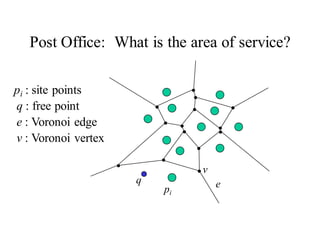
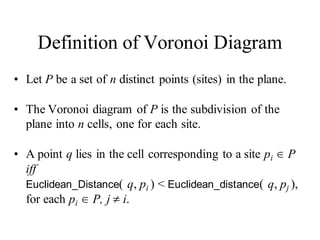
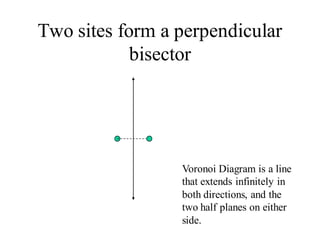
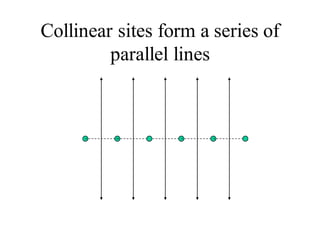
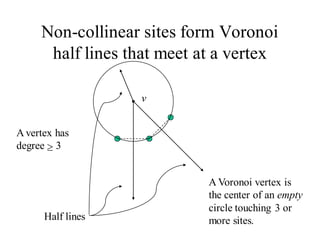
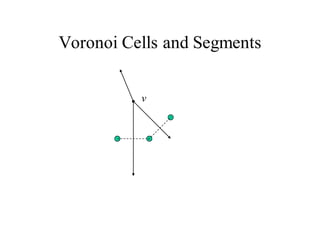
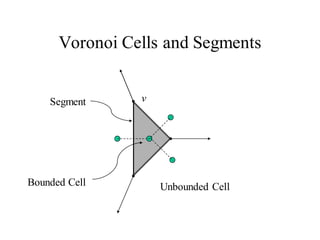
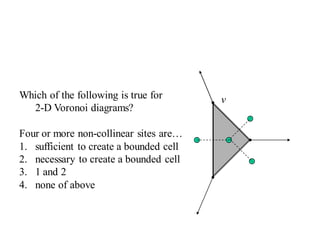
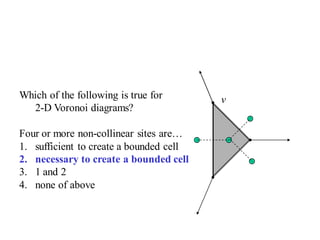
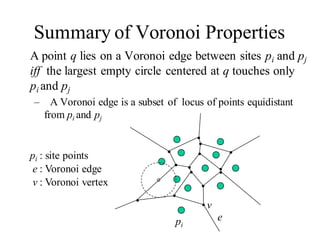
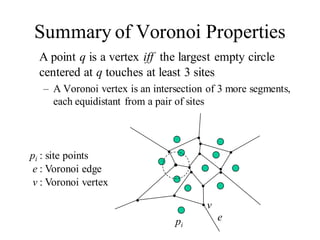
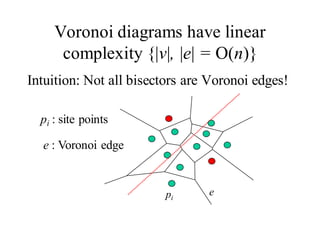
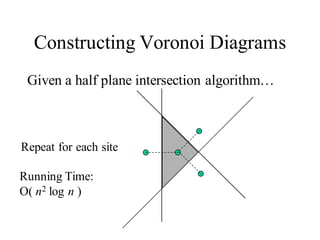
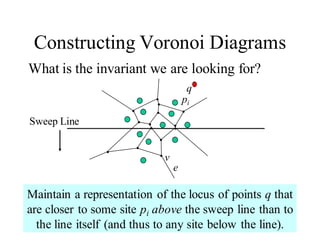
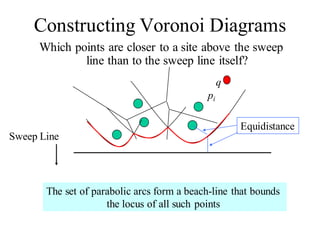
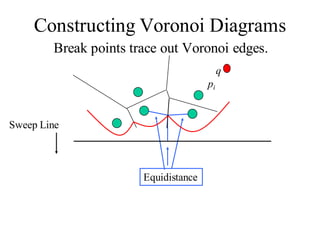
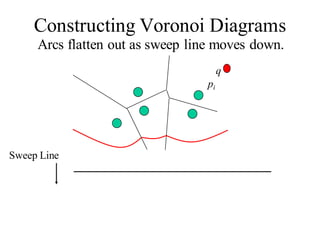
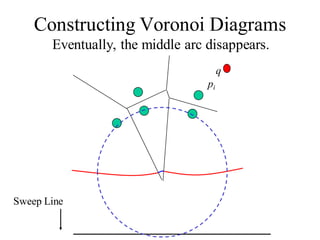
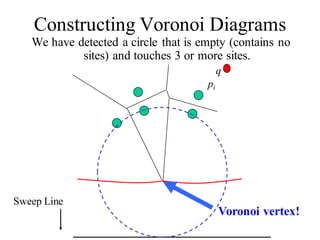
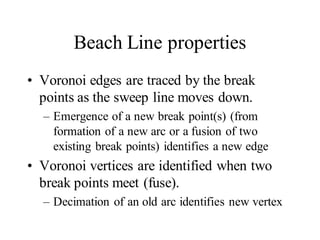
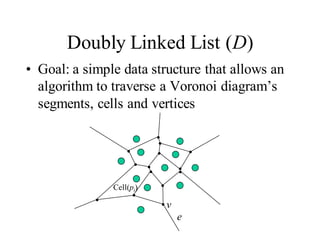
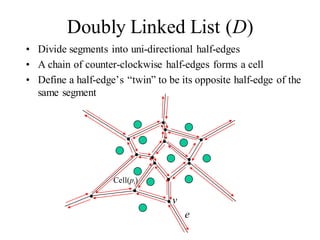
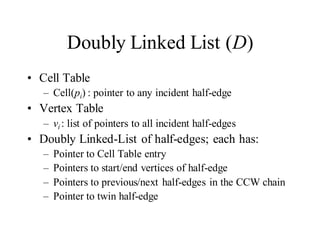
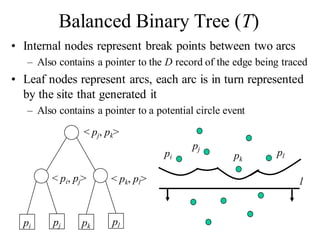
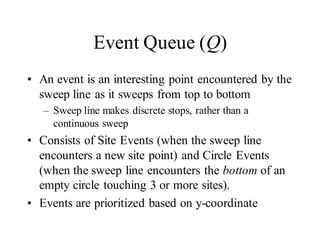
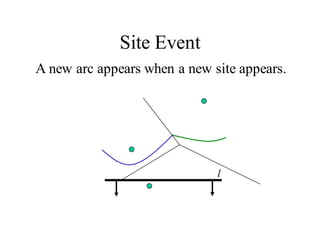
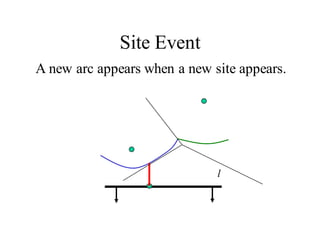
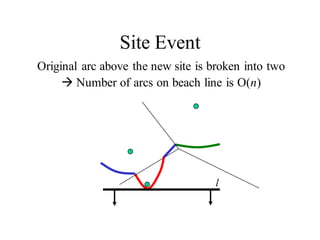
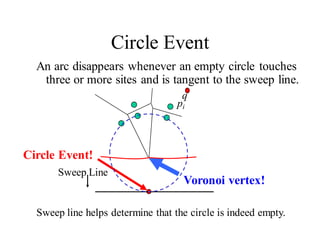
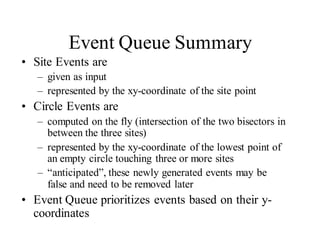
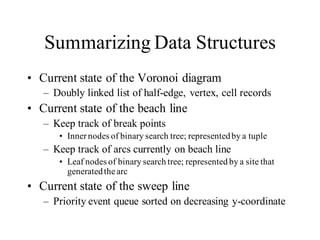
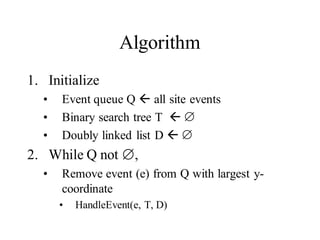
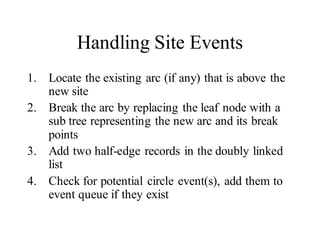
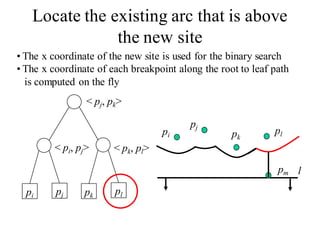
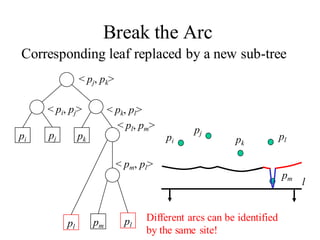
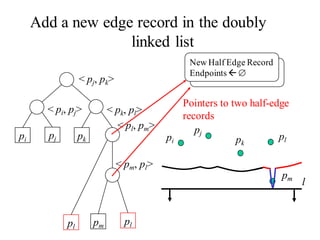
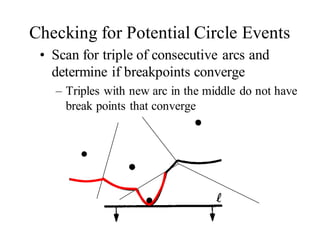
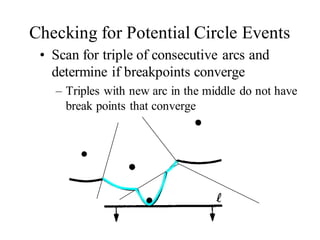
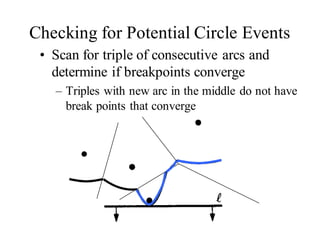
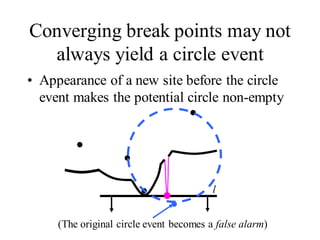
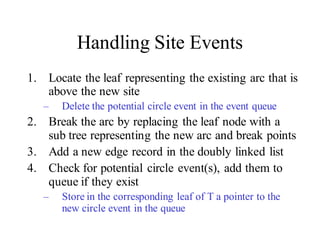
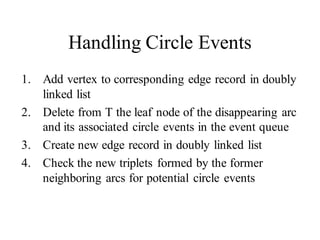
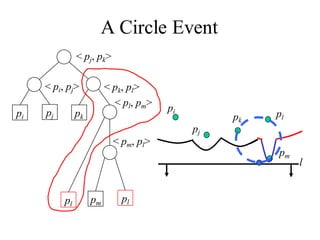
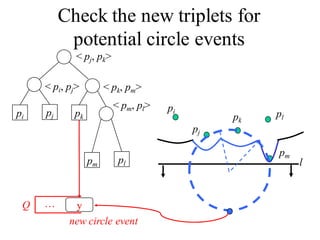
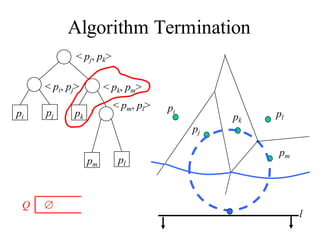
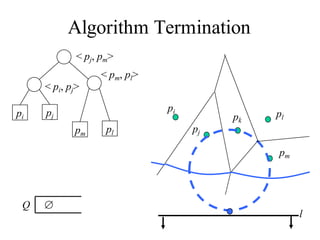
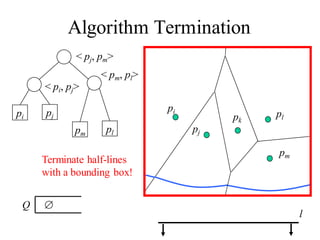
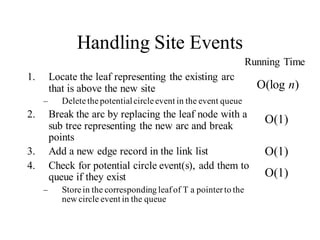
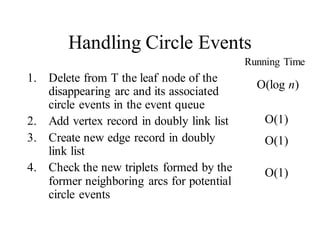
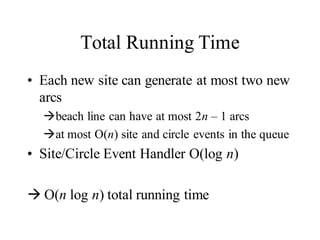
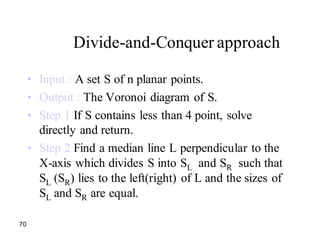
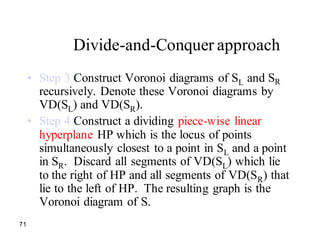
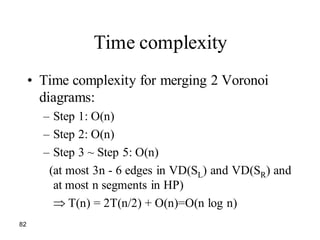
The document describes Voronoi diagrams and an algorithm for constructing them efficiently. Voronoi diagrams partition space into regions based on distance to points called sites. The algorithm uses a sweep line approach, maintaining the current state of the diagram. It handles events where the sweep line encounters a site or potential empty circle. The key data structures are a balanced binary search tree to represent the beach line, a doubly linked list to represent the constructed diagram, and a priority queue of events. The algorithm runs in O(n log n) time.