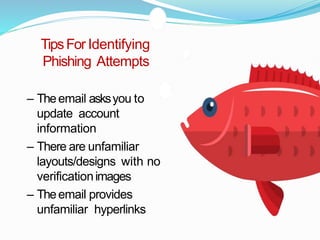
The document discusses cyber security and types of cyber attacks. It covers the key elements of cyber security including mobile security, end-user education, application security, network security, and information security. It describes common types of cyber attacks such as malware, ransomware, social engineering, phishing, and man-in-the-middle attacks. The document provides safety tips for users, including using antivirus software, practicing good password management, and being wary of suspicious links or requests for personal information.