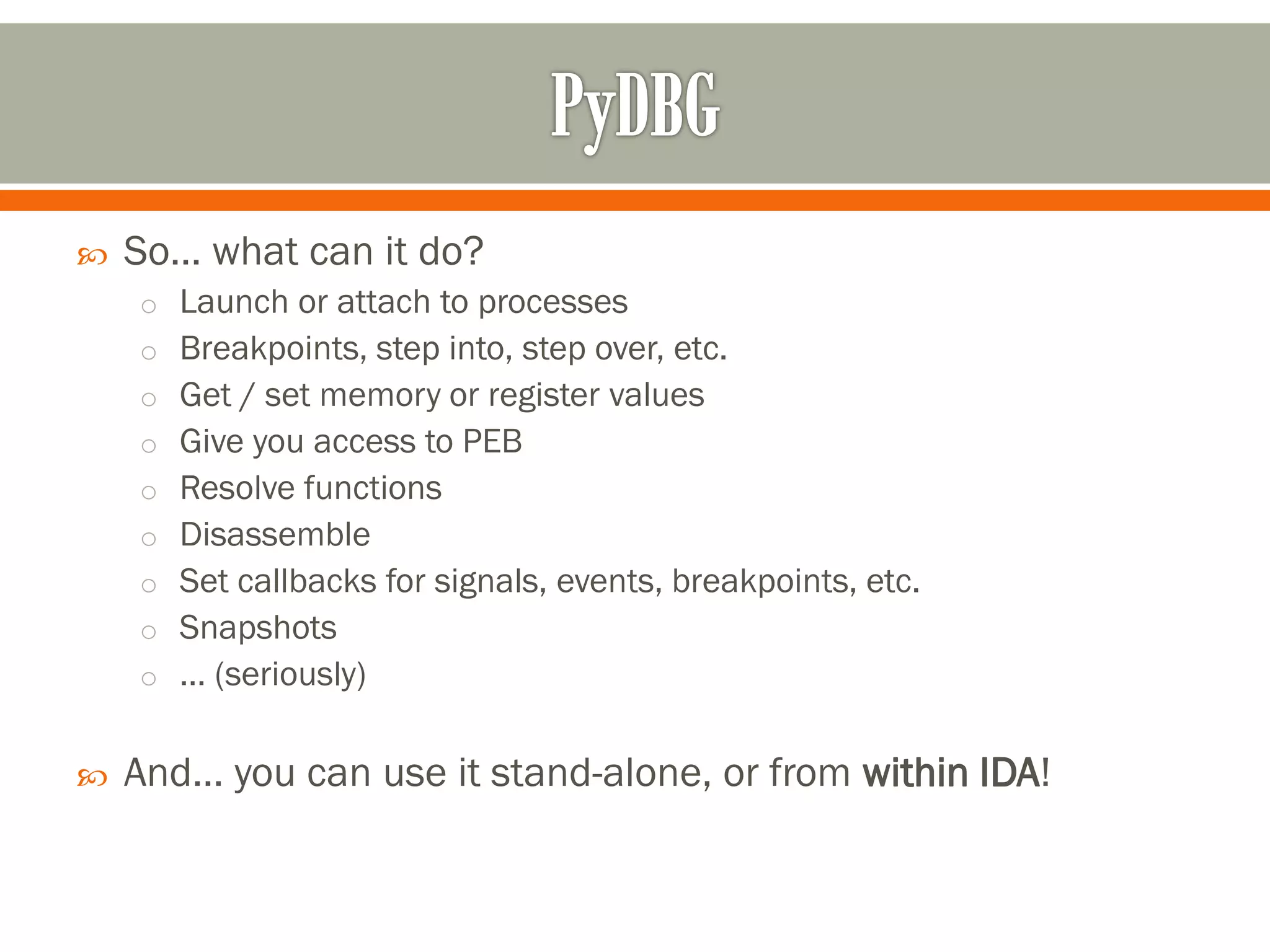
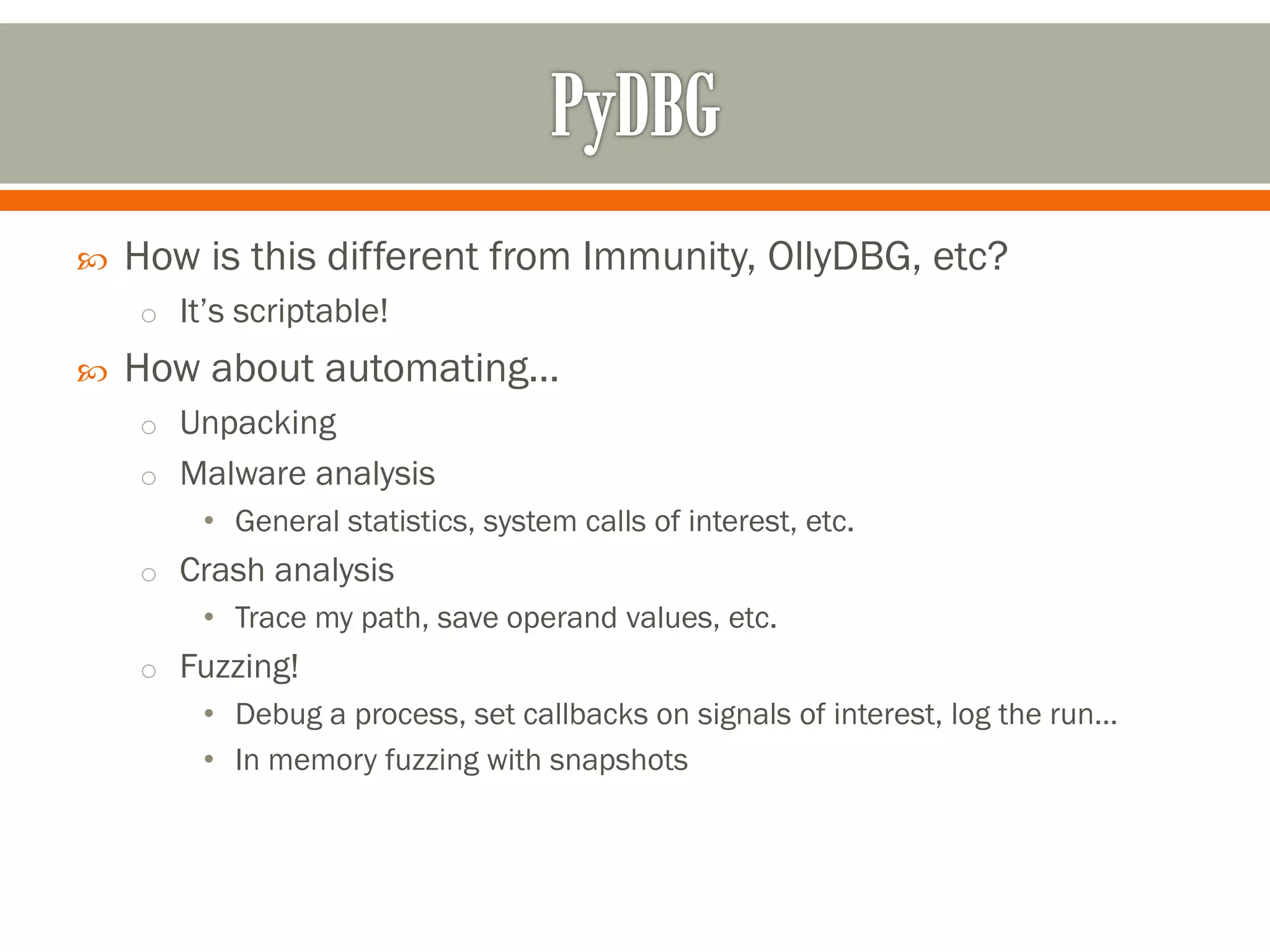
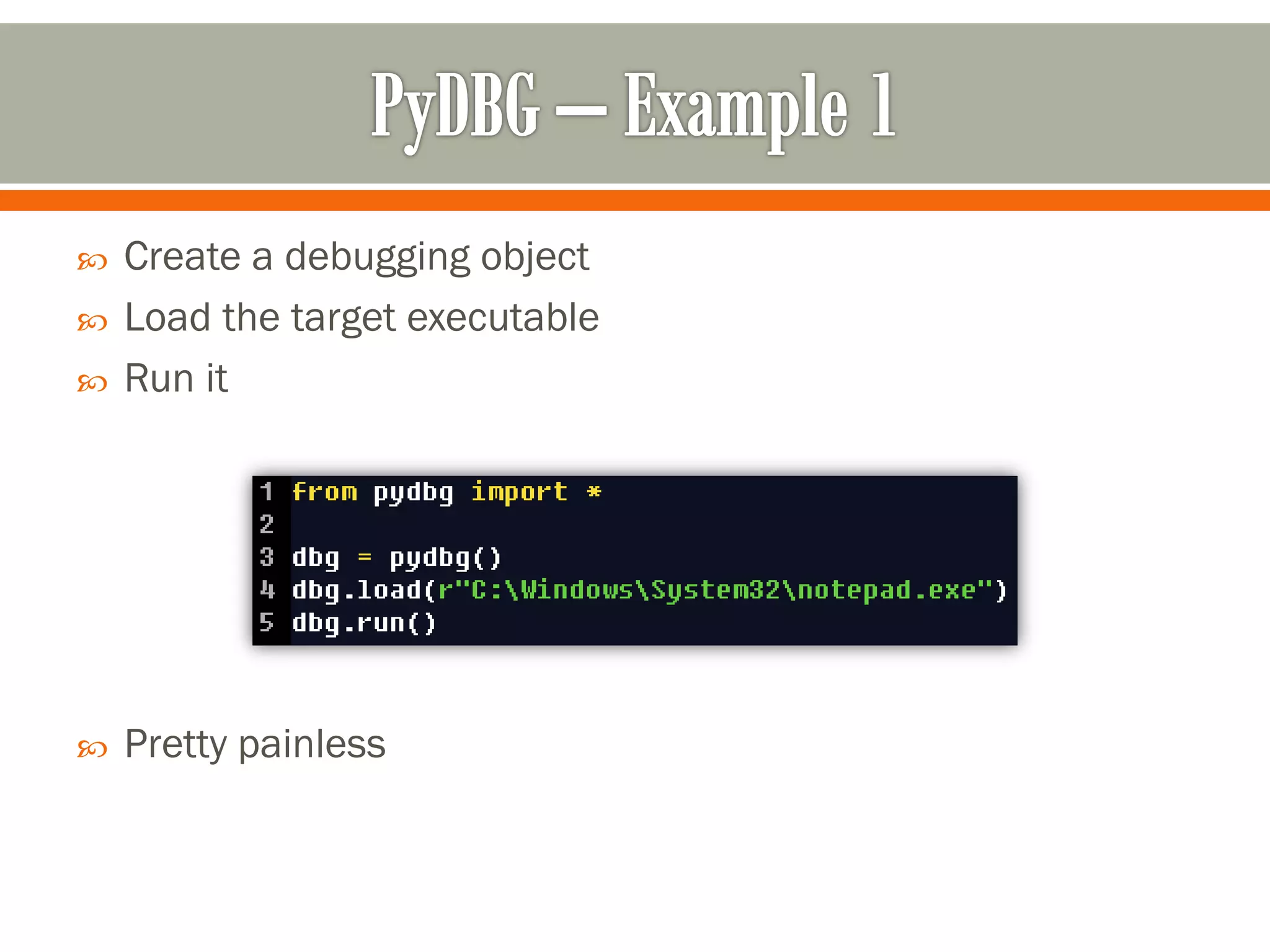
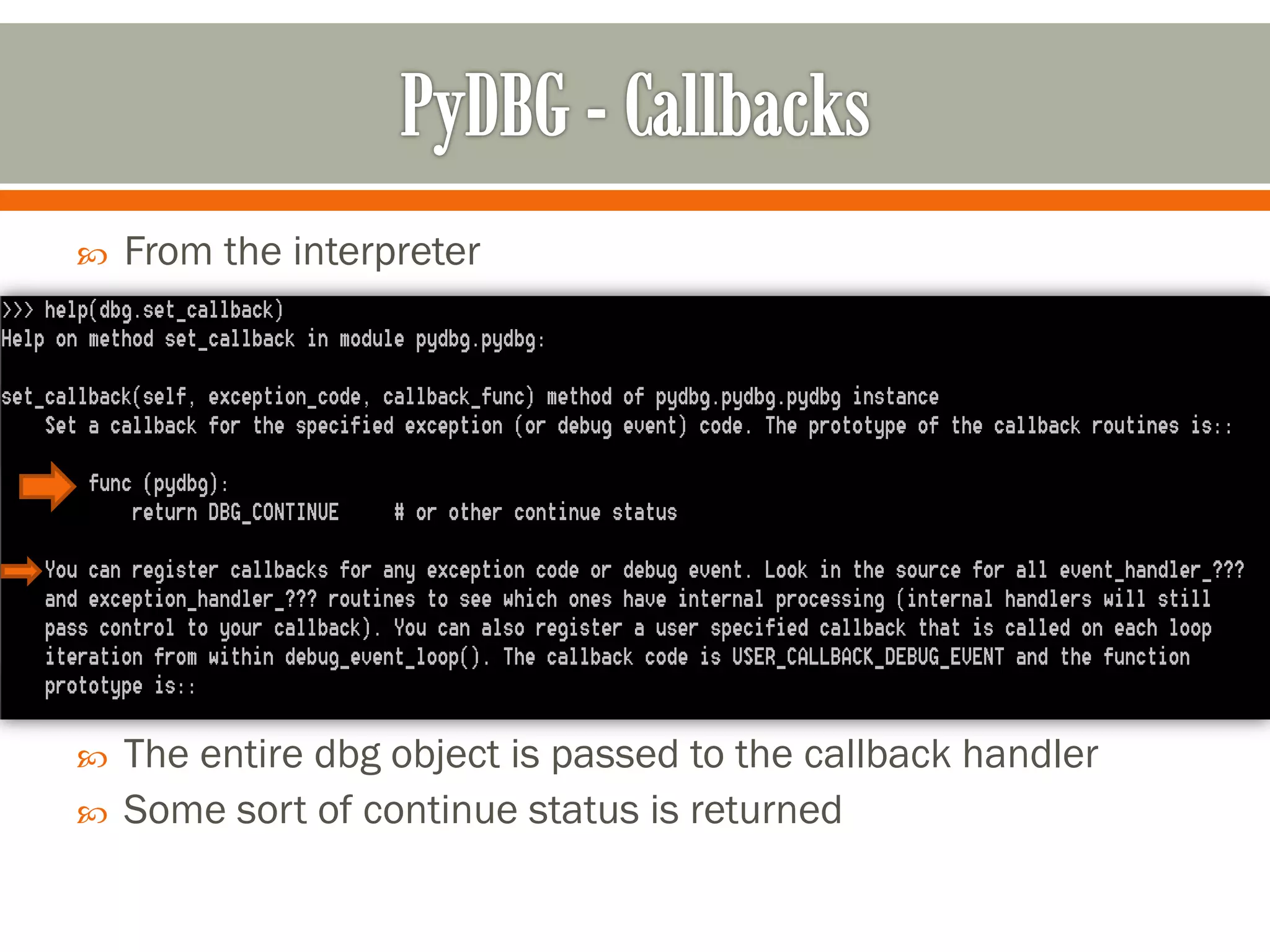
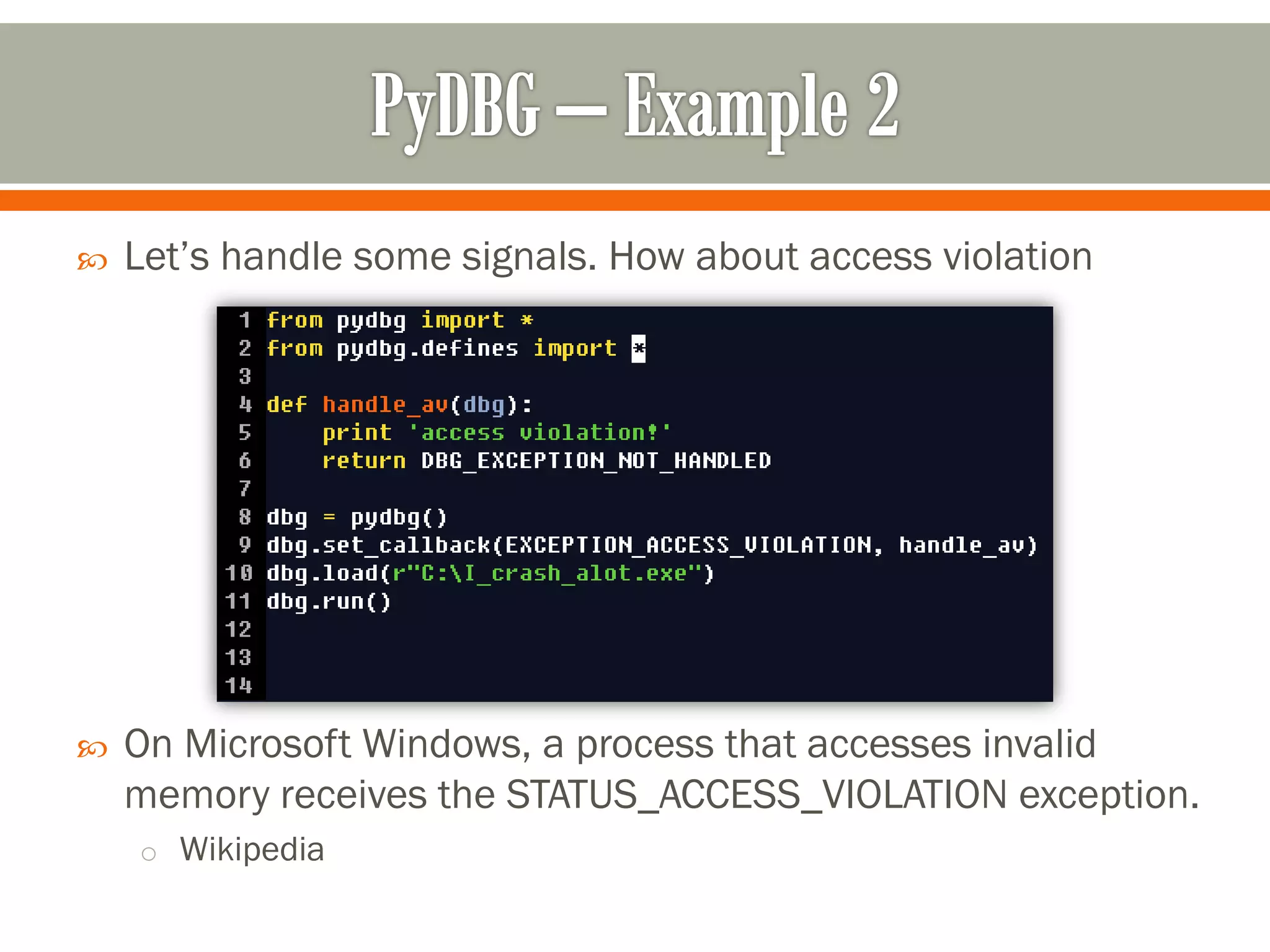
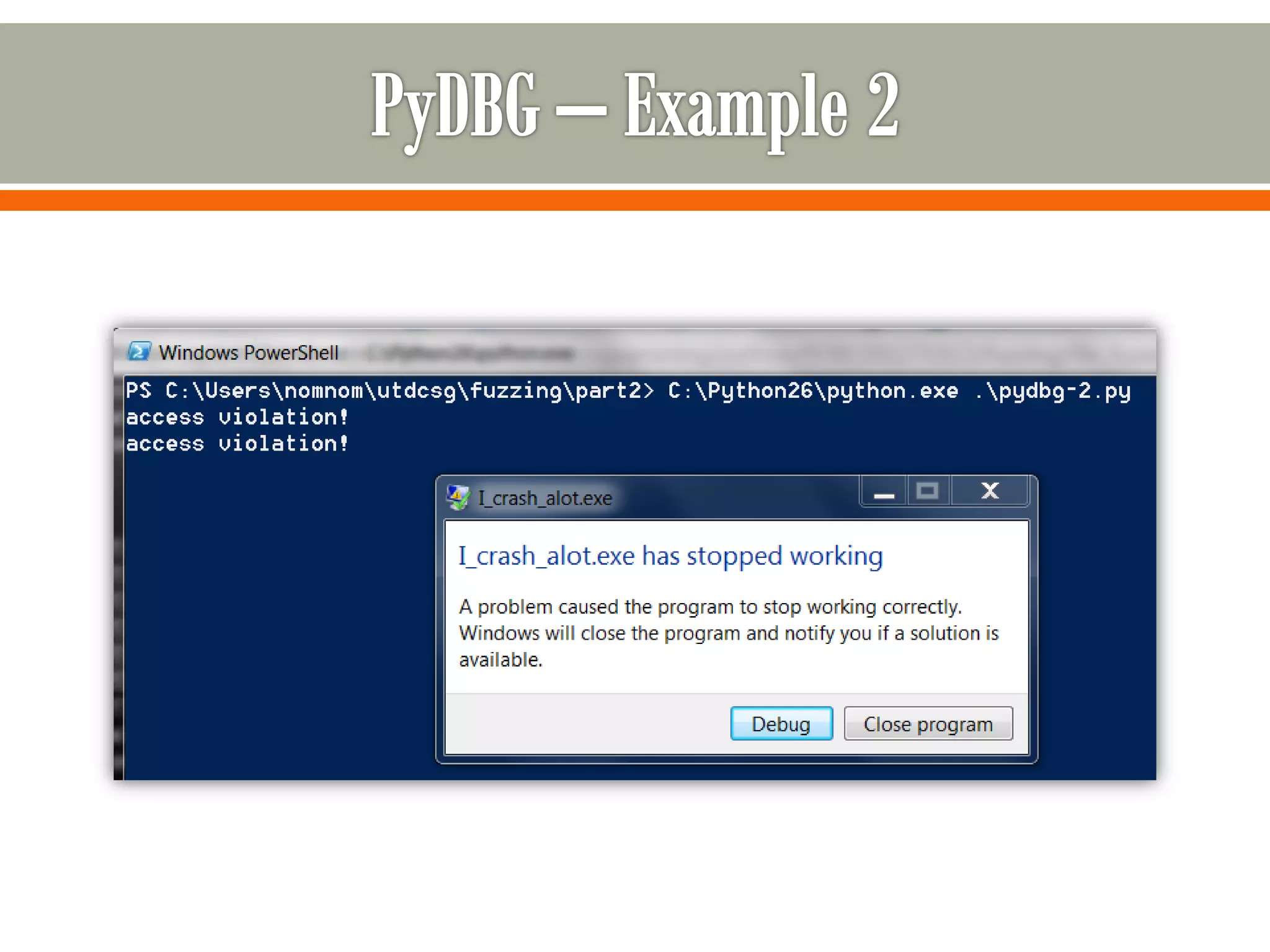
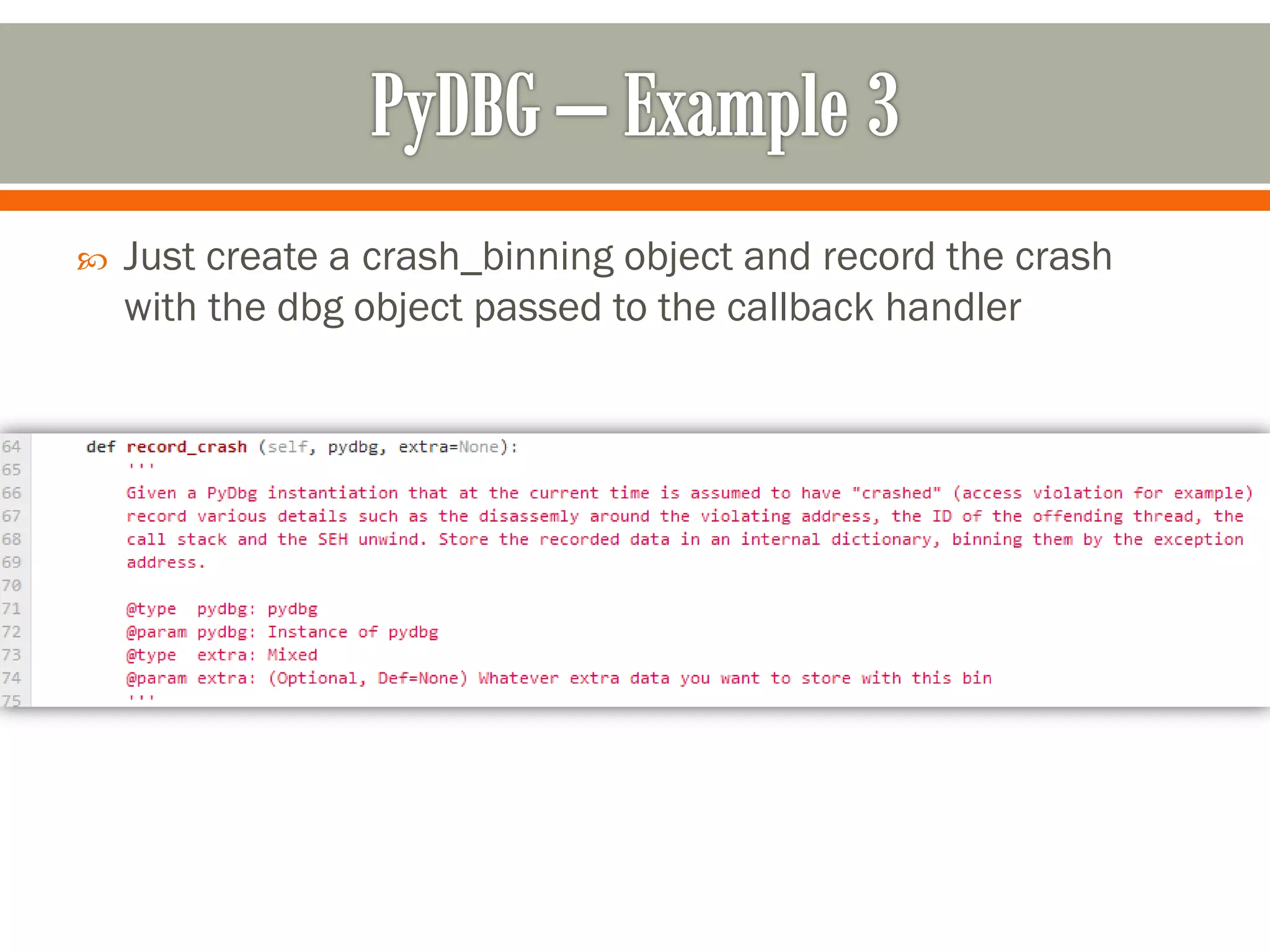
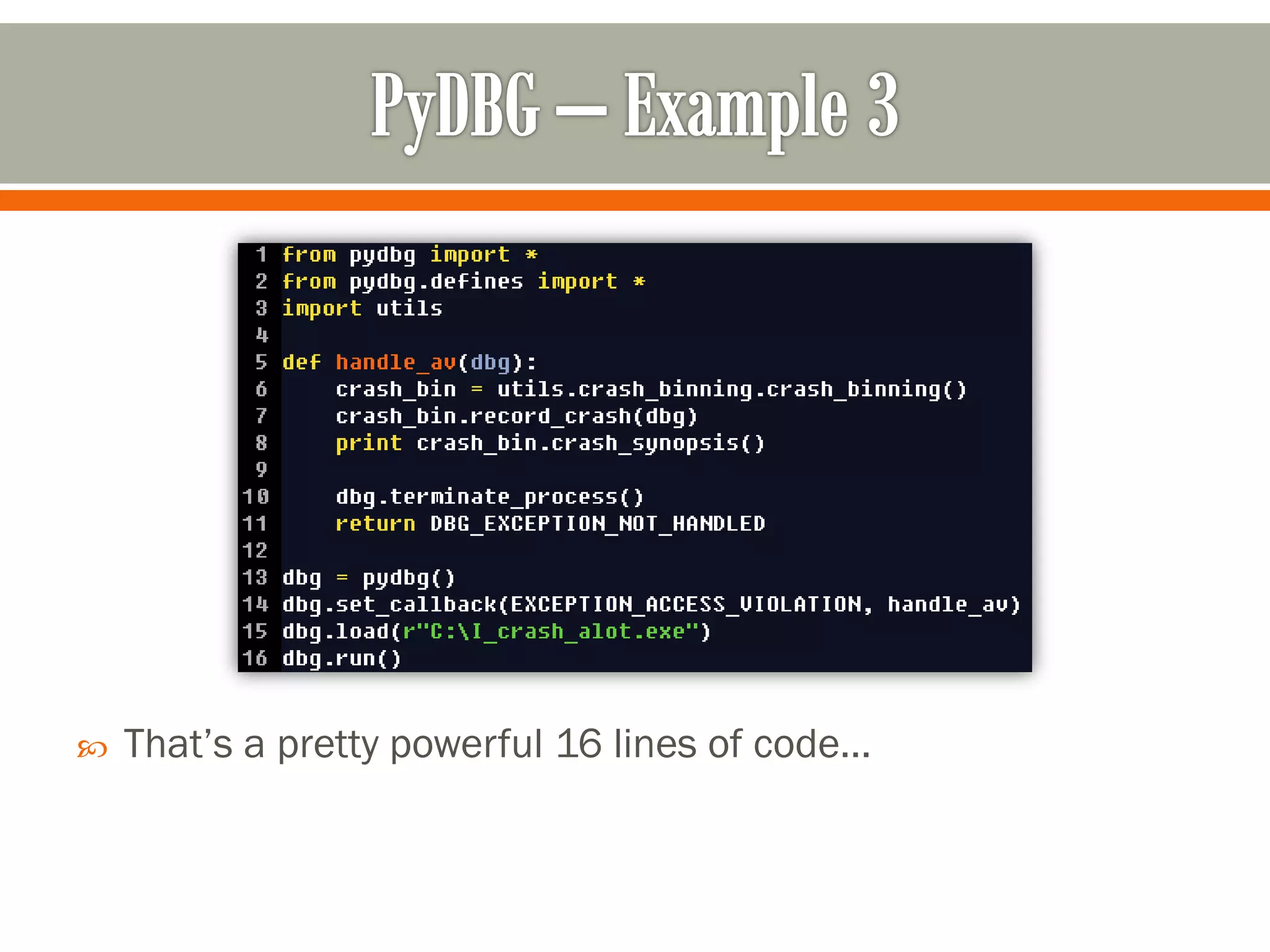
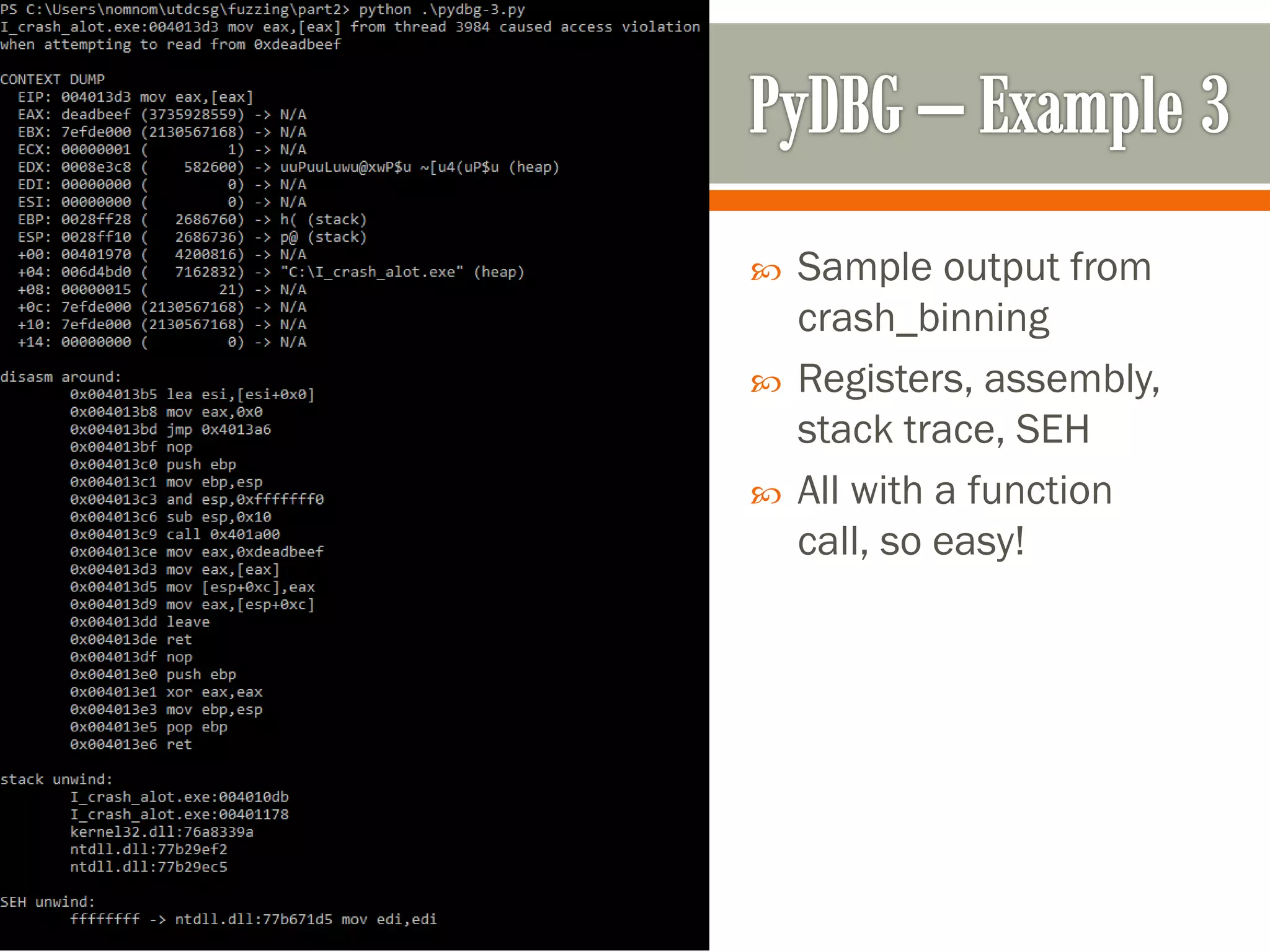
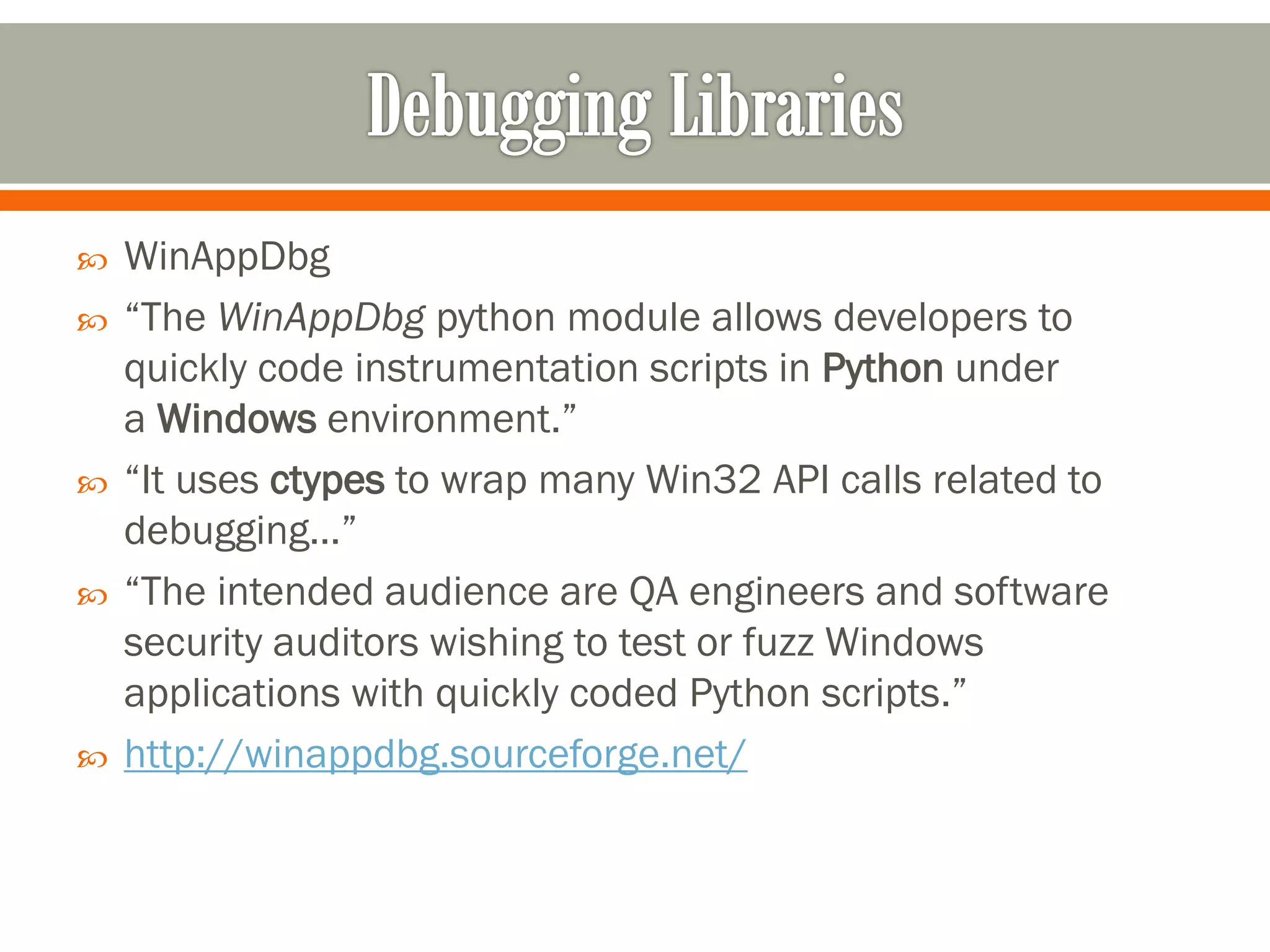
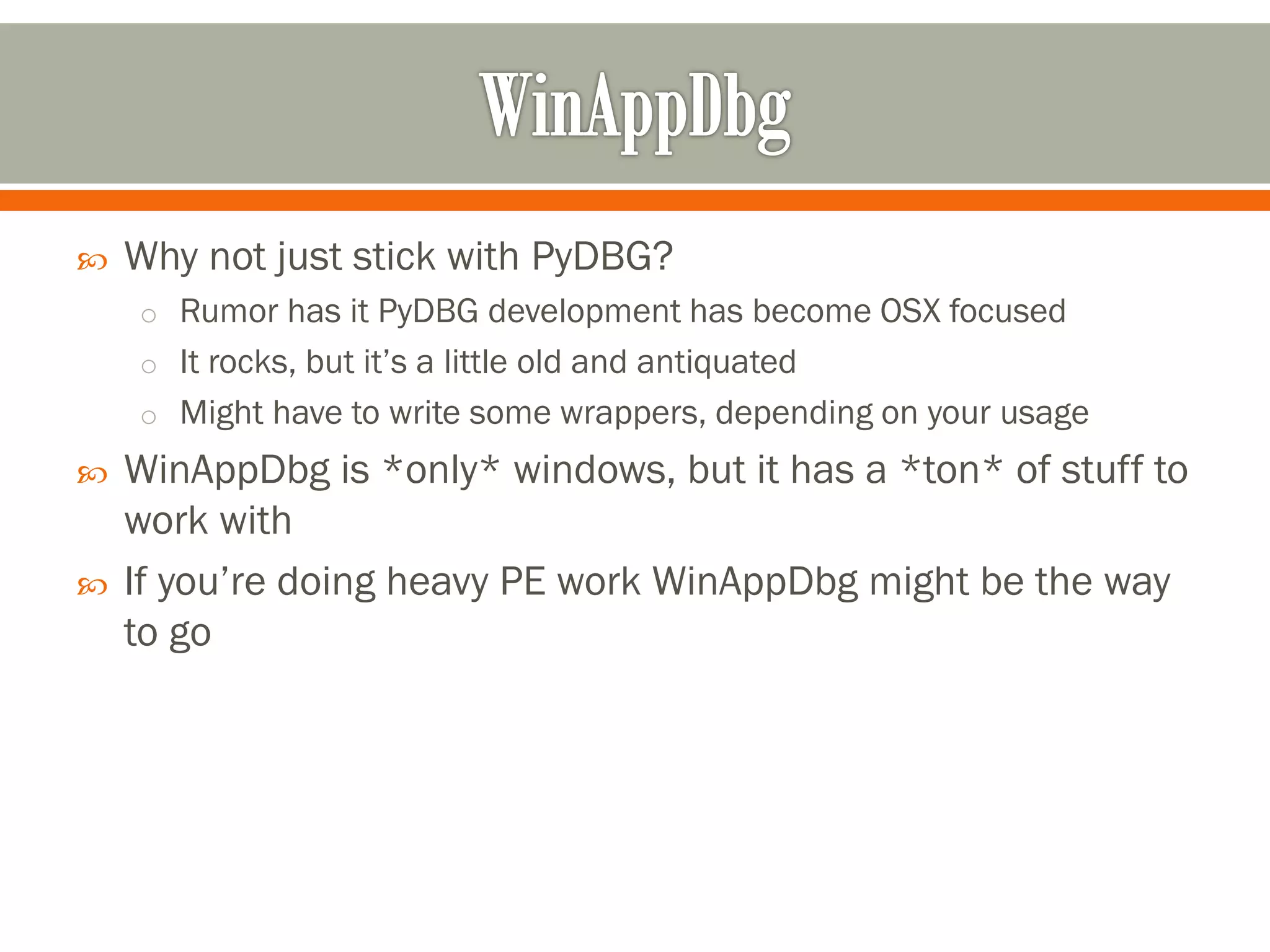
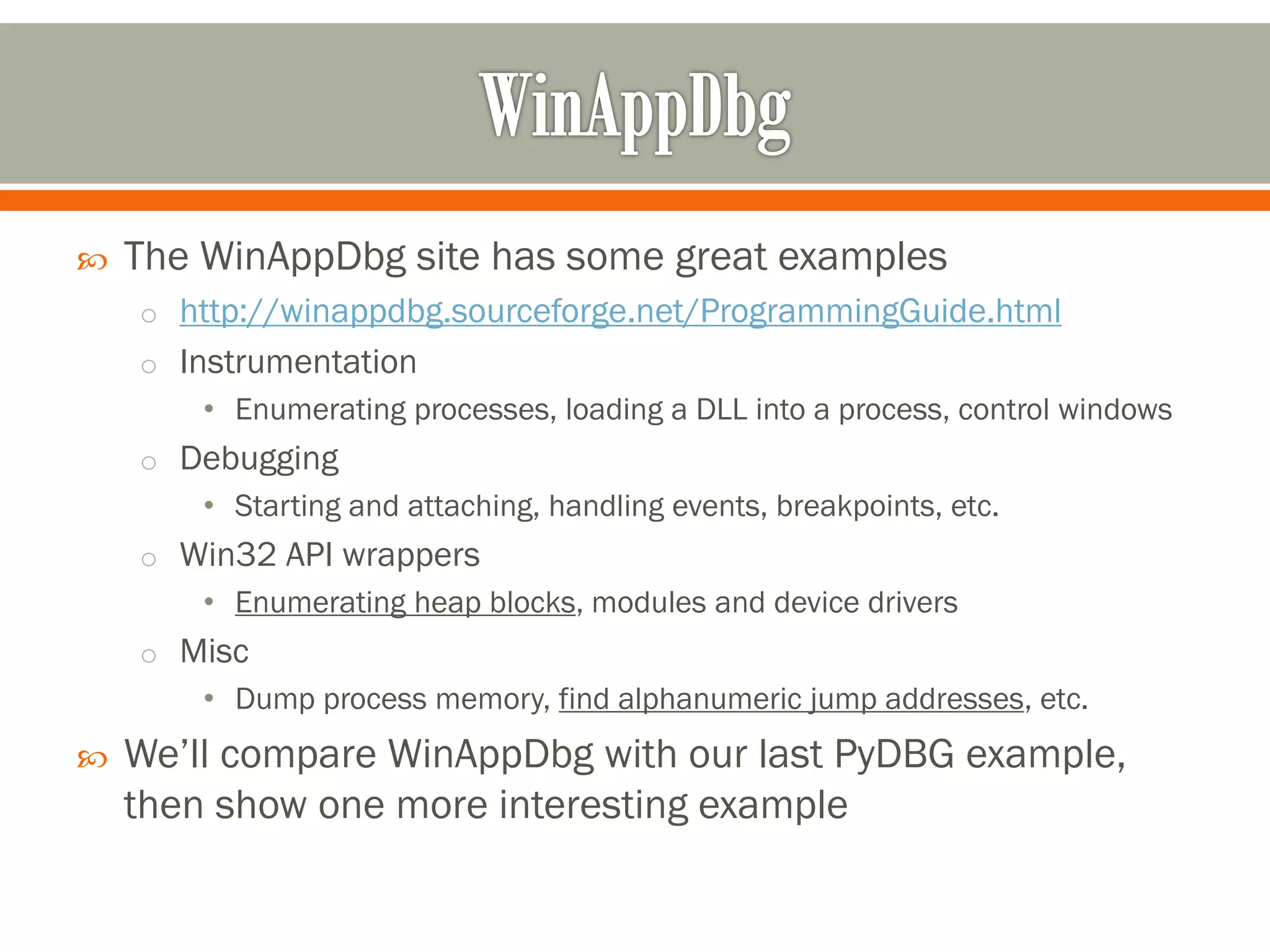
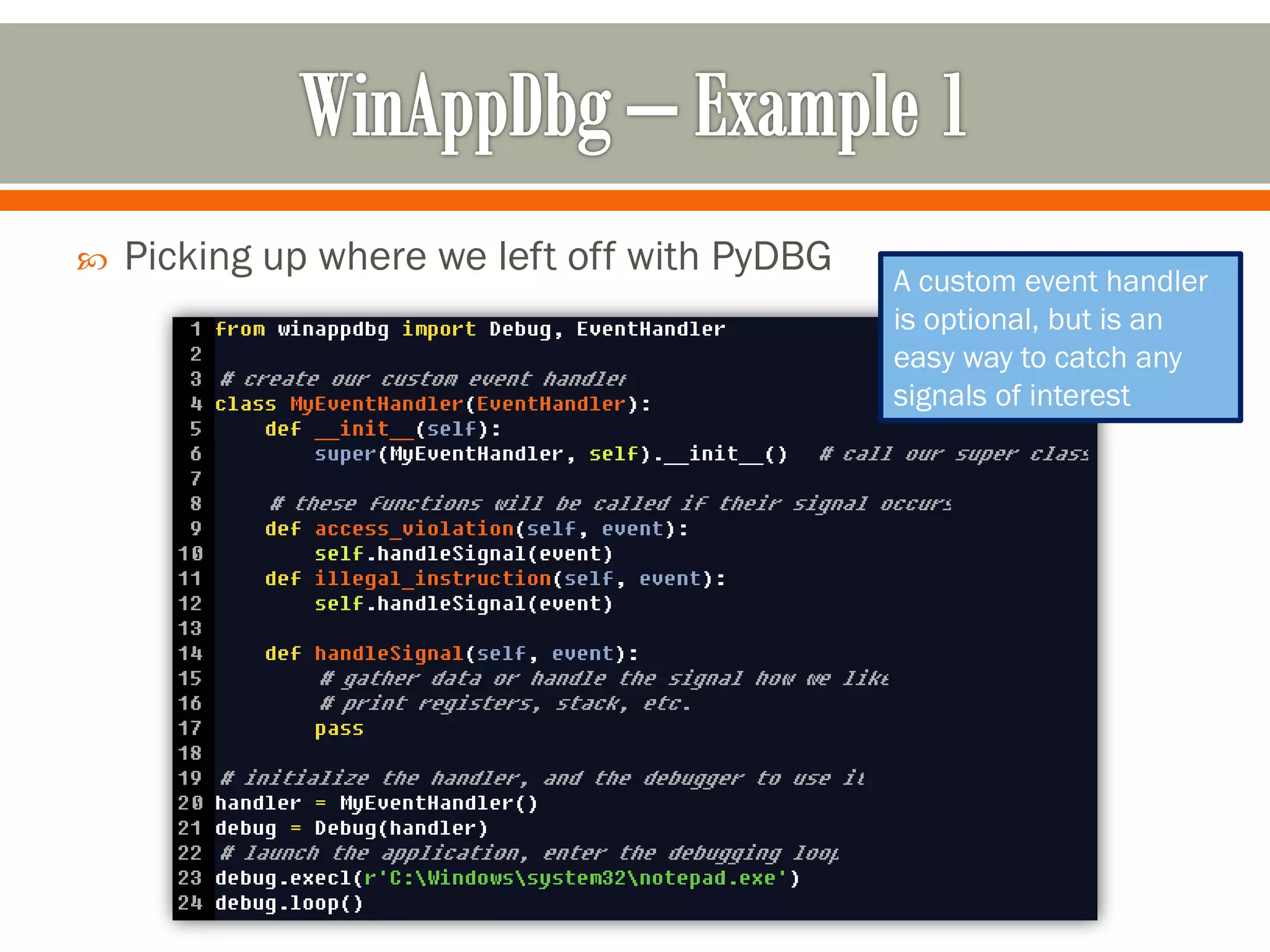
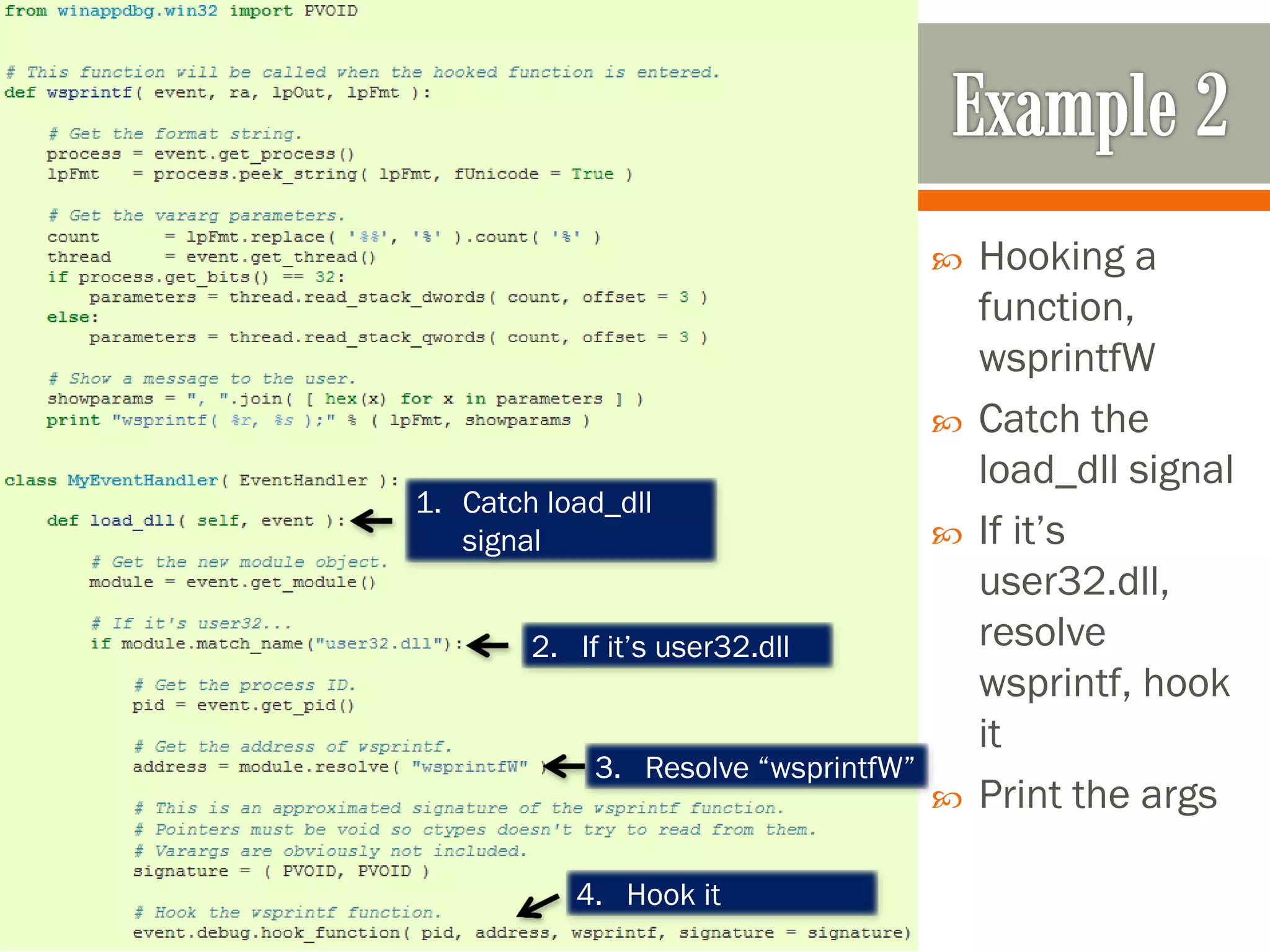
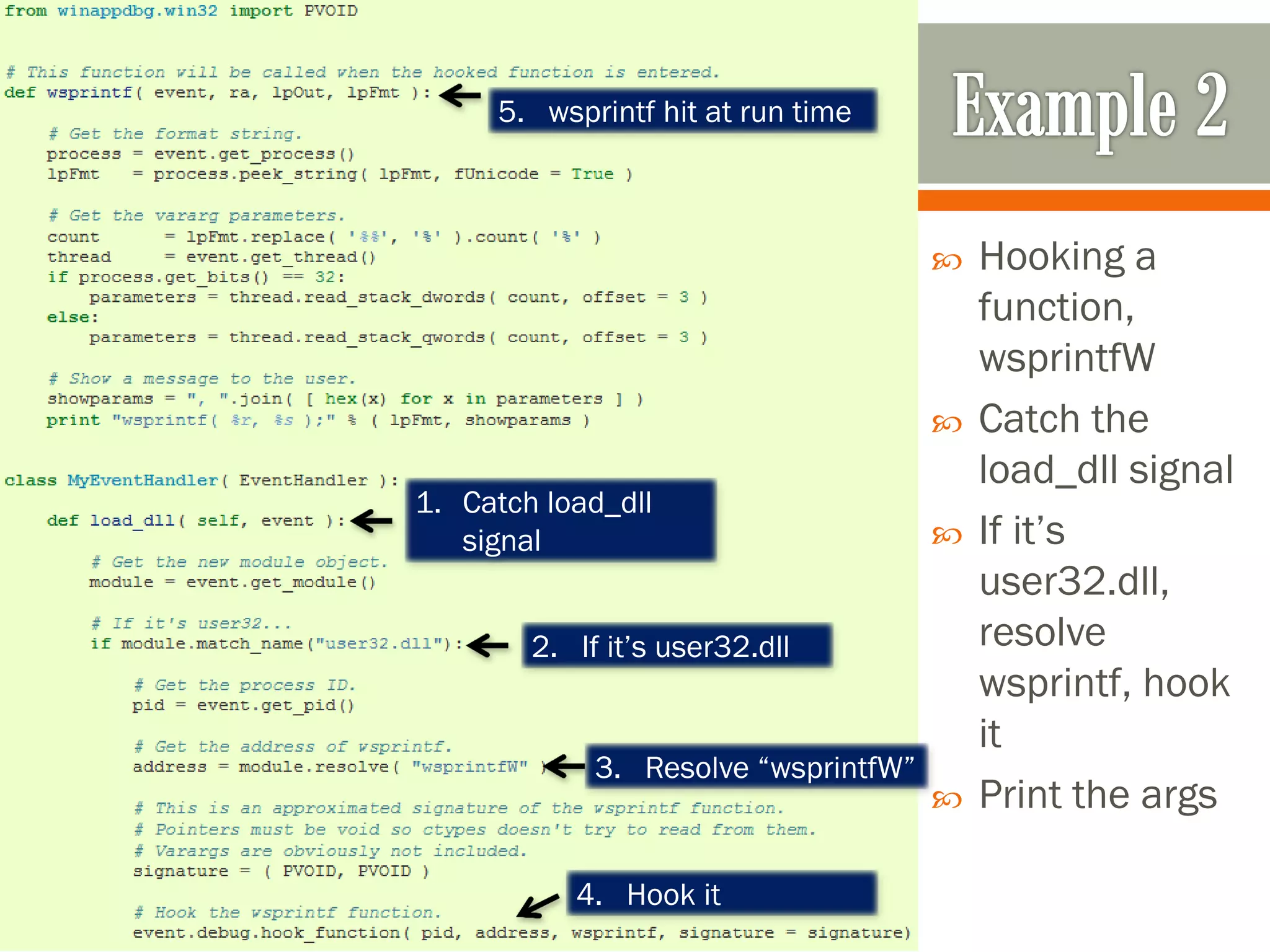
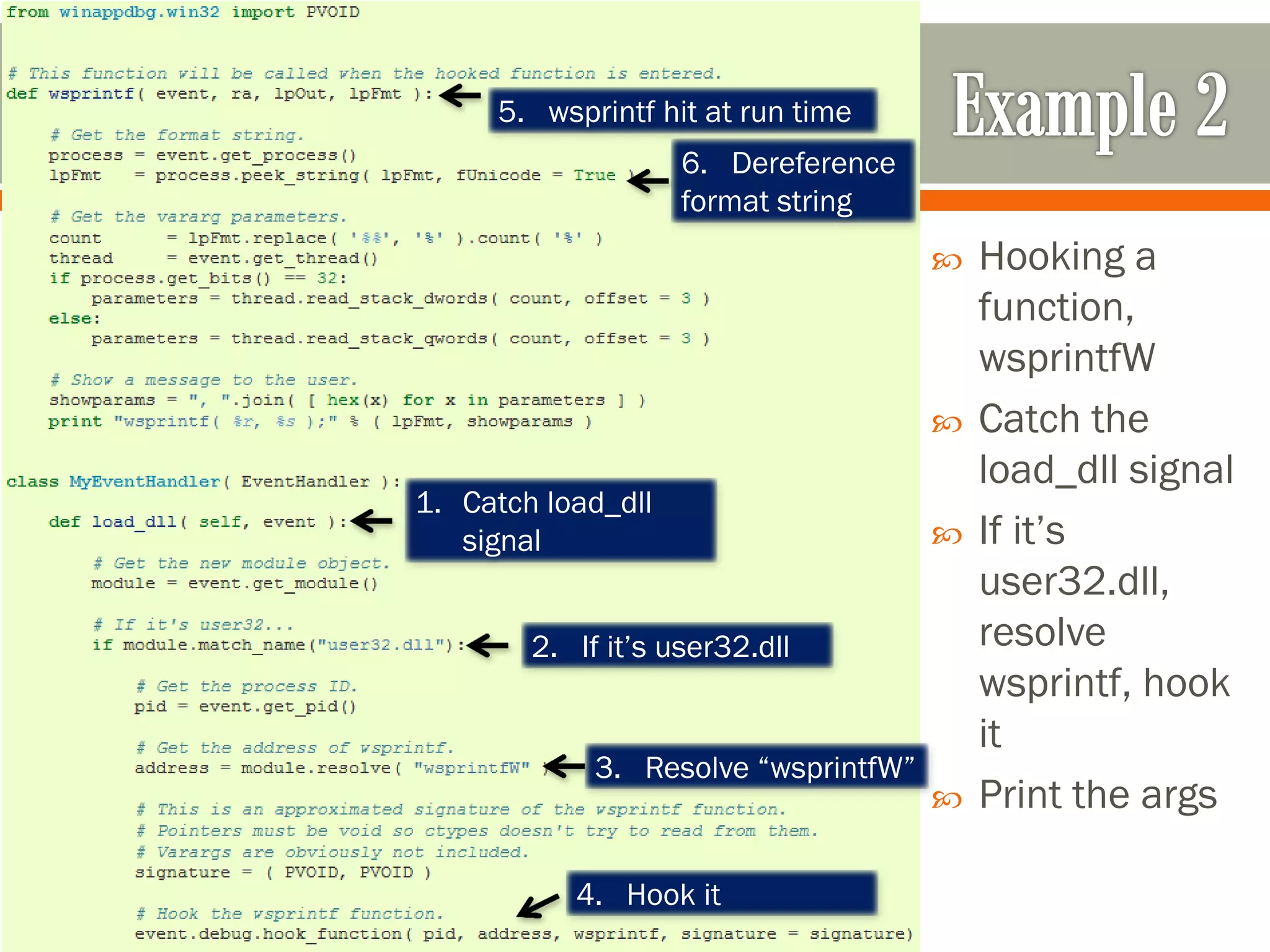
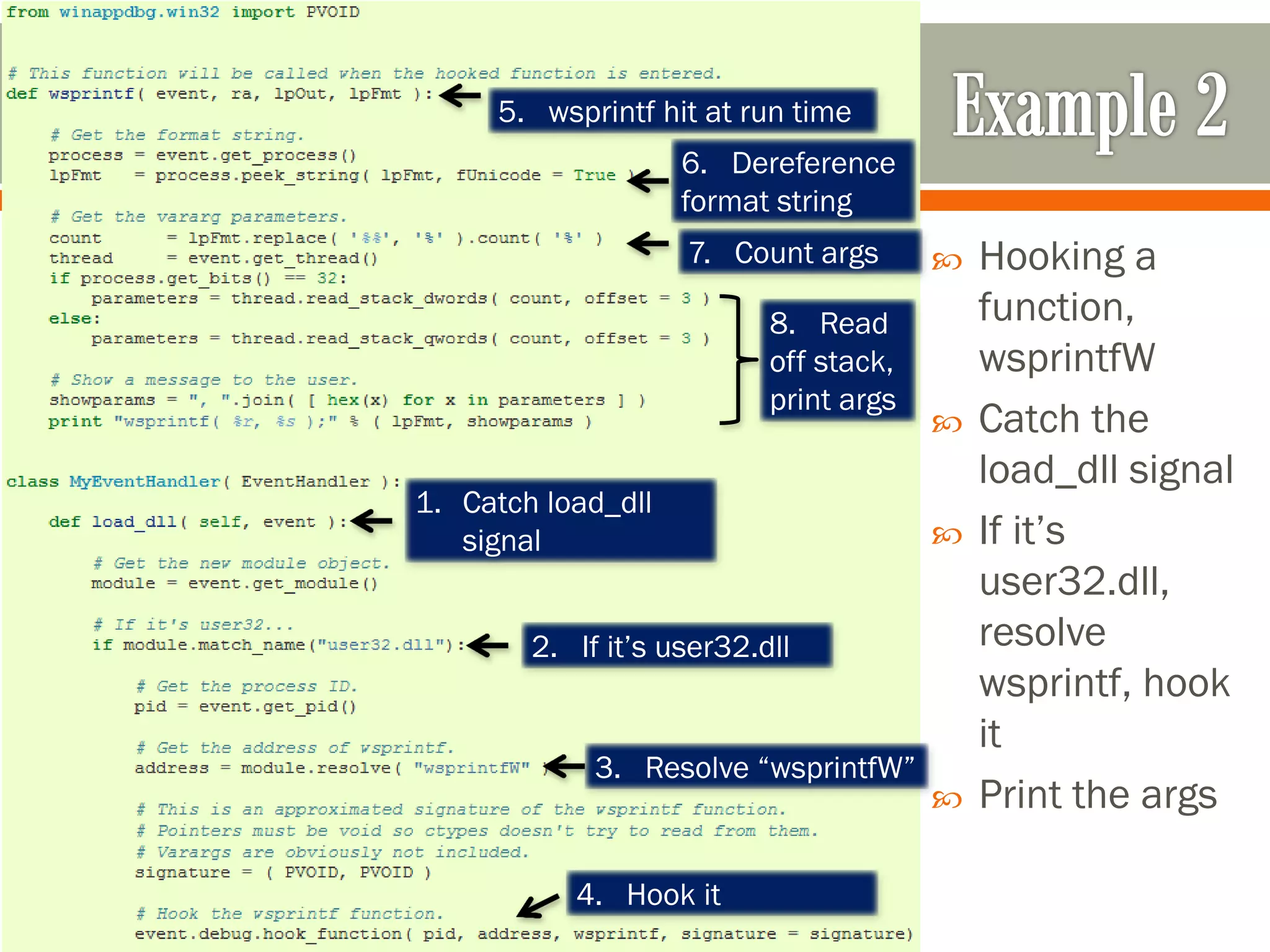
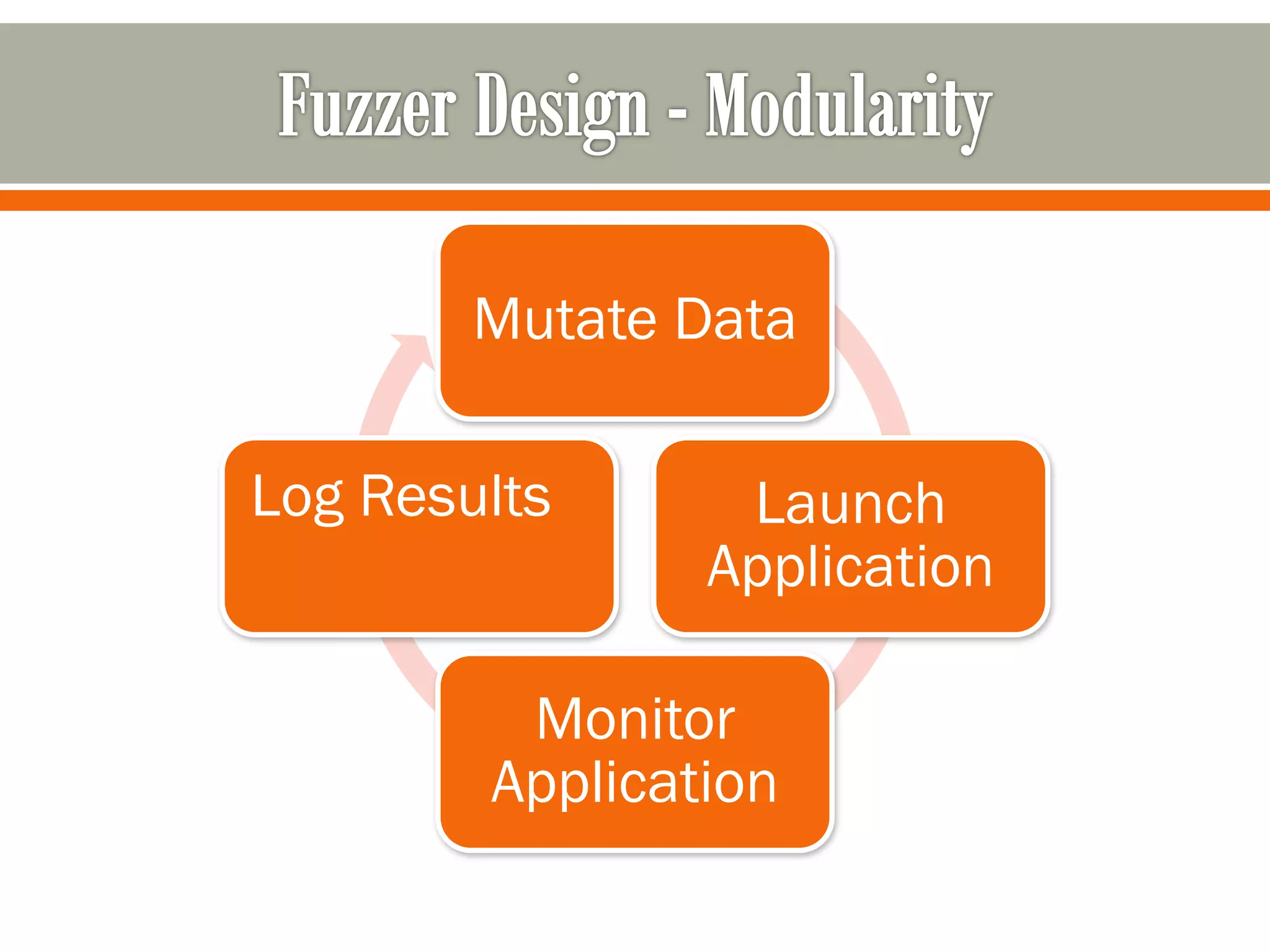
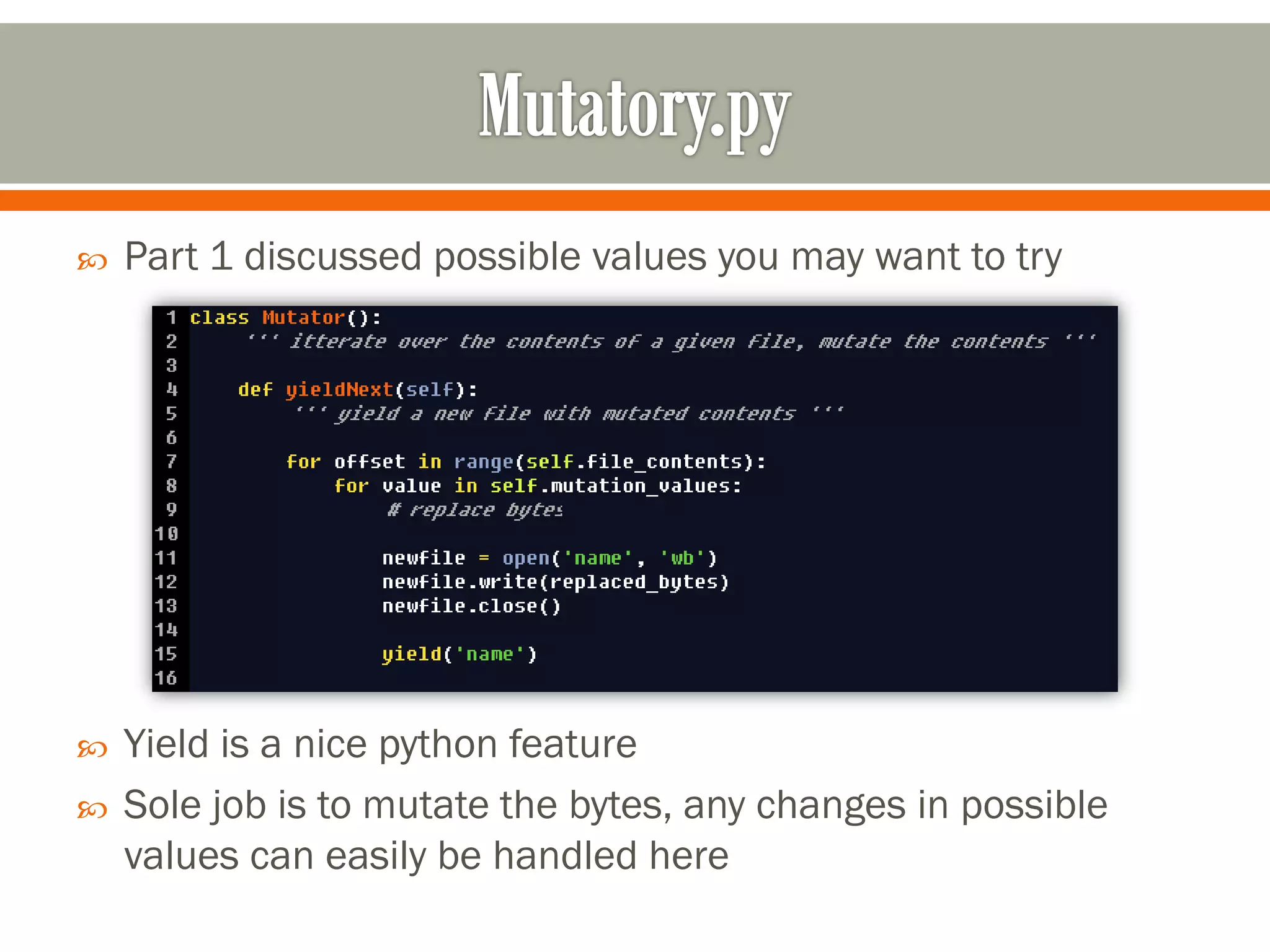
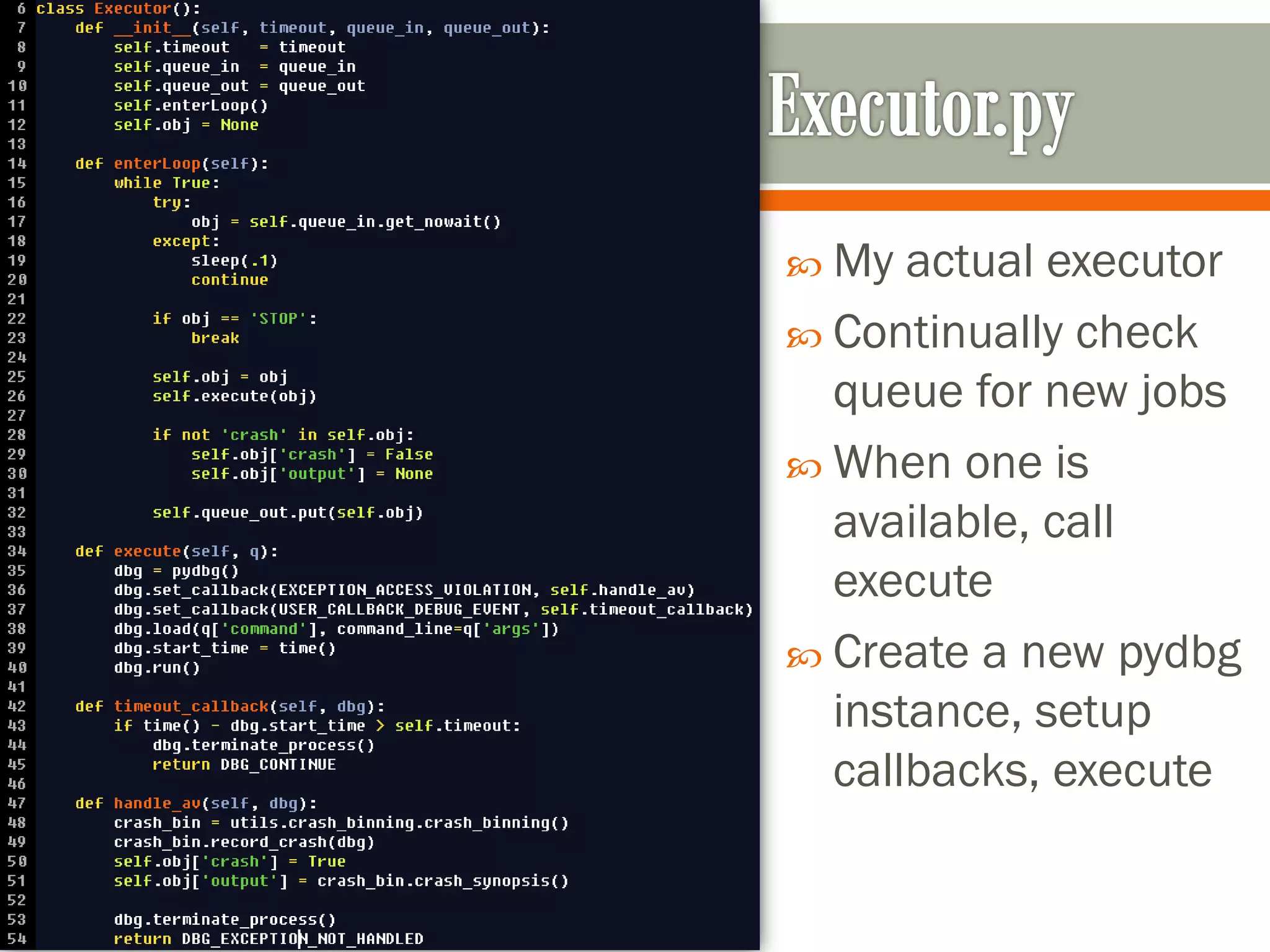
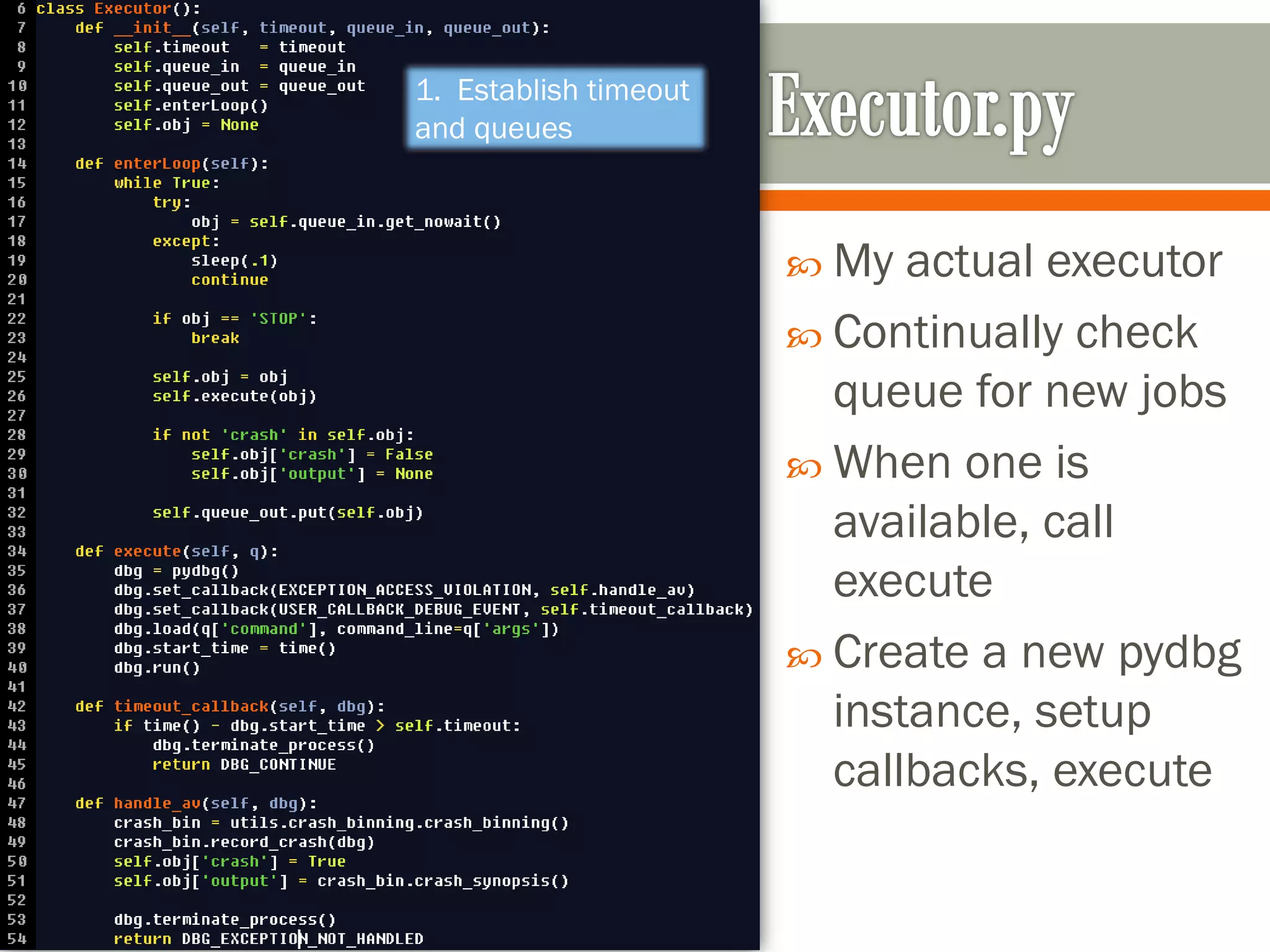
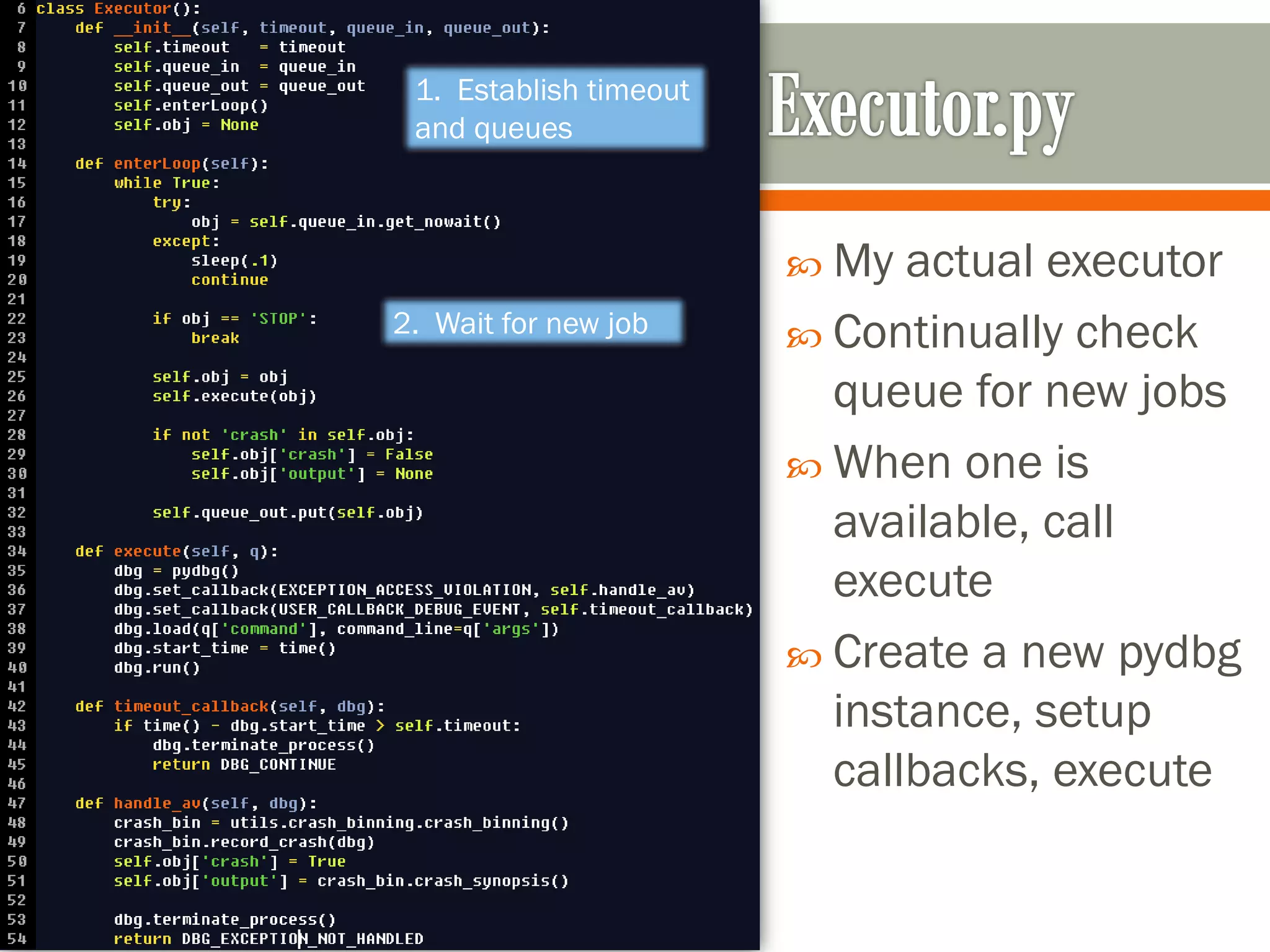
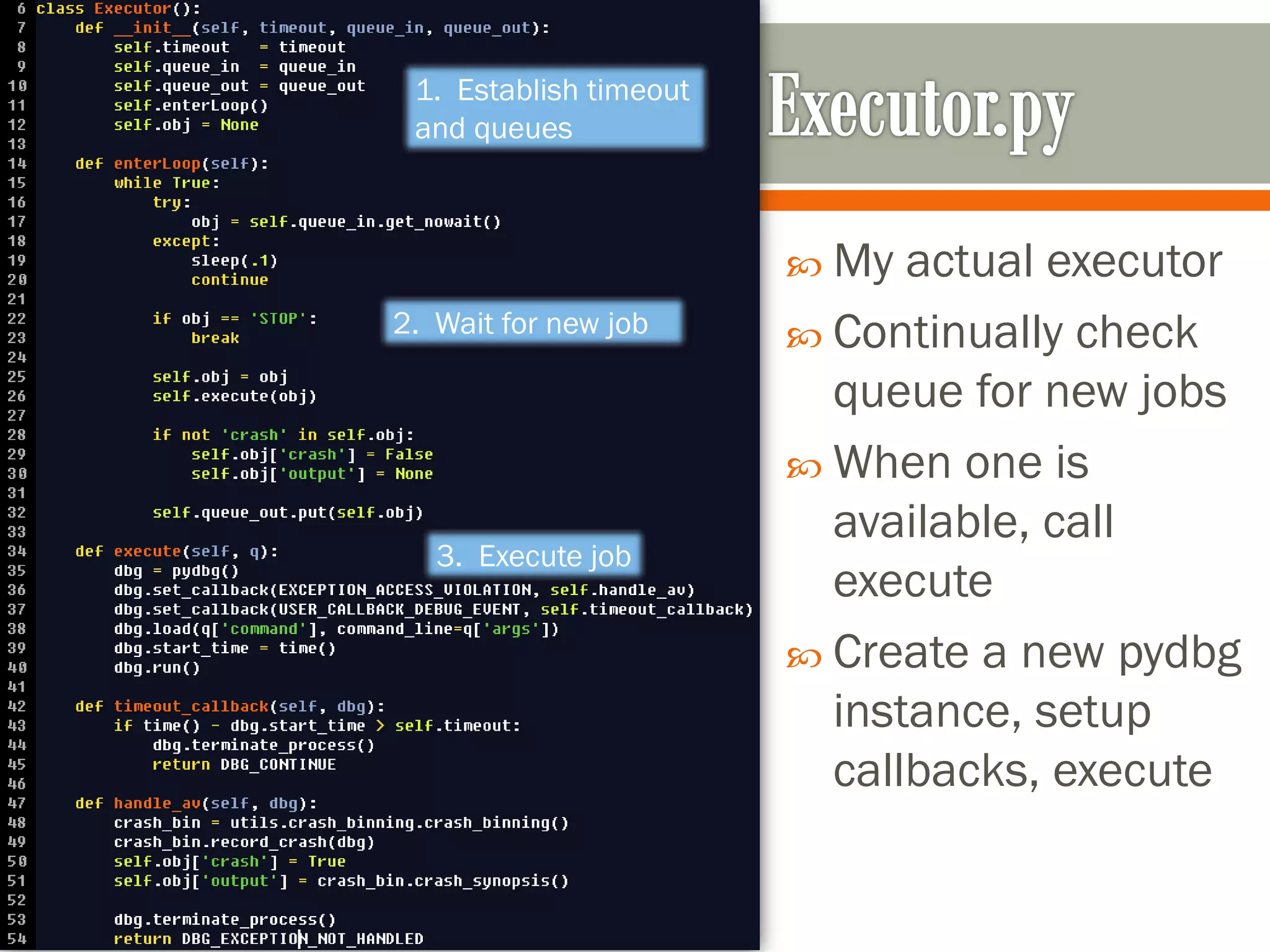
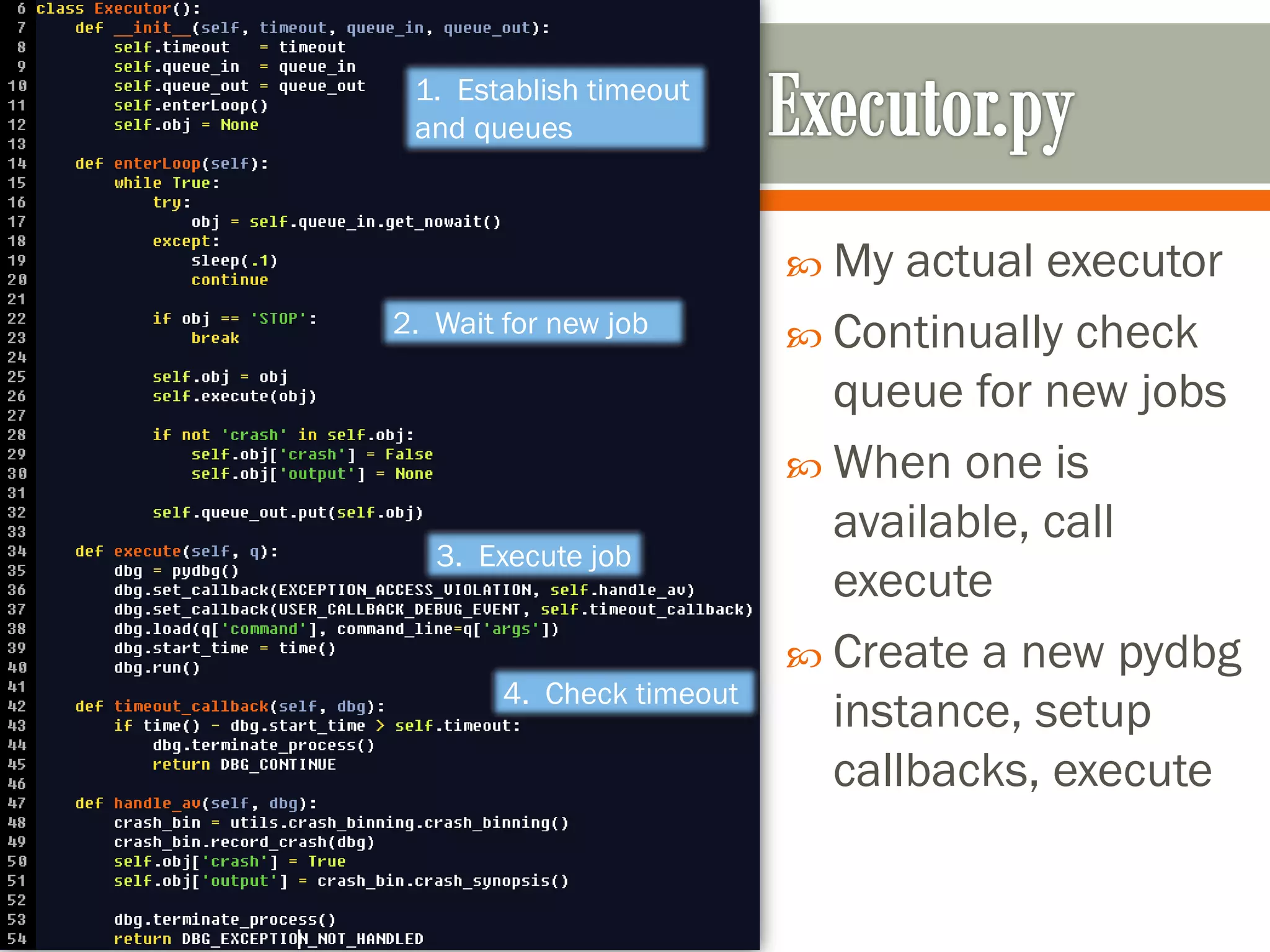
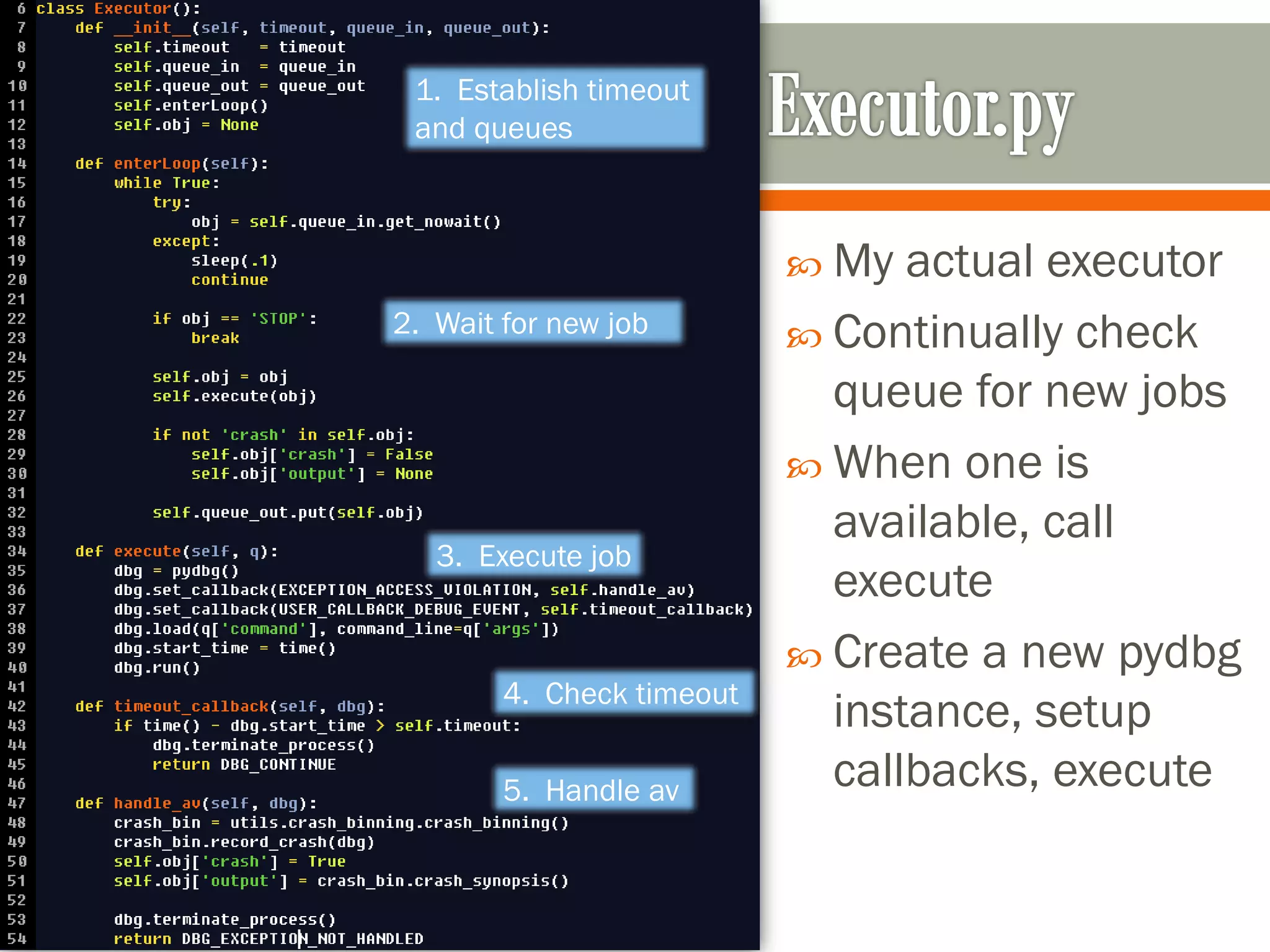
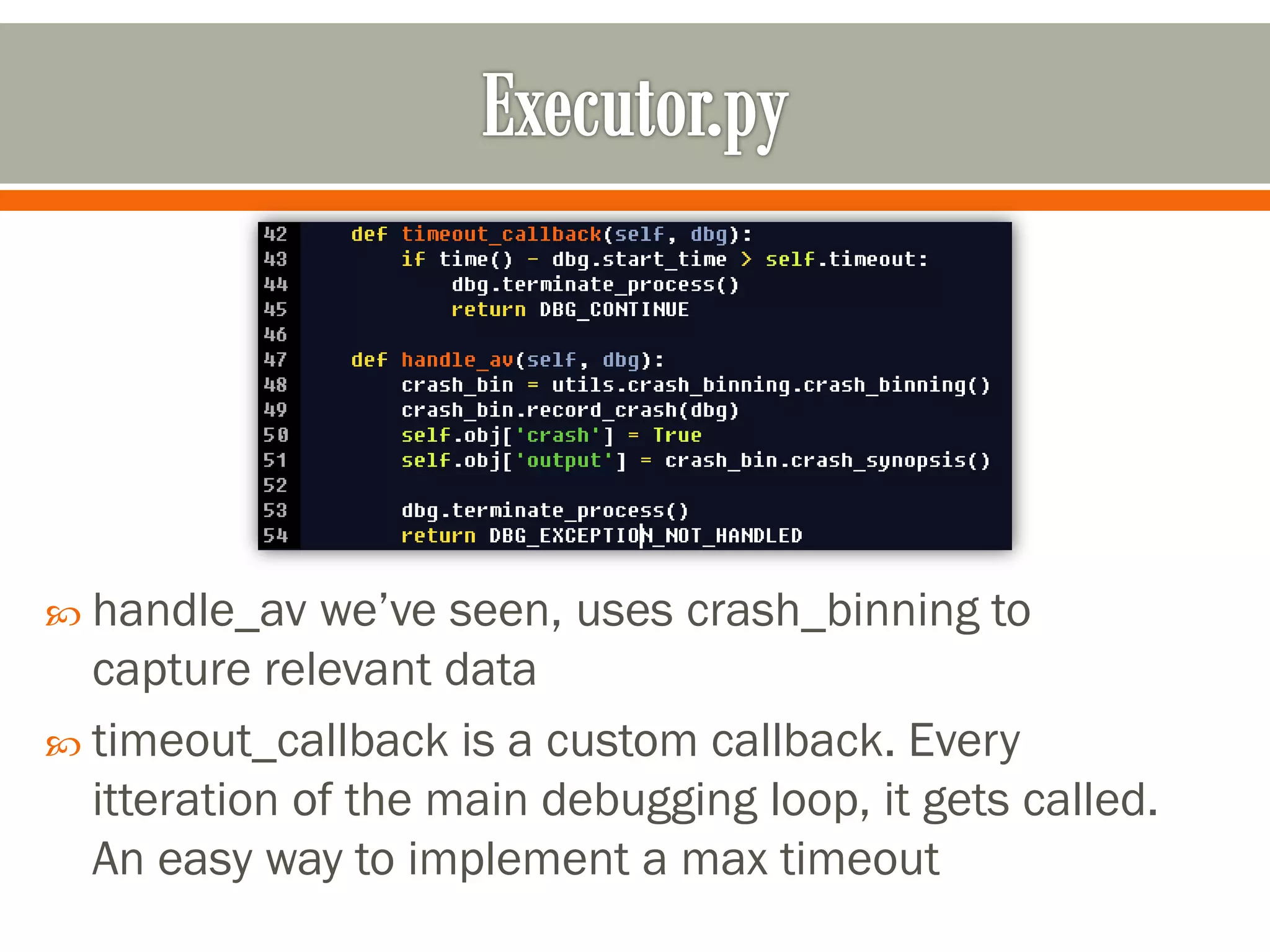
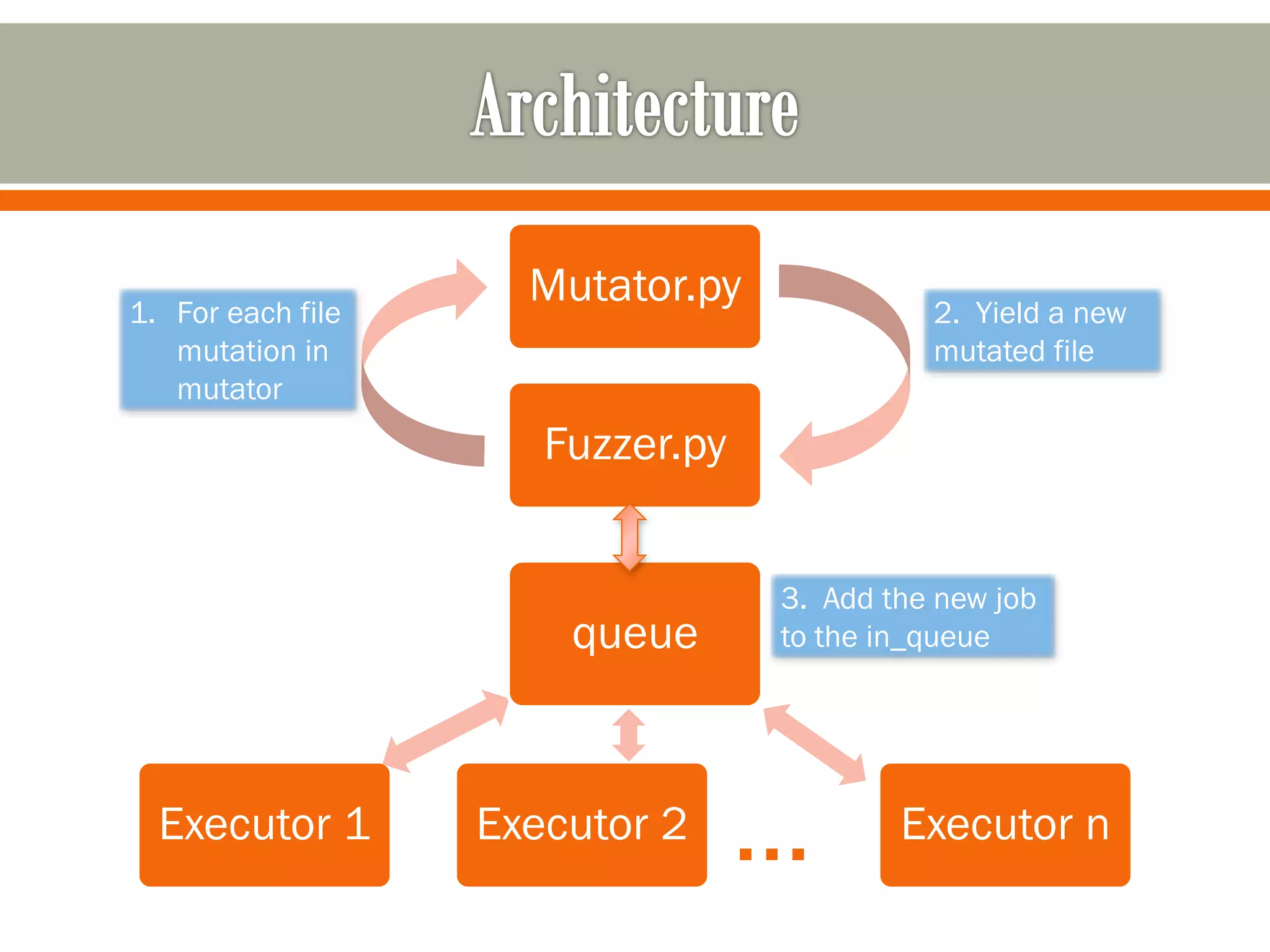
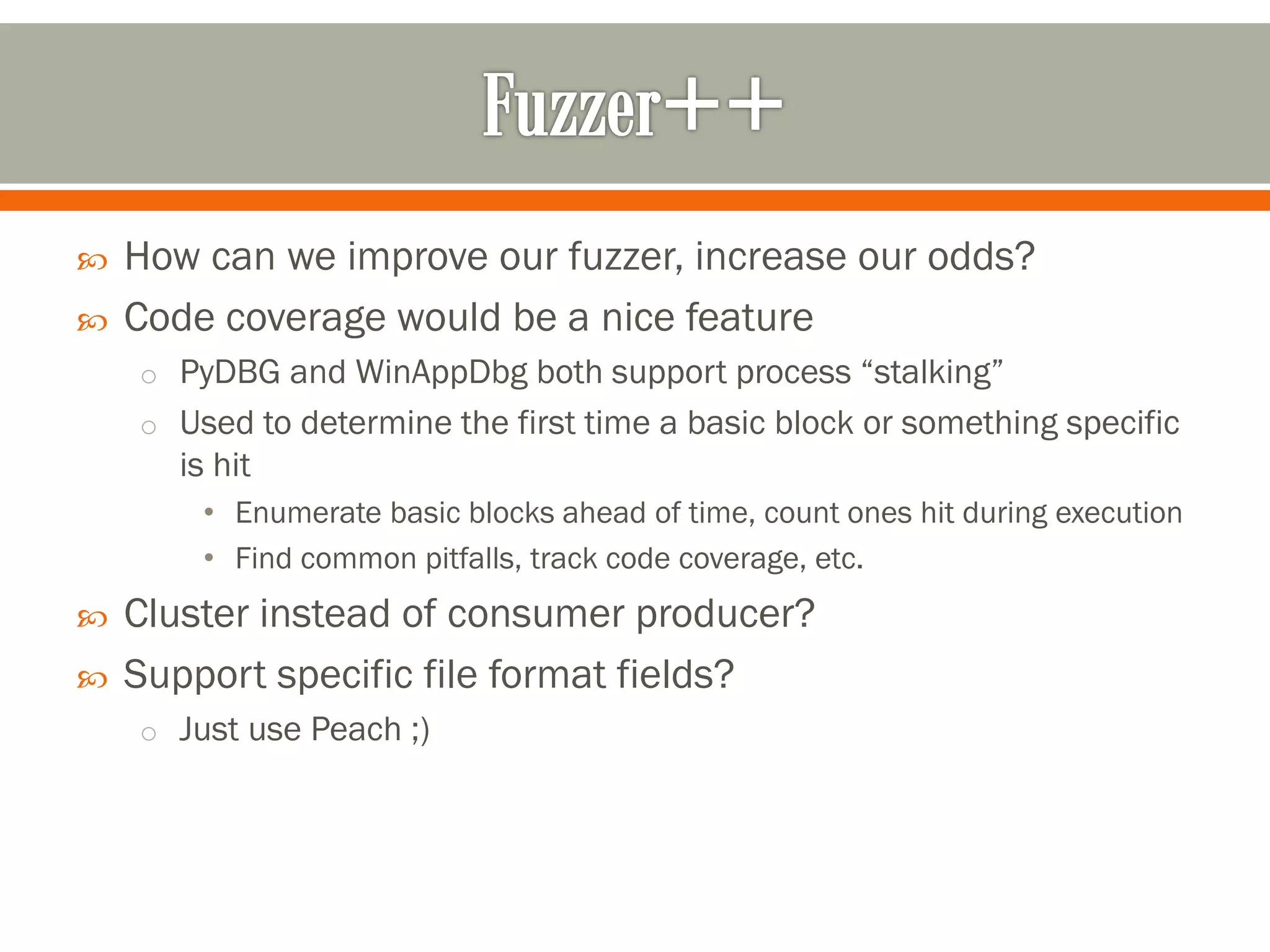
The document discusses tools and techniques for debugging and fuzzing applications on Windows, primarily focusing on pydbg and winappdbg. It outlines their capabilities such as process manipulation, memory access, and automation for tasks like malware analysis and crash handling. Furthermore, design goals for fuzzer development are highlighted, emphasizing modularity, reusability, and the importance of code coverage in enhancing fuzzing effectiveness.