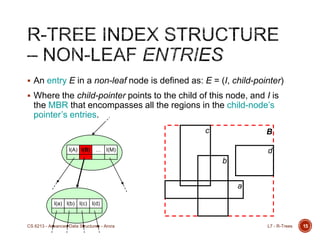
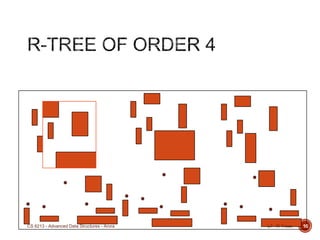
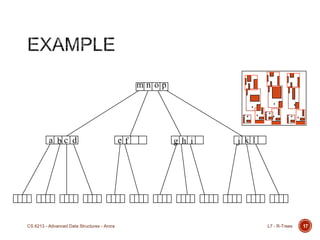
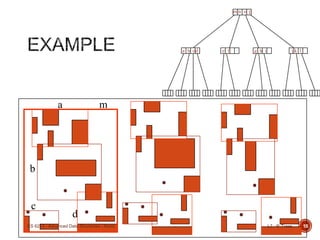
The document provides an overview of R-trees, a type of spatial data structure used for efficient indexing and retrieval of spatial objects, particularly in multidimensional spaces. It covers R-tree properties, insertion routines, splitting and condensing nodes, and querying strategies, emphasizing the importance of dynamic adjustments for maintaining optimal search performance. The course is part of an advanced data structures lecture by Professor Amrinder Arora at George Washington University.
![ An entry E in a leaf node is defined as:
E = (I, tuple-identifier)
Where I refers to the smallest binding n-dimensional region
(MBR) that encompasses the spatial data pointed to by its tuple-
identifier.
I is a series of closed-intervals that make up each dimension of
the binding region.
Example. In 2D, I = (Ix, Iy),
where Ix = [xa, xb], and Iy = [ya, yb].
13L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-13-320.jpg)
![[Not limited to 2D – higher dimensions are certainly possible.]
In general I = (I0, I1, …, In-1) for n-dimensions, and that Ik = [ka, kb].
If either ka or kb (or both) are equal to , this means that the
spatial object extends outward indefinitely along that dimension.
14L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-14-320.jpg)
![26
New index entry-records are added to the leaves.
Nodes that overflow are split, and splits propagate up the tree.
A split-propagation may cause the tree to grow in height.
The main Insert routine
Let E = (I, tuple-identifier) be the new entry to be inserted.
Let T be the root of the R-Tree.
[Ins_1] Locate a leaf L starting from T to insert E.
[Ins_2] Add E to L. If L is already full (overflow), split L into L and L‟.
[Ins_3] Propagate MBR changes (enlarged or reduced) upwards.
[Ins_4] Grow tree taller if node split propagation causes T to split.
L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-26-320.jpg)
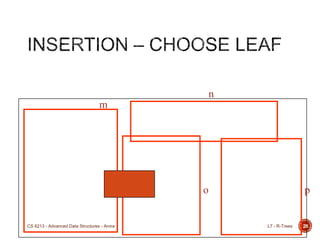
![29
[Ins_1] Locate a leaf L starting from T to insert E = (I, tuple-identifier).
Notion (i): Select the path that would require the least enlargement to include E.I.
Notion (ii): Resolve ties by choosing the child-node with the smallest MBR.
Invoke: L = ChooseLeaf (E, T).
A B C
@rN
A
C
B
E.I
rN
L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-29-320.jpg)
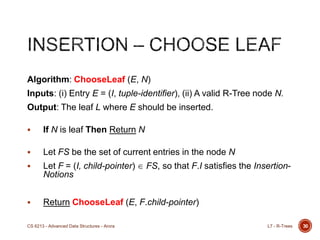
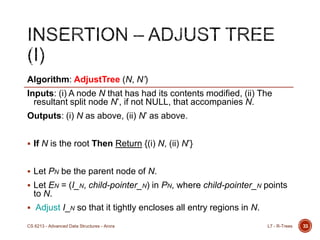
![31
[Ins_2] Add E to L.
Notion (i): If L has room for another entry, install E.
Notion (ii): Otherwise split L to obtain L and L‟, which between
them, will contain all previous entries in L and the new E
(consolidated for local optima).
[Ins_3] Propagate MBR changes upwards by invoking
AdjustTree (L, L‟).
Notion (i): Ascend from leaf L to the root T while adjusting the
covering rectangles MBR.
Notion (ii): If L‟ exists, propagate node splits as necessary; i.e.
attempt to install a new entry in the parent of L to point to L‟.
L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-31-320.jpg)
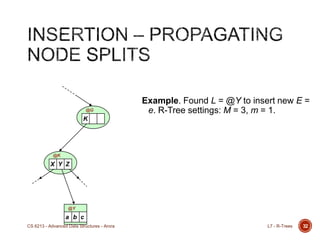
![[Ins_4] Grow Tree taller.
Notion: If the recursive node split propagation causes the root to
split, then create a new root whose children are the two resulting
nodes.
35
A B C
@T (root)
E F
@C
G H
@C’
L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-35-320.jpg)
![37
Current index entry-records are removed from the leaves.
Nodes that underflow are condensed, and its contents redistributed
appropriately throughout the tree.
A condense propagation may cause the tree to shorten in height.
The main Delete routine
Let E = (I, tuple-identifier) be a current entry to be removed.
Let T be the root of the R-Tree.
[Del_1] Find the leaf L starting from T that contains E.
[Ins_2] Remove E from L, and condense „underflow‟ nodes.
[Ins_3] Propagate MBR changes upwards.
[Ins_4] Shorten tree if T contains only 1 entry after condense propagation.
L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-37-320.jpg)
![ [Del_1] Find the leaf L starting from T that contains E.
Algorithm: FindLeaf (E, N)
Inputs: (i) Entry E = (I, tuple-identifier), (ii) A valid R-Tree node N.
Output: The leaf L containing E.
If N is leaf Then
If N contains E Then Return N
Else Return NULL
Else
Let FS be the set of current entries in N.
For each F = (I, child-pointer) FS where F.I overlaps E.I Do
Set L = FindLeaf (E, F.child-pointer)
If L is not NULL Then Return L
Next F
Return NULL
End If
38L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-38-320.jpg)
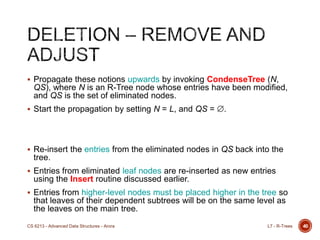
![[Del_2] Remove E from L, and condense „underflow‟ nodes.
[Del_3] Propagate MBR changes upwards.
Notion (i): Ascend from leaf L to root T while adjusting covering
rectangles MBR.
Notion (ii): If after removing the entry E in L and the number of
entries in L becomes fewer than m, then the node L has to be
eliminated and its remaining contents relocated.
39L7 - R-TreesCS 6213 - Advanced Data Structures - Arora](https://image.slidesharecdn.com/l7rtree-140408142112-phpapp02/85/R-Trees-and-Geospatial-Data-Structures-39-320.jpg)