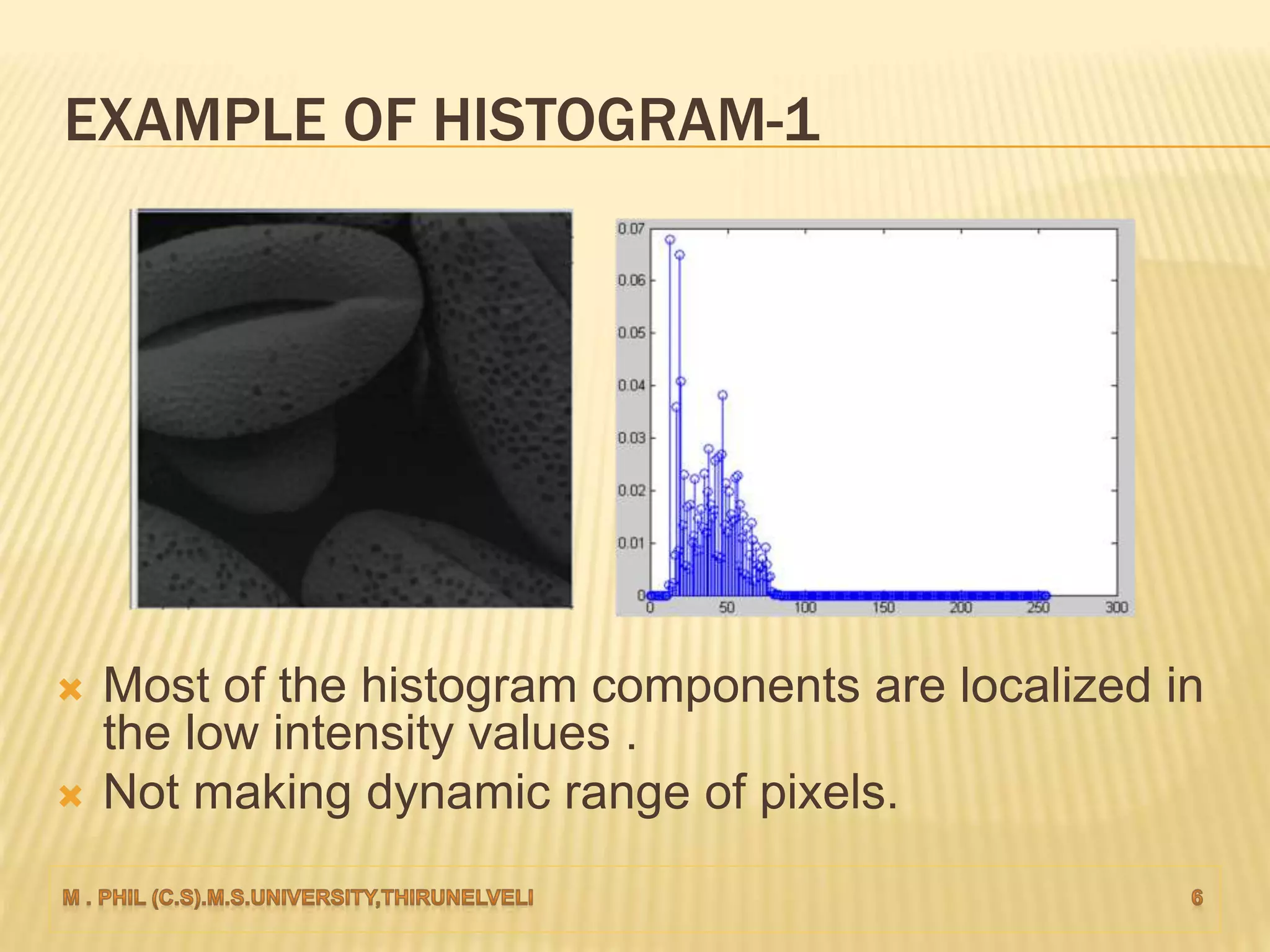
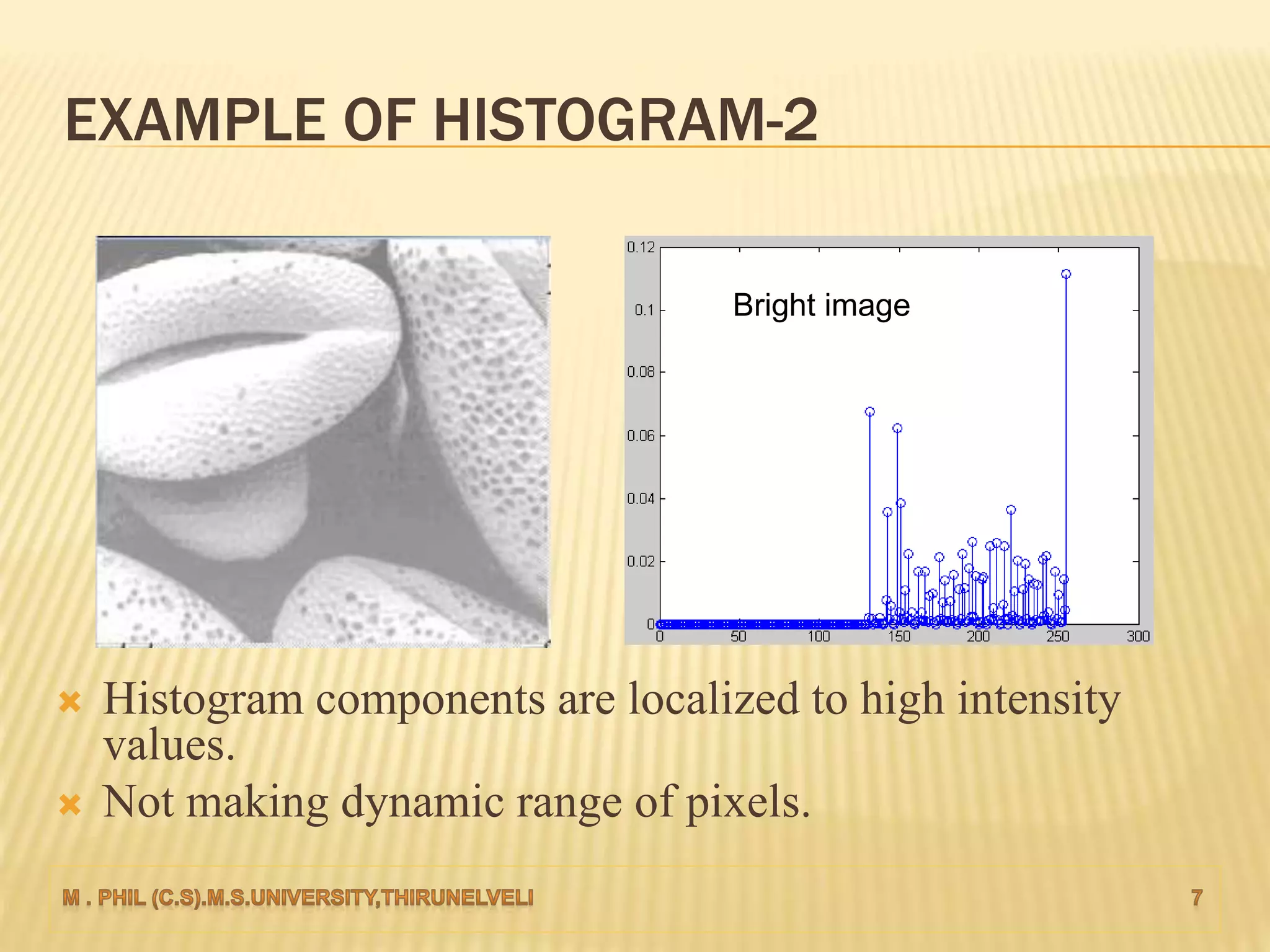
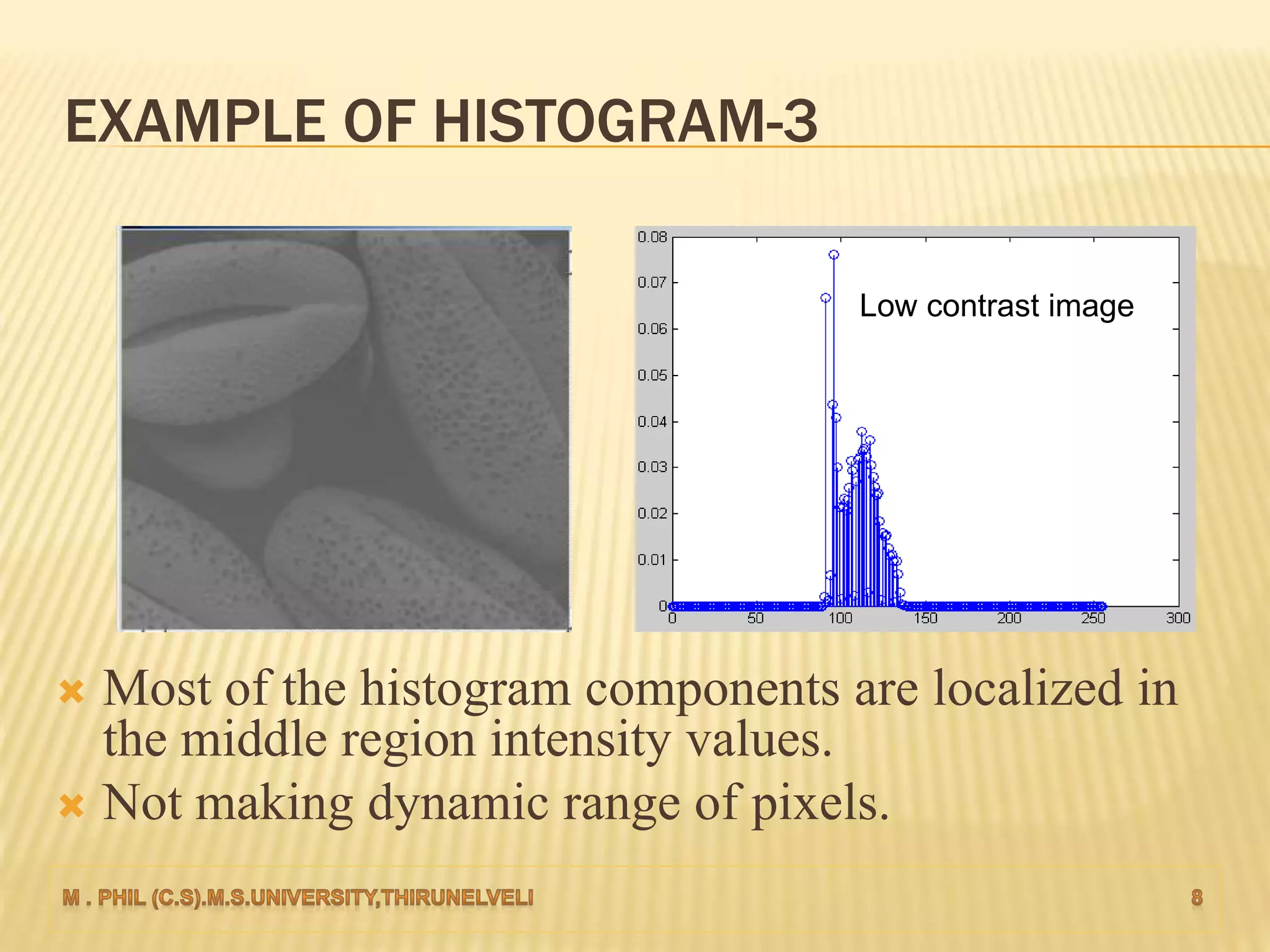
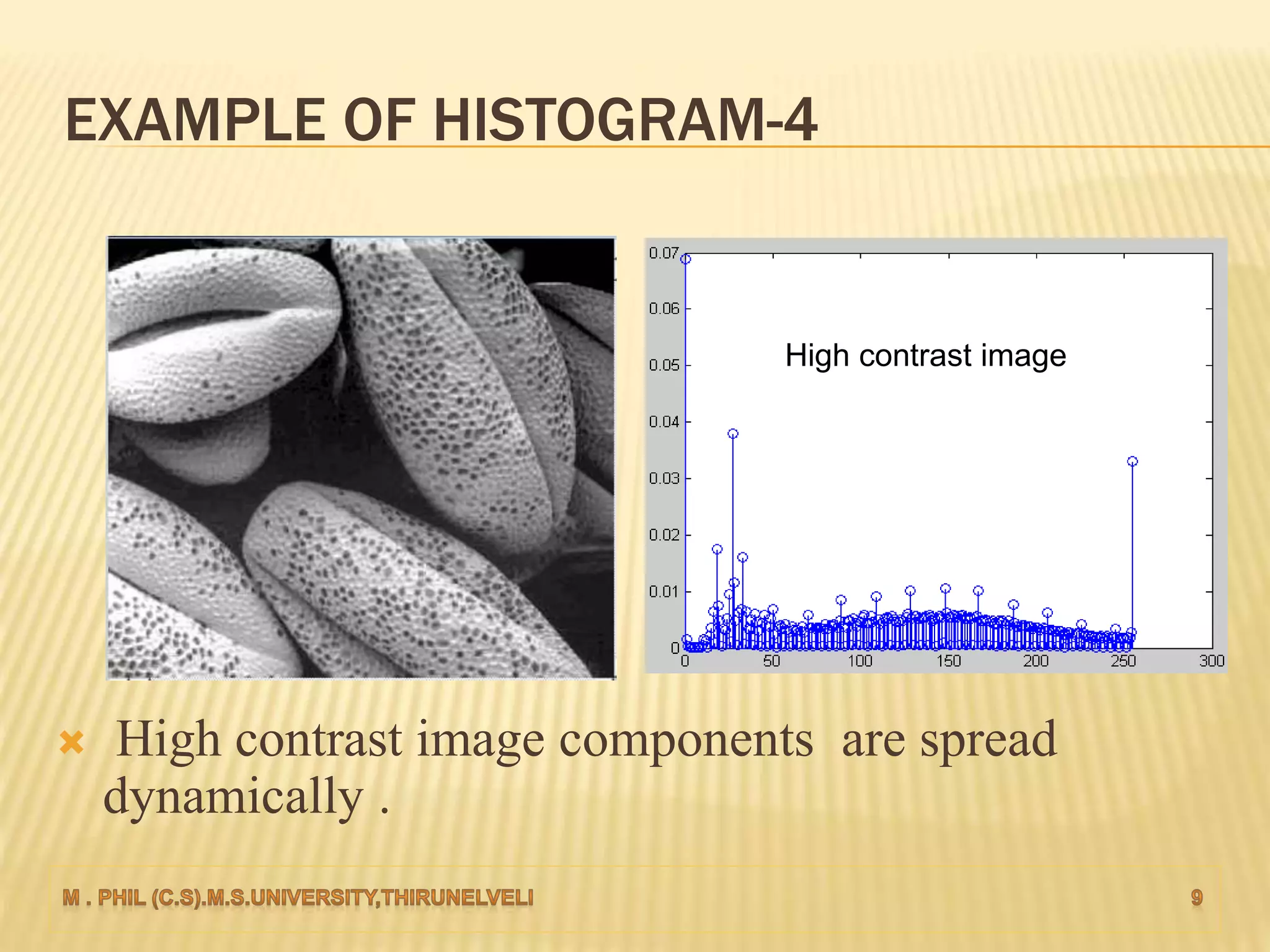
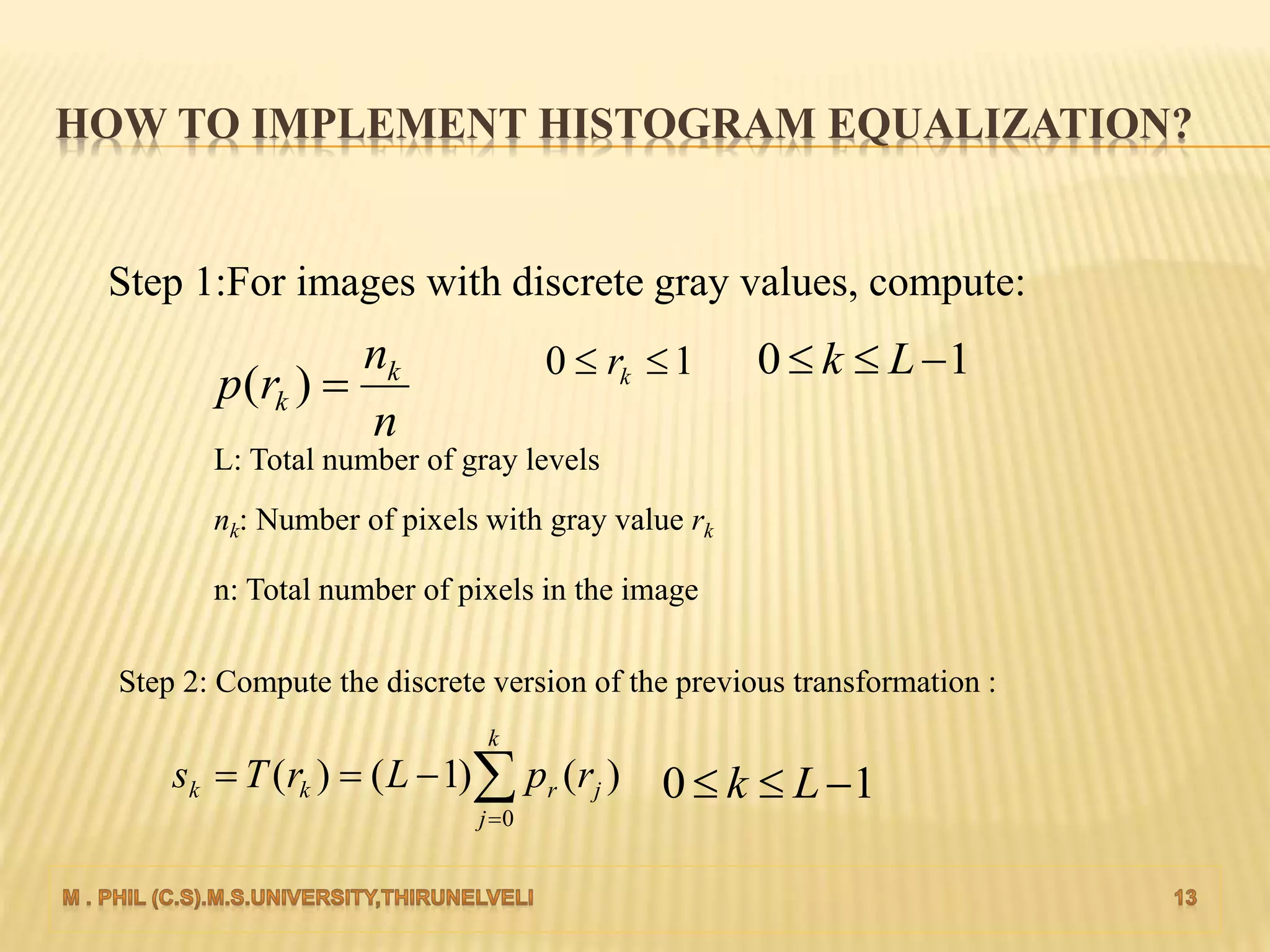
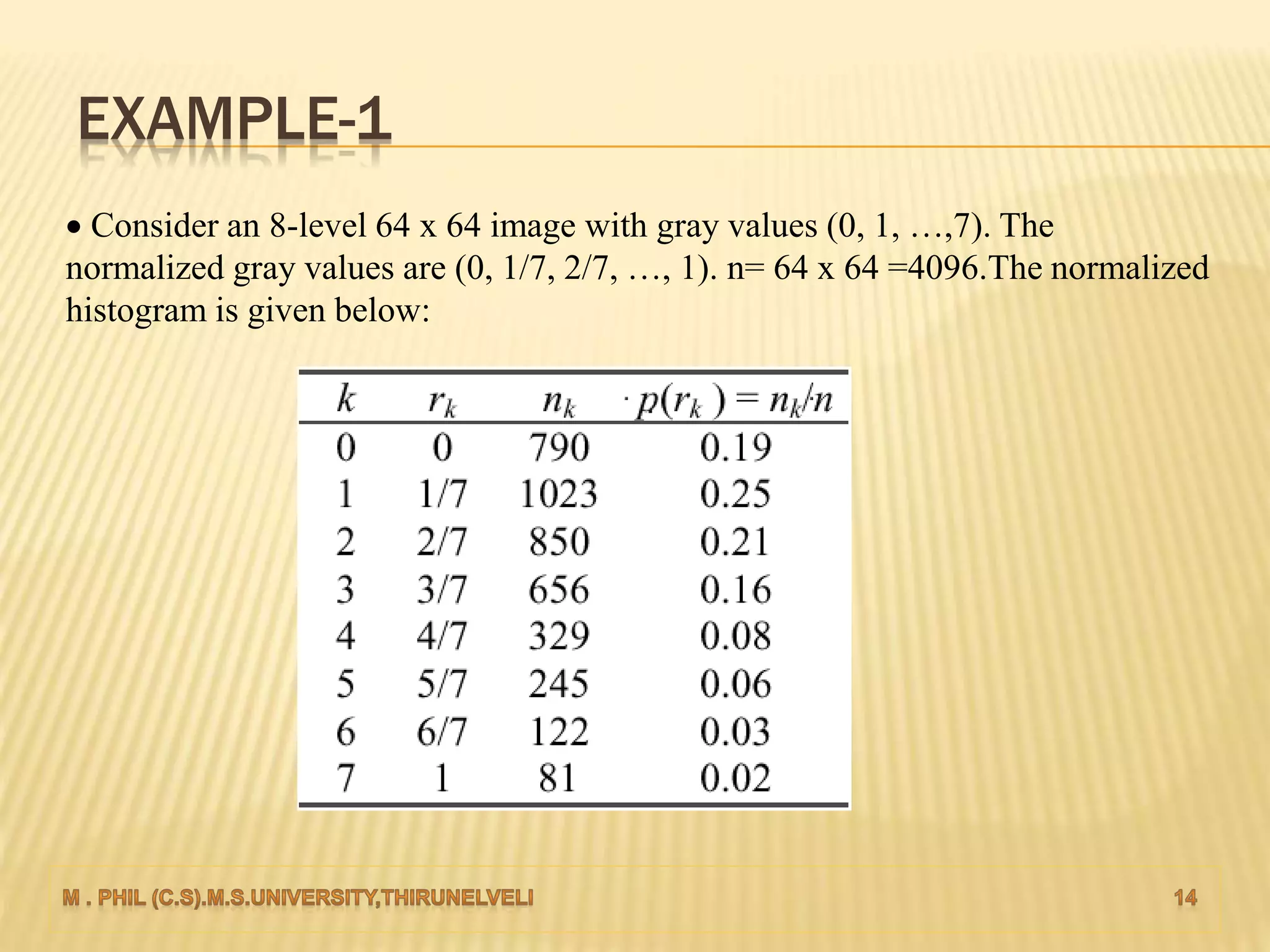
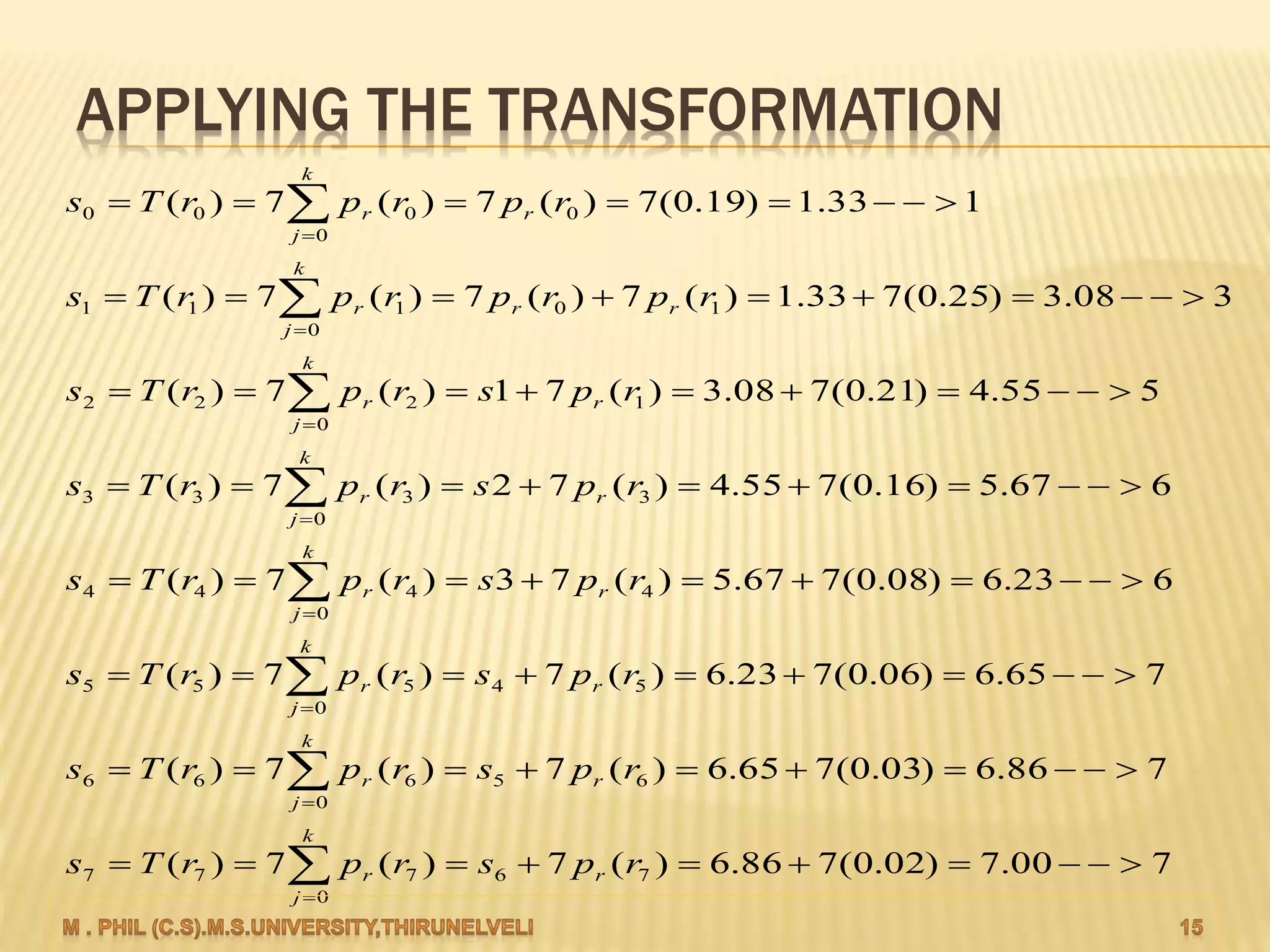
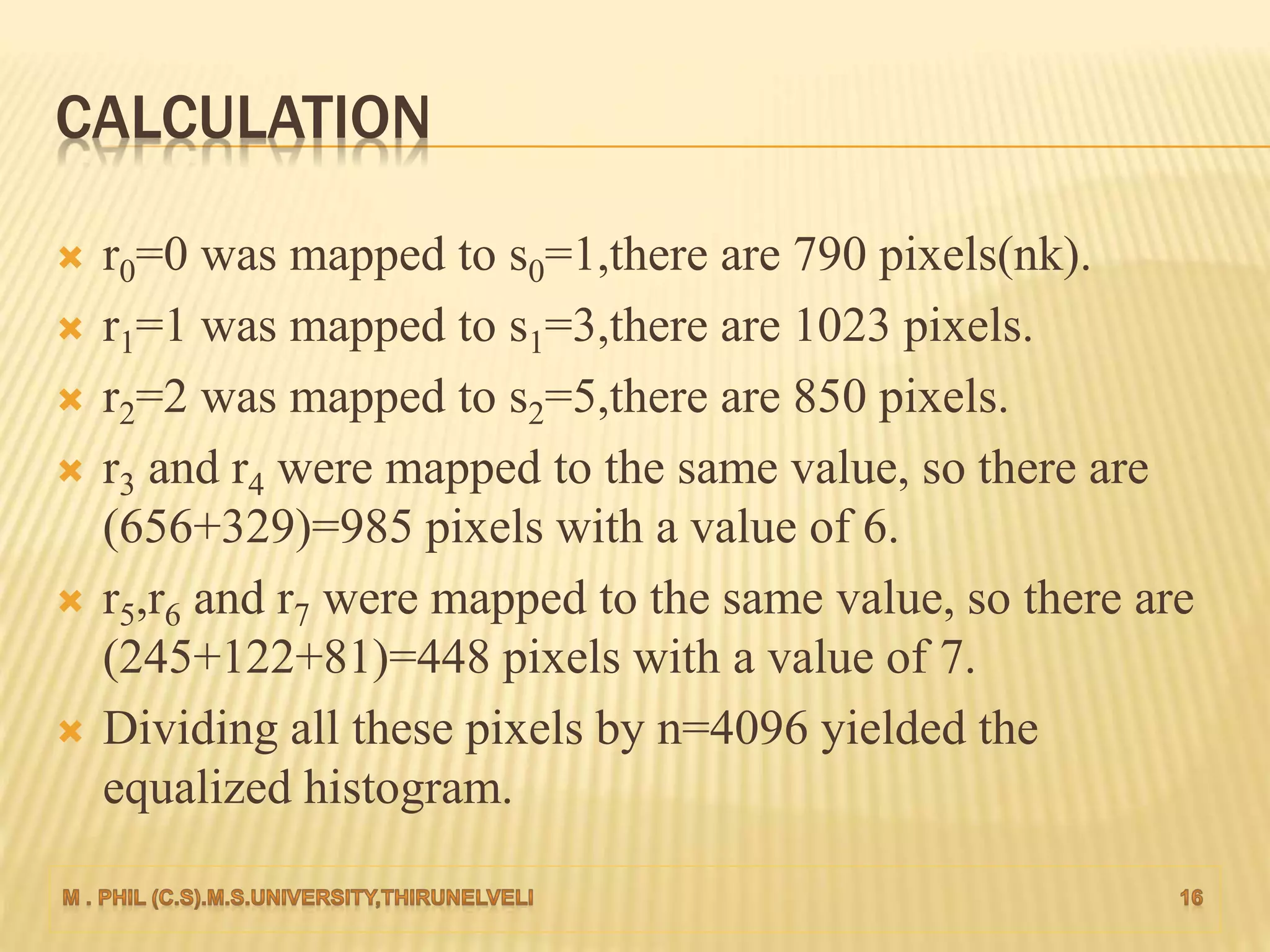
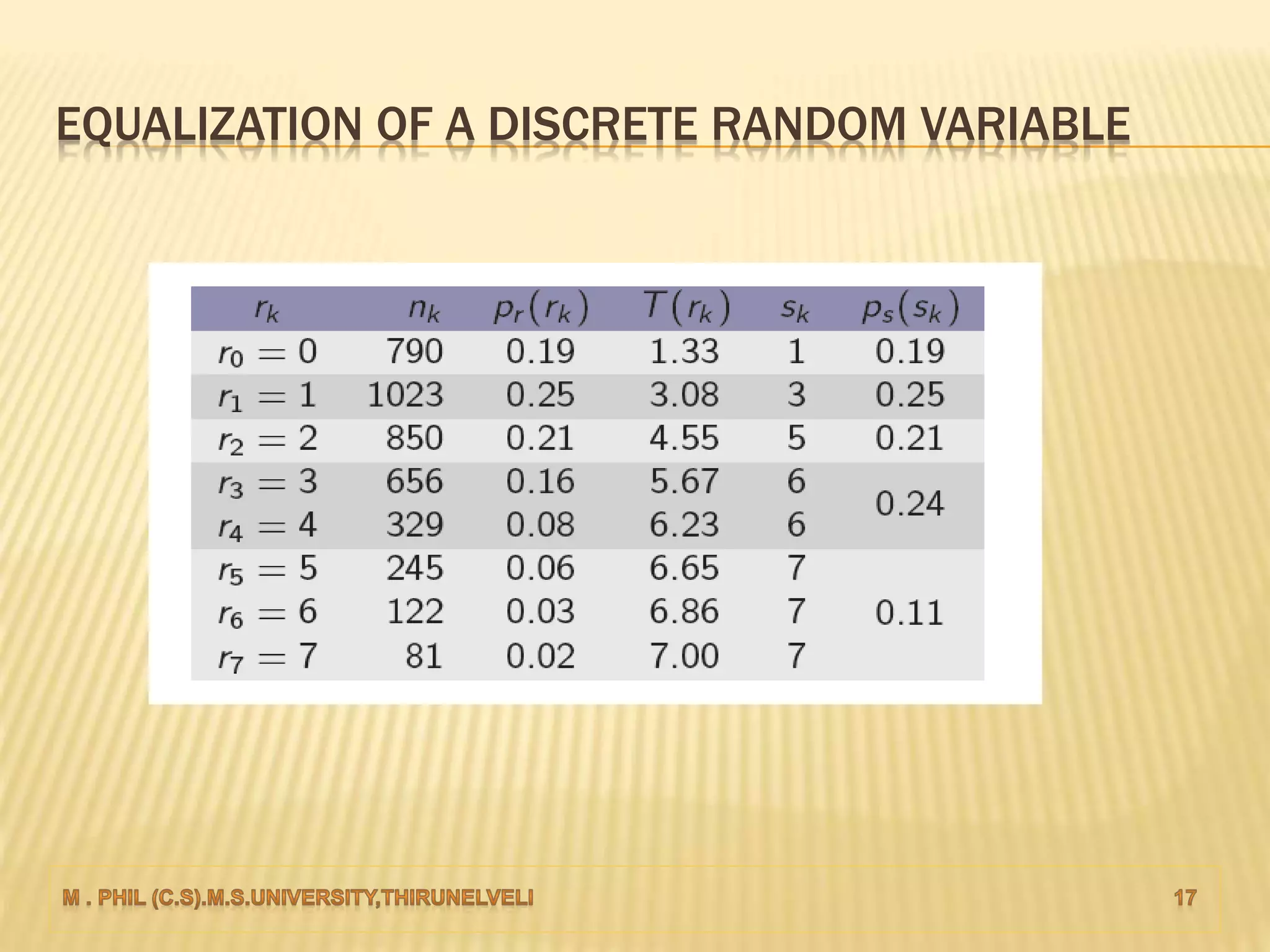
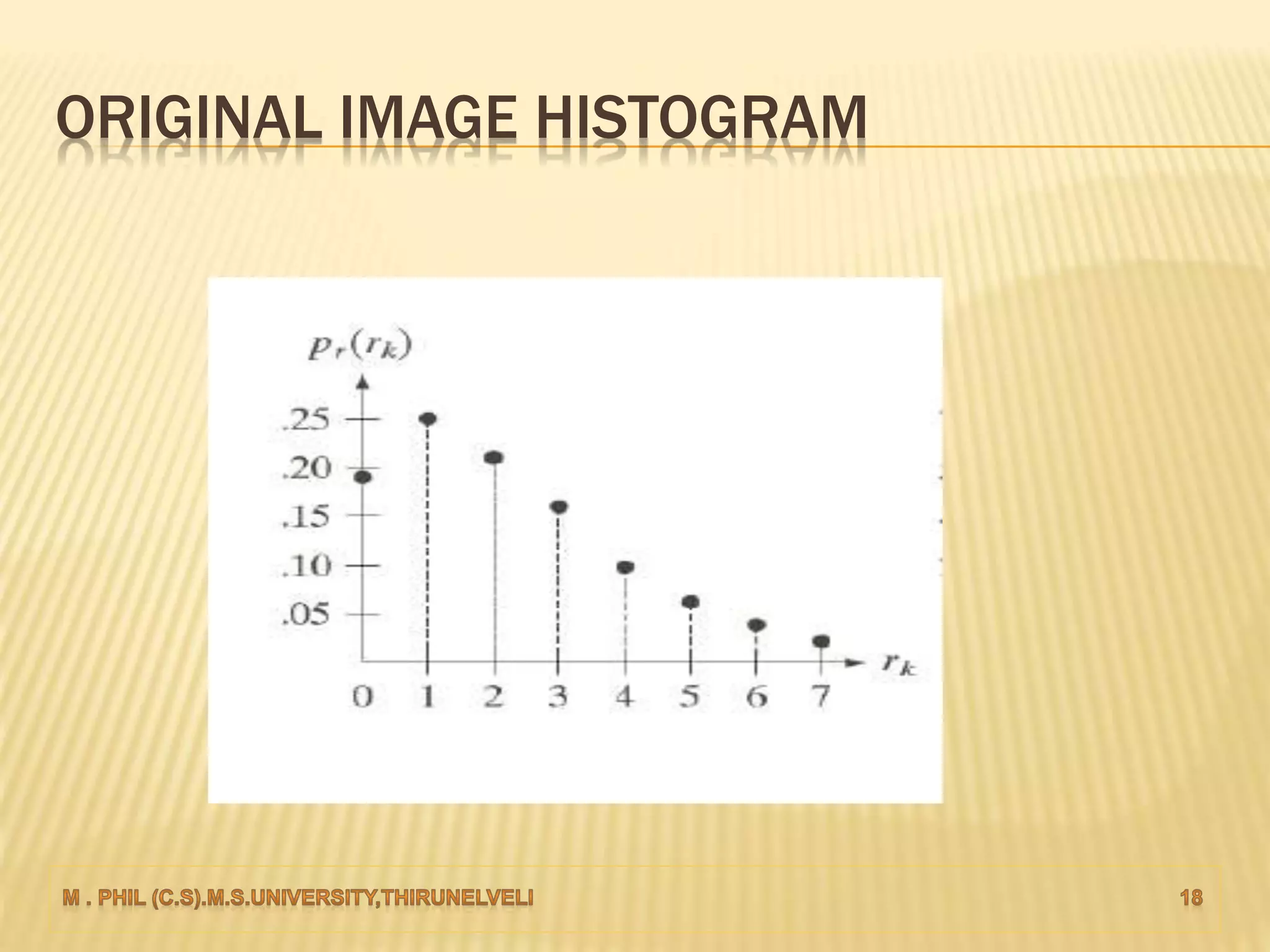
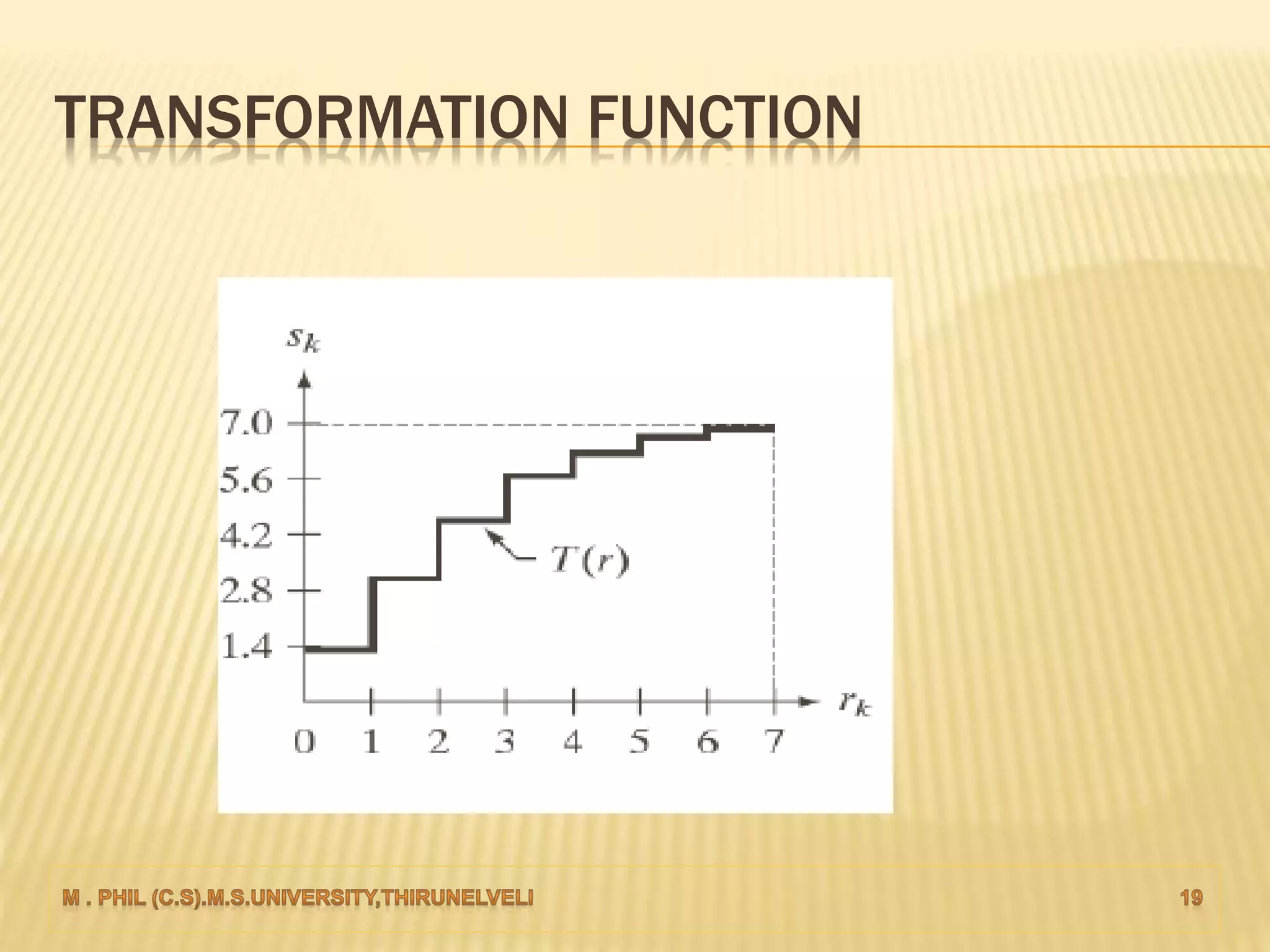
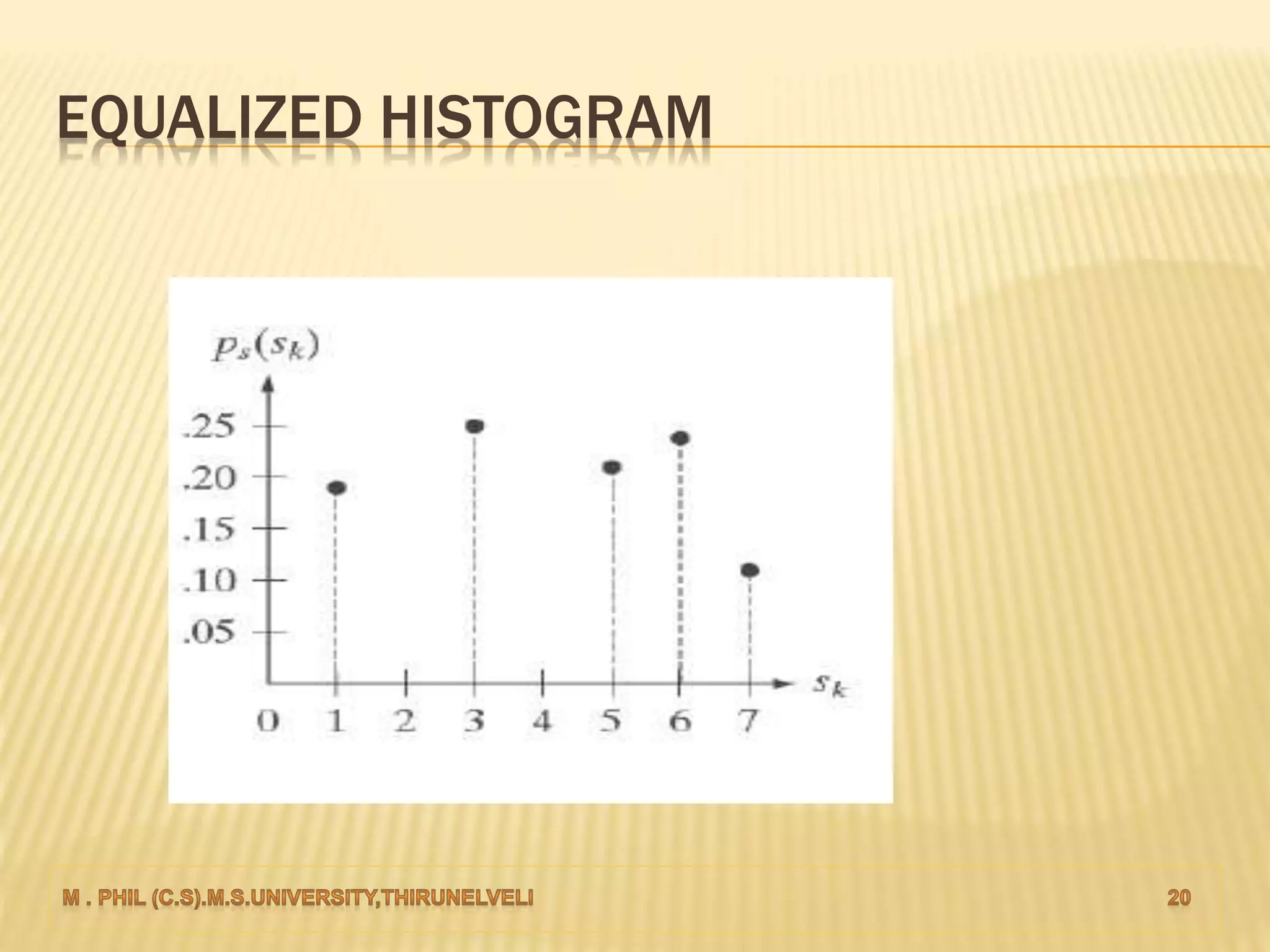
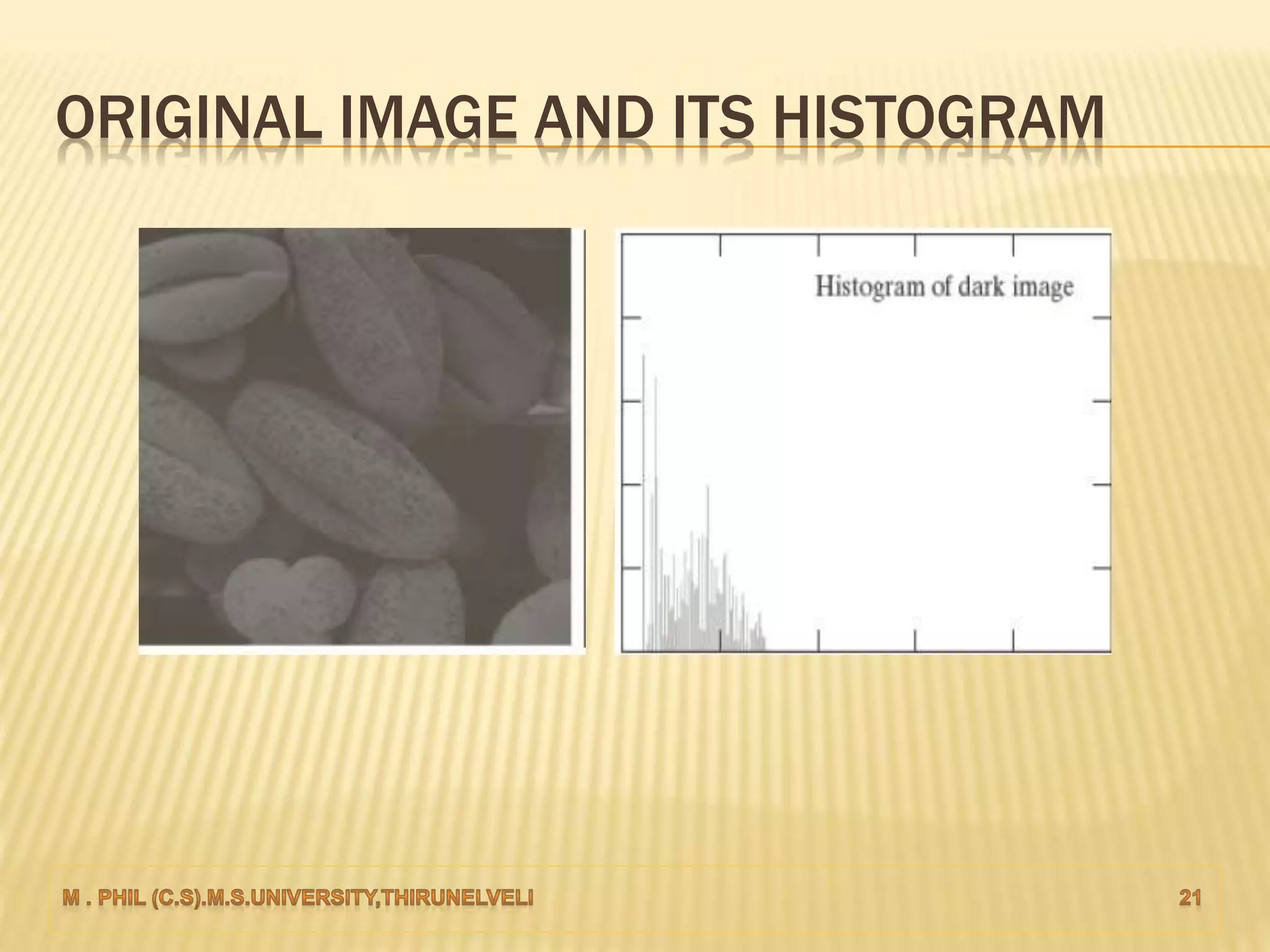
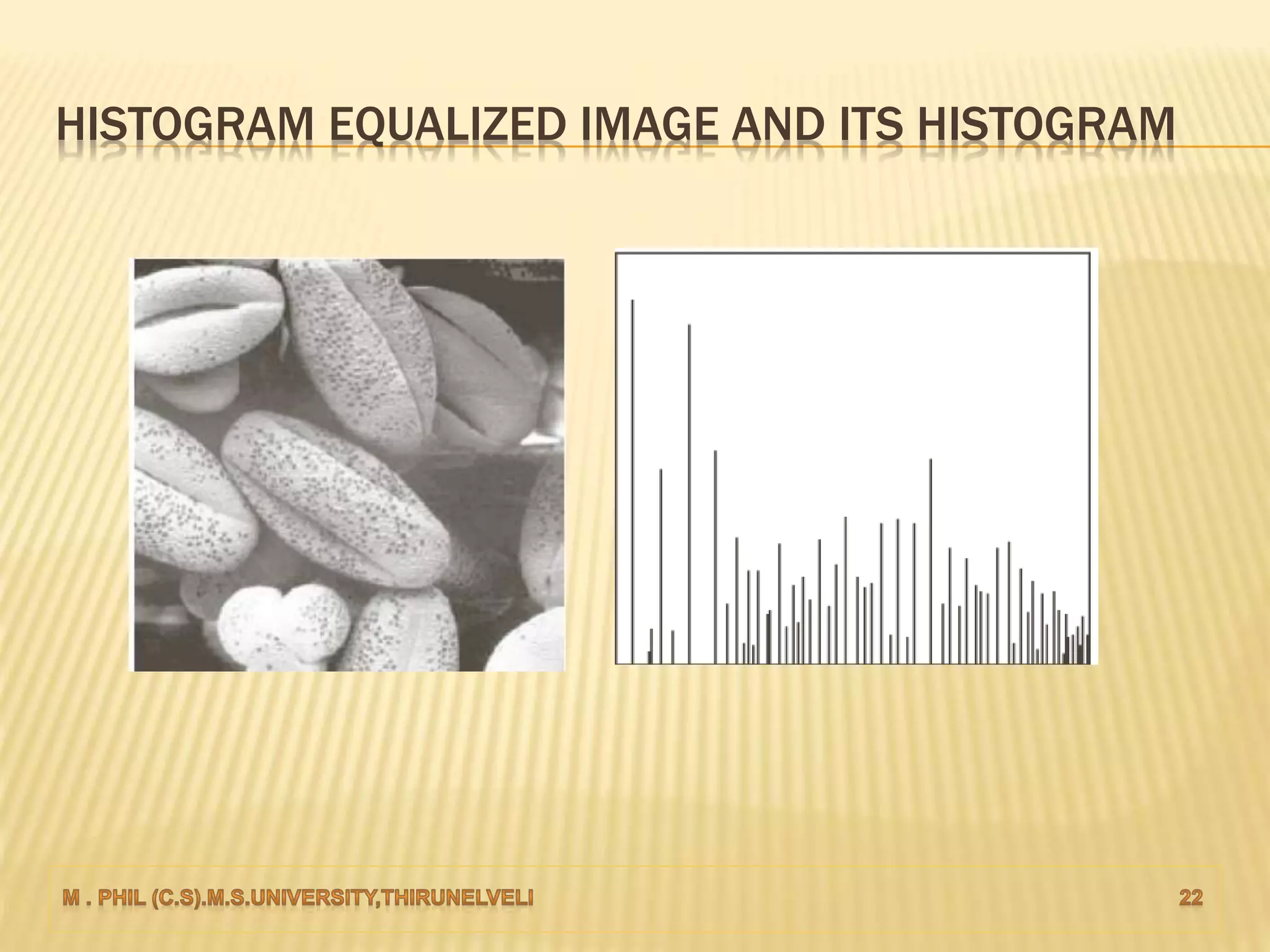
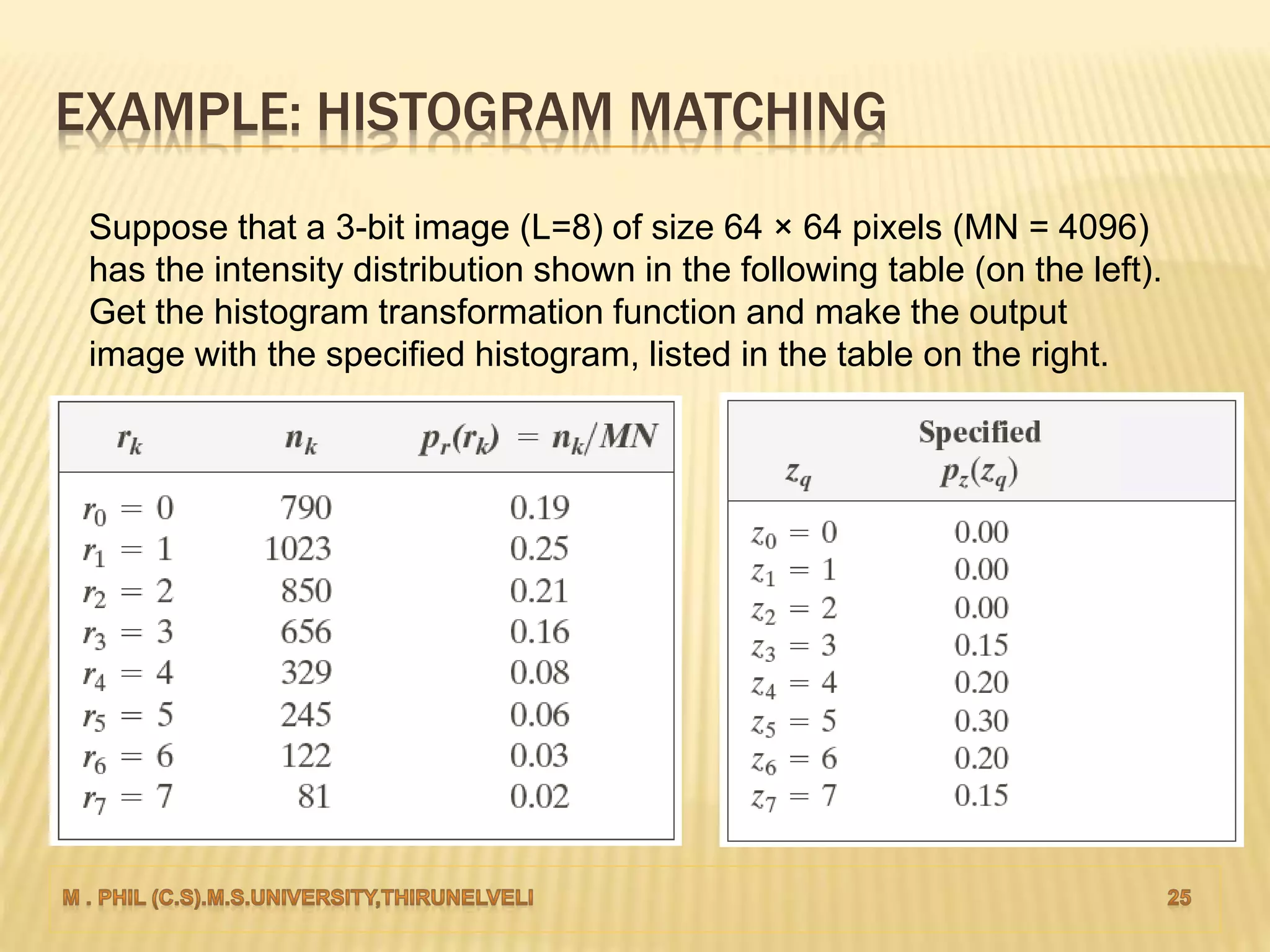
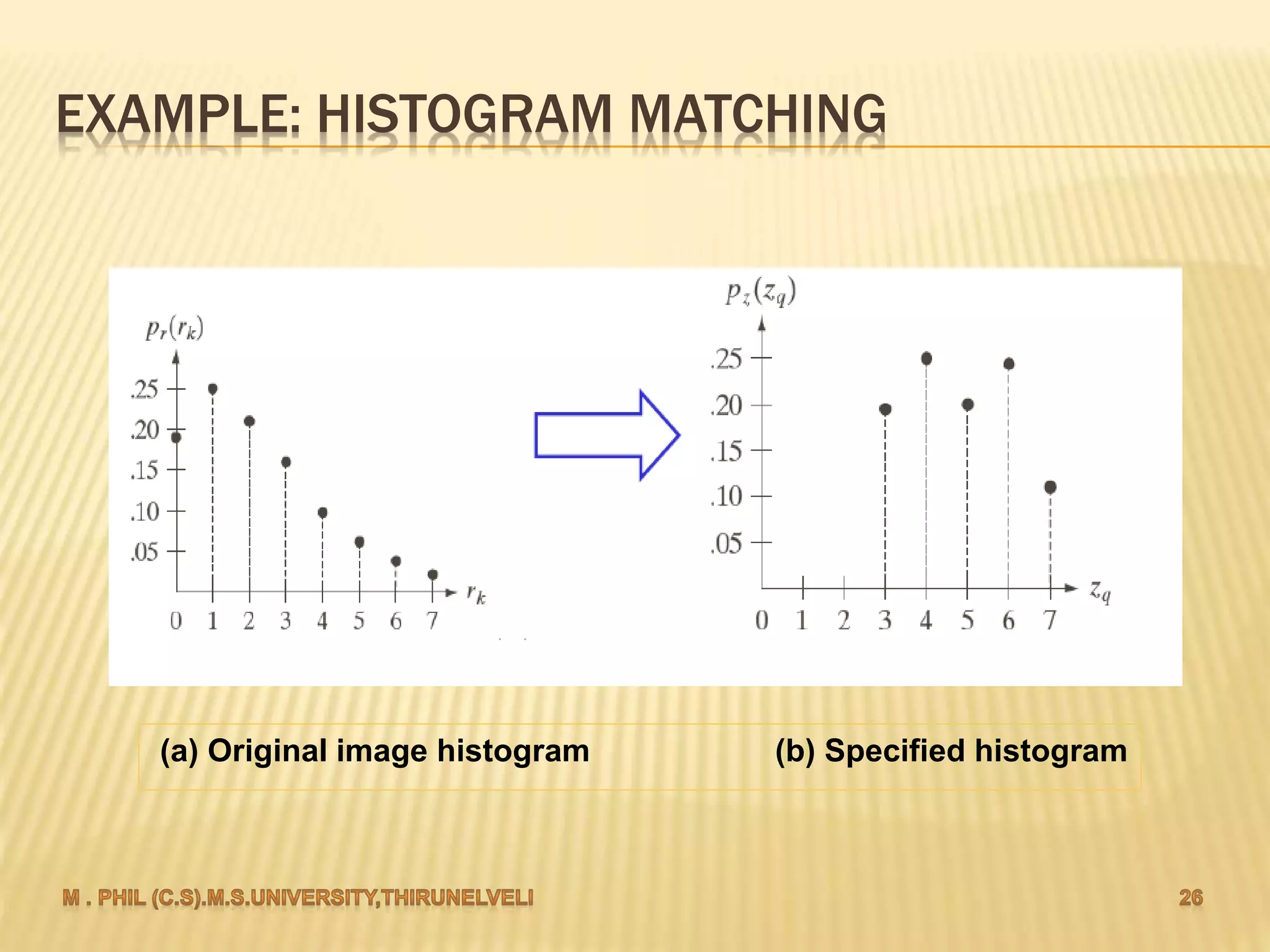
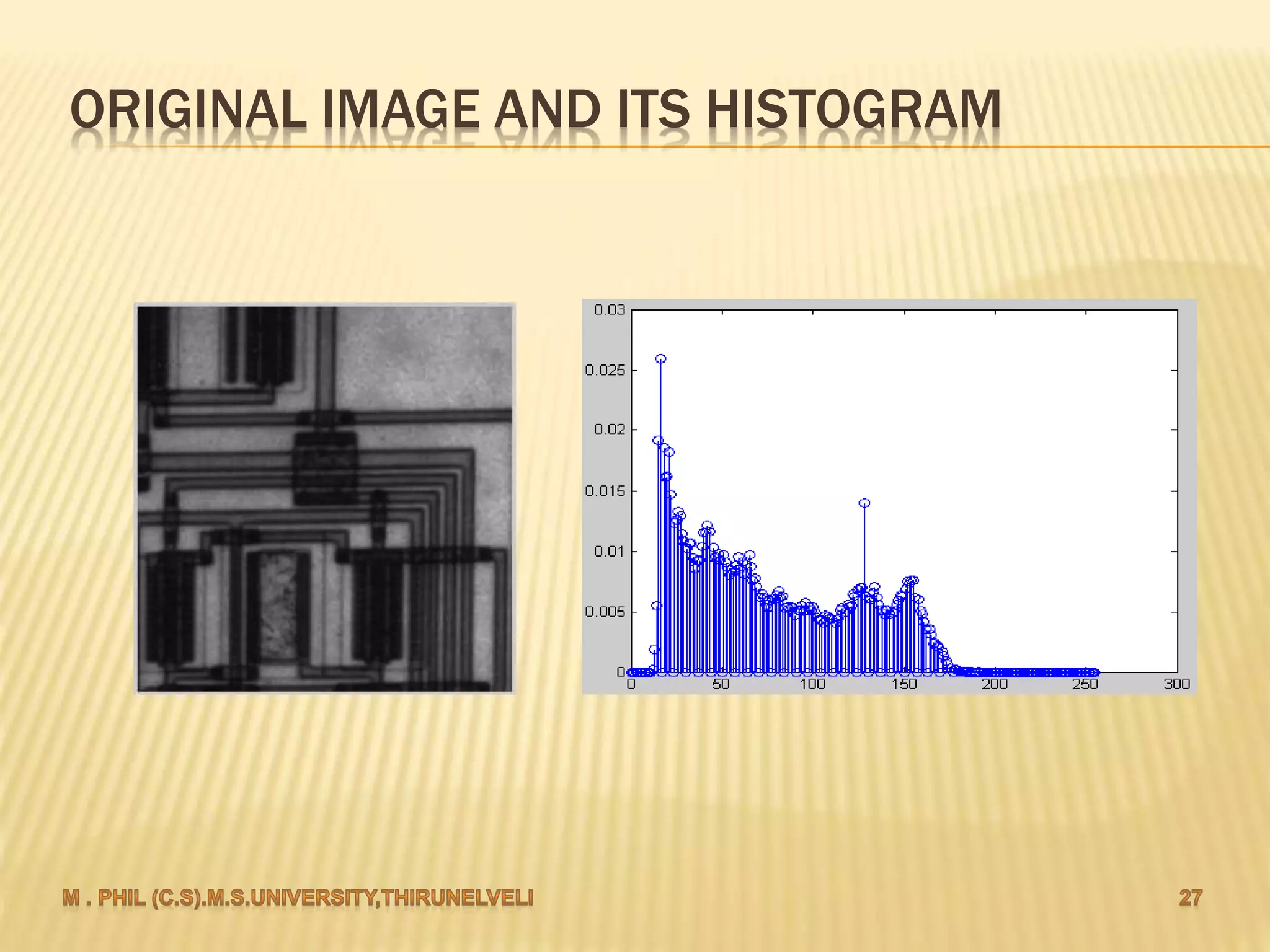
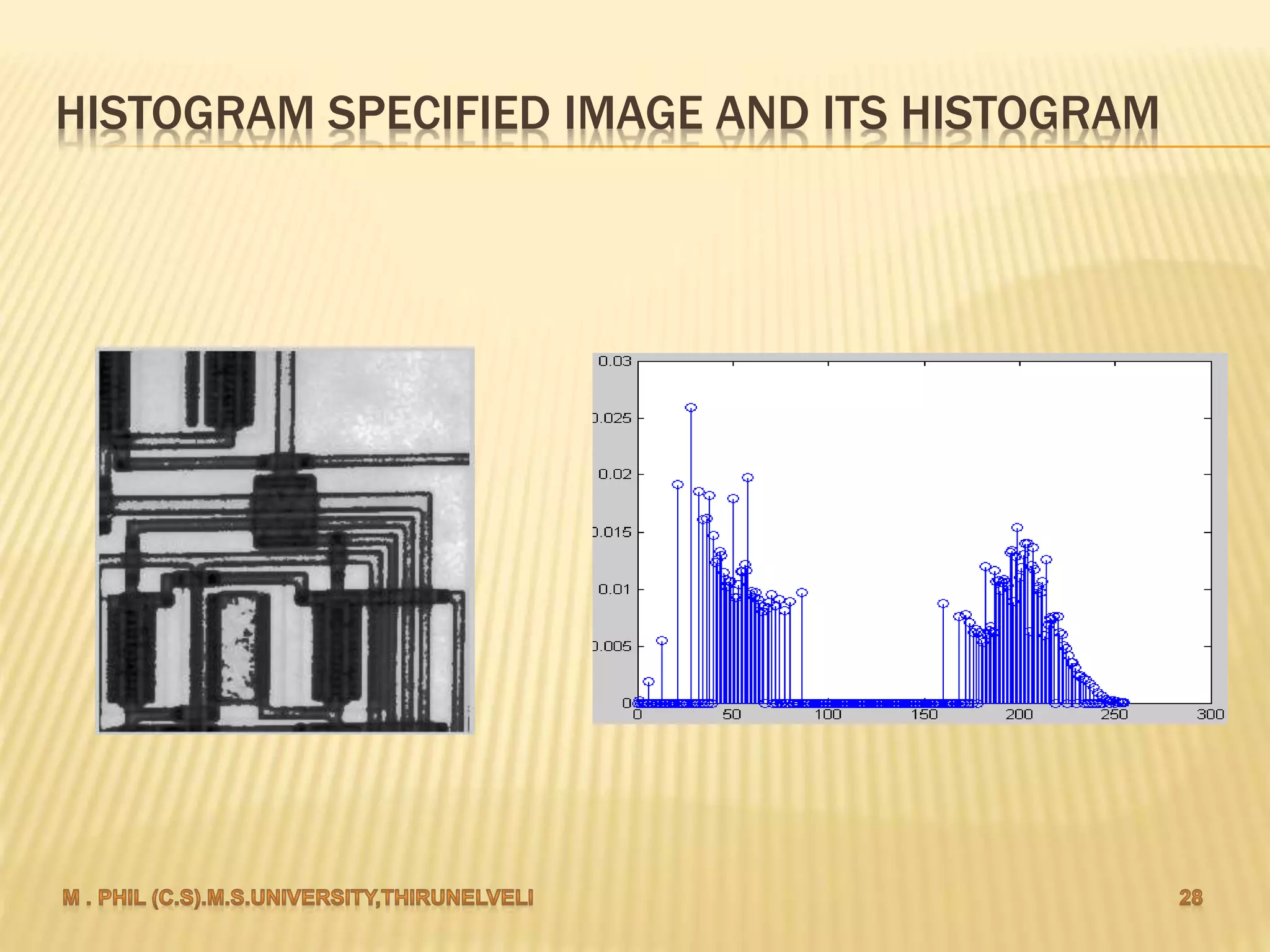
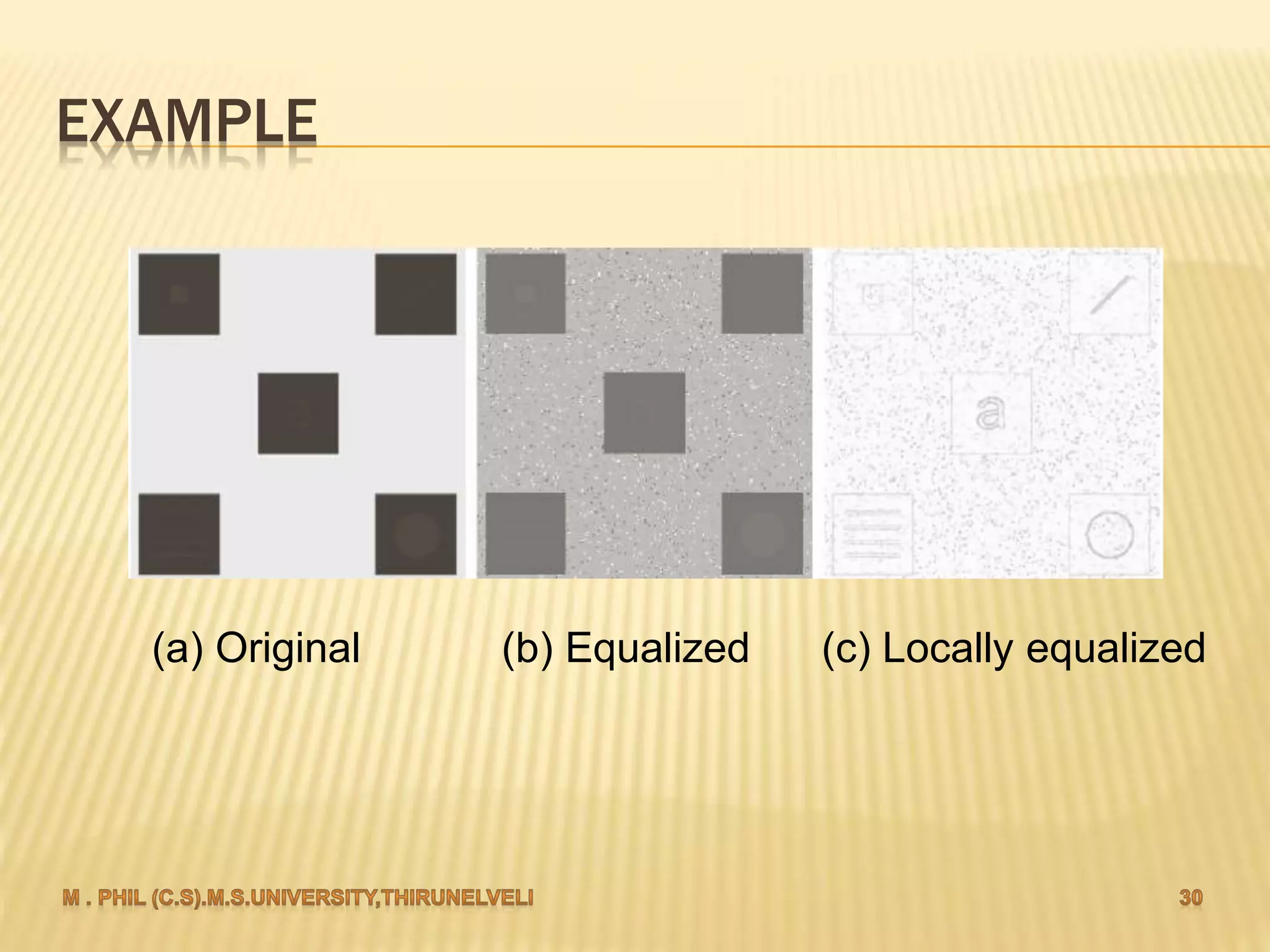
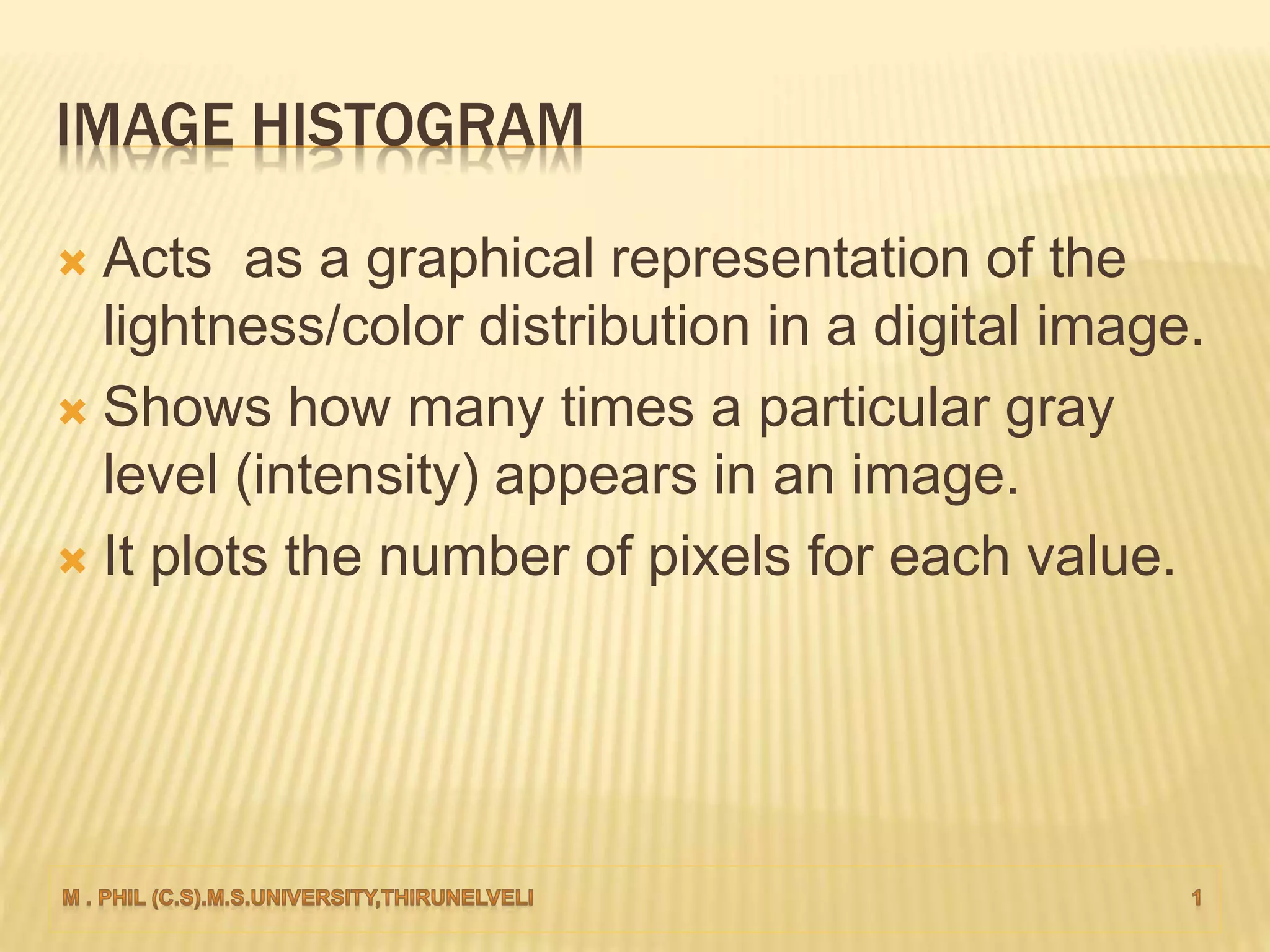
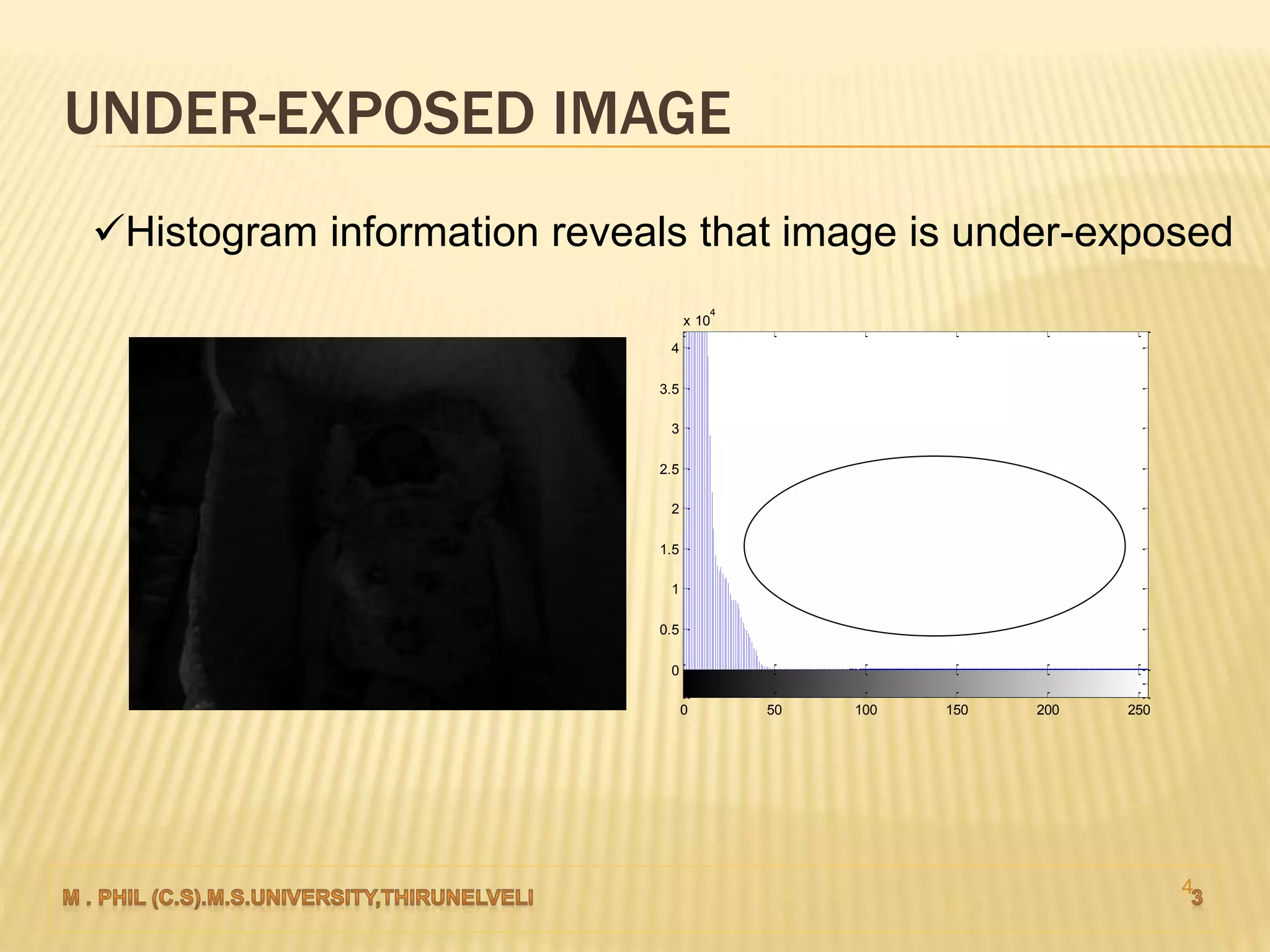
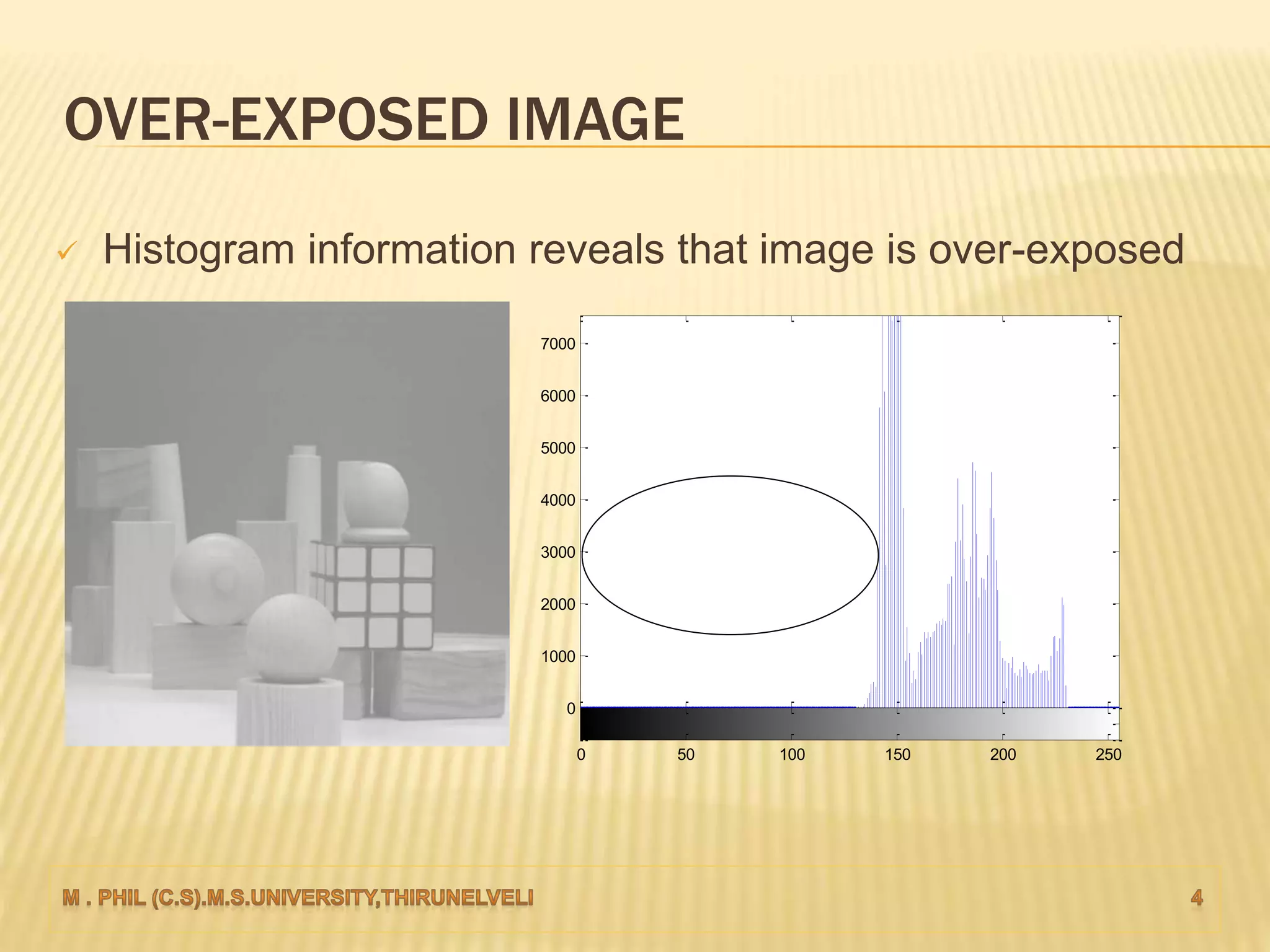
An image histogram represents the distribution of pixel intensities in a digital image. It plots the number of pixels for each tonal value. Histograms can reveal if an image is under-exposed or over-exposed based on where most pixel values are concentrated. Histogram equalization improves contrast by spreading out pixel values across intensity levels. Local histogram equalization applies this within neighborhoods to enhance detail while preserving edges.

![HISTOGRAM PROCESSING
The histogram of a digital image with gray
levels in the range [0, L-1]
Discrete function:
h(rk) = nk
rk - kth gray level
nk - number of pixels in the image having
gray level rk.](https://image.slidesharecdn.com/histogrambasedenhancement-161025174243/75/Histogram-based-enhancement-6-2048.jpg)