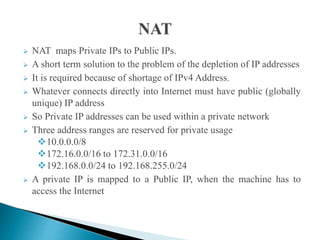
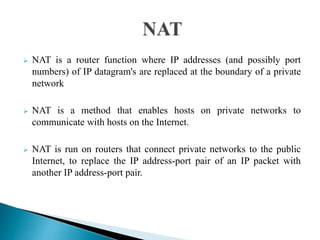
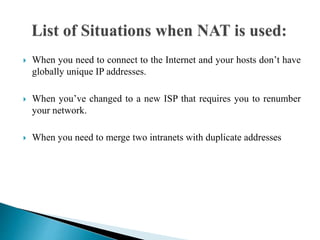
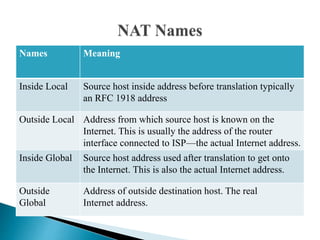
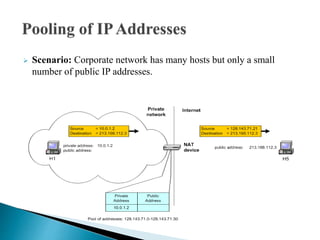
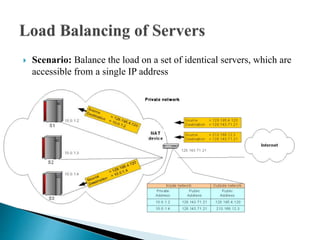
NAT maps private IP addresses to public IP addresses, allowing multiple devices on a private network to share a single public IP address to access the Internet. It is commonly used when there is a shortage of IPv4 addresses. There are different types of NAT, including dynamic NAT which maps private addresses to public addresses on a need basis, and NAPT which allows thousands of devices to share one IP address by also mapping port numbers. NAT solves issues like merging networks with duplicate private addresses and changing ISPs without renumbering an entire network.