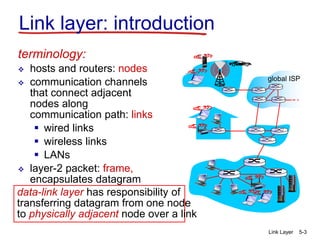
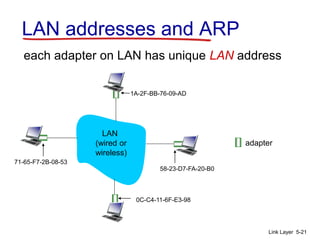
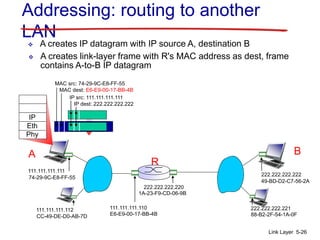
The document provides an overview of the link layer. It discusses the goals and services of the link layer, including error detection, correction, and sharing access to broadcast channels through multiple access protocols. It describes various link layer technologies like Ethernet, switches, and VLANs. It also covers topics like link layer addressing using MAC addresses, the Address Resolution Protocol (ARP) for mapping IP addresses to MAC addresses, and examples of multiple access protocols including Carrier Sense Multiple Access with Collision Detection (CSMA/CD) used in Ethernet networks.