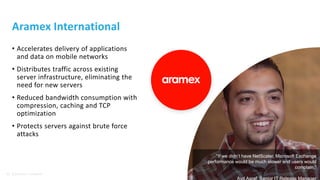
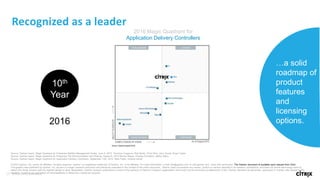
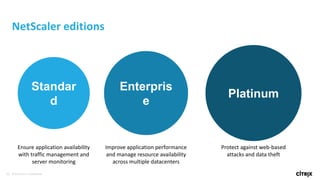
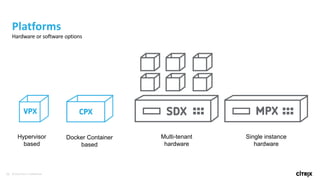
This document discusses how Citrix NetScaler delivers solutions to address common business challenges related to application delivery, including technical debt, hybrid cloud management, reliability, performance, and security issues. It provides an overview of NetScaler's capabilities such as cloud native elasticity, high performance, hybrid SSL support, AWS AutoScale integration, multi-NIC/IP support in Azure, server monitoring and load management, SSL offloading, application acceleration, and more. Case studies are presented showing how NetScaler has helped customers like Washington State DOT and Aramex International improve application availability, performance, and security.