This document covers advanced data structures in the context of graphs, detailing their representations, properties such as degrees, paths, cycles, and topological sorting, as well as their applications in various fields like transportation and social networking. Several methods for representing graphs, including adjacency matrices and lists, are discussed, along with specialized representations for trees. The document also touches on the challenges of managing large graphs and algorithms for finding paths within them.
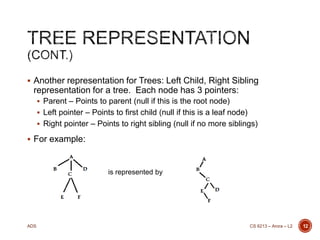
![ Using a matrix A[1..n,1..n] where A[i,j] = 1 if (i,j) is an
edge, and is 0 otherwise. This representation is called
the adjacency matrix representation. If the graph is
undirected, then the adjacency matrix is symmetric about
the main diagonal.
Using an array Adj[1..n] of pointers, which Adj[i] is a
linked list of nodes which are adjacent to i.
The matrix representation requires more memory, since it
has a matrix cell for each possible edge, whether that
edge exists or not. In adjacency list representation, the
space used is directly proportional to the number of
edges.
If the graph is sparse (very few edges), then adjacency
list may be a more efficient choice.
CS 6213 – Arora – L2 Advanced Data Structures - Graphs 9
GRAPH REPRESENTATIONS](https://image.slidesharecdn.com/l2-140128155116-phpapp01/85/Graphs-Trees-Paths-and-Their-Representations-9-320.jpg)

![ Graphs can be characterized in many ways. Two
important ones being:
Directed or Undirected
Weighted or Unweighted
Both Adjacency Matrix (AM) and Adjacency List (AL)
representations can be used for graphs – weighted
or unweighted, directed or undirected.
A[i,j] = A[j,i] if graph is undirected. So, we could decide to use
just the upper triangle.
If graph is weighted, in adjacency list, we can also store the
weight. AL[i] = [(j,w(i,j)), (k,w(i,k)), …]
CS 6213 – Arora – L2 Advanced Data Structures - Graphs 11
GRAPH CHARACTERIZATIONS](https://image.slidesharecdn.com/l2-140128155116-phpapp01/85/Graphs-Trees-Paths-and-Their-Representations-11-320.jpg)
![ When updating values in a tree, such as the size of the
subtree rooted at a node, the weight of the subtree
rooted at a node, etc, there are two main methods:
Recompute whenever there is a modify operation (addition of a
node, deletion of a node, changing the weight of a node, etc).
Recomputations usually only need to propagate from the change
node upwards to the root. [Advantage: Values always up to date,
Disadvantages: Lot of time spent in Recompute, Method cannot
be run concurrently.]
Use a dirty flag and set to true when there is a change. Set dirty
flag to true for all ancestors (navigate to parent, until the root).
Recompute when there is a need, or as per a schedule.
[Advantages: Efficient, Methods (other than the “recomputed”
operation can be run concurrently. Disadvantages: Values are out
of date at times.]
CS 6213 – Arora – L2 Advanced Data Structures - Graphs 18
UPDATING VALUES](https://image.slidesharecdn.com/l2-140128155116-phpapp01/85/Graphs-Trees-Paths-and-Their-Representations-18-320.jpg)
![ Given each of the graph representations, how do we
find a path?
Shortest path algorithms
Dijkstra
All Pairs Shortest Paths
[Refer to CS 6212 Notes for details]
CS 6213 – Arora – L2 Advanced Data Structures - Graphs 20
PATHS](https://image.slidesharecdn.com/l2-140128155116-phpapp01/85/Graphs-Trees-Paths-and-Their-Representations-20-320.jpg)