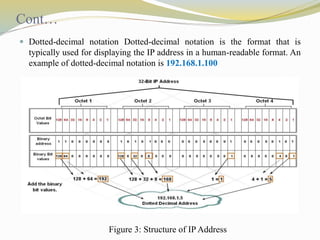
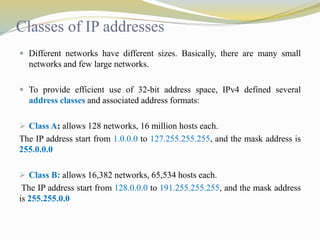
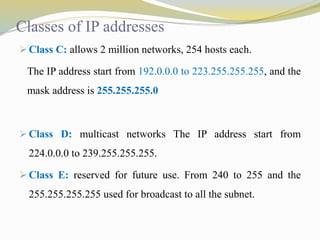
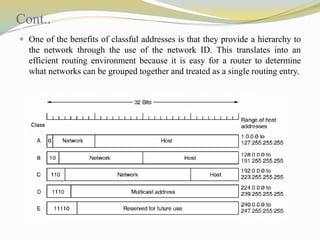
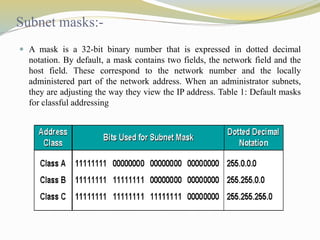
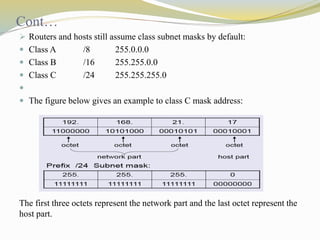
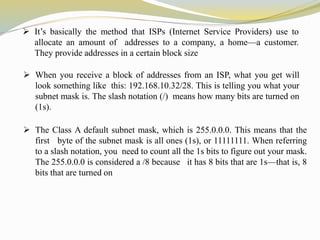
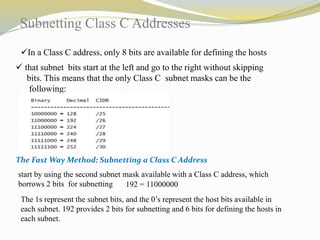
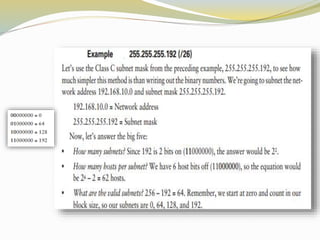
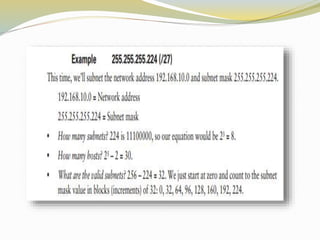
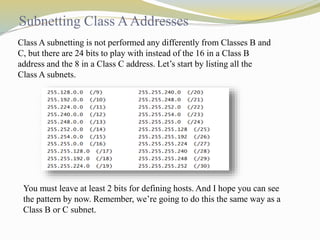
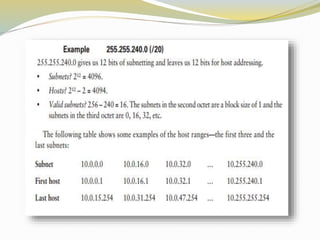
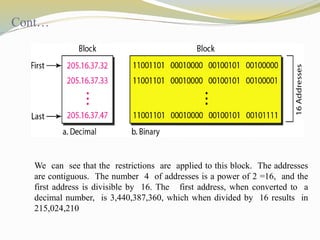
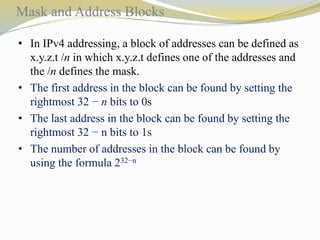
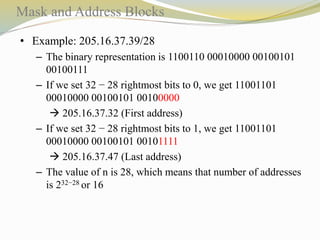
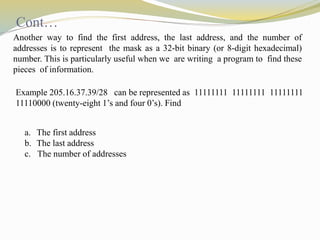
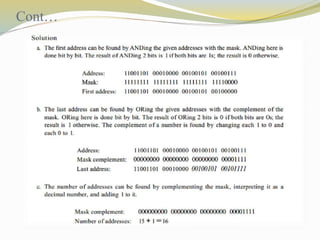
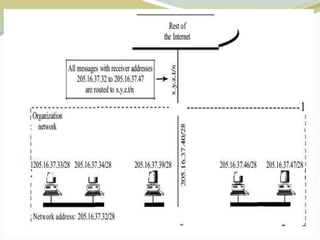
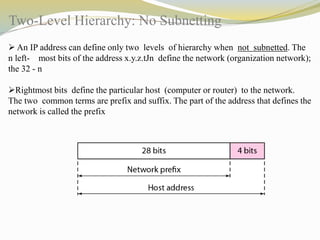
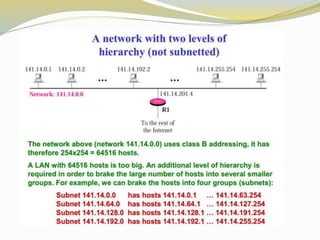
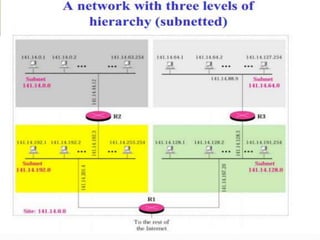
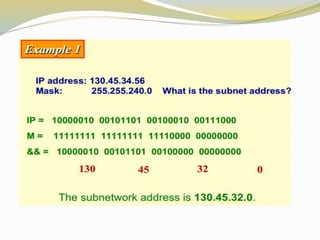
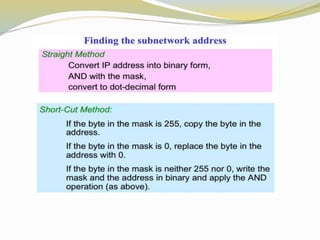
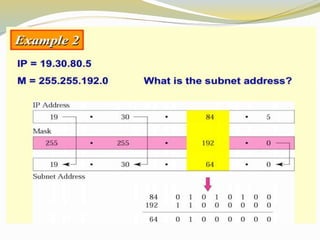
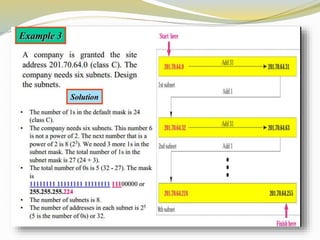
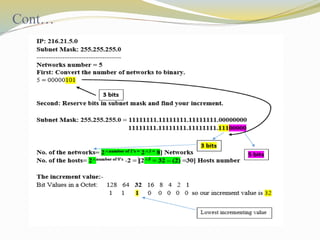
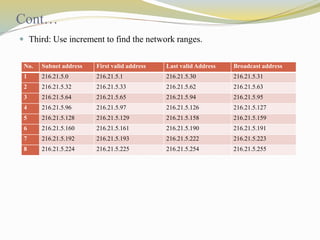
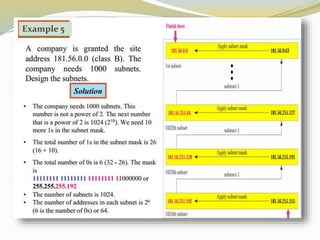
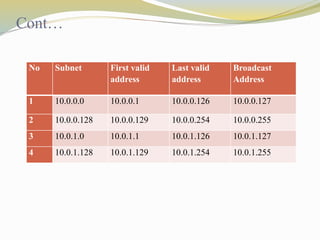
This document discusses the Internet Protocol (IP) version 4 and 6. It describes the key tasks of IP including addressing computers and fragmenting packets. IP version 4 uses 32-bit addresses while IP version 6 uses 128-bit addresses and has improvements like larger address space and better security. The document also covers IP address classes, private addressing, subnetting, Classless Inter-Domain Routing (CIDR), and address blocks.