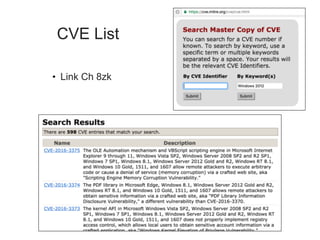
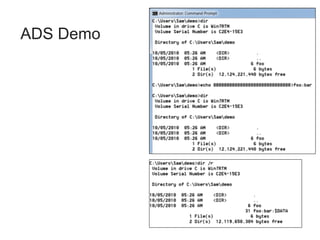
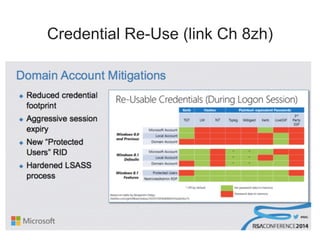
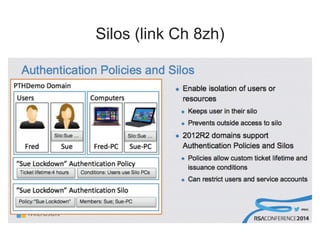
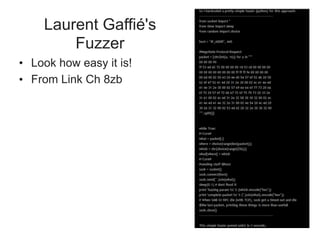
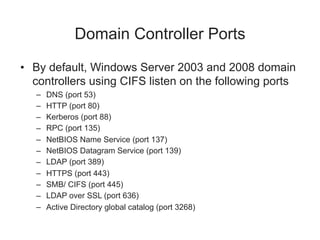
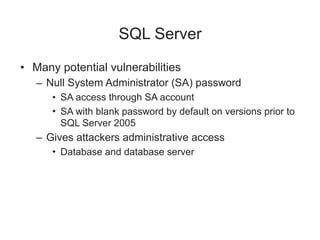
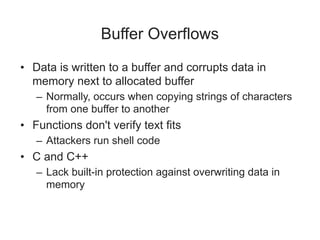
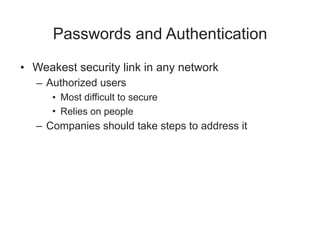
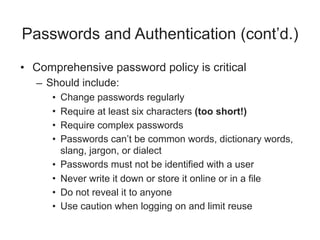
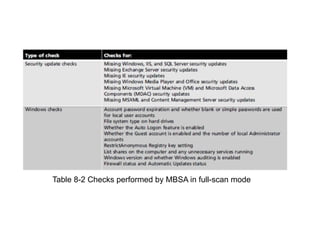
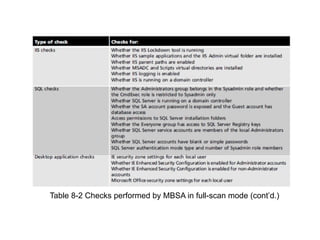
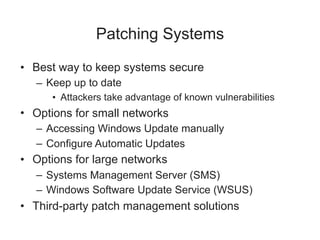
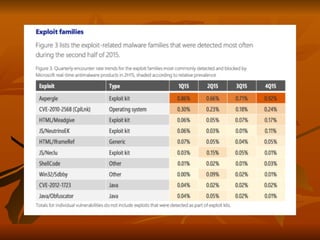
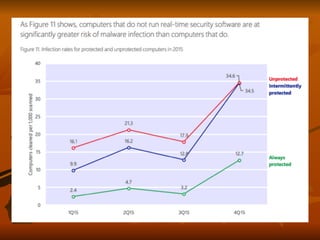
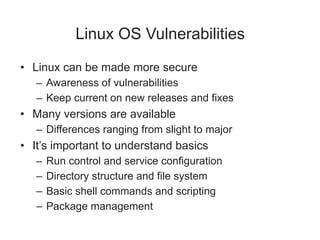
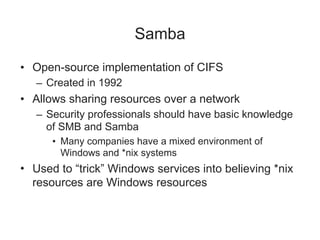
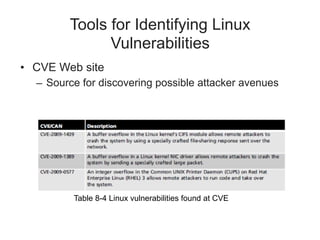
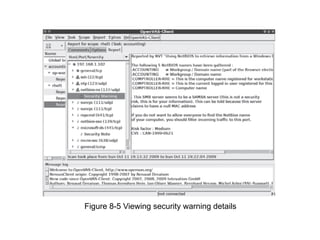
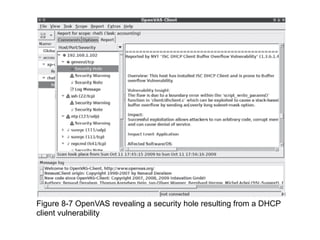
Chapter 8 of 'Hands-On Ethical Hacking and Network Defense' discusses vulnerabilities in Windows and Linux operating systems, emphasizing the importance of identifying, fixing, and hardening these systems against threats. It covers various vulnerabilities, best practices for patch management, antivirus solutions, and tools for identifying security issues for both operating systems. Additionally, the chapter highlights the need for user awareness training and maintaining up-to-date systems to mitigate risks.