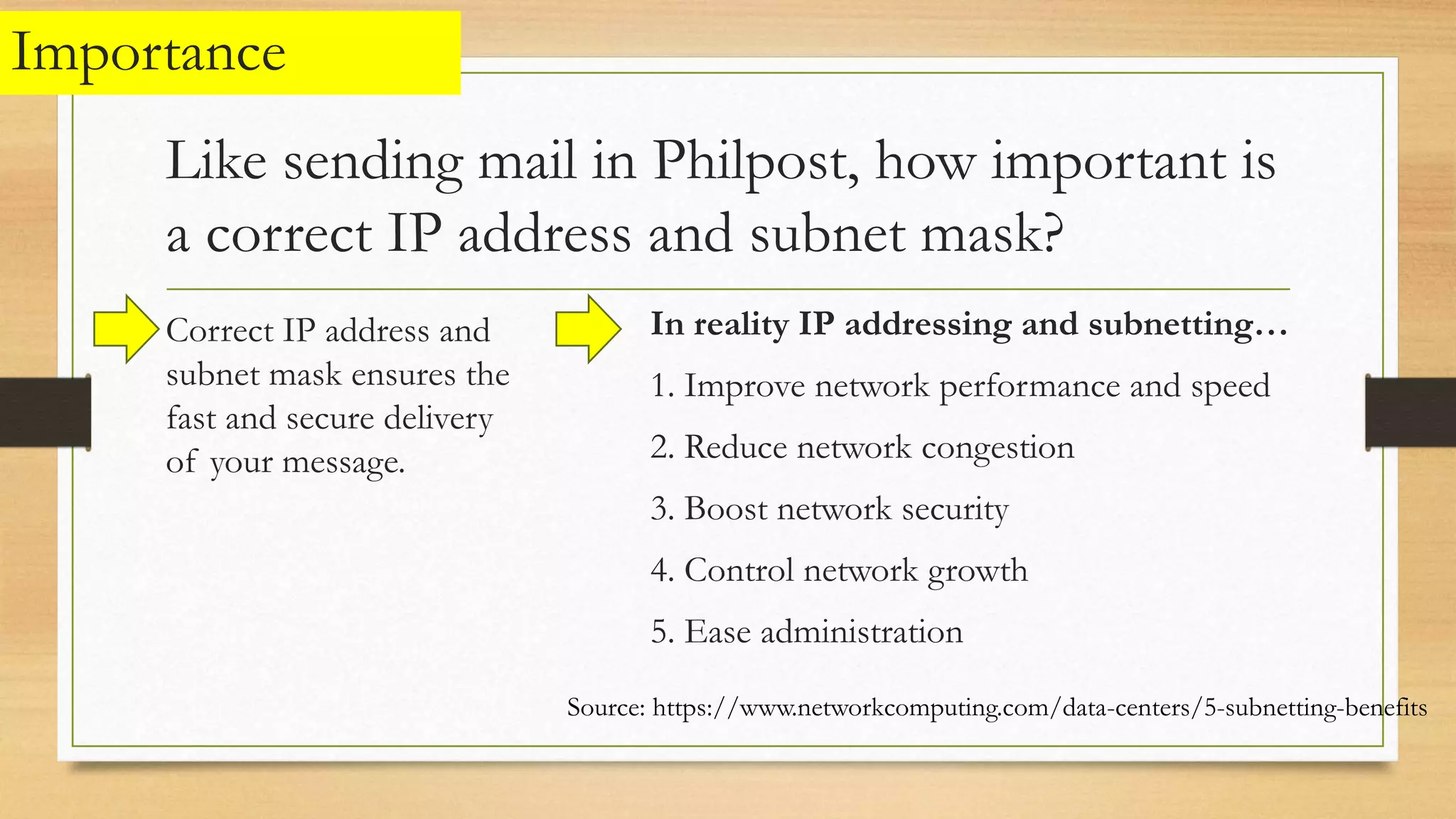
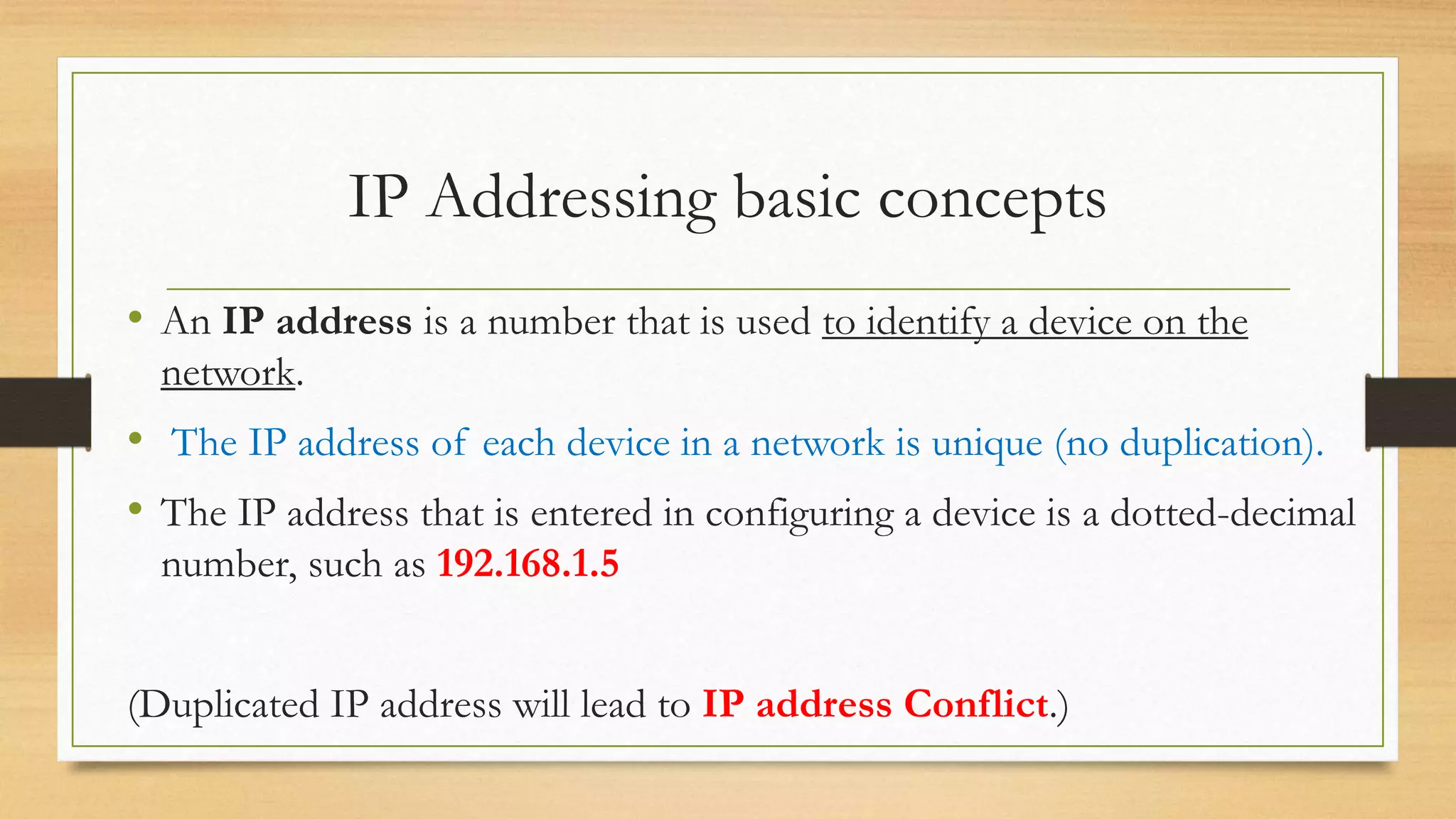
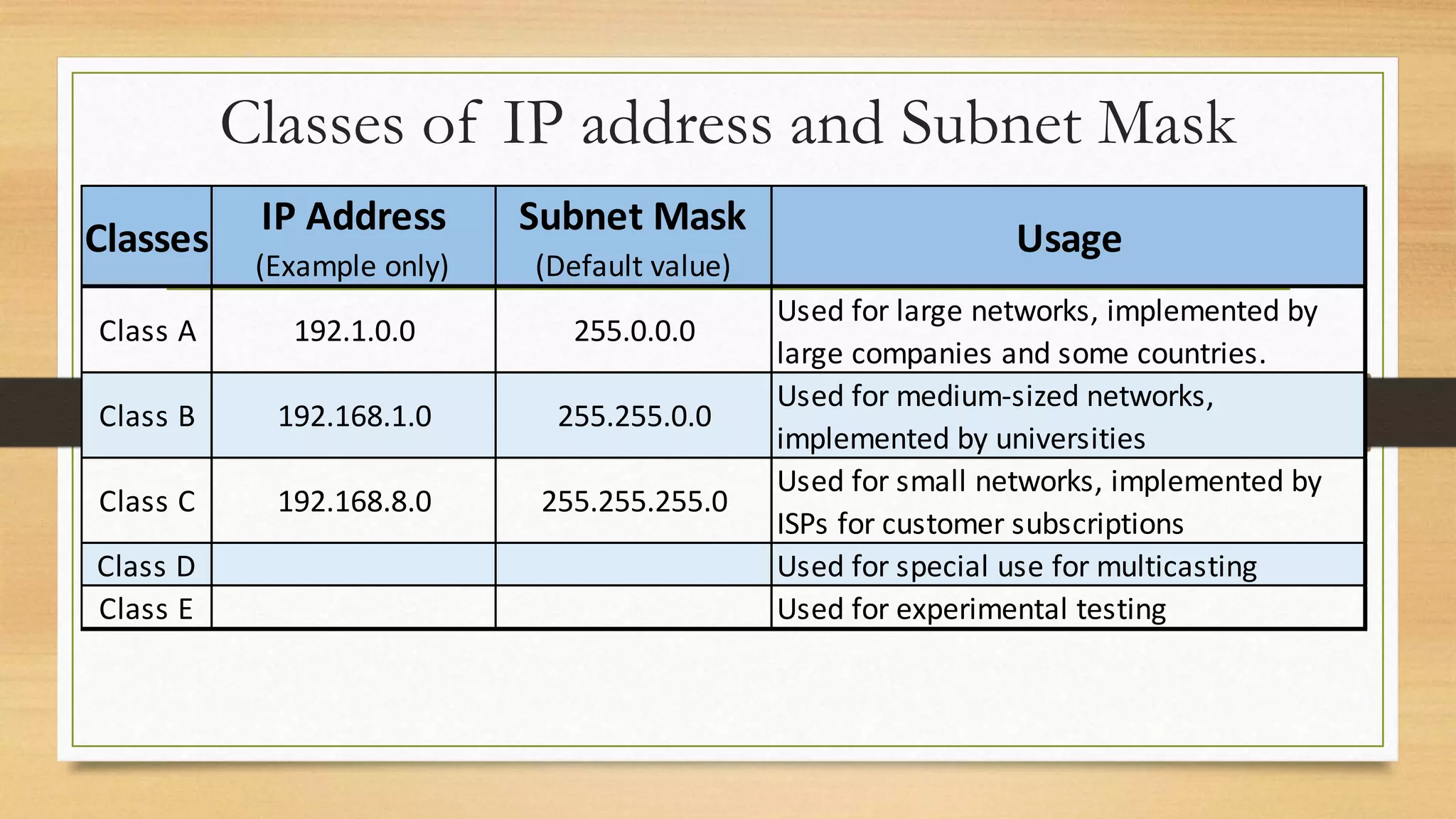
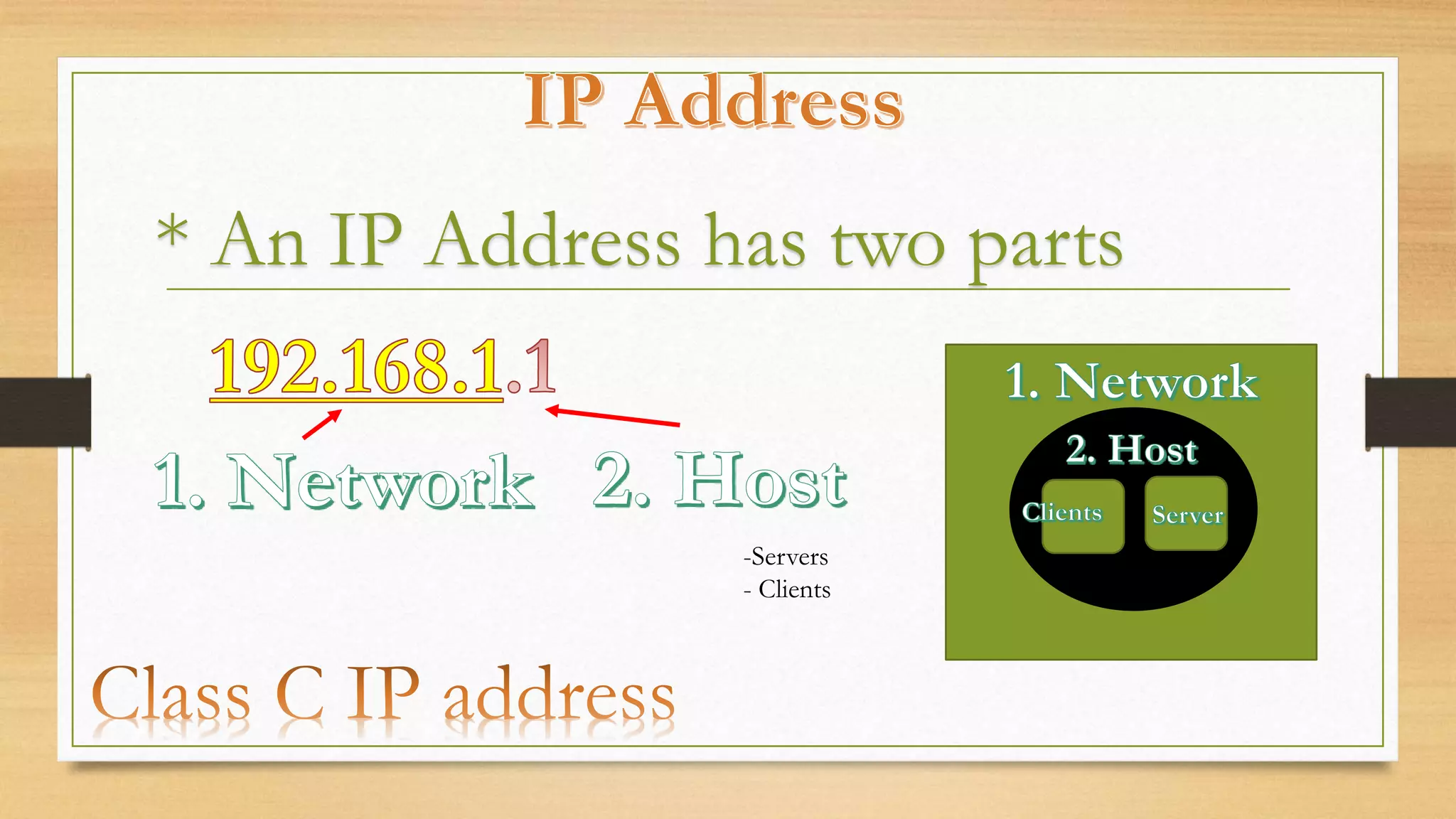
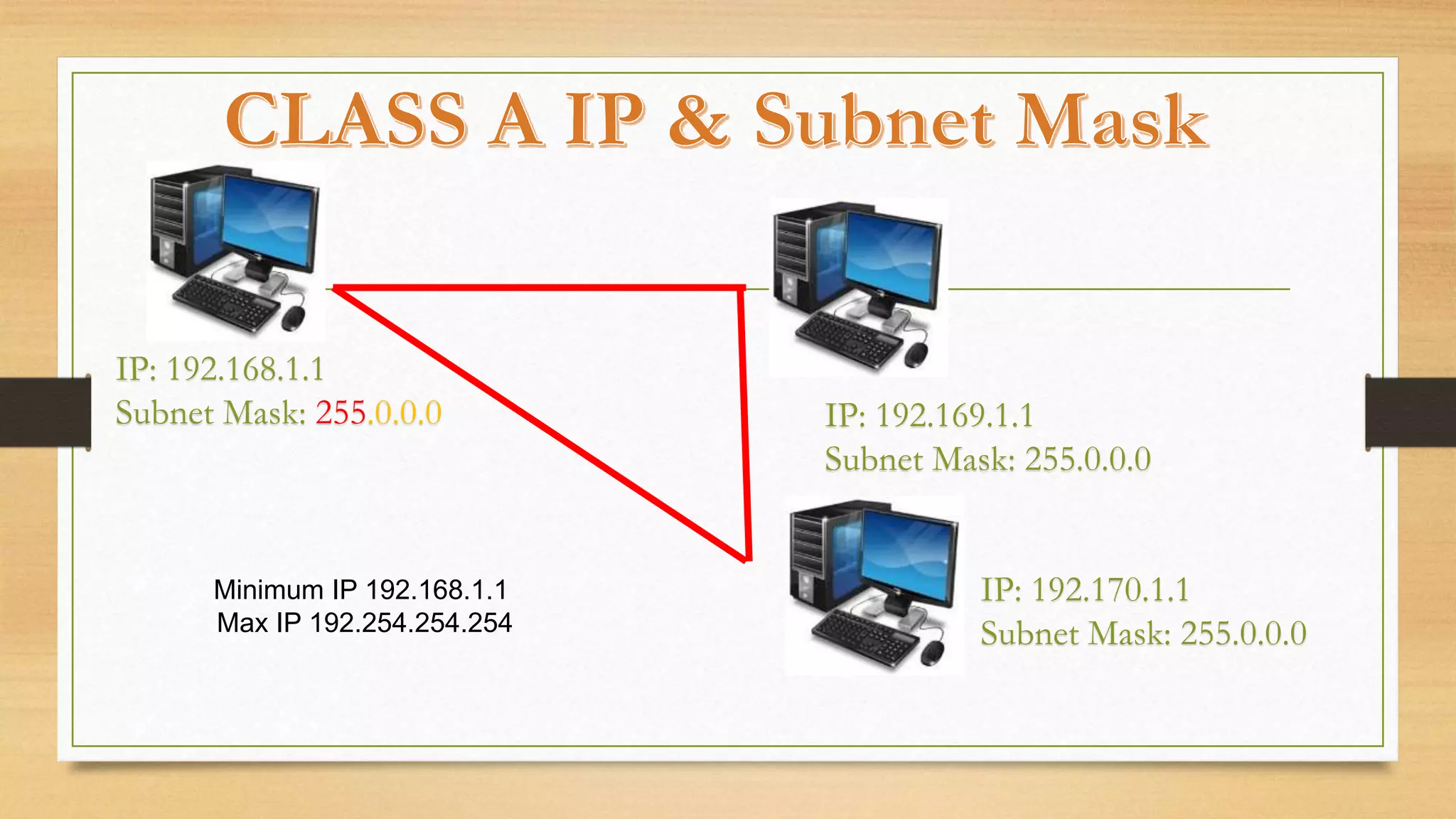
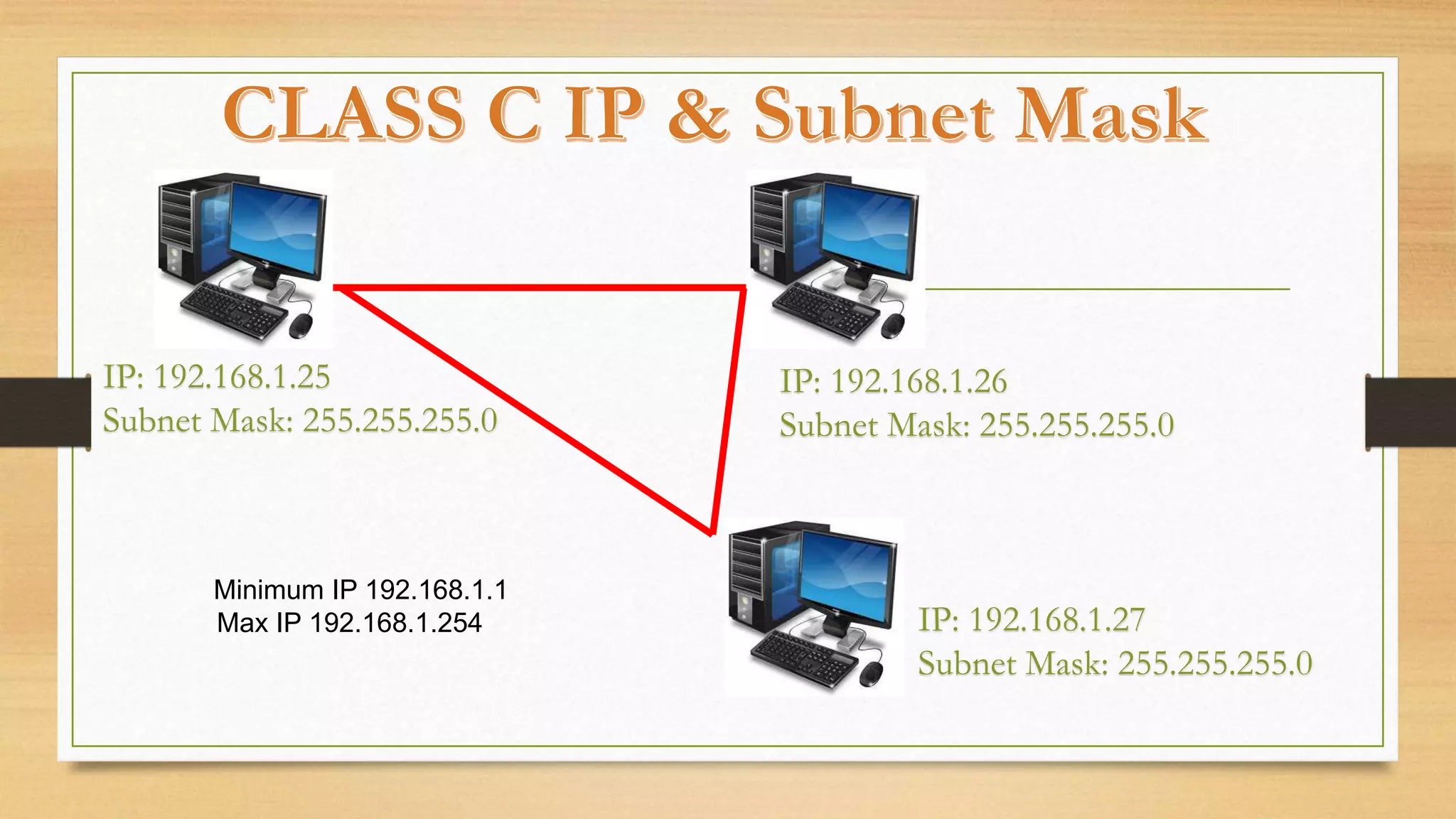
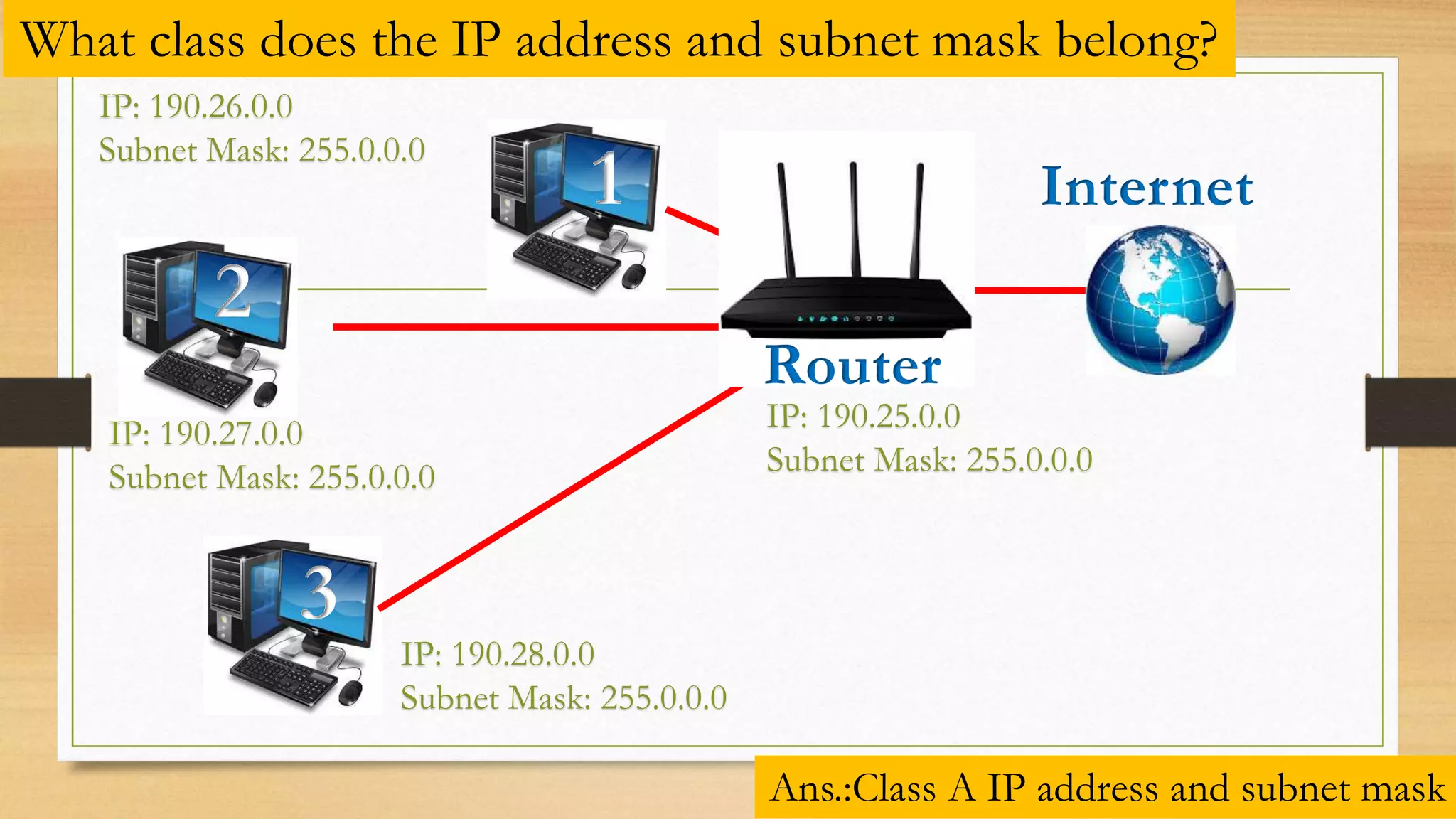
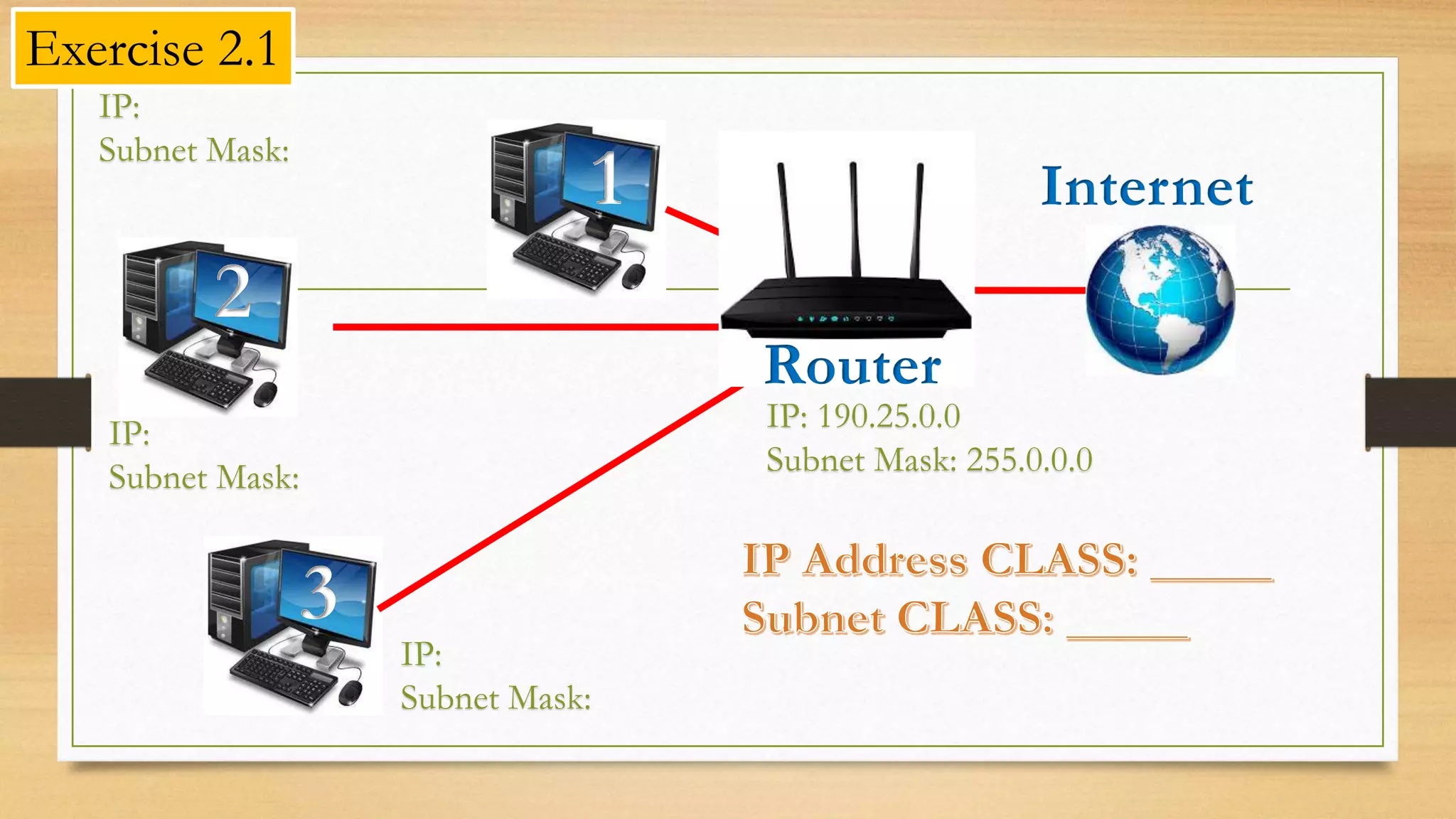
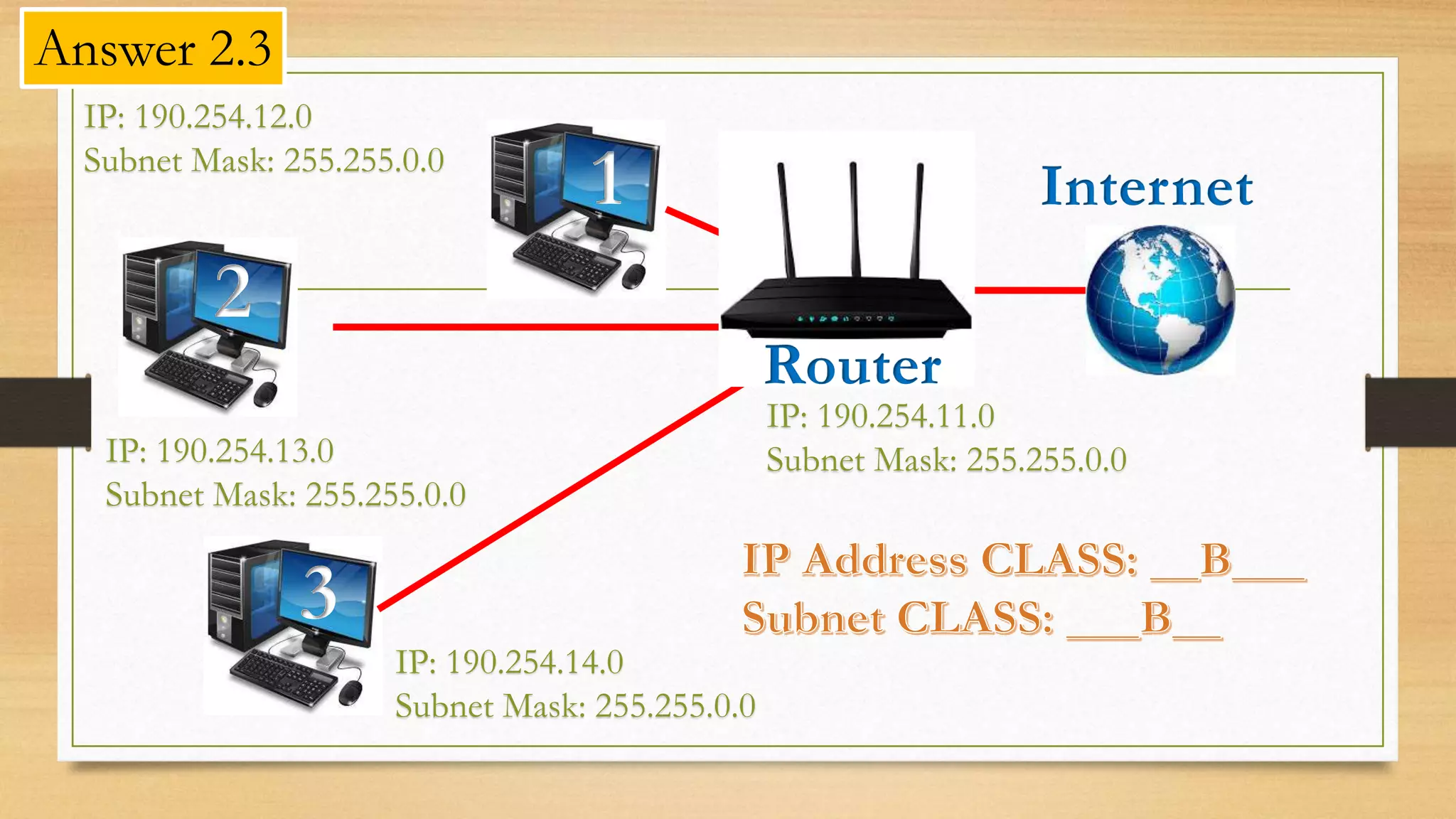
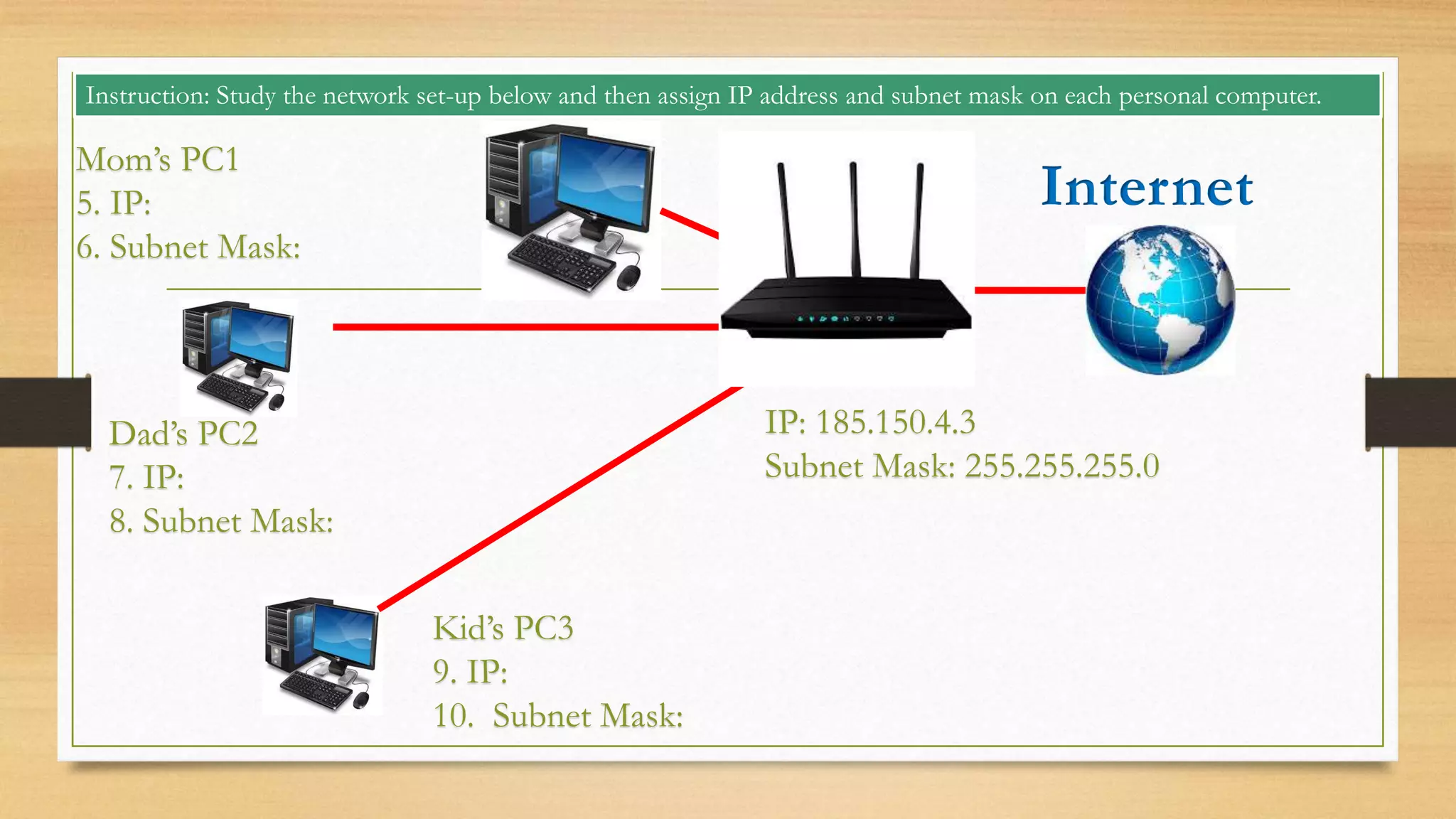
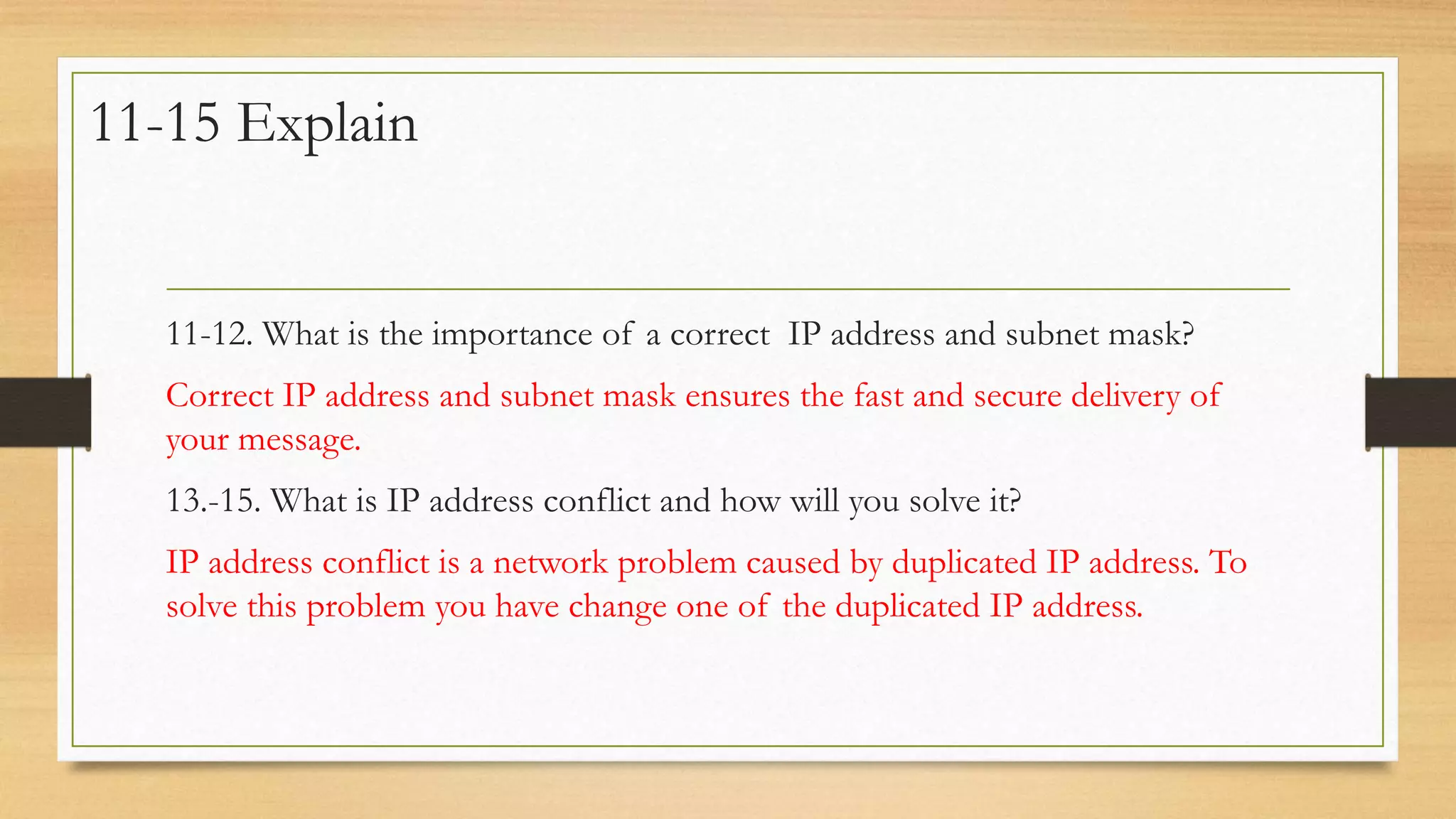
The document discusses IP addressing and subnetting. It defines IP address and subnet mask, and explains their importance for proper network communication. It covers classes of IP addresses and examples of subnet masks. The document also demonstrates how to identify network classes, perform IP addressing and subnetting, and troubleshoot issues like IP address conflicts. Key learning points are defining IP addresses and subnet masks, understanding basic IP addressing concepts, and correctly applying subnetting. Exercises are included to help with skills like assigning IP addresses and solving network problems.