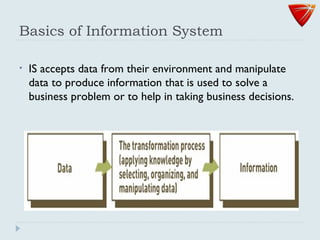
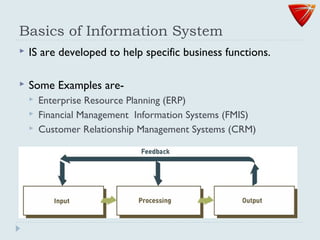
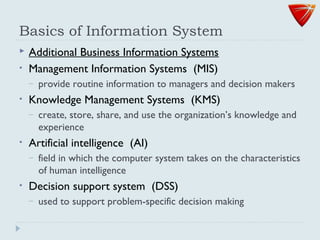
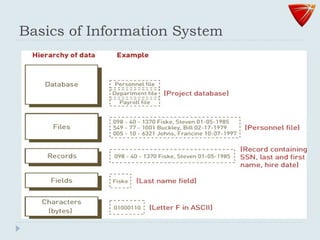
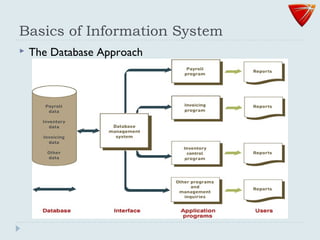
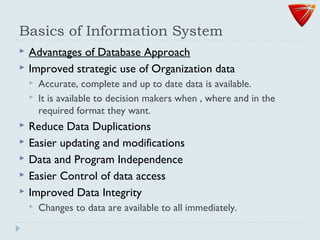
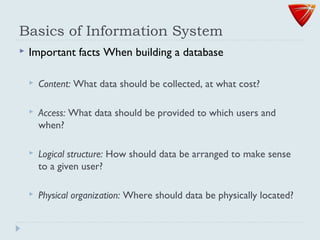
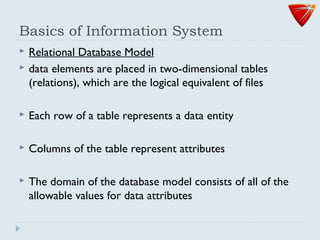
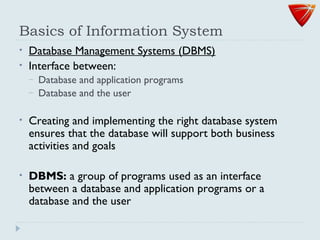
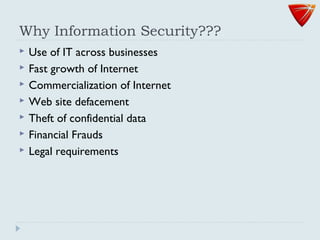
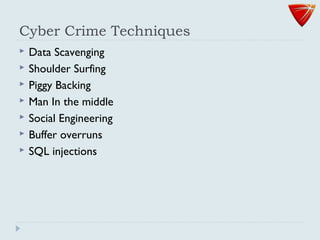
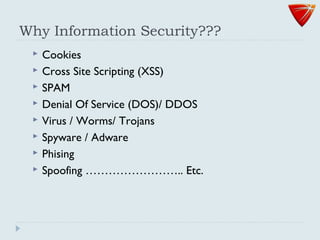
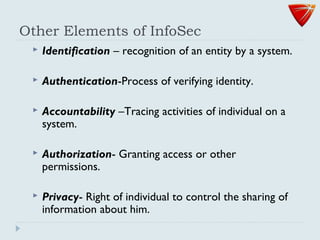
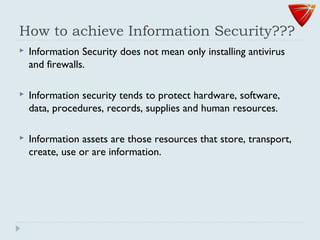
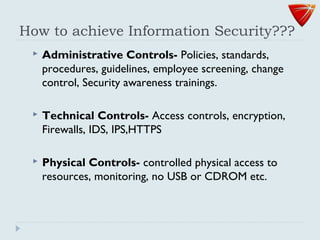
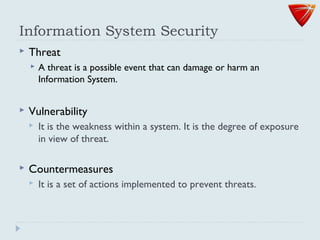
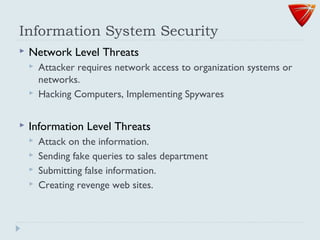
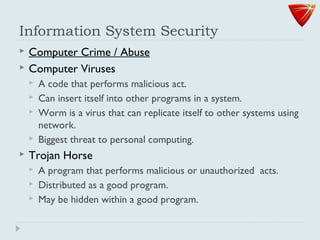
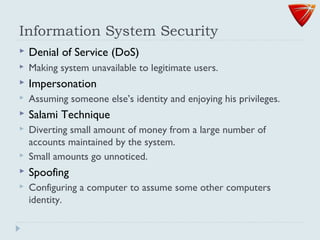
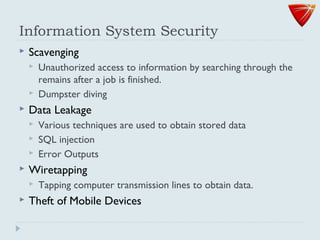
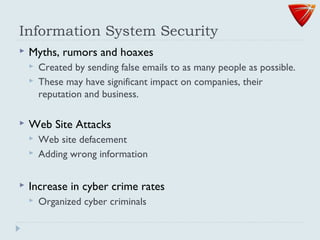
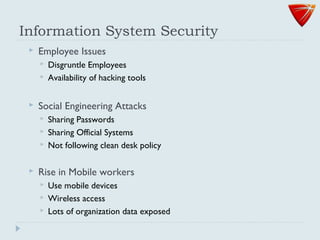
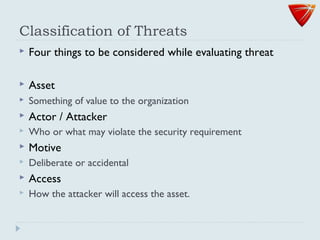
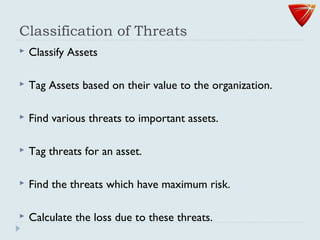
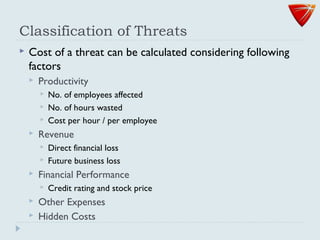
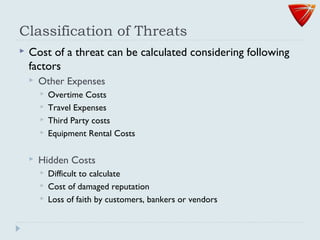
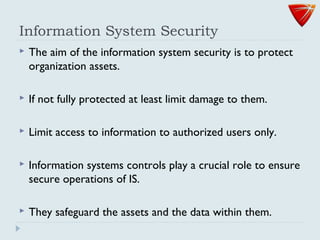
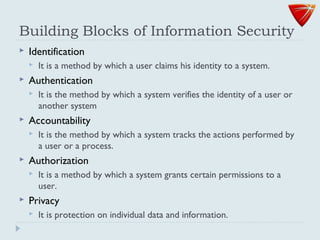
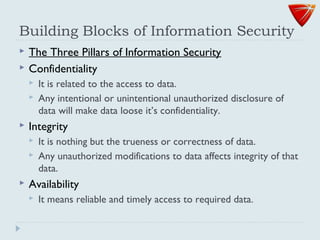
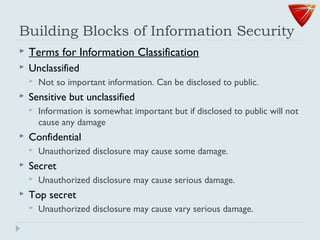
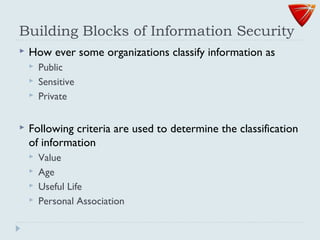
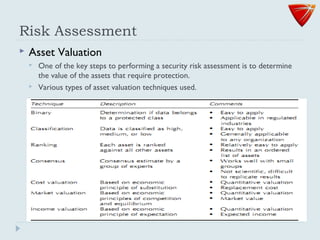
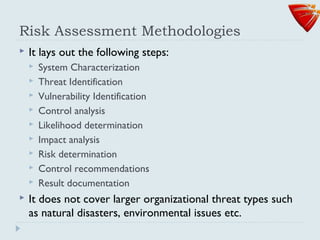
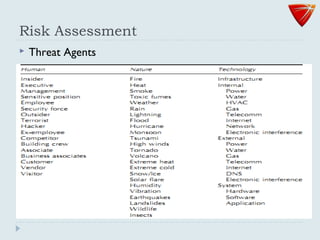
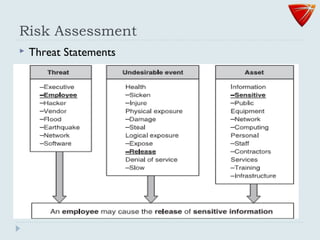
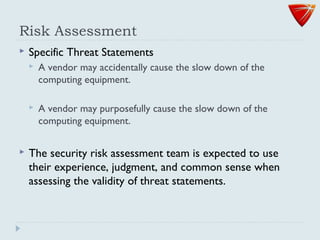
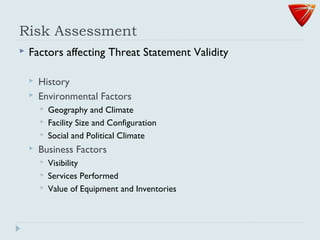
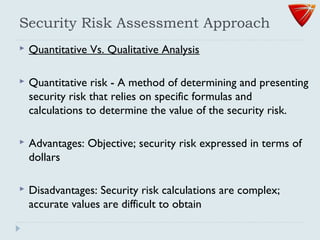
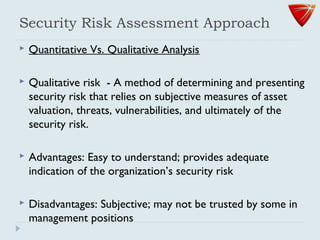
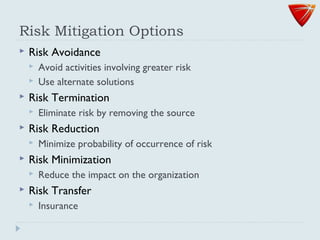
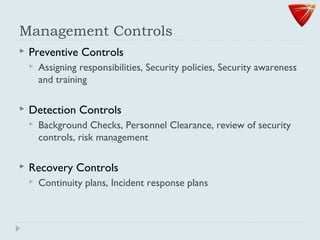
The document discusses the fundamentals of information systems and security, highlighting the components, functions, and various types of information systems used in businesses. It emphasizes the importance of data management, the rise of cyber threats, and the need for effective security measures to protect organizational assets. Additionally, it outlines key concepts related to information security, such as confidentiality, integrity, availability, and various types of security controls.