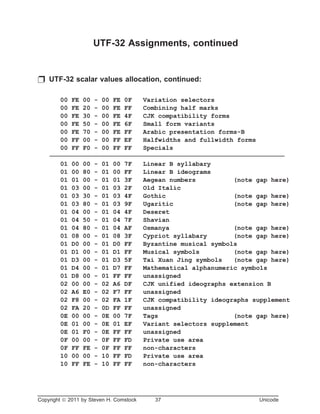
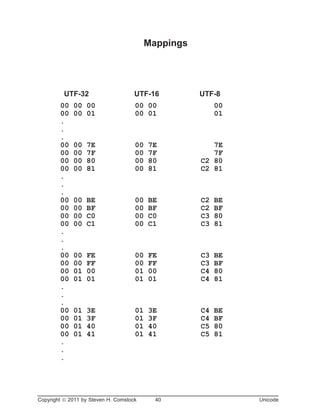
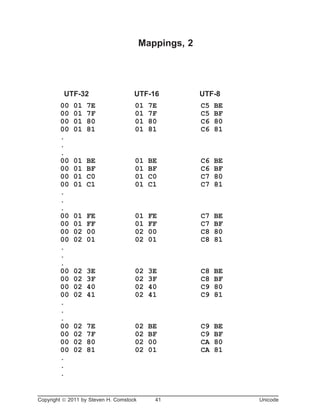
Unicode is a standard for representing characters across different platforms and languages. It defines coding schemes like UTF-8, UTF-16, and UTF-32 to represent characters as binary values. UTF-16 uses 16-bit values for most characters but introduces surrogate pairs to represent some characters requiring two 16-bit values. UTF-32 uses 32-bit values for all characters. UTF-8 varies the number of bytes per character from 1 to 4 to optimize for English. Unicode aims to support all languages with a single encoding scheme.



![Characters, Glyphs, and Fonts
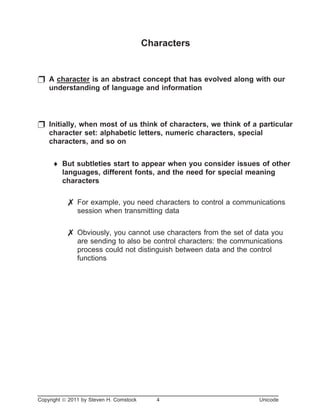
p In computer terms, a character is a grouping of bits (binary ones
and zeros) in packages of 8: one or more bytes
p There are two broad classes of characters: data characters and
control characters
¨ Although one could make a case that data characters are just
control characters whose function is to display a glyph
7 A glyph is the visible representation of a character
¨ Consider the [data] character called "upper case A"; the
following are various glyphs that represent that character:
7 A - Arial
7 A - Times New Roman
7 A - Courier new
7 A - Garamond
7 A - Bodoni
7 A - Park Avenue
7 A - FlamencoD
¨ And so on; notice the concept of a font sneaking in here: a font
is a set of glyphs used to represent a collection of characters
[usually in a similar style]
Copyright ã 2011 by Steven H. Comstock 5 Unicode](https://image.slidesharecdn.com/uncdtalk-170222200741/85/Uncdtalk-5-320.jpg)