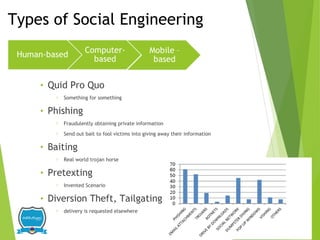
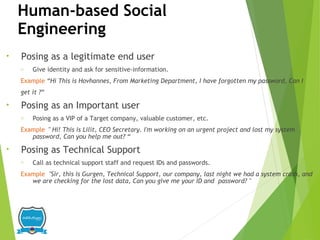
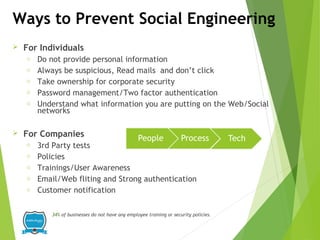
This document discusses social engineering, which involves manipulating individuals to reveal sensitive information, often leading to data breaches. It highlights various techniques, case studies, and statistics indicating the prevalence and costs of such attacks on organizations, emphasizing the need for awareness and defensive measures. The document also outlines types of social engineering, including phishing and pretexting, and offers recommendations for individuals and companies to protect against these threats.