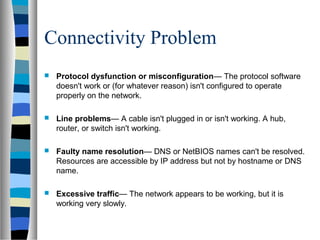
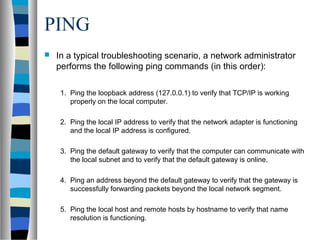
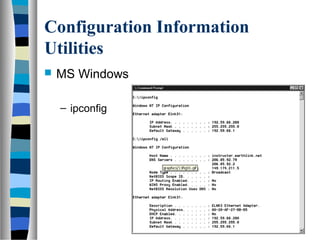
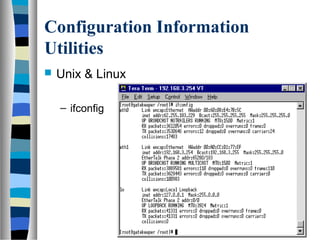
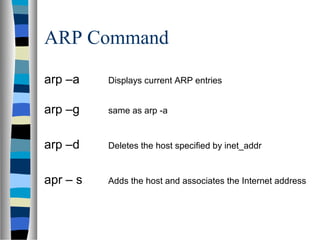
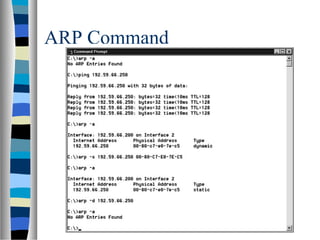
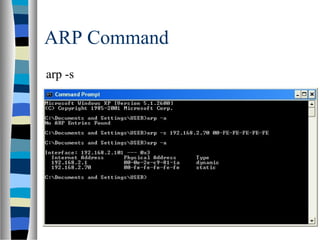
This document discusses using connectivity utilities to troubleshoot common network problems. It describes four types of connectivity problems: protocol problems, line problems, name resolution problems, and network performance problems. It then explains key connectivity utilities like Ping, IPConfig, Ifconfig and ARP that can be used to diagnose these issues. Specific sequences of commands with these utilities are provided to methodically test network connectivity and troubleshoot problems.