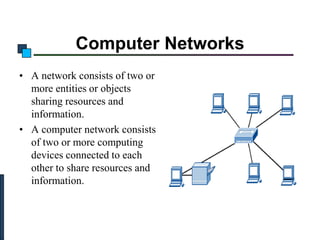
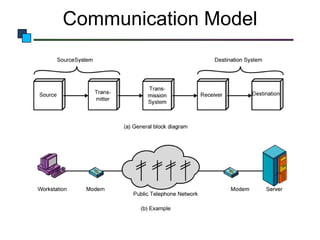
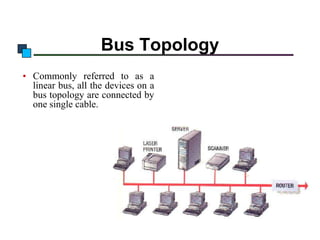
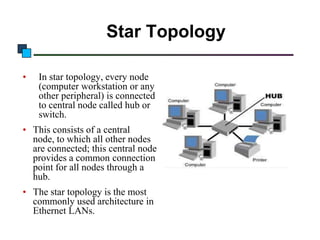
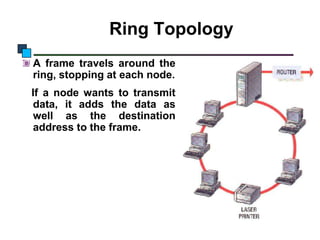
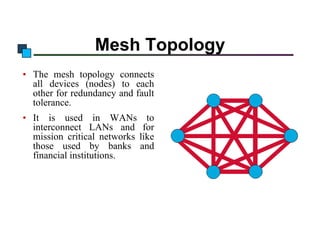
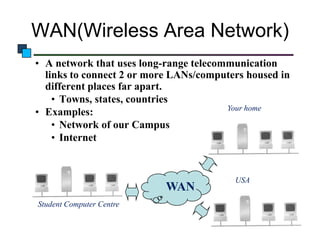
Computer networks allow computing devices to connect and share resources. A network consists of connected devices like computers, printers, and servers. It uses communication hardware and protocols to transmit data. Common network hardware includes hubs, switches, routers, and cables. Networks can be configured in various topologies like bus, star, ring, or mesh. Networks are also classified based on their scope - a local area network (LAN) connects devices within a building, while a wide area network (WAN) spans a larger geographic area. Key roles are clients, which initiate data requests, and servers, which provide resources and services to clients.