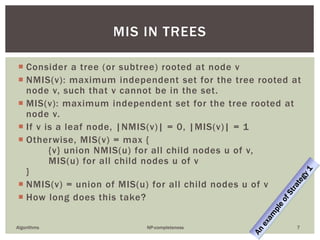
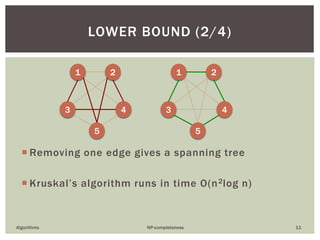
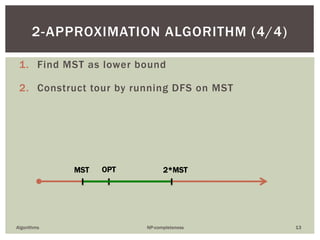
This document discusses algorithms for NP-complete problems. It introduces the maximum independent set problem and shows that while it is NP-complete for general graphs, it can be solved efficiently for trees using a recursive formulation. It also discusses the traveling salesperson problem and presents a dynamic programming algorithm that provides a better running time than brute force. Finally, it discusses approximation algorithms for the TSP and shows a 2-approximation algorithm that finds a tour with cost at most twice the optimal using minimum spanning trees.