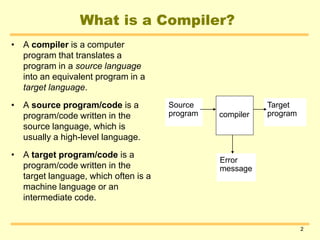
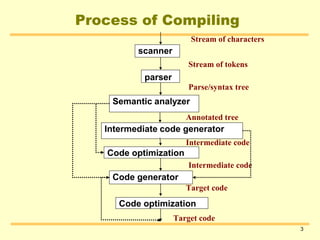
A compiler is a computer program that translates a program written in a source language into an equivalent program in a target language. The compilation process involves scanning the source code, parsing it, performing semantic analysis, generating intermediate code, optimizing the code, and finally generating the target code. Key data structures used in compilers include symbol tables to store information about identifiers, literal tables to store constants, and parse trees to represent the syntactic structure of the program.