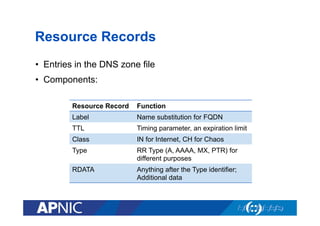
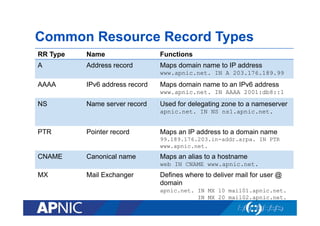
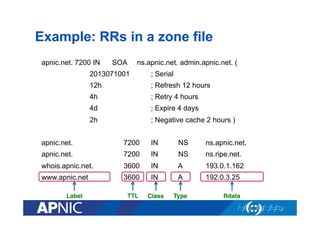
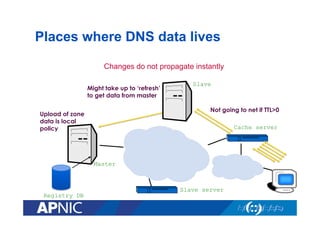
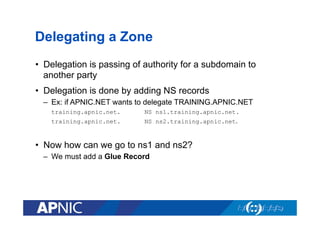
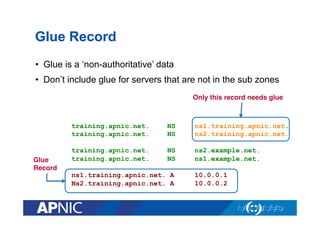
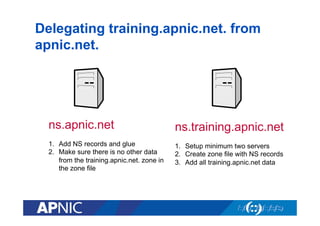
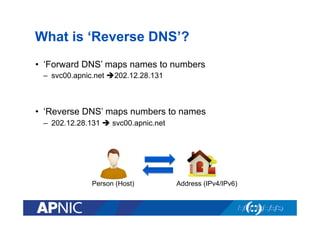
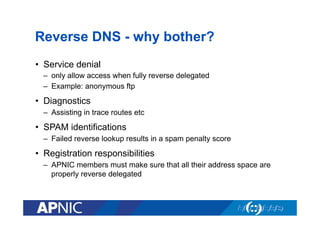
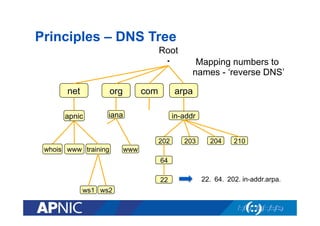
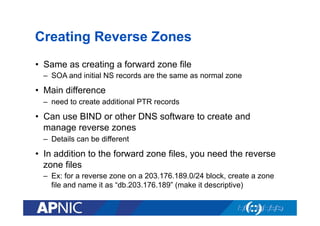
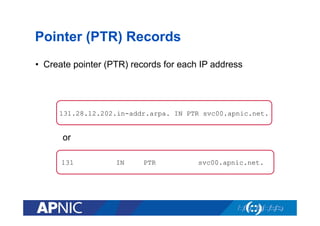
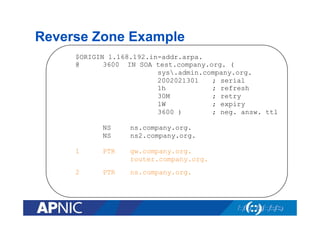
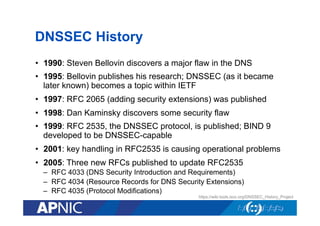
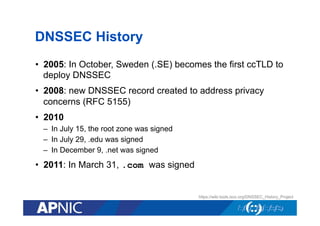
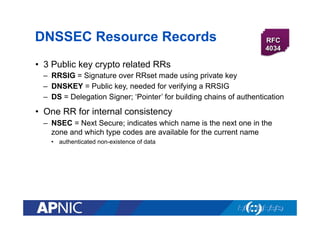
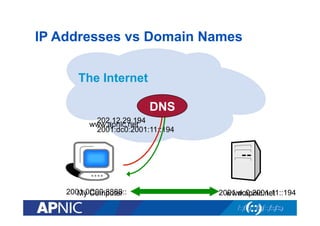
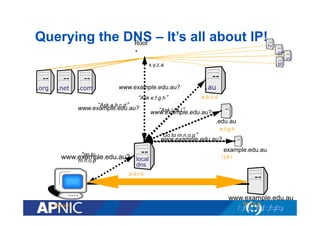
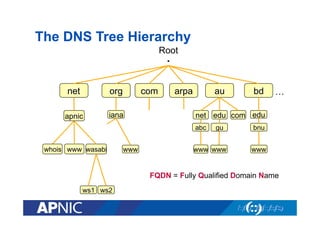
This document provides an overview and introduction to DNS and DNSSEC. It begins with introducing the presenter, Nurul Islam Roman, and his background and areas of expertise. The overview section lists the topics to be covered, including DNS overview, forward and reverse DNS, DNS security overview, TSIG, and DNSSEC. The document then delves into explanations of DNS overview, how it works, its features and components. It also covers IP addresses vs domain names, the DNS tree hierarchy, domains, root servers, resolvers, authoritative and recursive nameservers. Finally, it discusses resource records, common RR types, reverse DNS, delegation, glue records and responsibilities around APNIC and ISPs for reverse delegations.
![Old Solution: hosts.txt
• A centrally-maintained file, distributed to all hosts on the
Internet
• Issues with having just one file
–
–
–
–
–
–
Becomes huge after some time
Needs frequent copying to ALL hosts
Consistency
Always out-of-date
Name uniqueness
Single point of administration
// hosts.txt
SERVER1
WEBMAIL
FTPHOST
128.4.13.9
4.98.133.7
200.10.194.33
This feature still exists:
[Unix] /etc/hosts
[Windows] c:windowshosts](https://image.slidesharecdn.com/dnsdnssecbynurulislam-131201222818-phpapp02/85/DNS-DNSSEC-by-Nurul-Islam-7-320.jpg)
![Root Servers
• The top of the DNS hierarchy
• There are 13 root name servers operated around the world,
with names from [a-m].root-servers.net
• There are more than 13 physical root name servers
– Each rootserver has an instance deployed via anycast
• Root hints file come in many names (db.cache, named.root,
named.cache, named.ca)
– Get it from ftp.rs.internic.net
• See root-servers.org for more detail](https://image.slidesharecdn.com/dnsdnssecbynurulislam-131201222818-phpapp02/85/DNS-DNSSEC-by-Nurul-Islam-13-320.jpg)