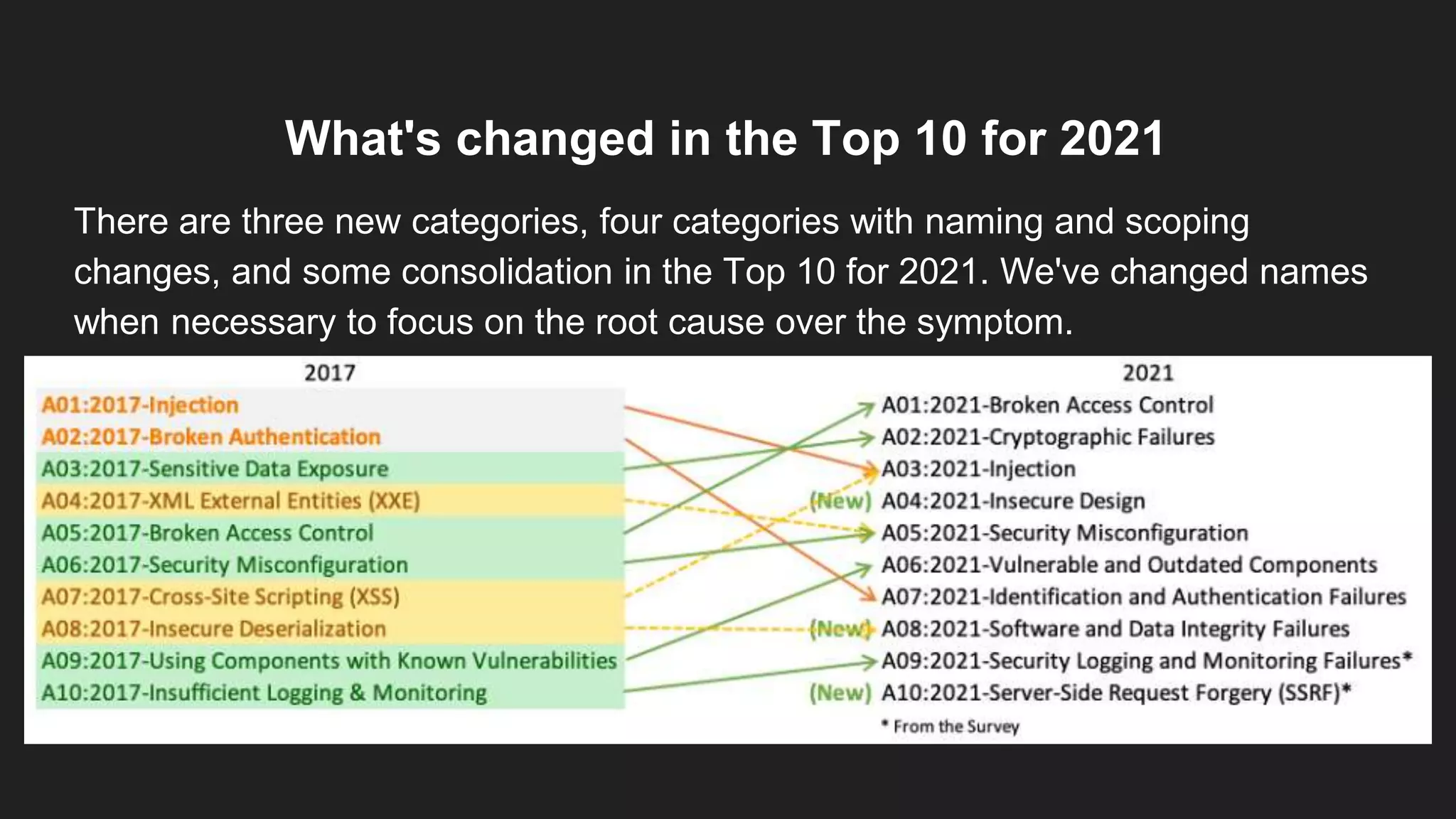
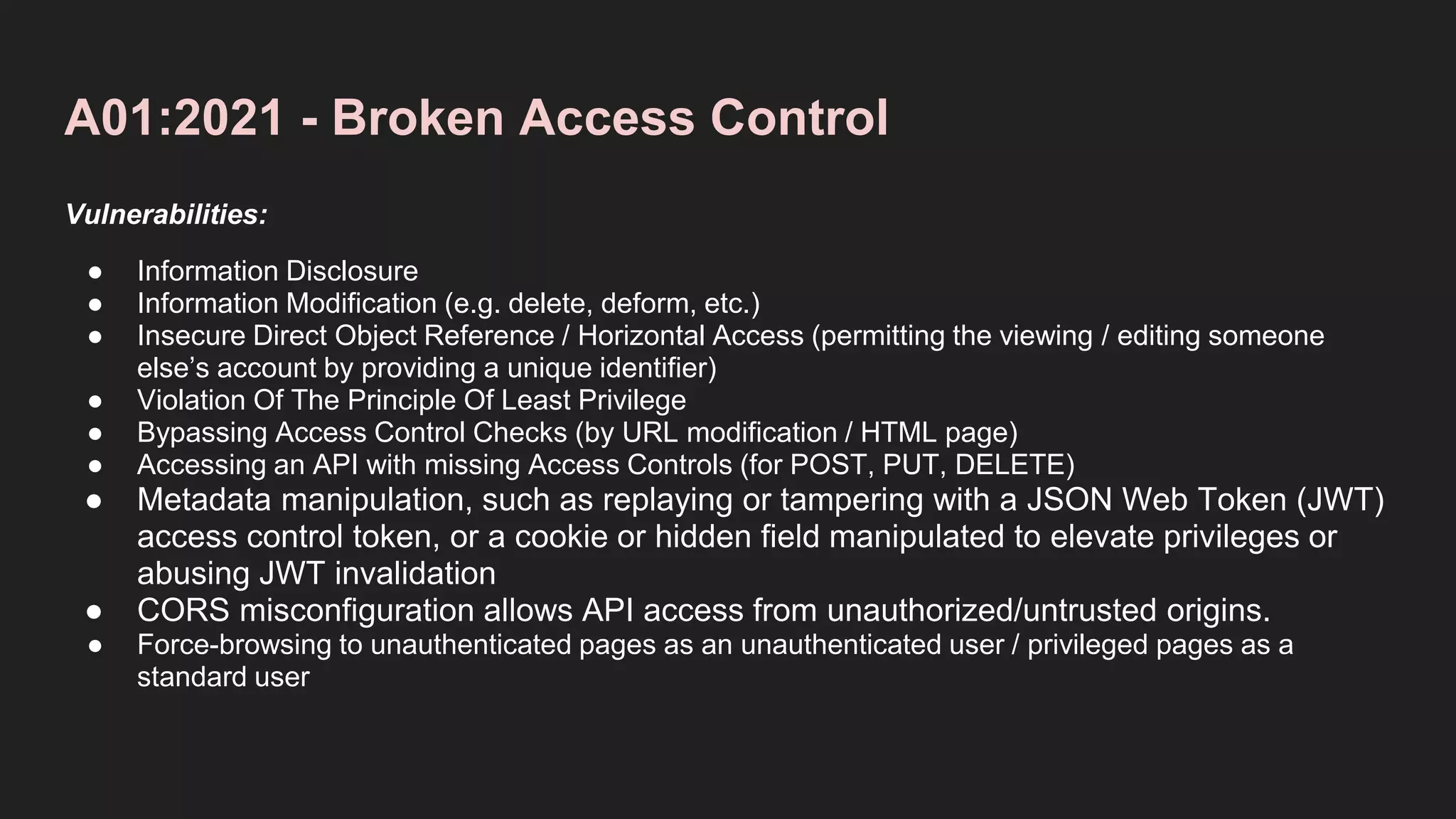
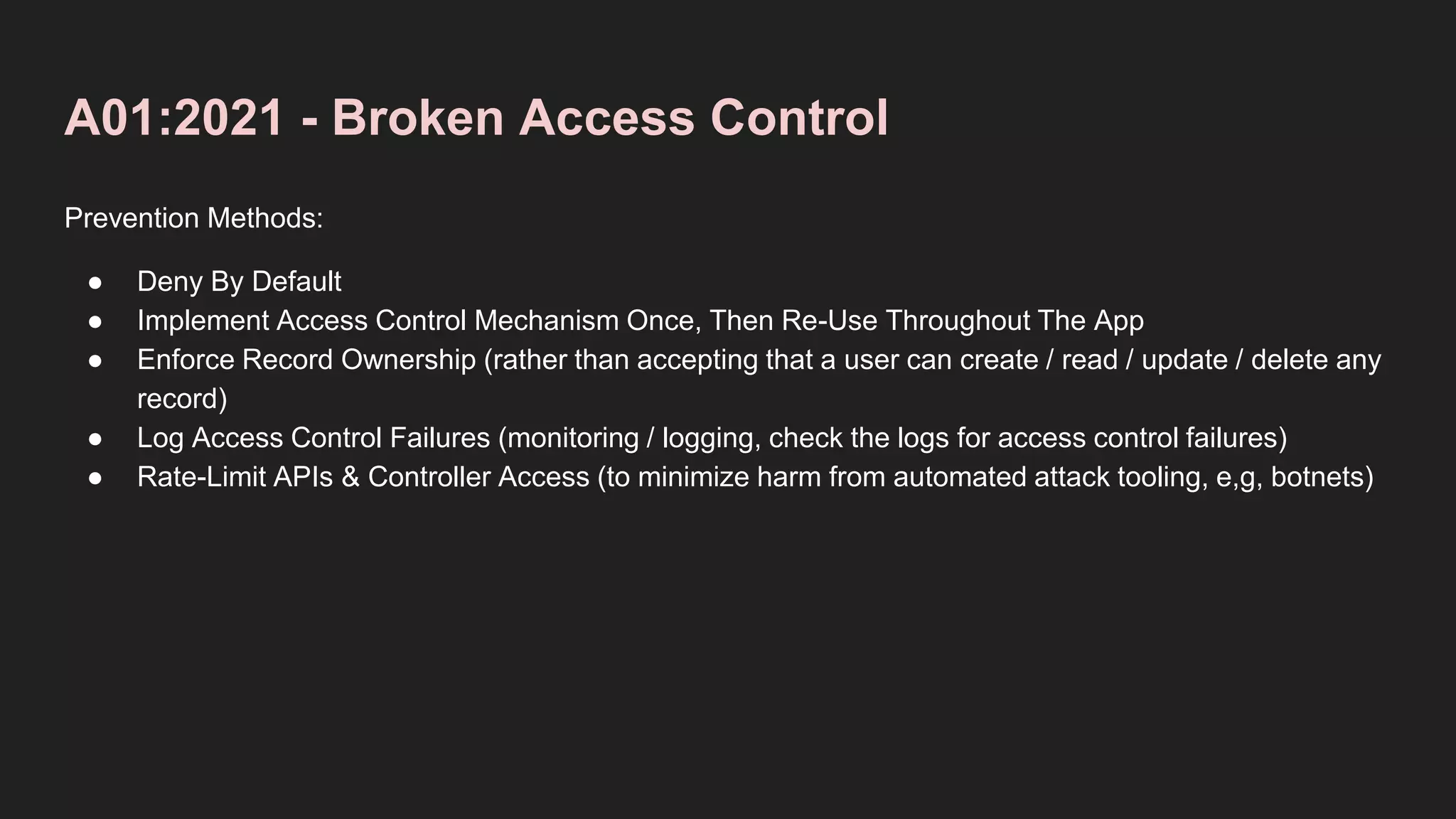
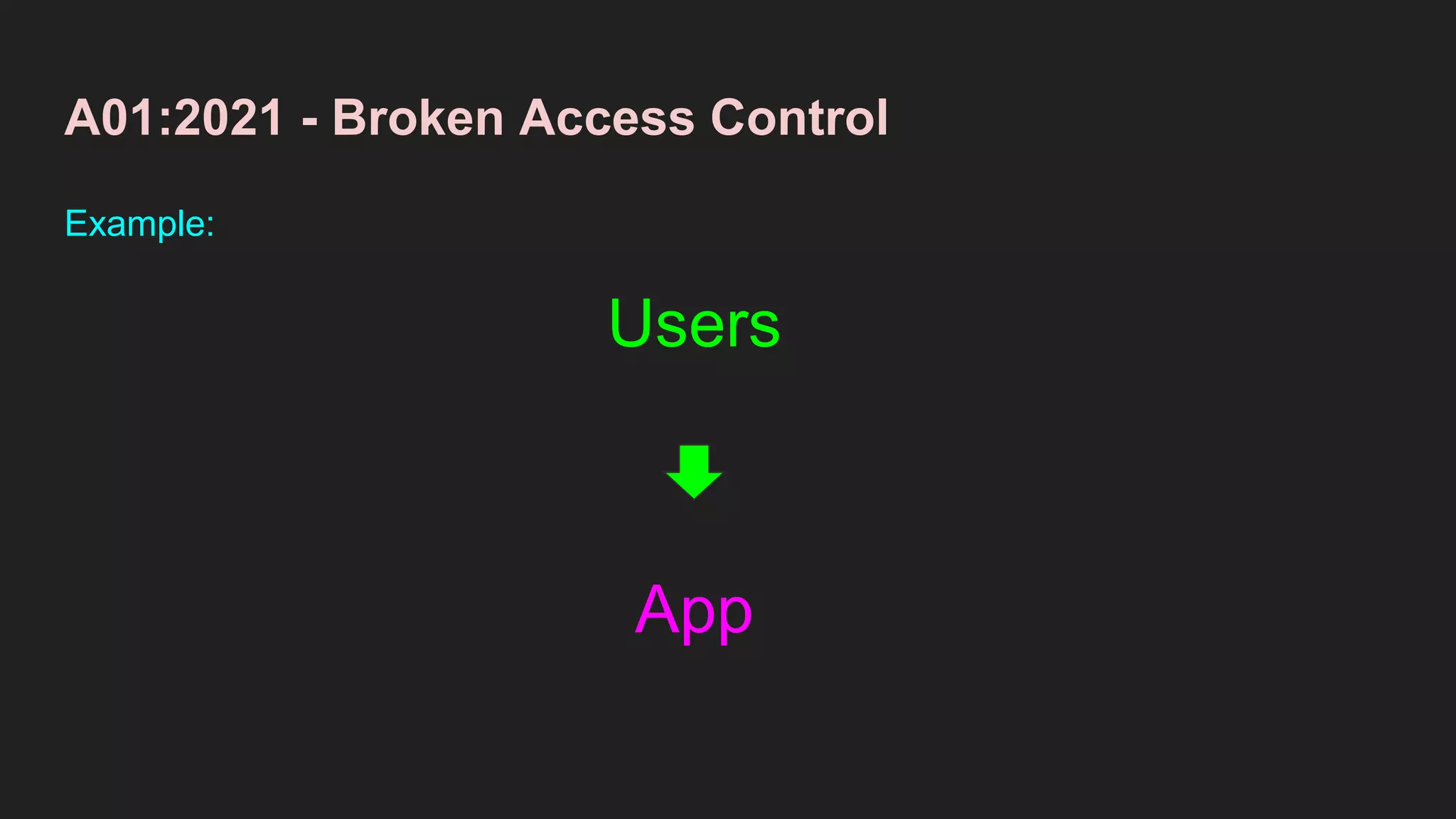
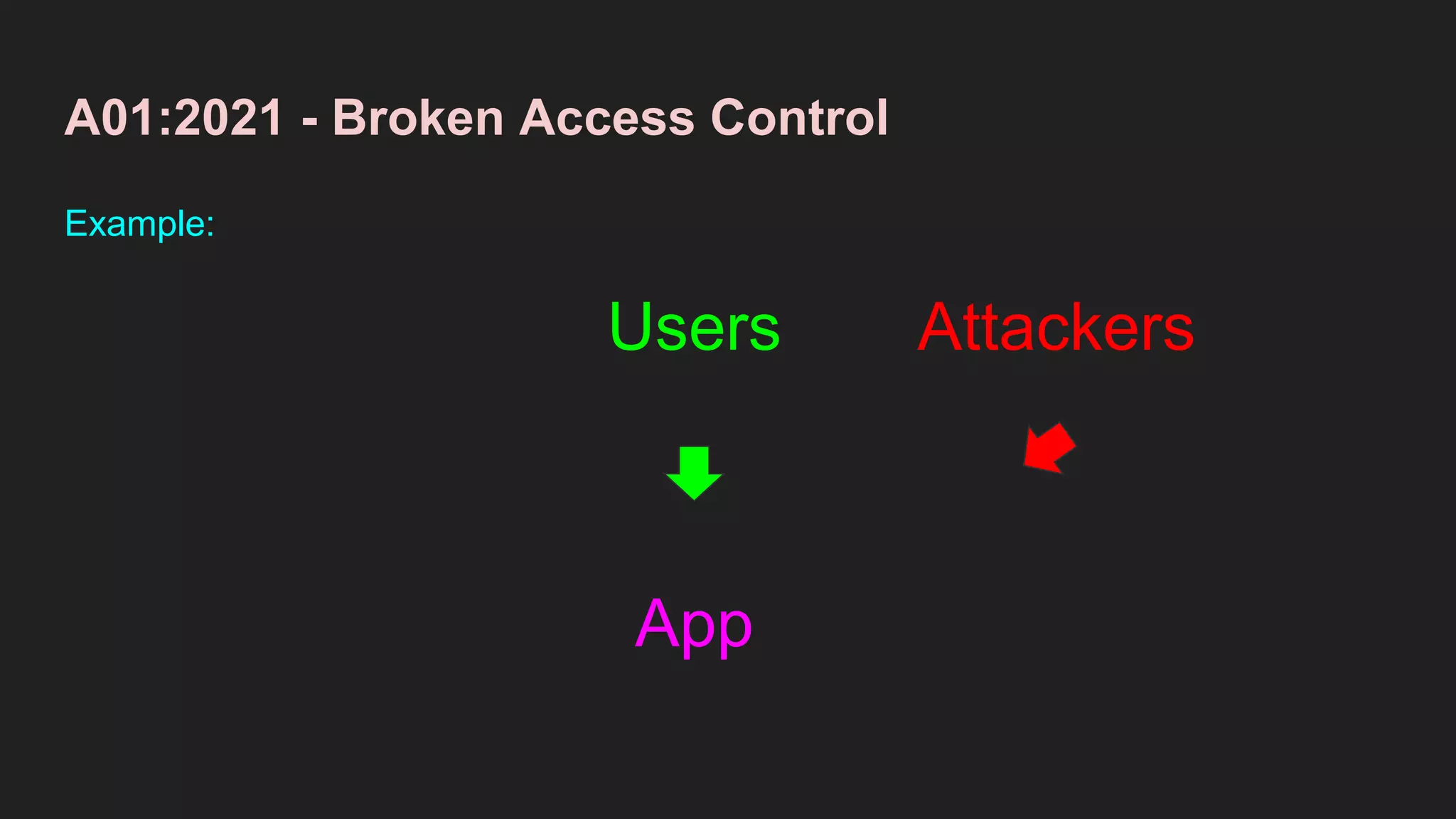
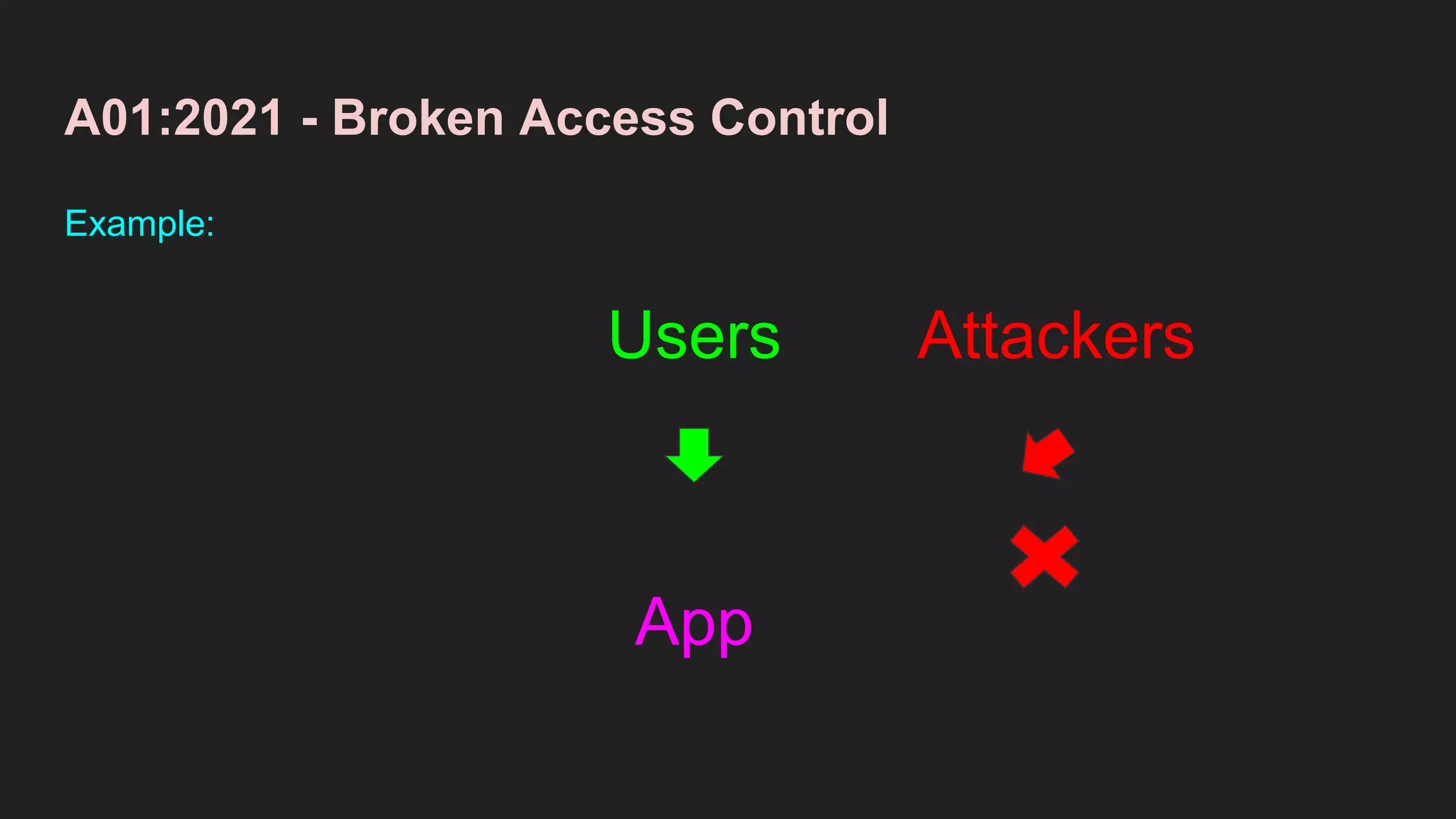
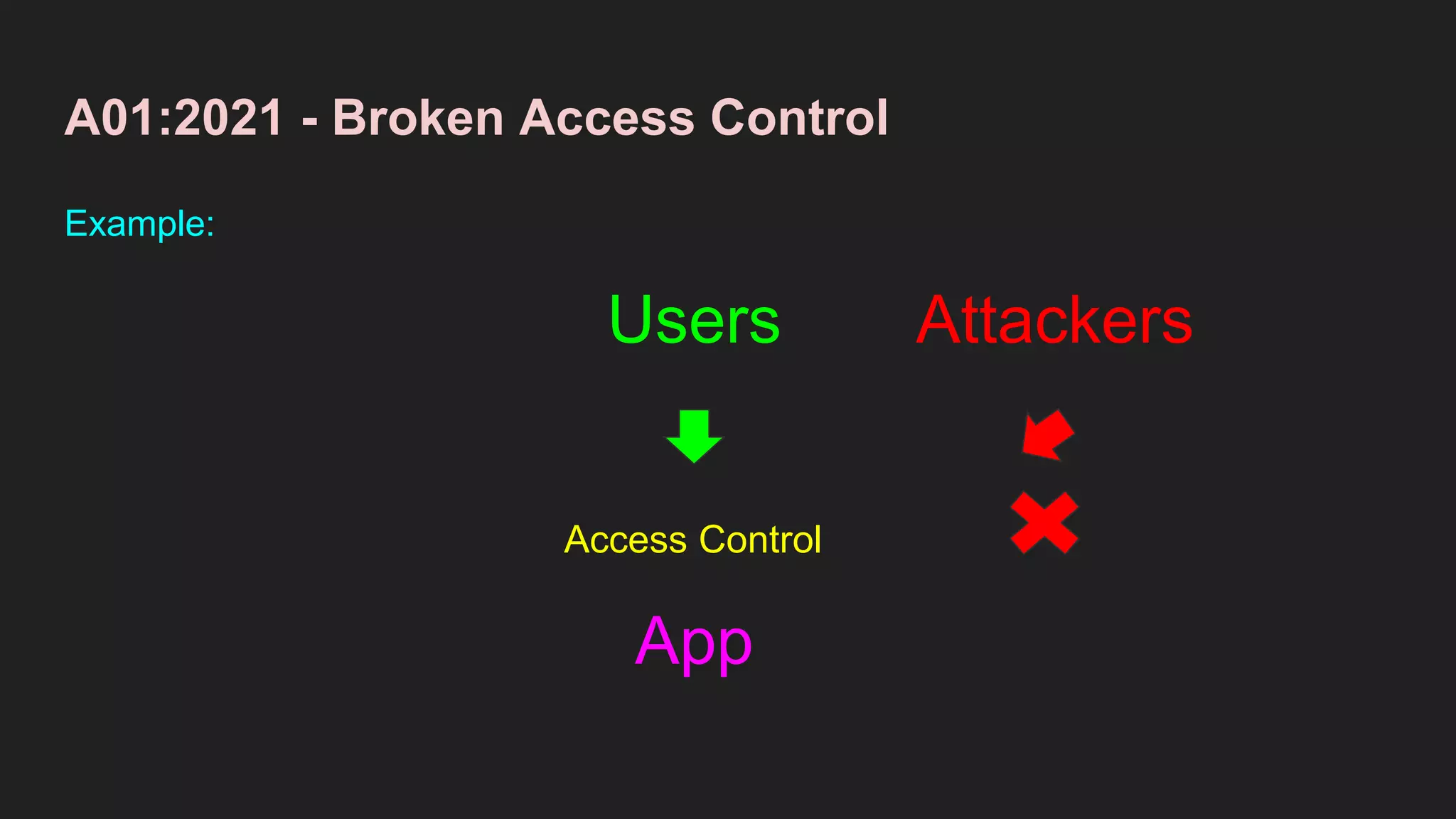
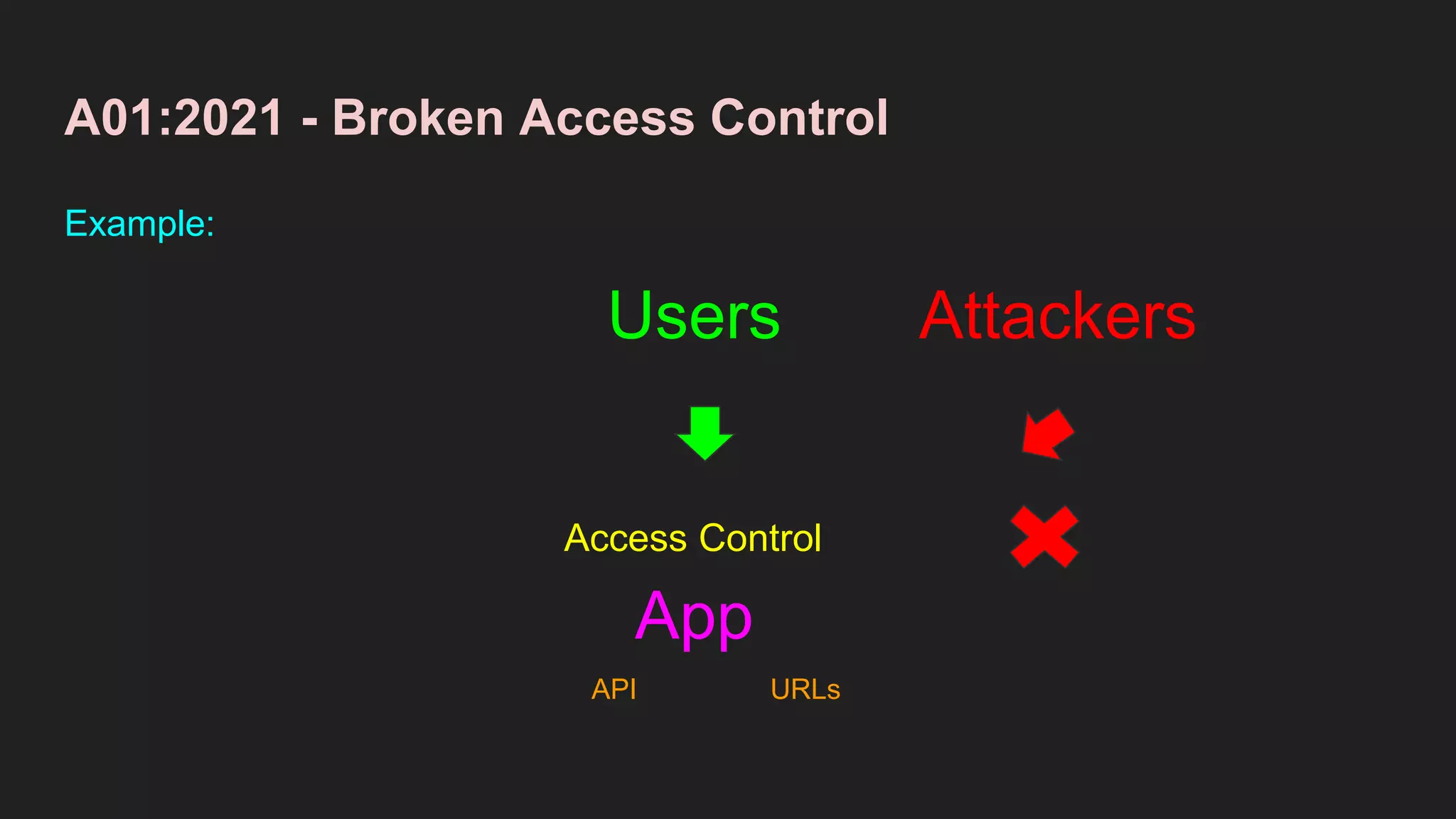
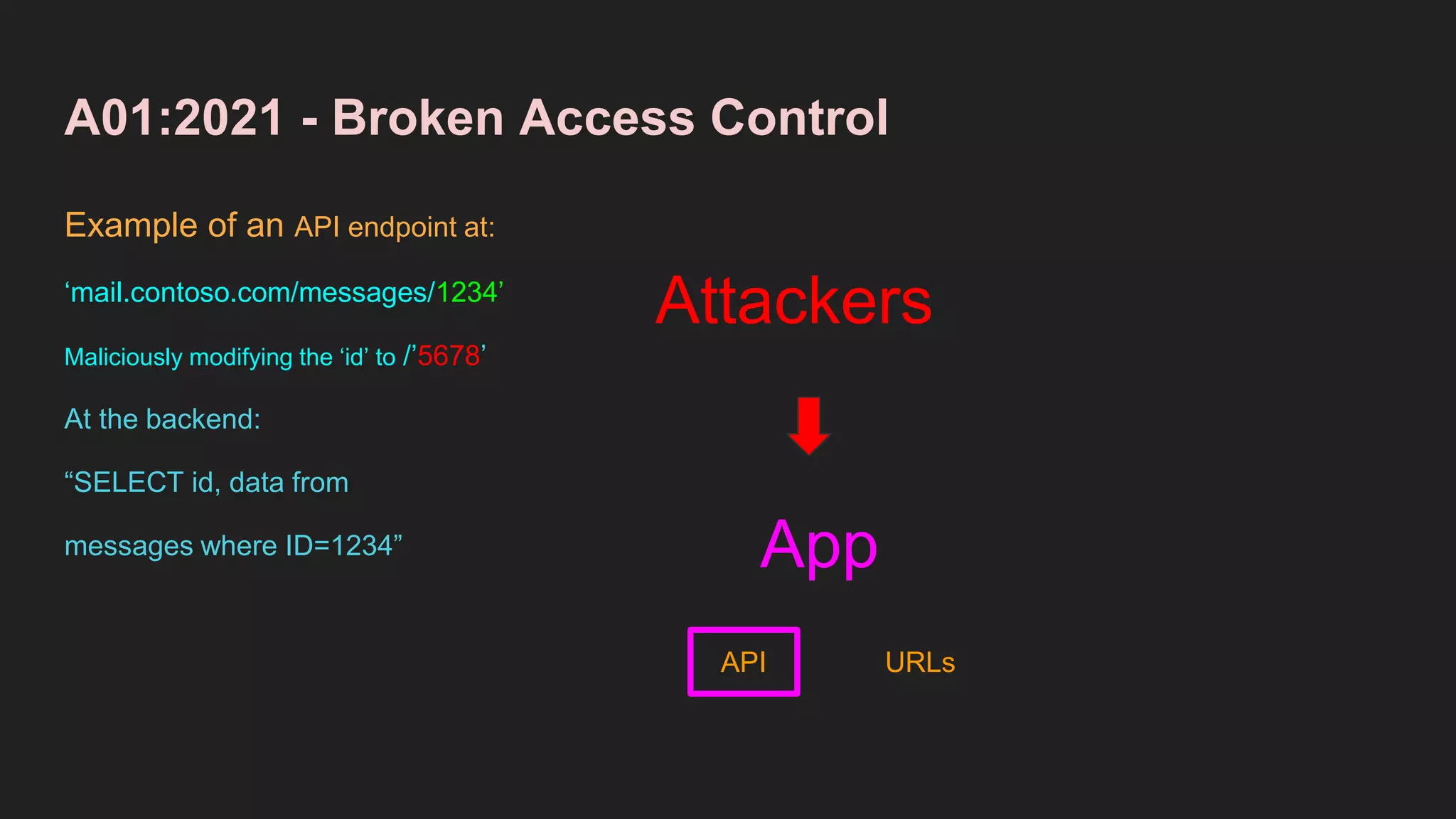
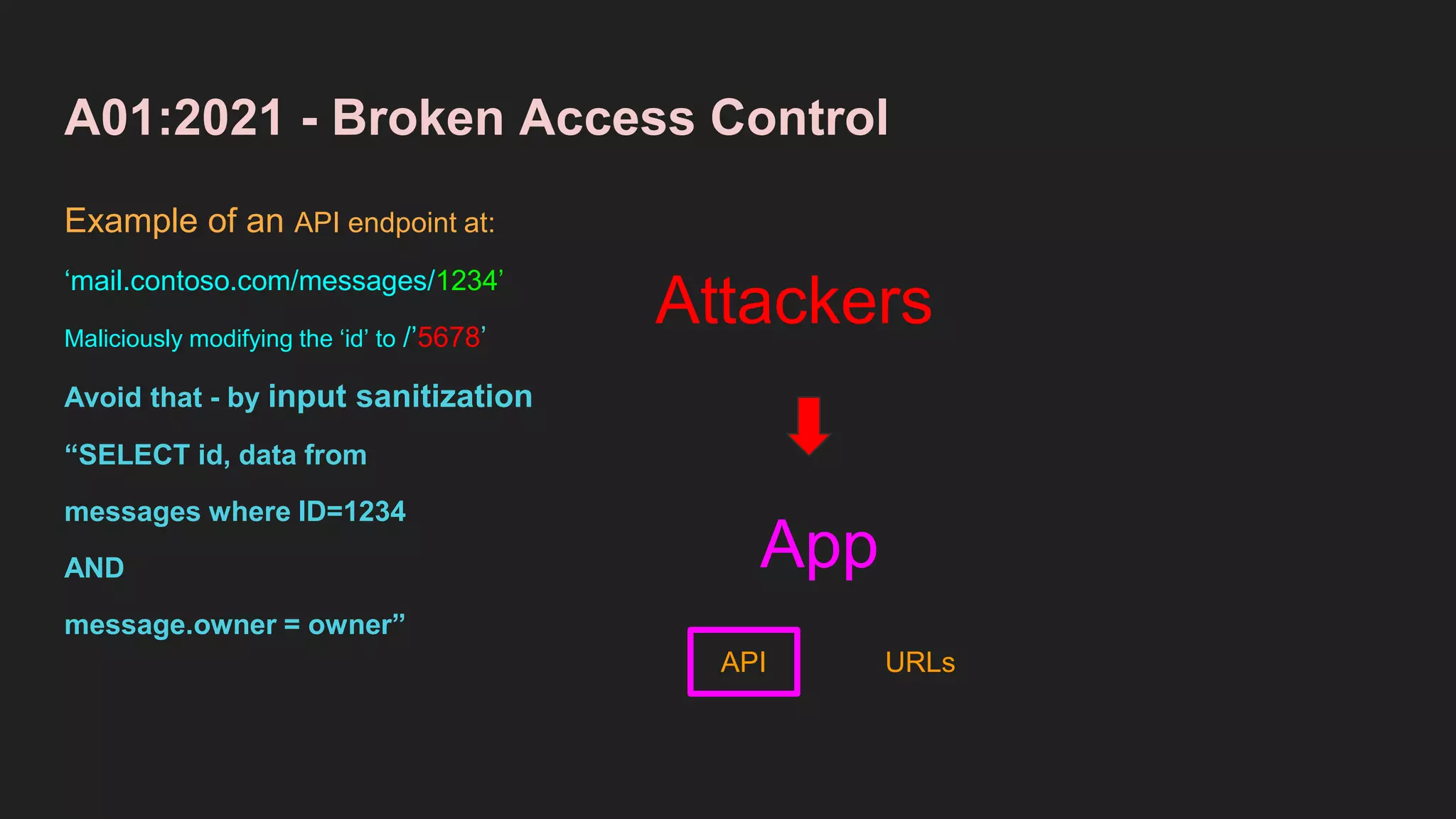
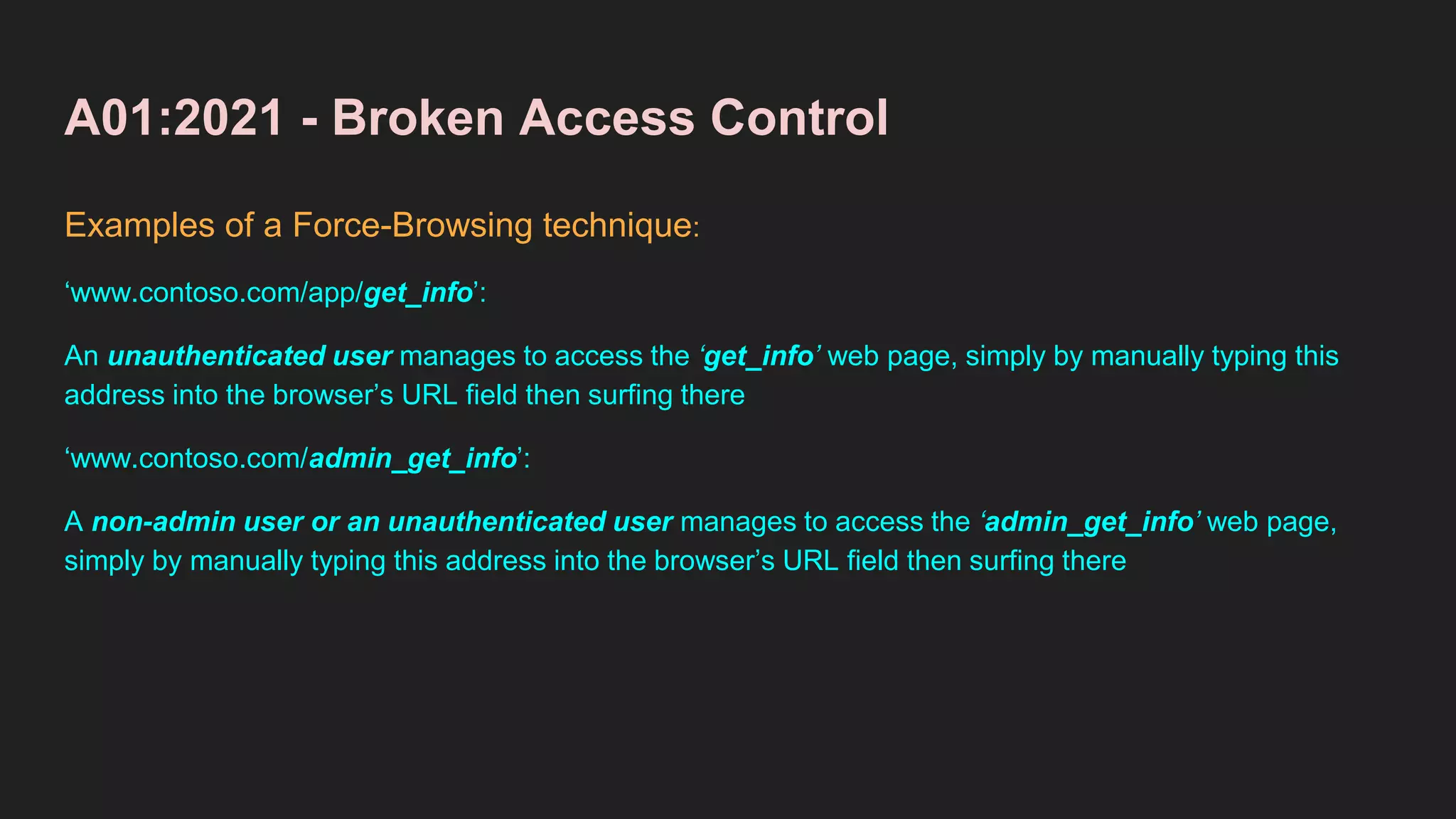
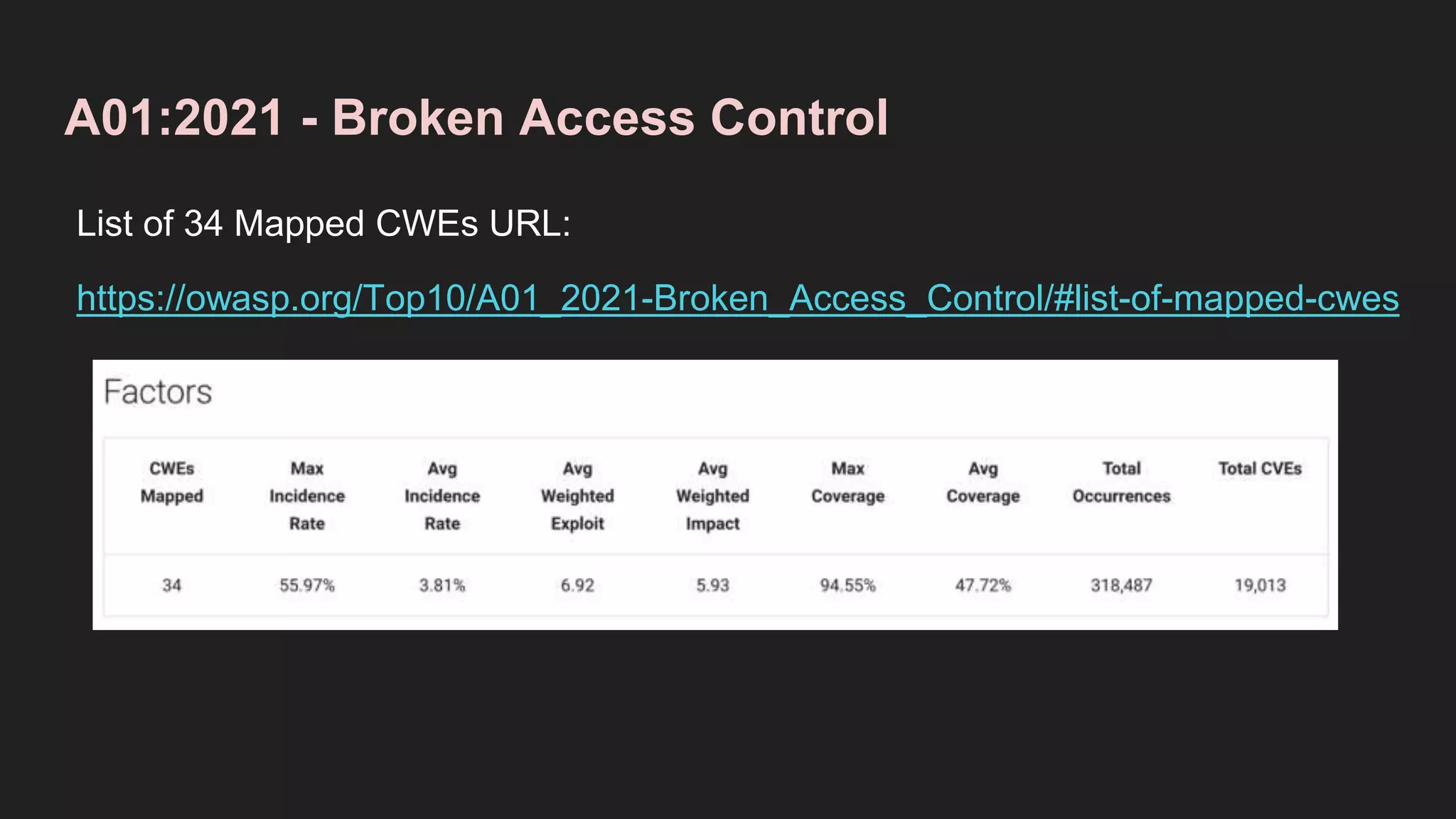
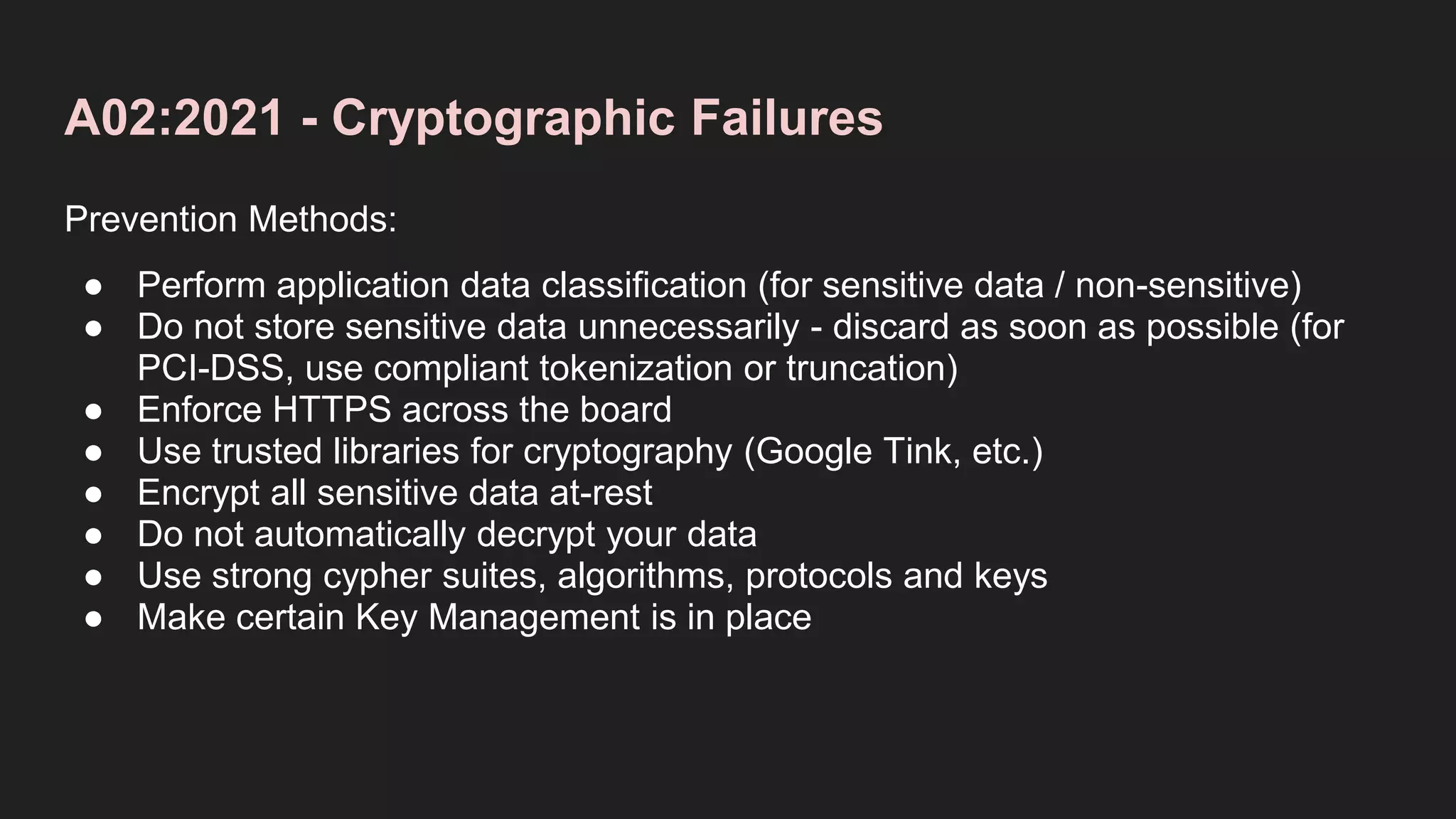
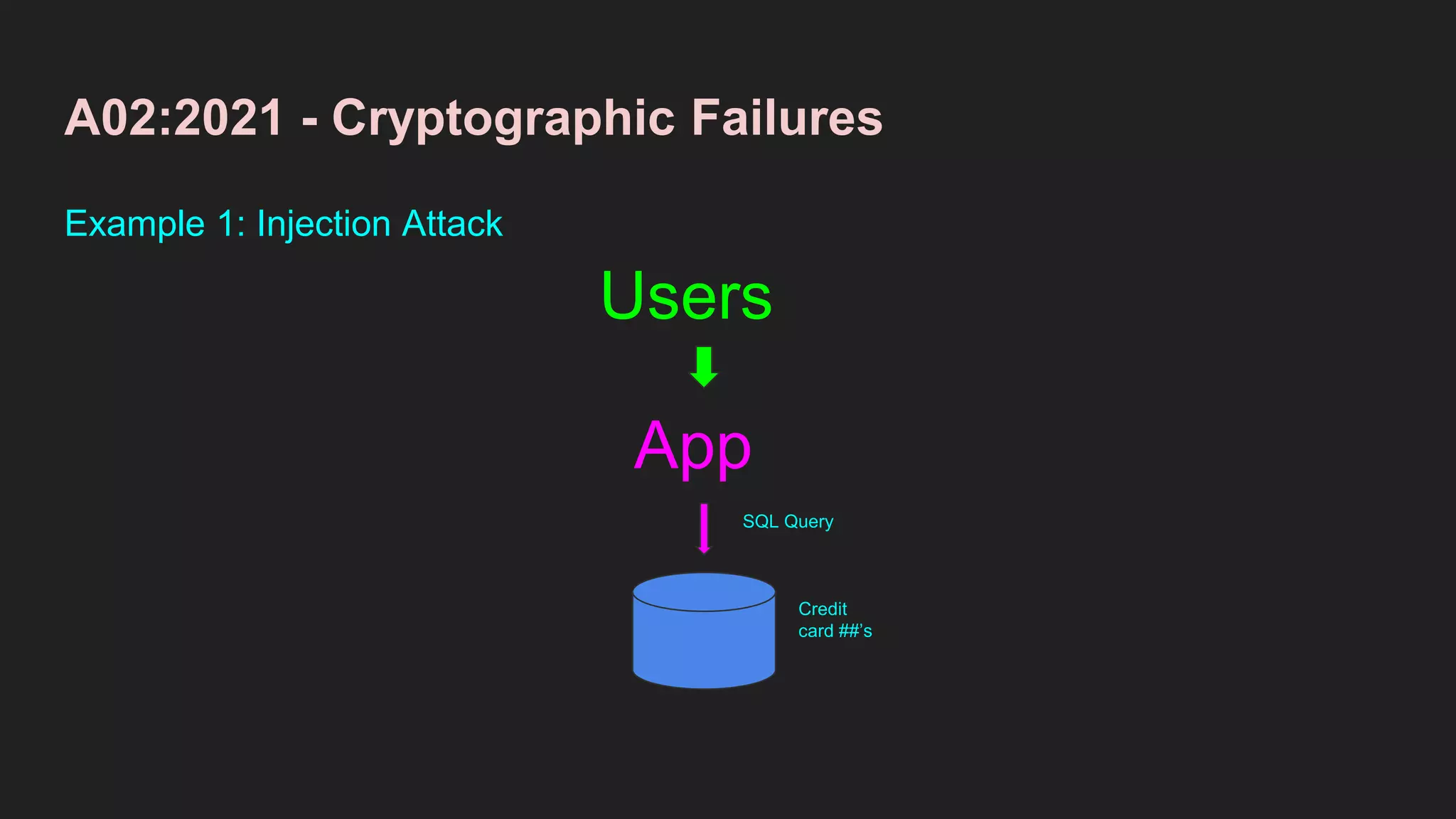
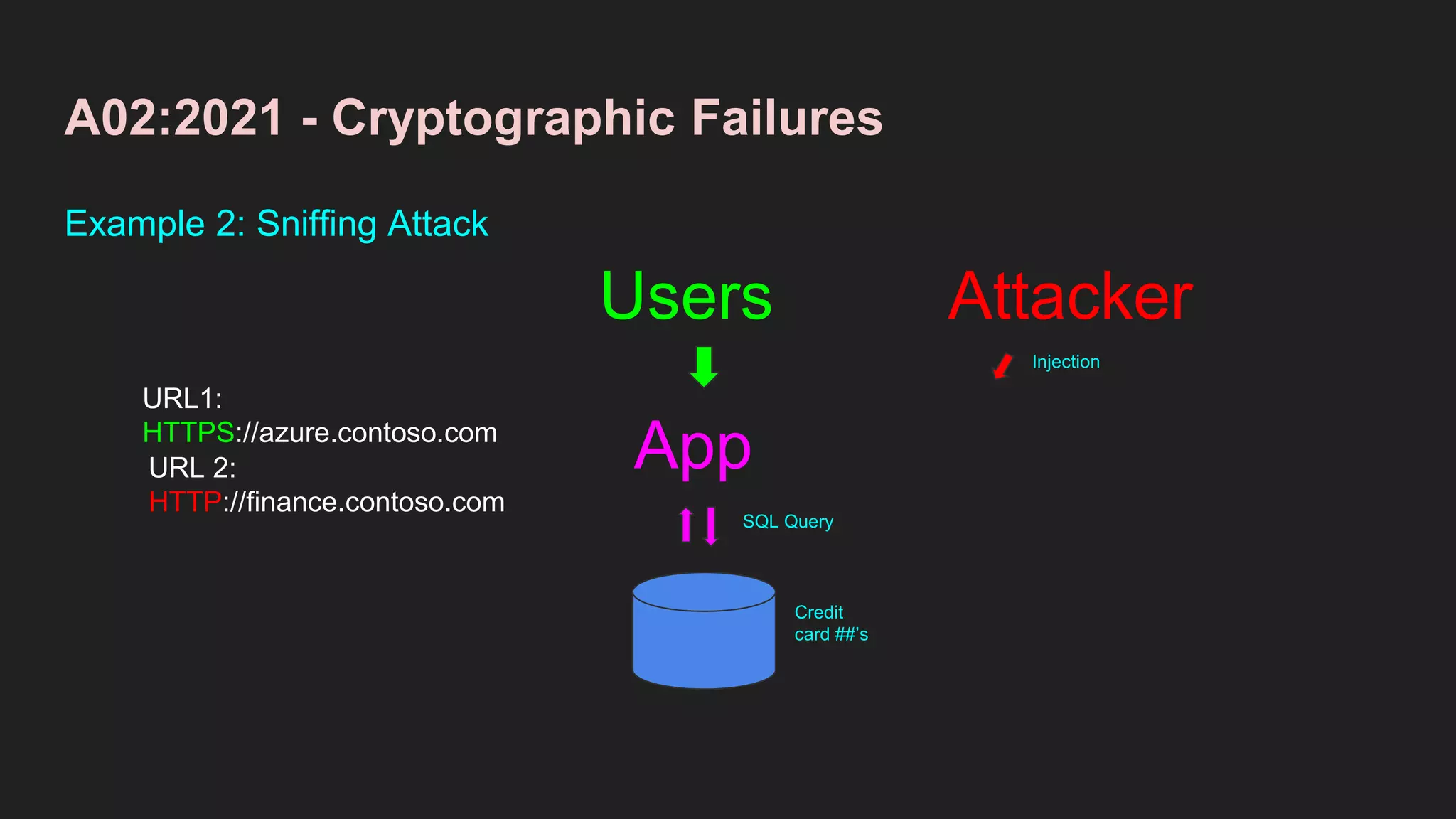
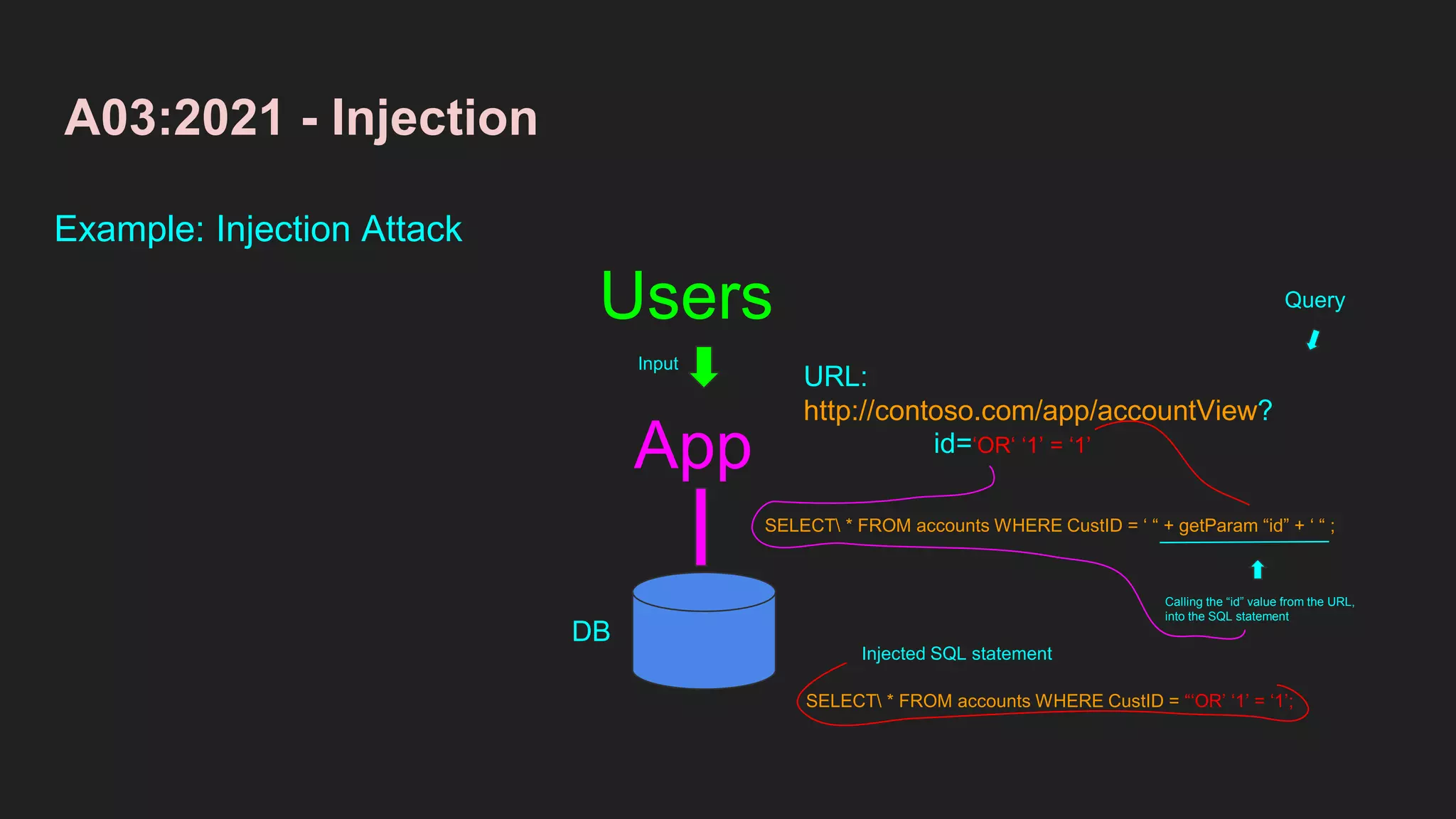
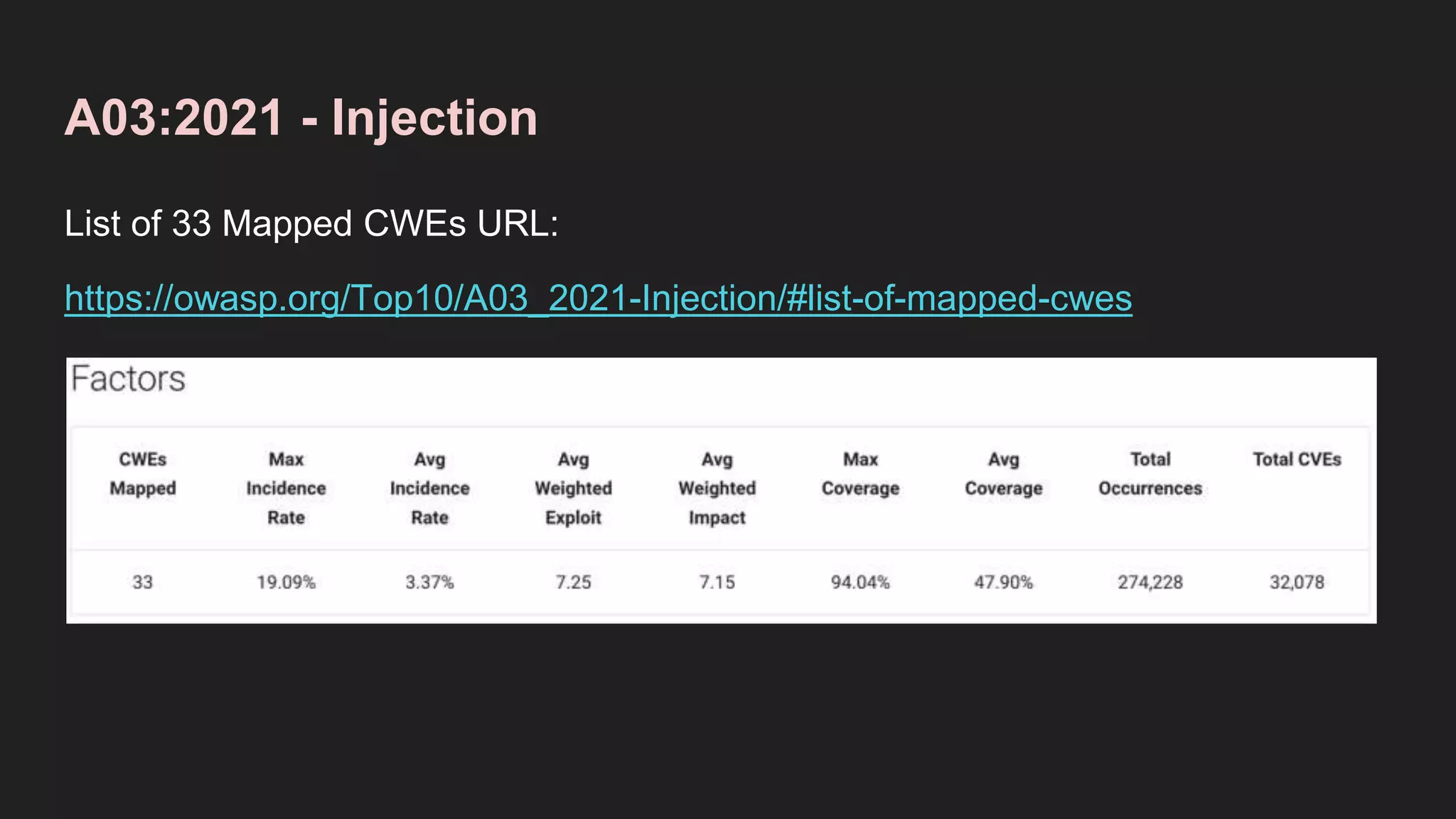
The document provides information about the OWASP Top 10 2021 list of web application security risks. It describes the top risk, A01: Broken Access Control, giving its definition, examples of vulnerabilities it can enable, prevention methods, and examples. It also summarizes the second and third top risks, A02: Cryptographic Failures and A03: Injection, in a similar manner.