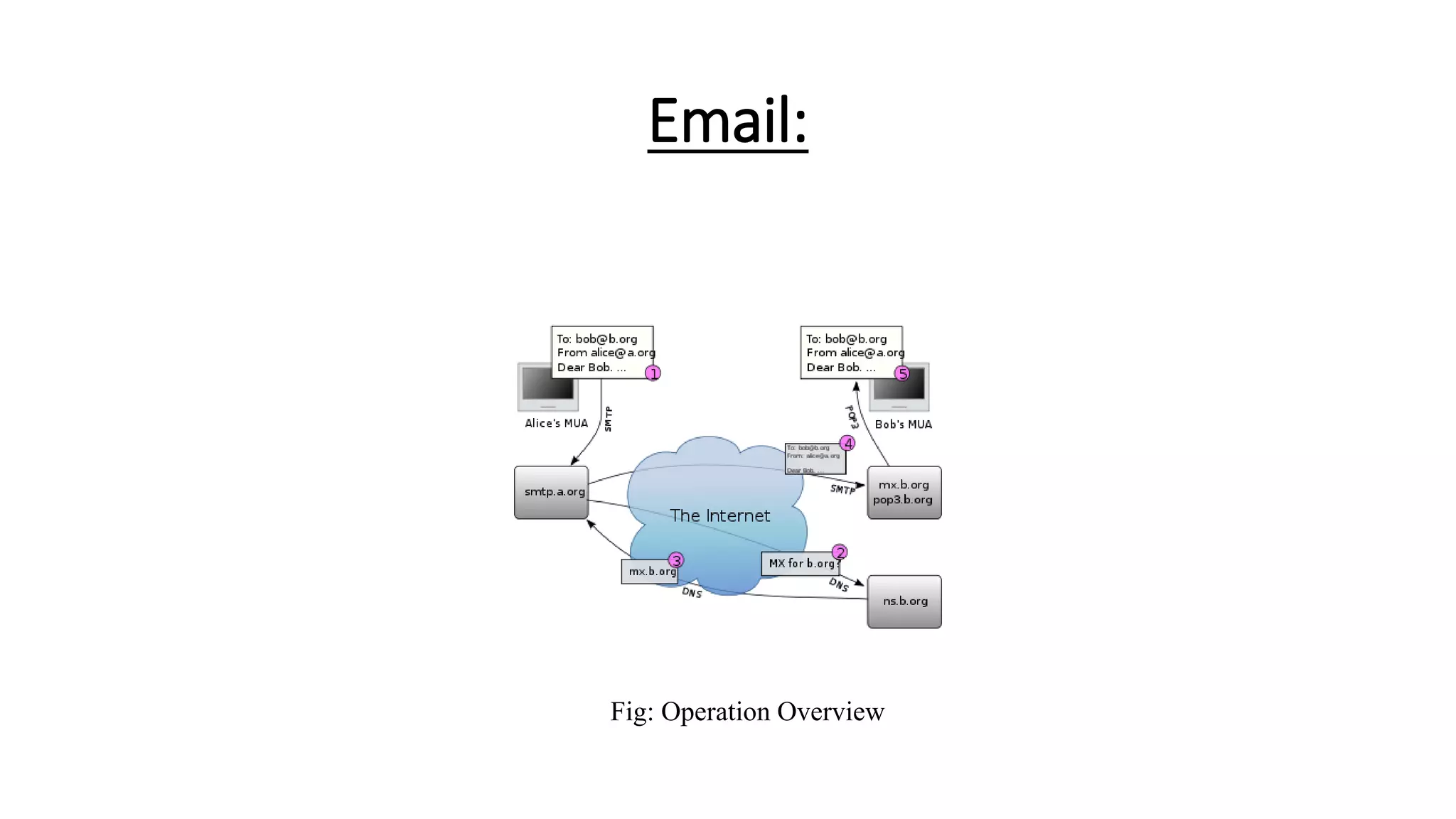
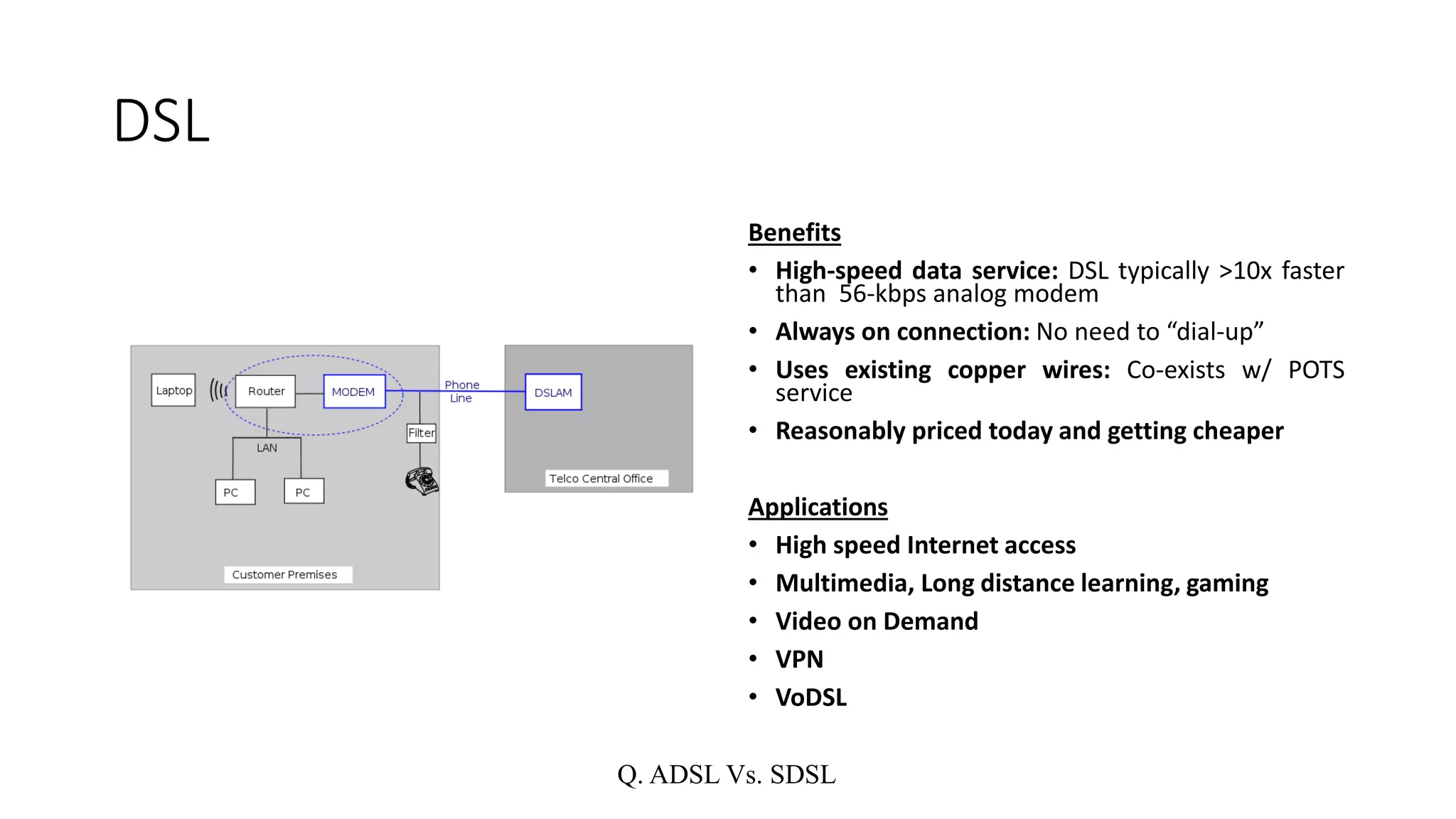
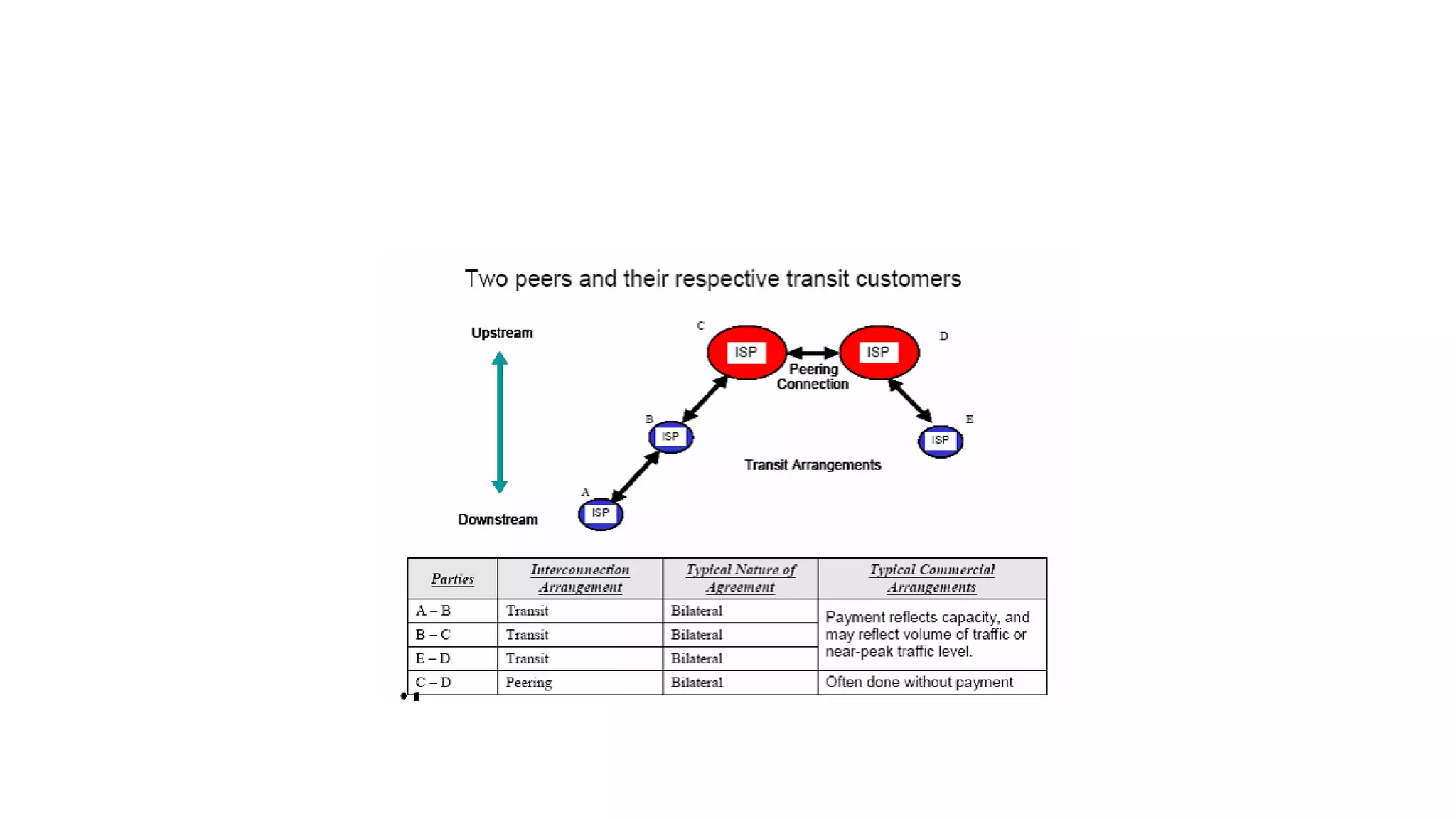
This document discusses various topics related to internet and intranet applications including email, internet protocols, multimedia broadcasting, internet relay chat, broadband communication technologies, data centers, e-commerce, and unified messaging. It provides details on email formats, protocols like POP3, IMAP, MAPI. It also explains technologies like DSL, cable internet, VOIP, and protocols like IRC, SIP, and RTP. Further, it summarizes concepts of data warehousing, packet clearing houses, and benefits of unified messaging and e-commerce.