Embed presentation
Download as PDF, PPTX




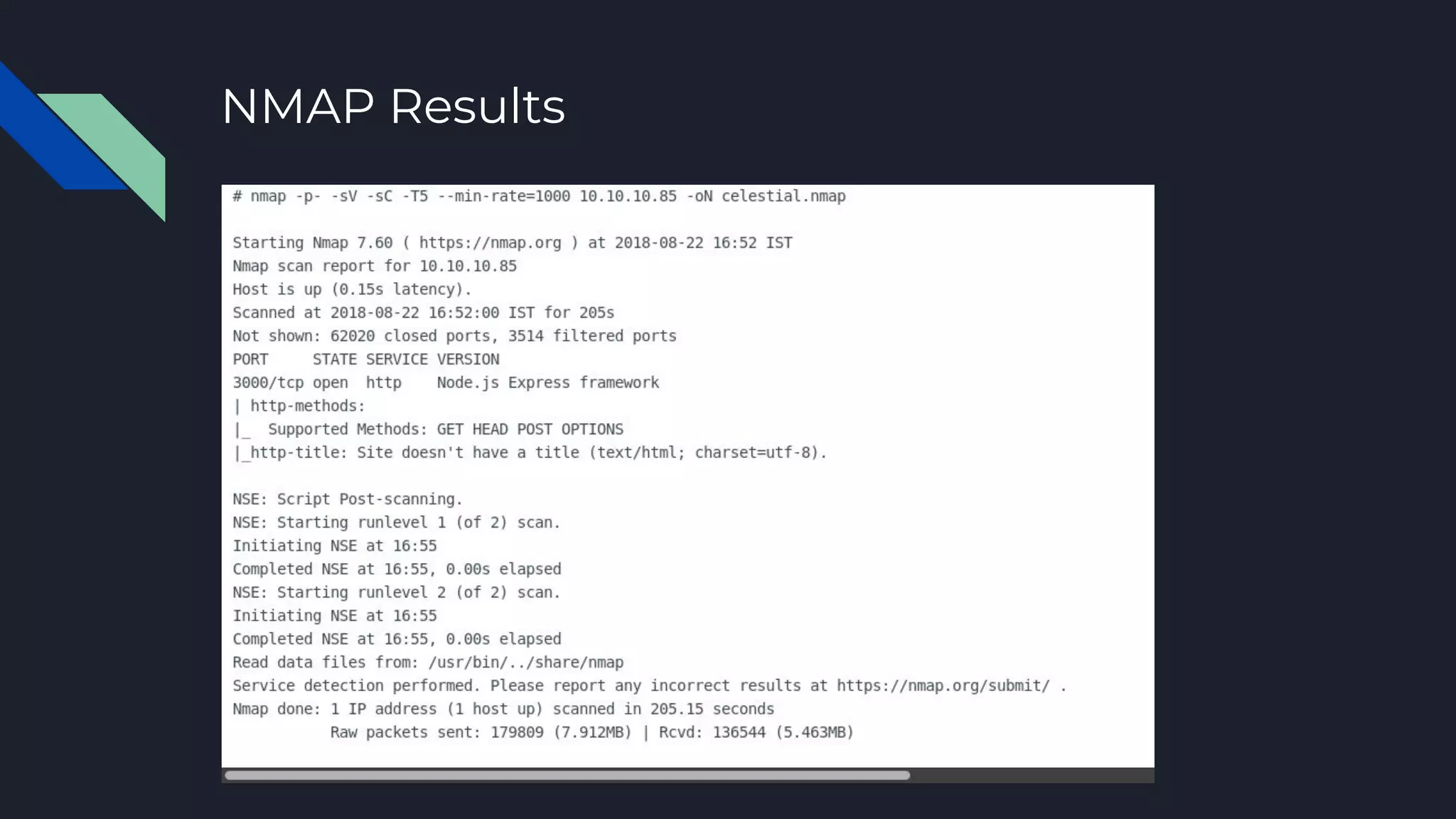




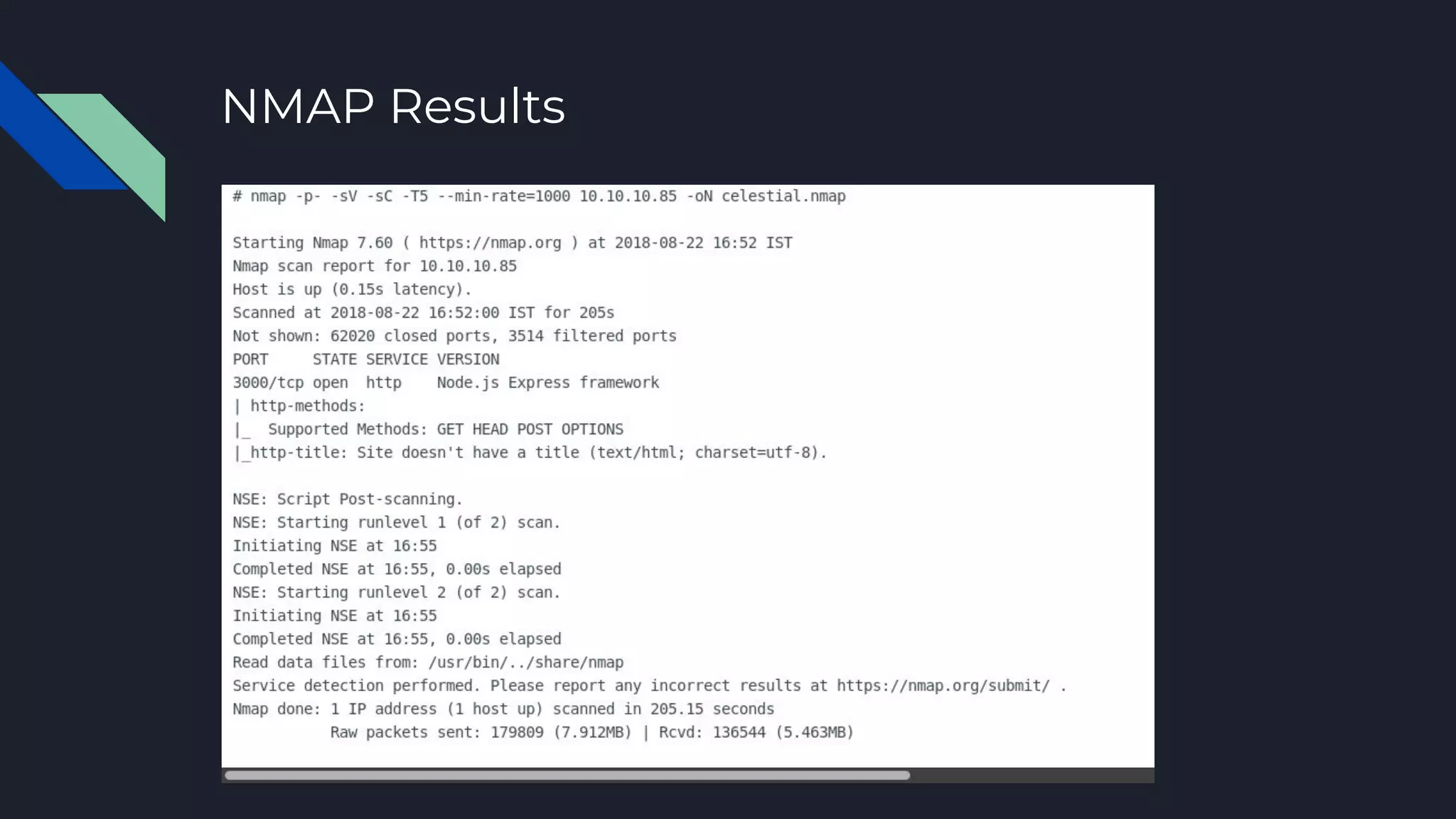
1. The document discusses the steps of a penetration test against a target machine called Celestial on the Hack the Box platform. 2. It outlines reconnaissance, enumeration through Nmap scanning, exploitation to gain initial access, escalation of privileges from user to root, establishing persistence, and clean-up to remove traces of access. 3. The target is an Linux machine at IP 10.10.10.85, and the session will walk through each step of the penetration test process.