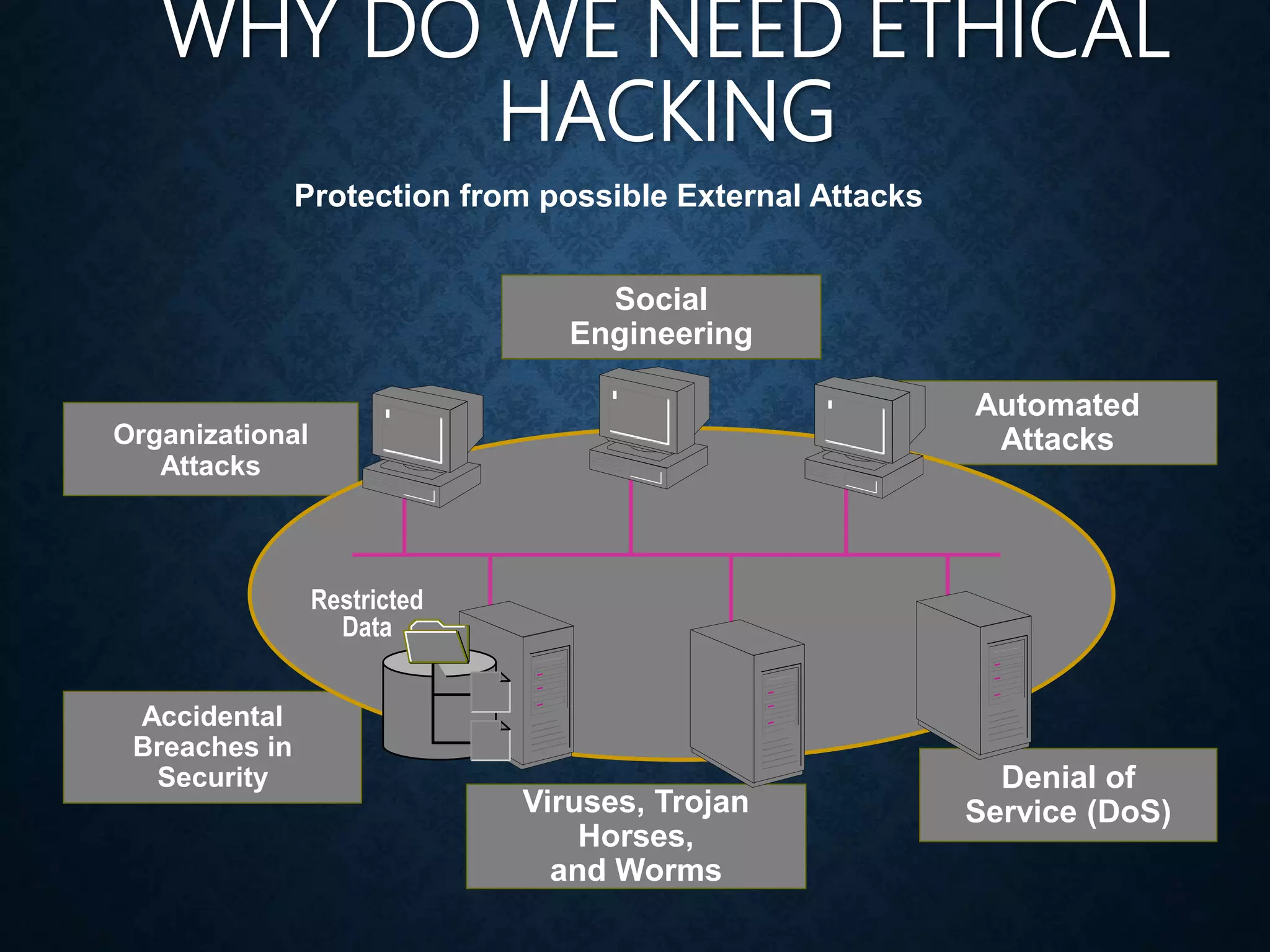
This document discusses ethical hacking and provides an overview of key concepts. It defines ethical hacking as legally breaking into computer systems to test defenses without damaging systems or stealing information. It describes different types of hackers including black hat, white hat, and grey hat hackers. The document outlines the hacking process and required skills of an ethical hacker such as knowledge of operating systems, firewalls, and networking protocols. It discusses why ethical hacking is important to protect against external attacks and close security vulnerabilities.