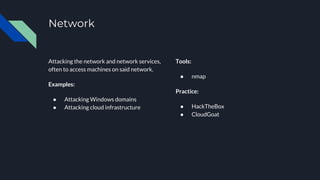
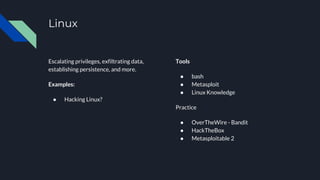
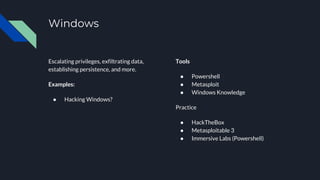
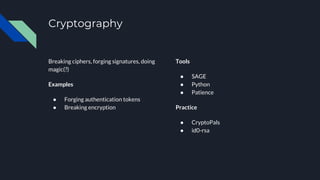
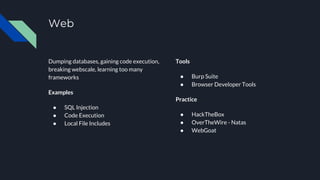
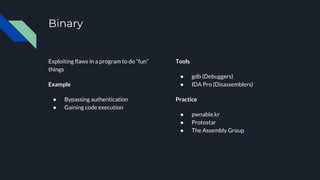
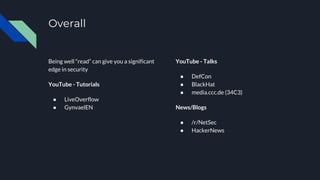
The document provides an introduction to exploitation and offers various resources and tools for getting started in computer security, focusing on different areas such as network, system, web, cryptography, and binary exploitation. It outlines specific tools like Kali Linux, Metasploit, and Burp Suite along with practice platforms like HackTheBox and OverTheWire. The document also lists events, meetings, and online resources for further learning and community engagement.