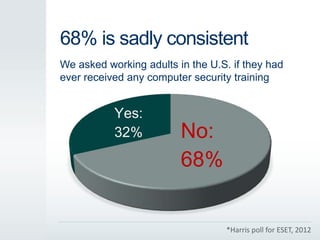
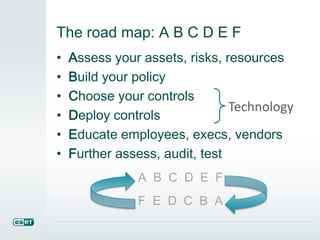
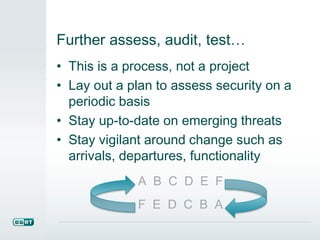
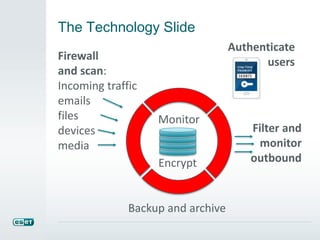
The document discusses the critical need for computer security training, highlighting that a significant majority of U.S. adults have not received such training, which leads to numerous security vulnerabilities. It outlines the steps for improving security awareness, including assessing risks and educating employees, emphasizing that a well-informed workforce can reduce the impact of cyber threats. The document underscores that effective security policies and continuous training are necessary for organizations to protect sensitive information and maintain compliance with industry regulations.