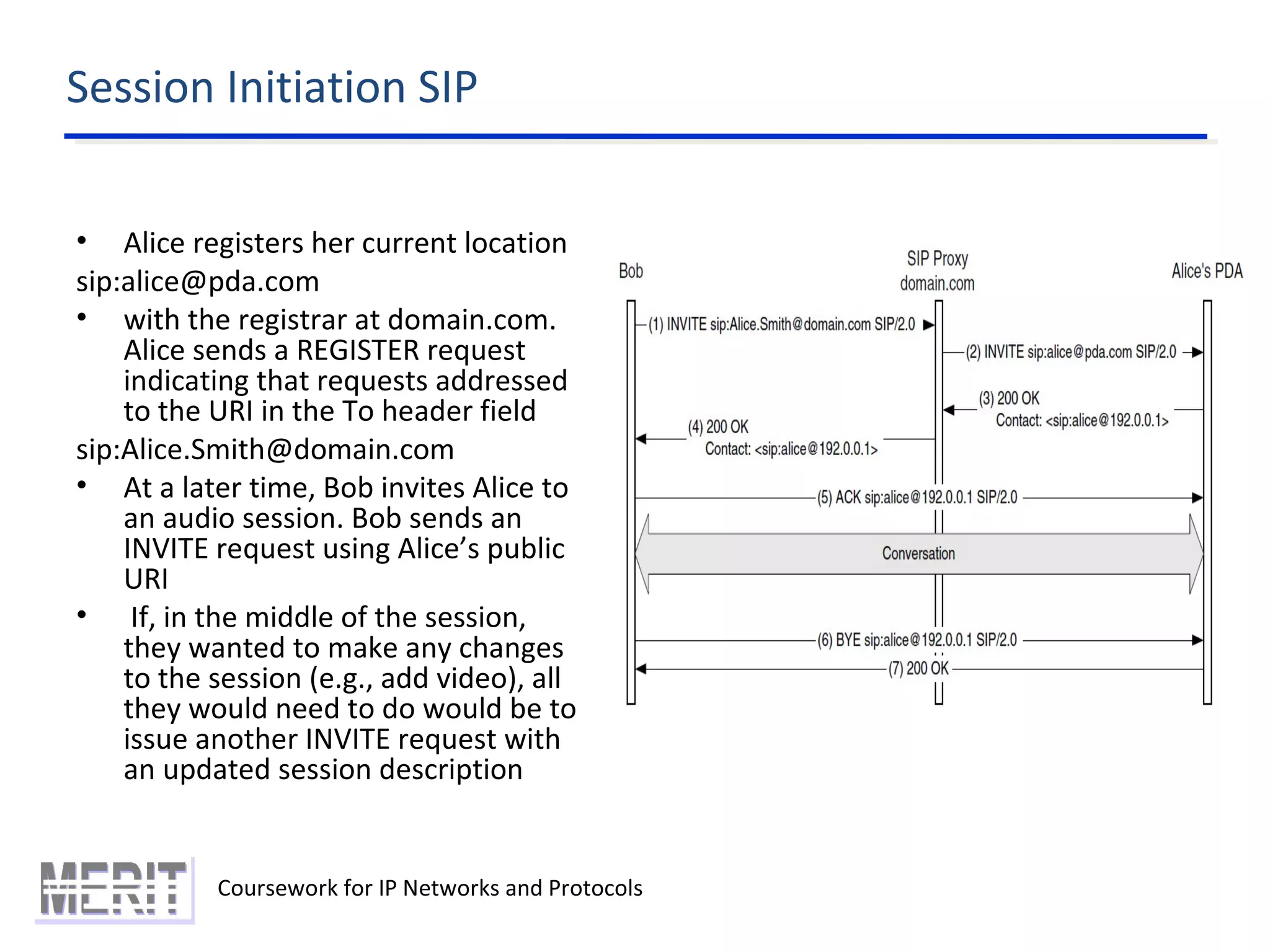
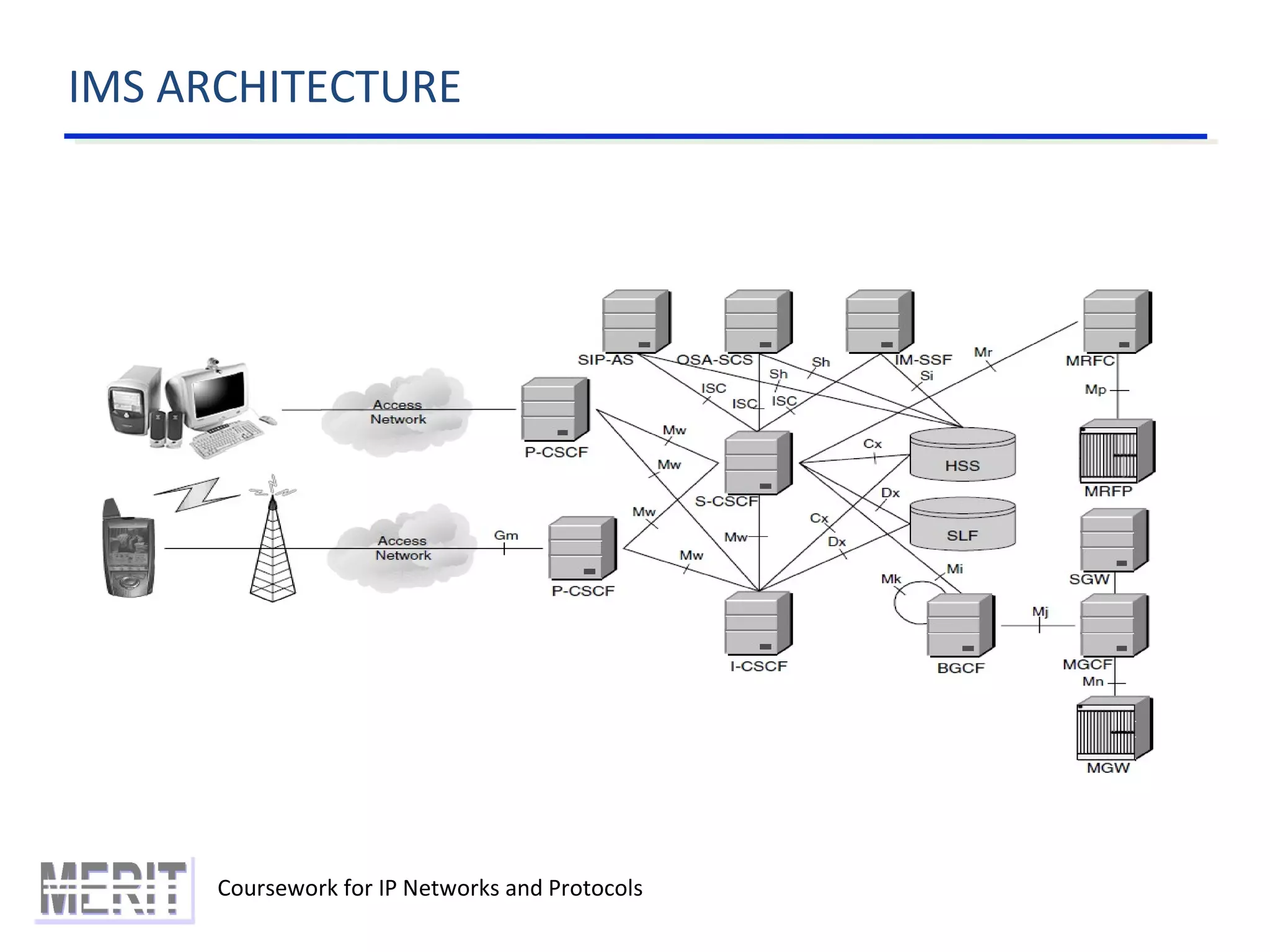
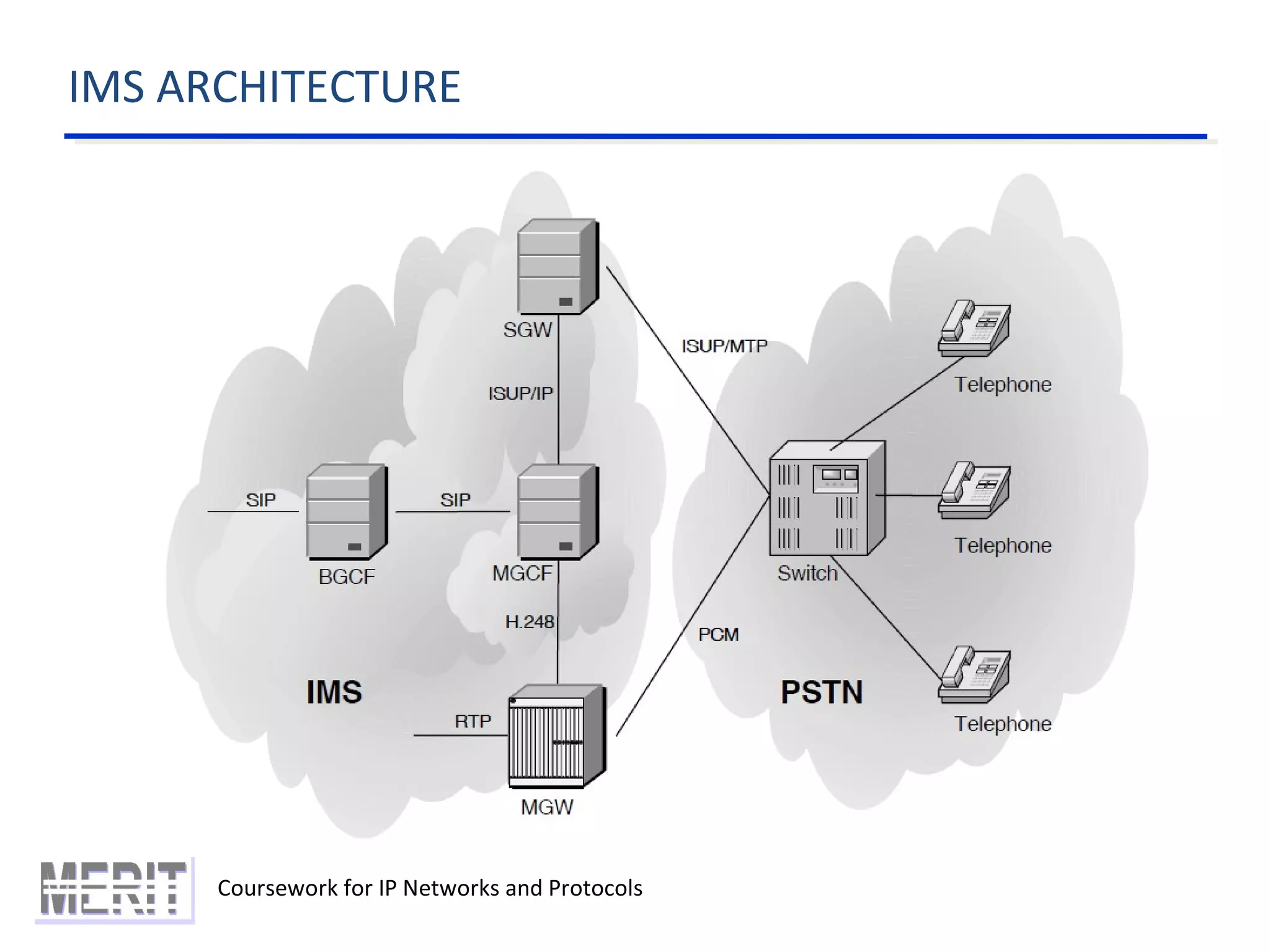
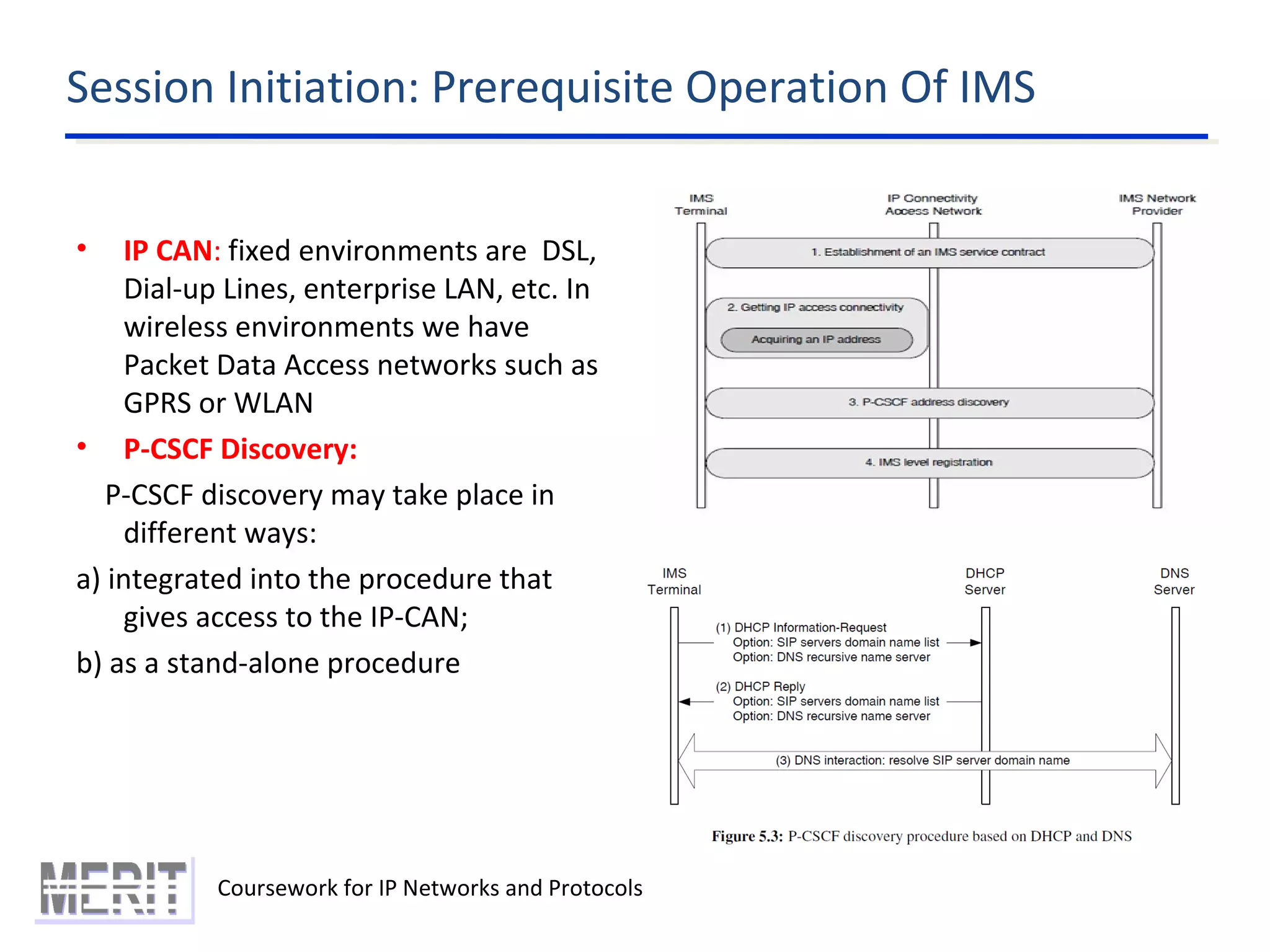
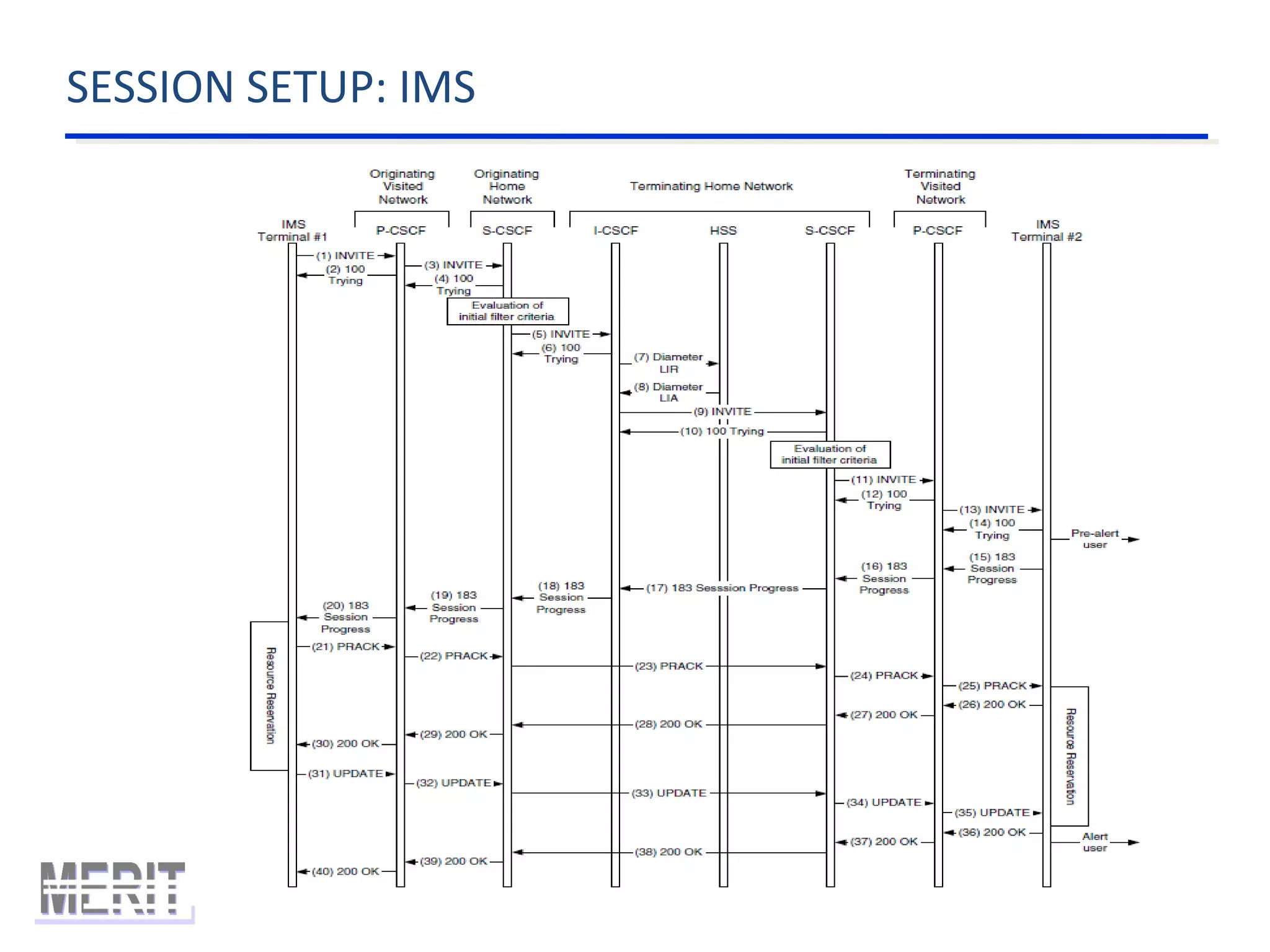
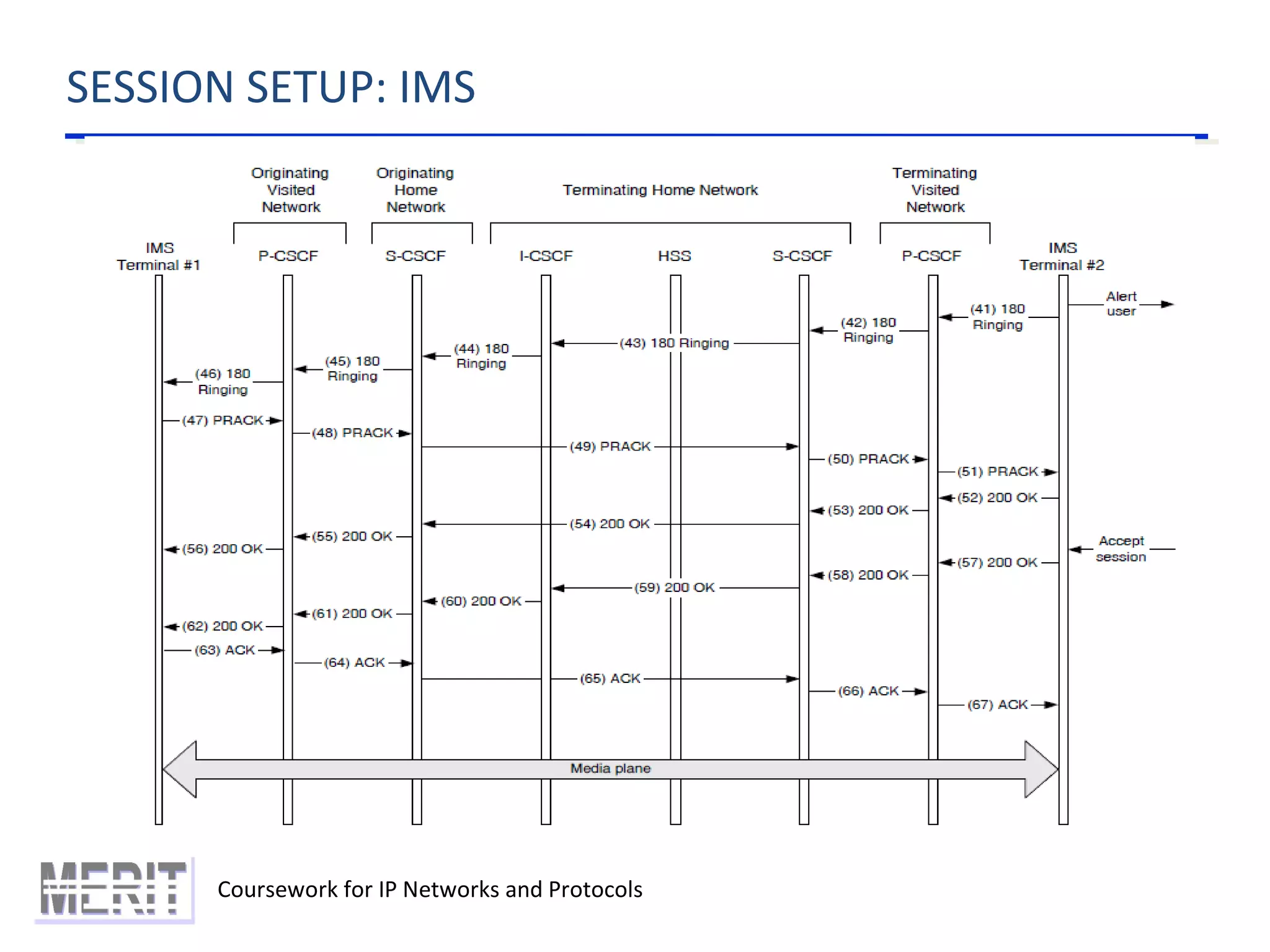
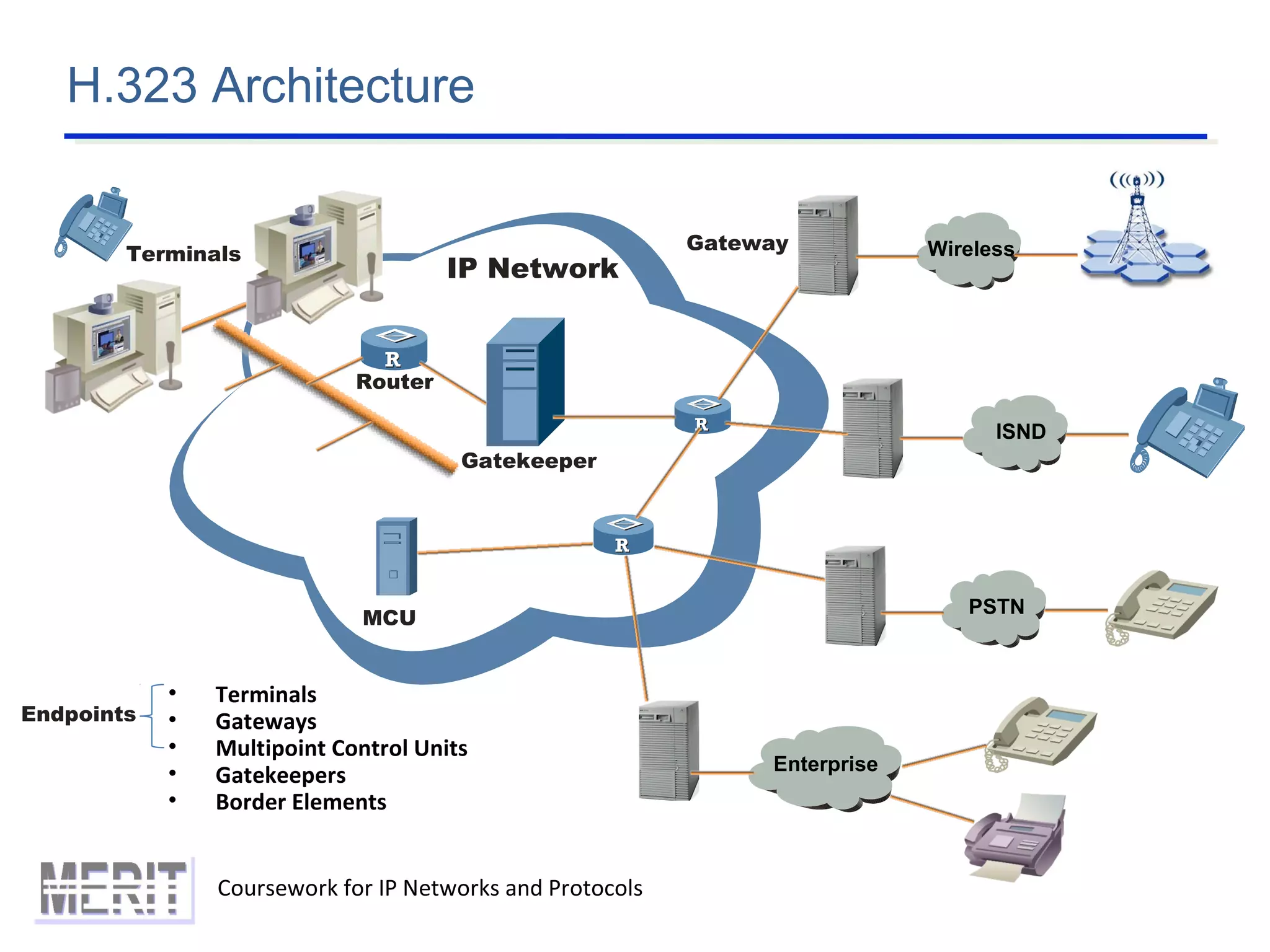
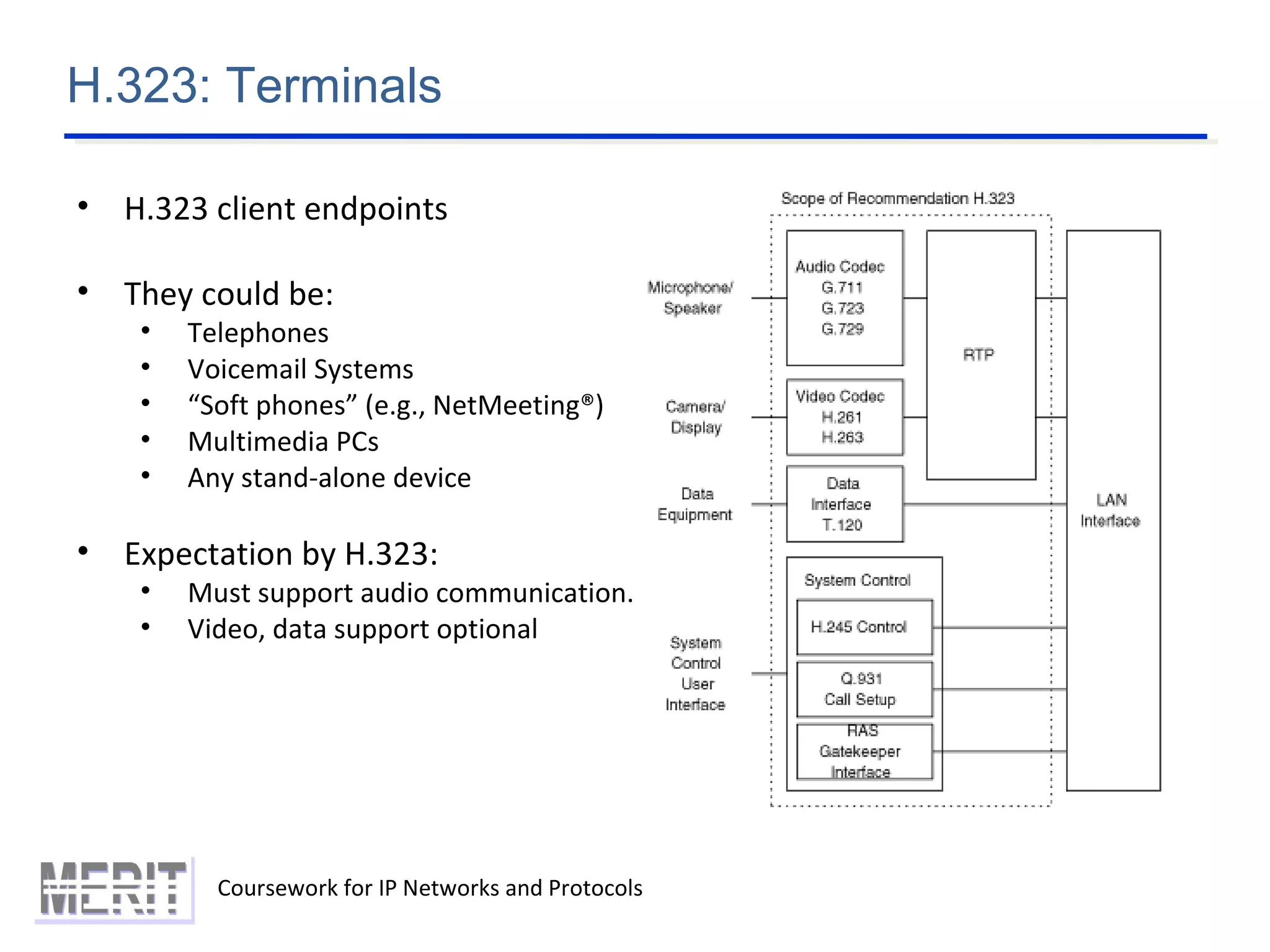
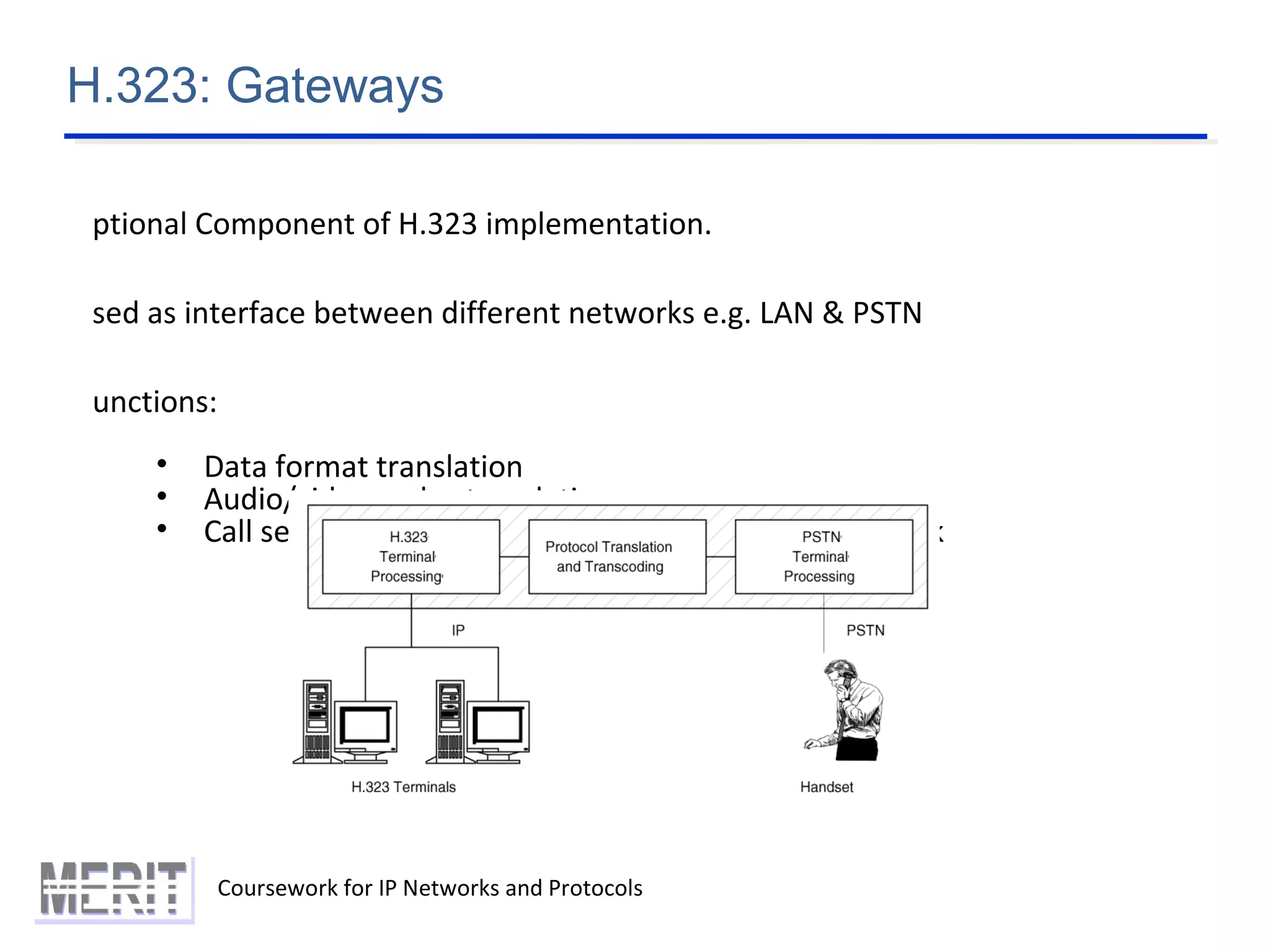
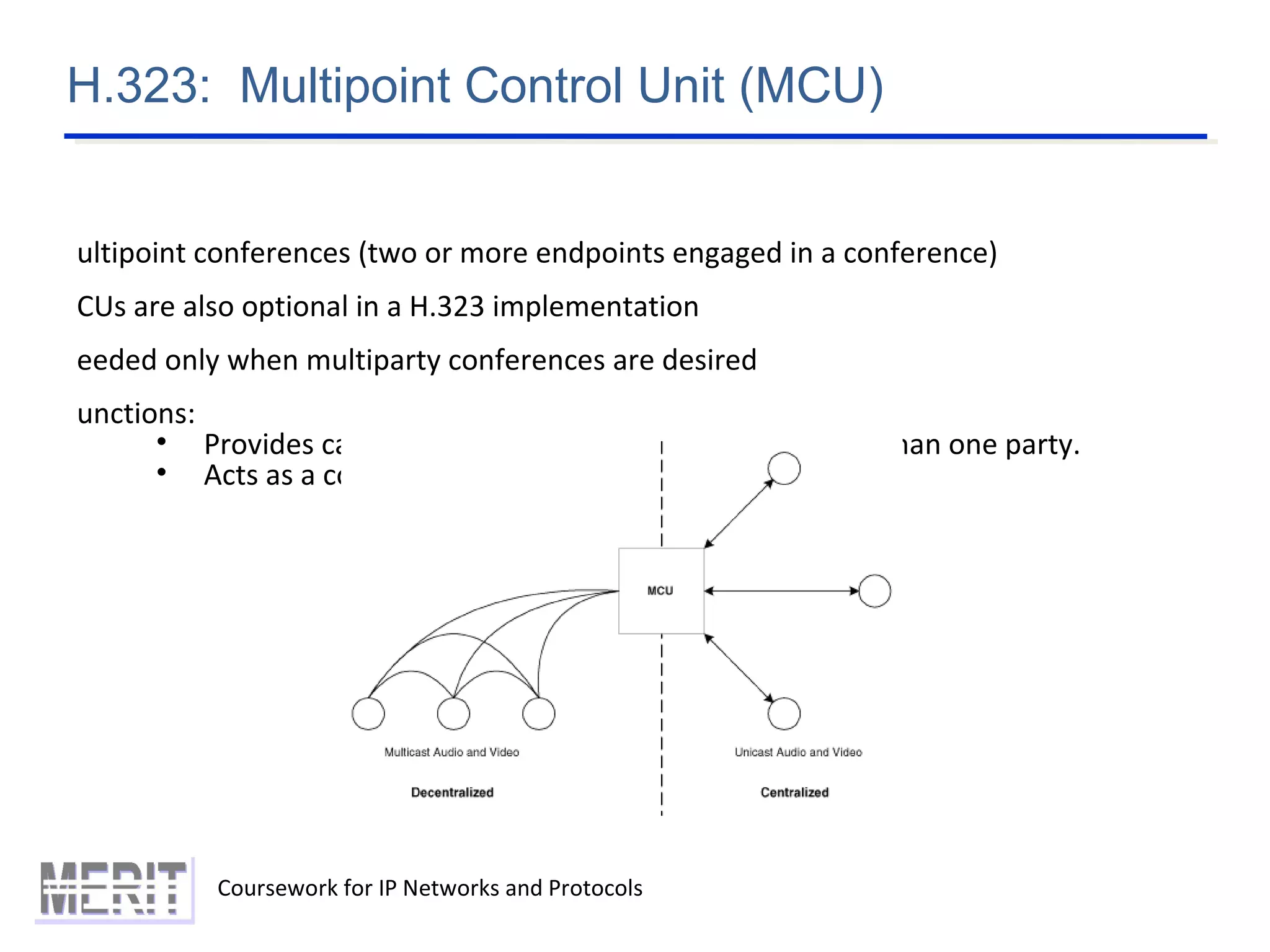
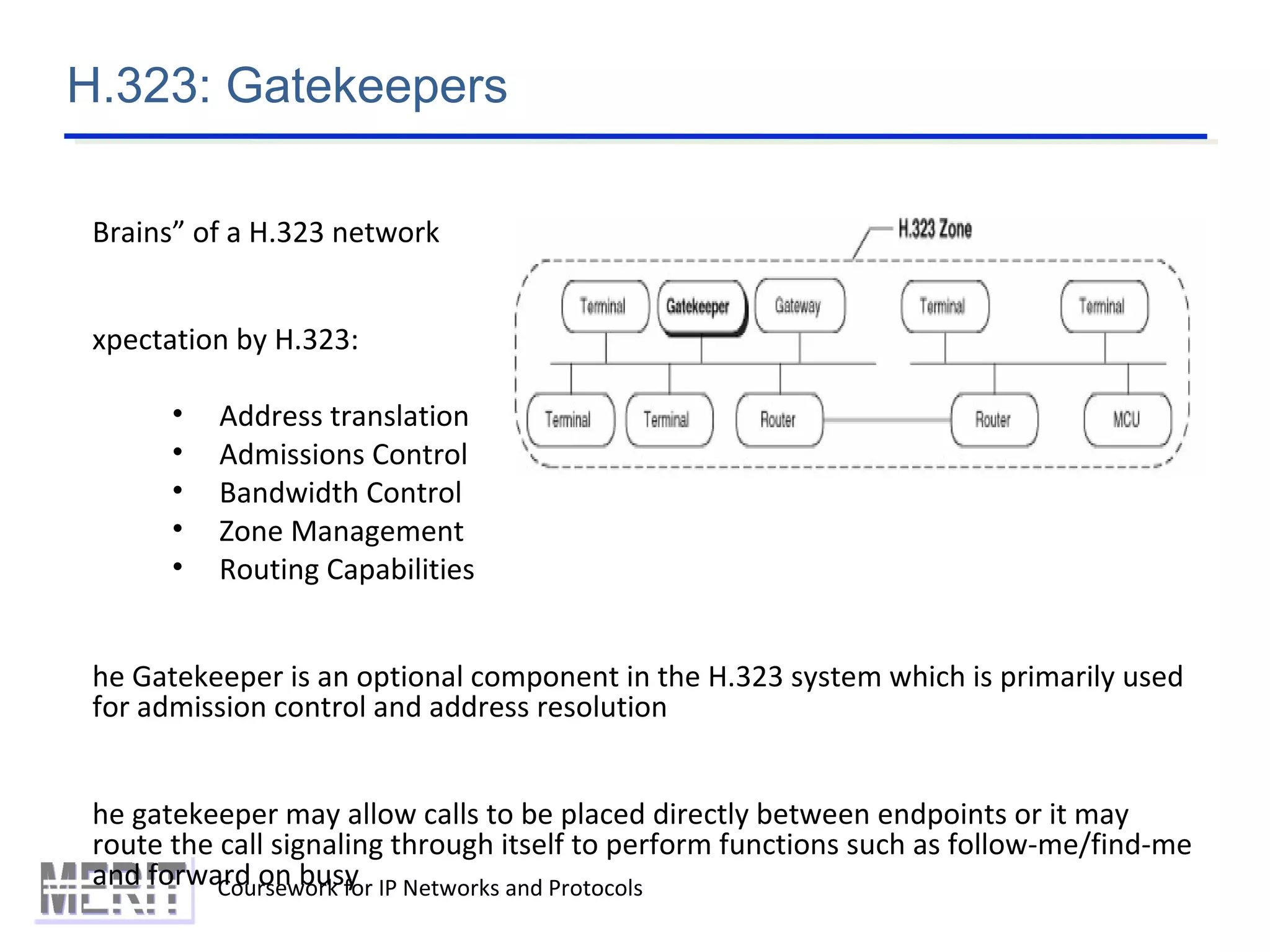
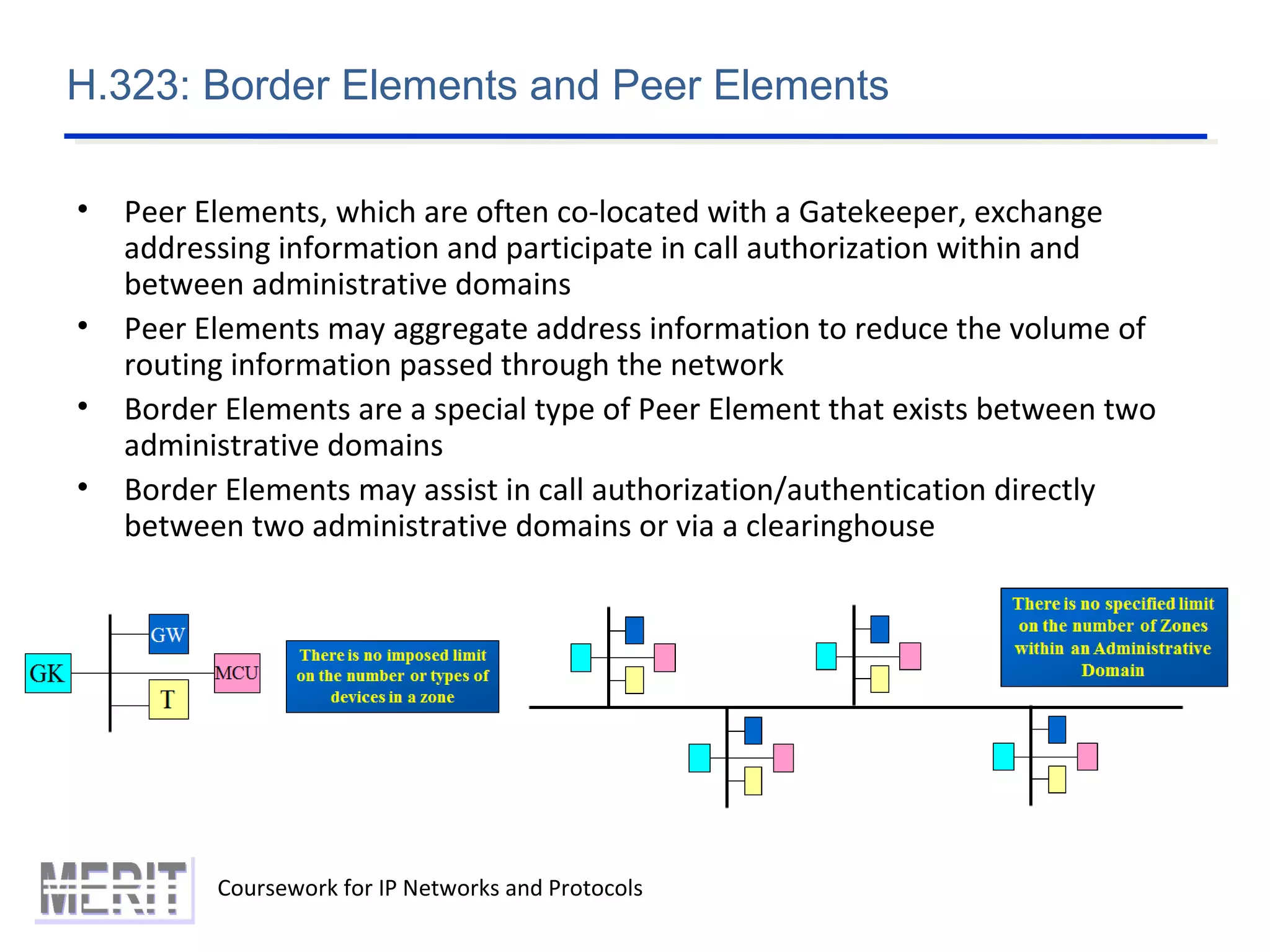
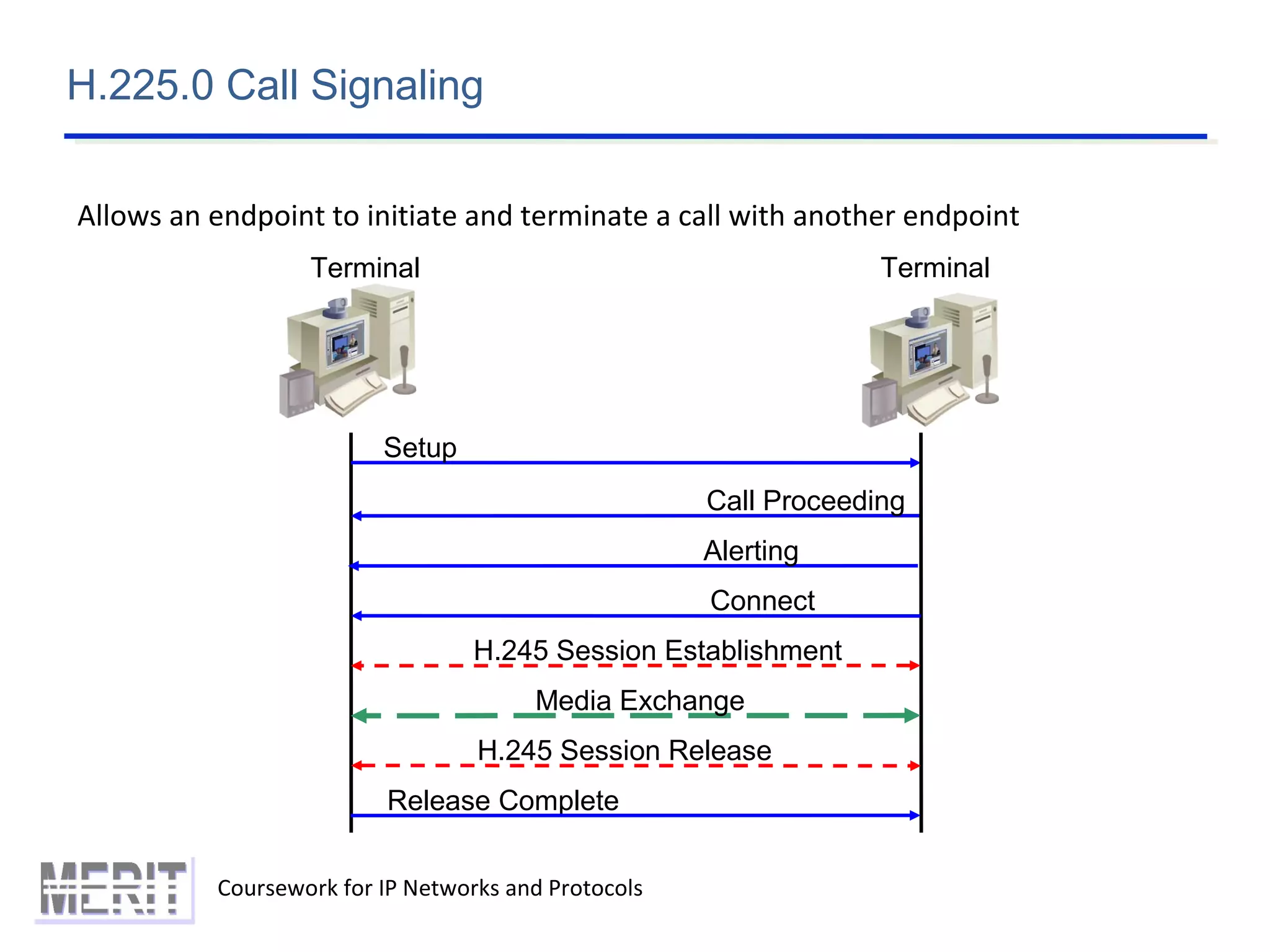
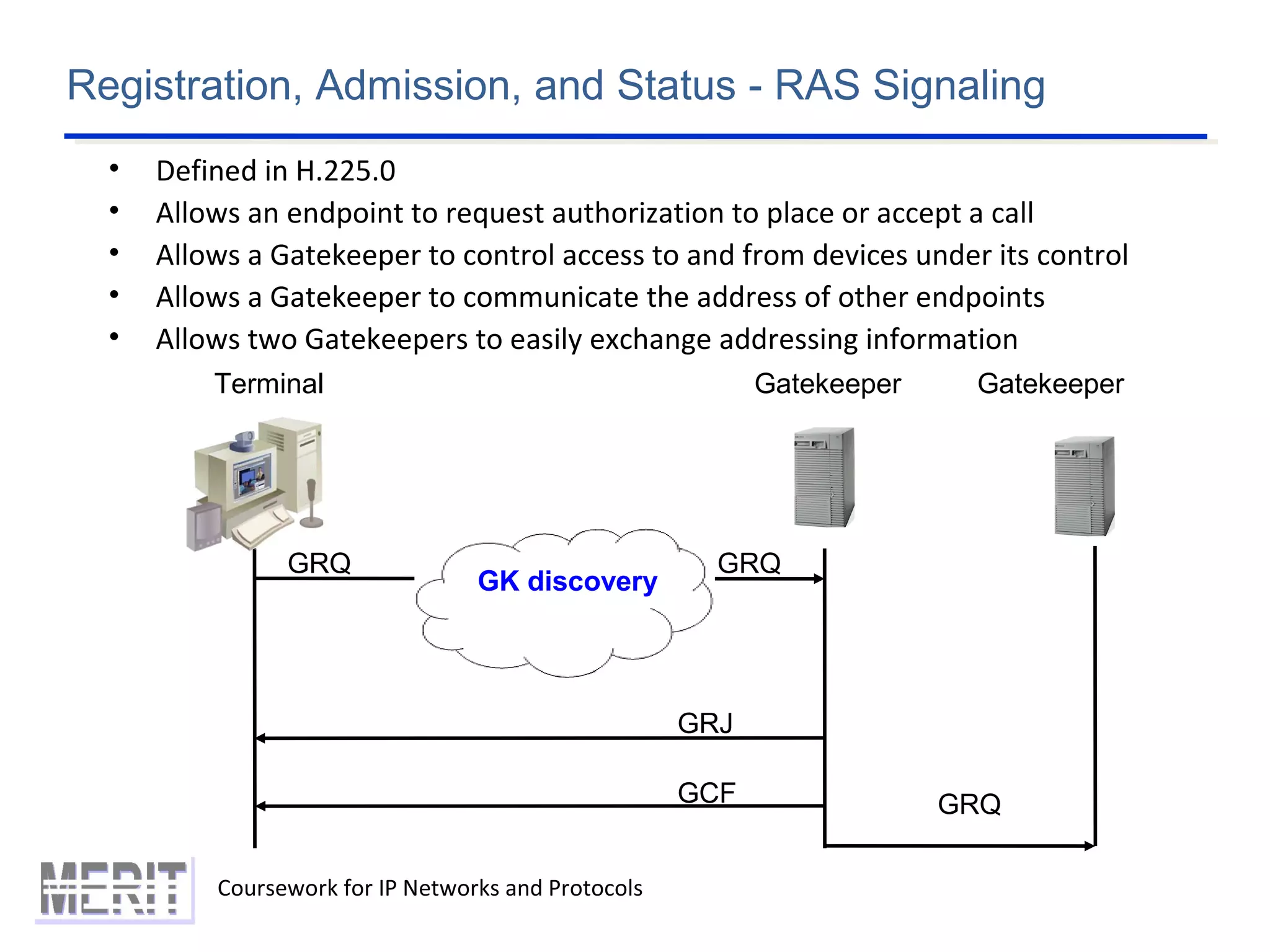
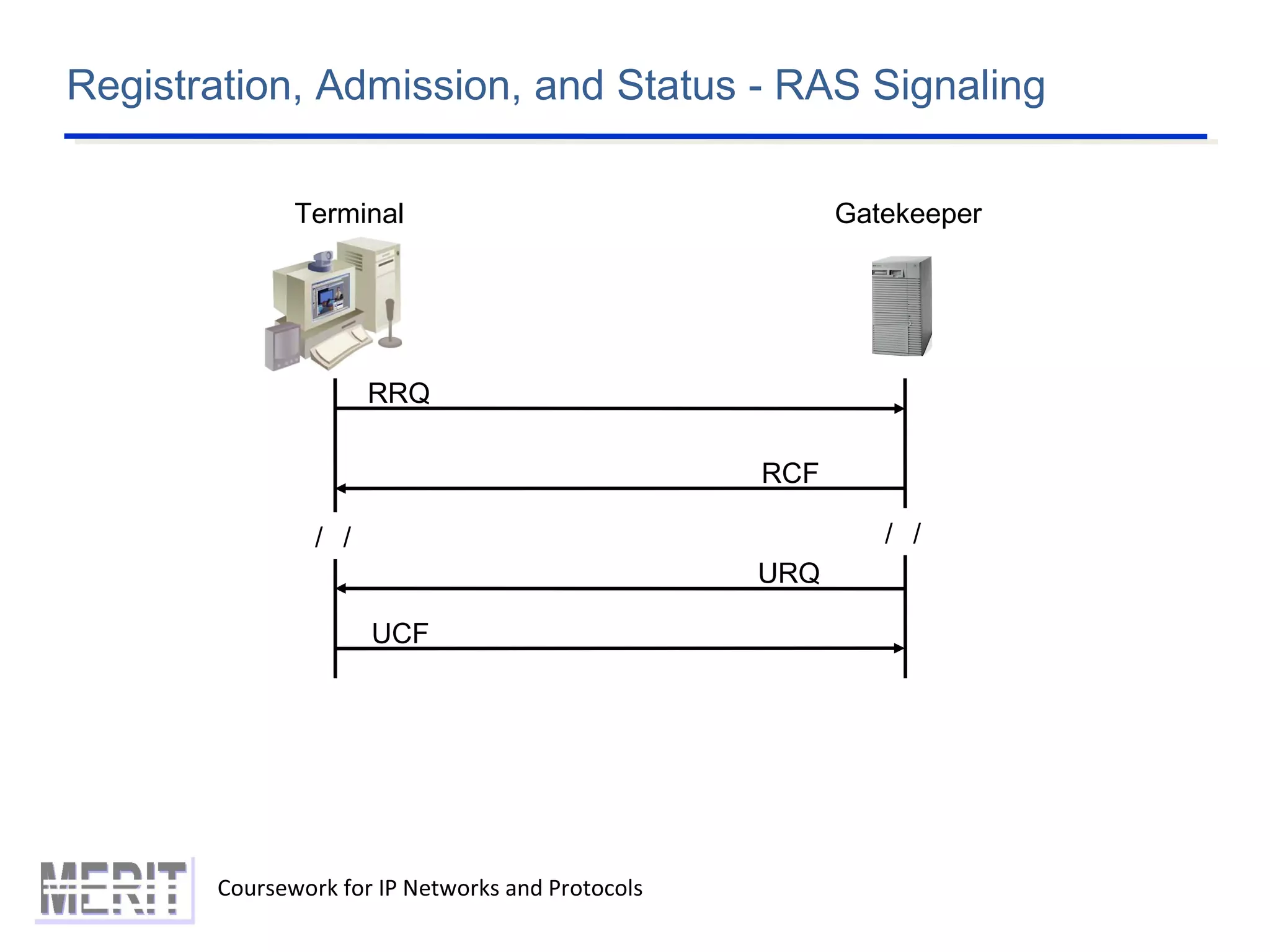
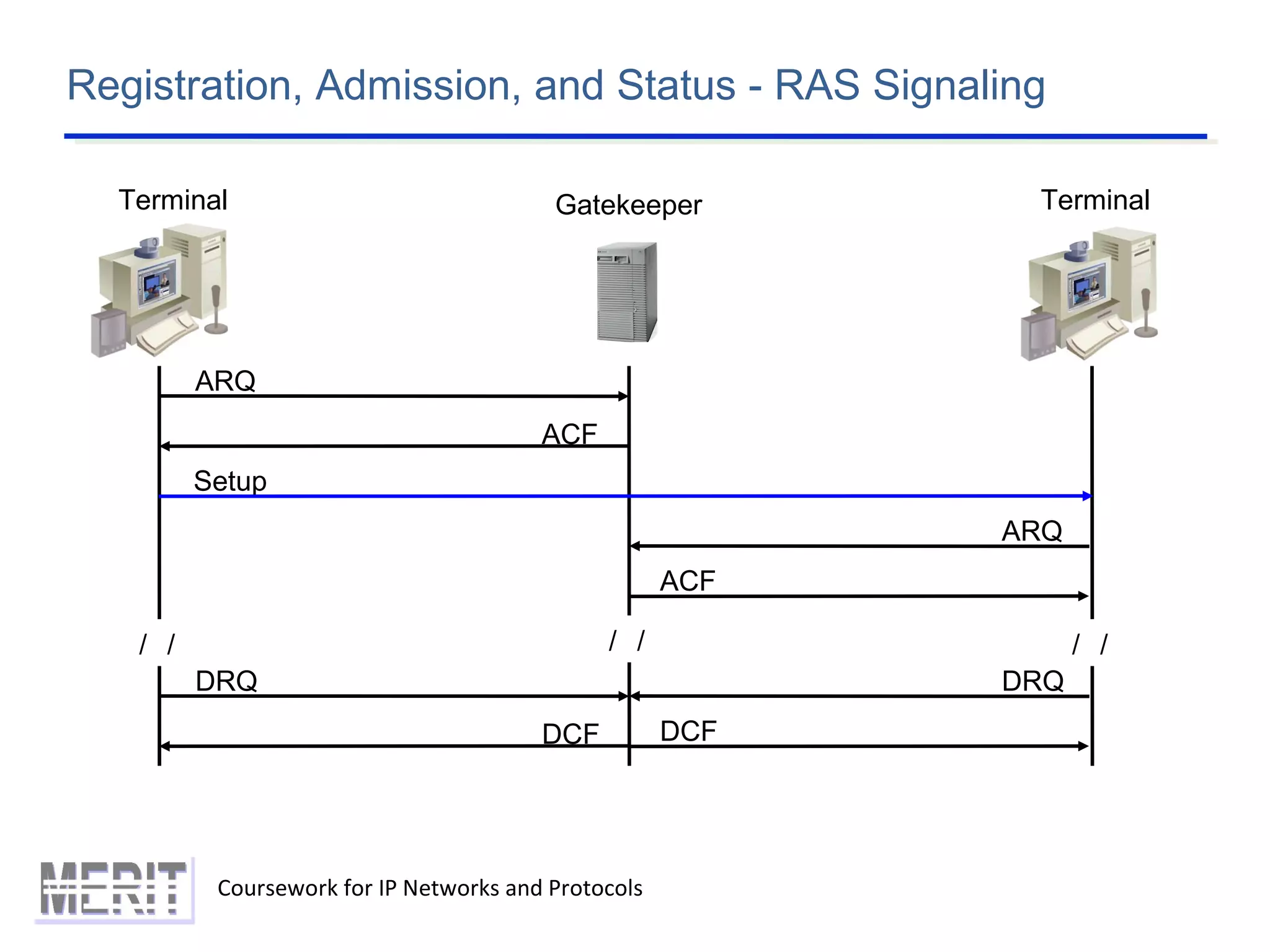
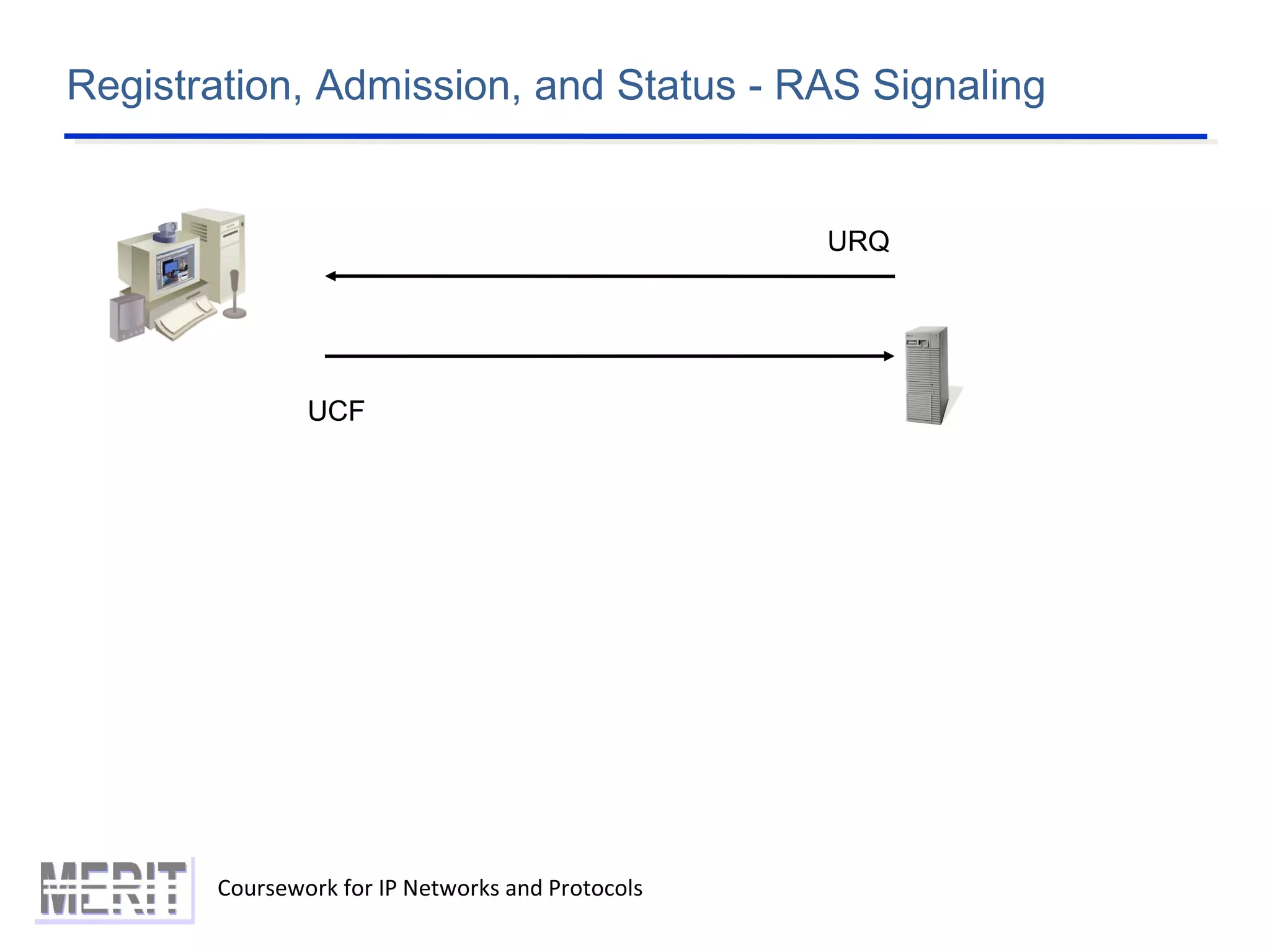
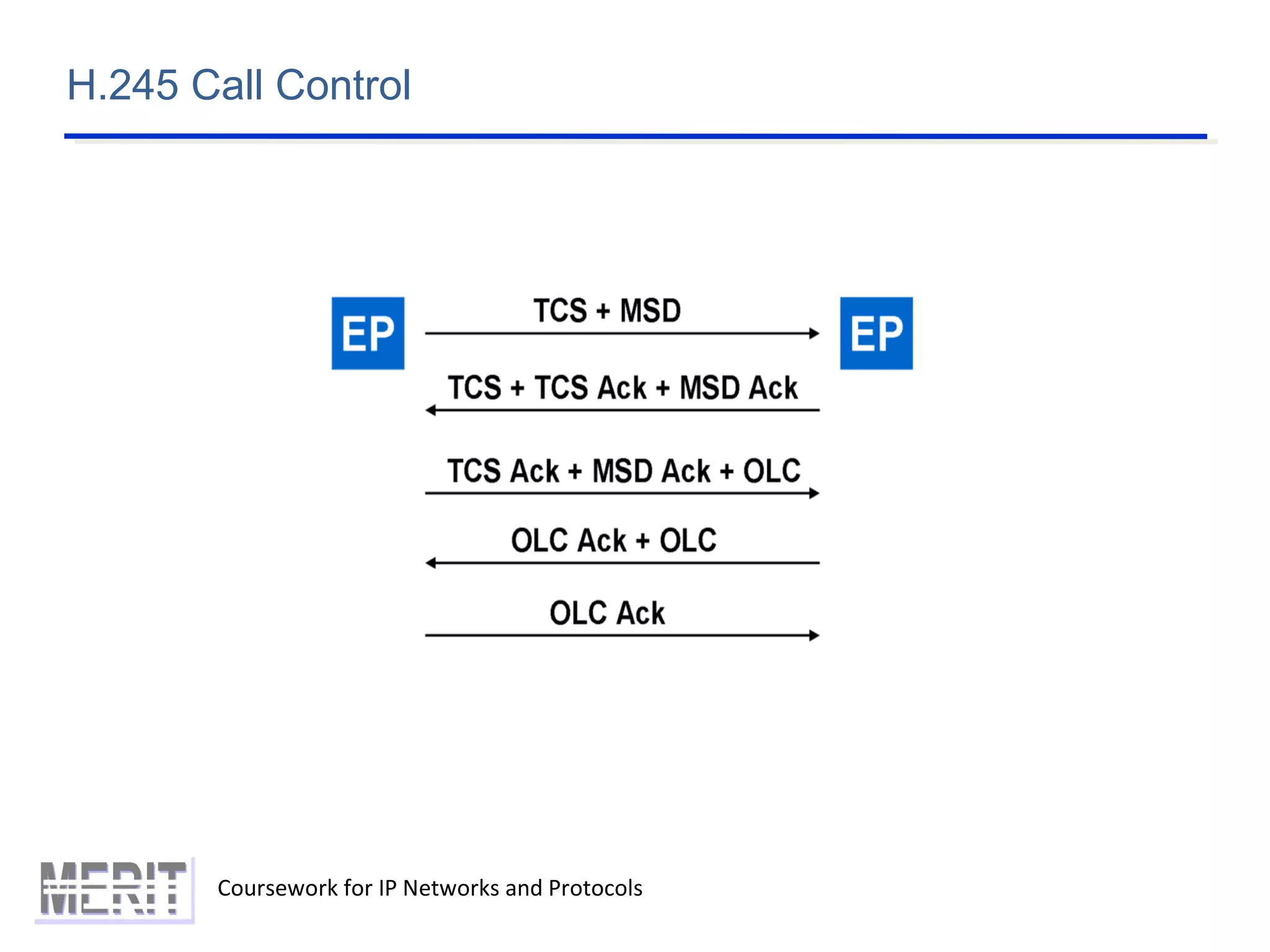
This document provides an overview of multimedia services over IP networks and discusses two key protocols used: SIP and H.323. It describes the basics of SIP including session descriptions using SDP, message format, and session initiation. It also discusses SIP applications like IMS including requirements, protocols used, and architecture. For H.323, it outlines the network architecture including terminals, MCUs, gateways, and gatekeepers. It then describes the H.323 signaling protocols including RAS, H.225 call signaling, and H.245 call control.