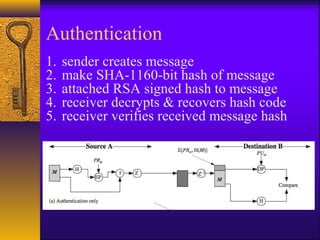
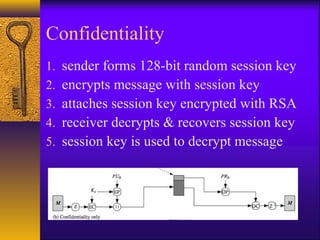
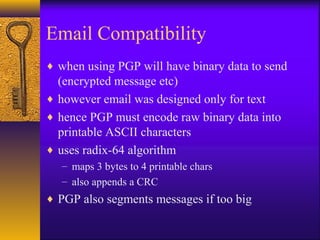
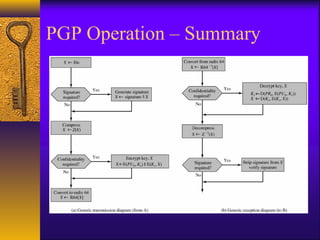
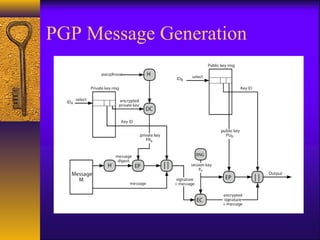
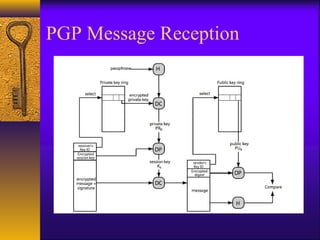
Electronic mail security requires confidentiality, authentication, integrity, and non-repudiation. Privacy Enhanced Mail (PEM) and Pretty Good Privacy (PGP) provide these security services for email. PEM uses canonical conversion, digital signatures, encryption, and base64 encoding. PGP provides authentication via digital signatures and confidentiality through symmetric encryption of messages with randomly generated session keys. Secure/Multipurpose Internet Mail Extensions (S/MIME) also supports signed and encrypted email to provide security.

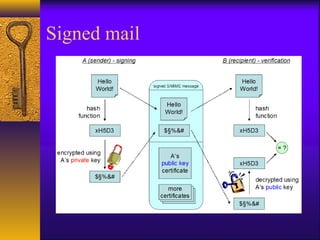
![Signed mail
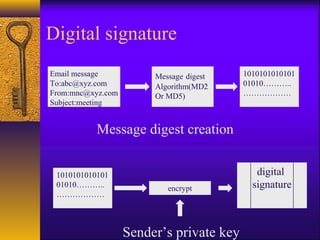
1. The user writes the message as clear-text.
2. The message digest is being calculated
(using SHA-1[2] or MD5[3]).
3. The message digest is being encrypted
using the signer’s private key (DSS[4] or
RSA[5]).](https://image.slidesharecdn.com/emailsecurity-170204180203/85/Email-security-26-320.jpg)
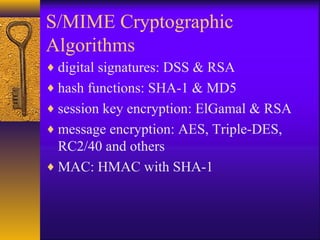
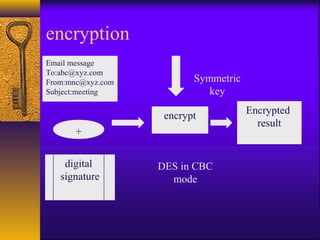
![Encrypted mail
1. The user writes the message as clear-text.
2. A random session key is being created
(tripleDES[6] or RC2[7])
3. The message is being encrypted using the
random session key.
4. For every recipient, the session key is being
encrypted using the recipient’s public key
(DH[8] or RSA[5]).](https://image.slidesharecdn.com/emailsecurity-170204180203/85/Email-security-28-320.jpg)