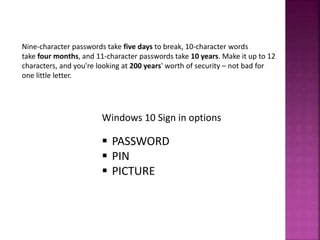
This document discusses data security and password protection. It explains that passwords should be strong, with a minimum of 6 characters including letters, numbers, and symbols. Longer passwords are more secure, with 12+ character passwords being very secure. The document also discusses encryption, explaining that encryption translates plain text into encrypted ciphertext using a key, and the same key is needed for decryption. Encryption securely protects data by allowing only authorized parties with the key to access it. Common encryption methods include DES, RSA, AES, Blowfish and Twofish. Free encryption tools include Veracrypt, Bitlocker and AxCrypt.