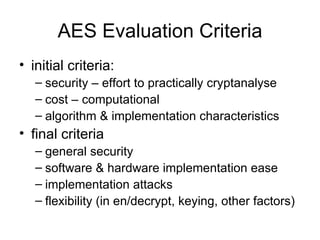
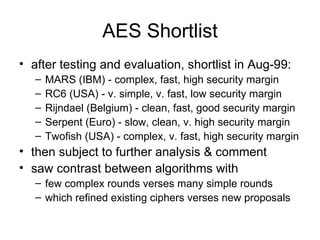
- The document discusses the Advanced Encryption Standard (AES) and its selection as a replacement for the Data Encryption Standard (DES). It describes the selection process conducted by the National Institute of Standards and Technology (NIST).
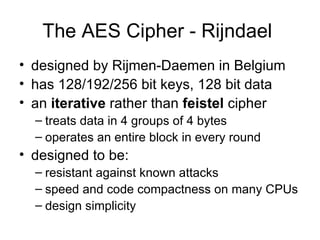
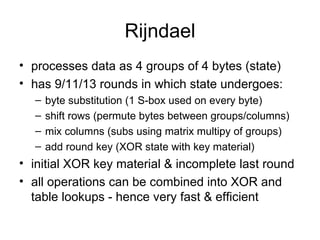
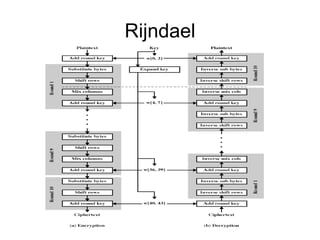
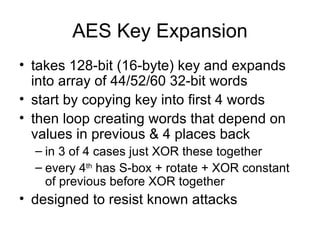
- Rijndael, designed by Vincent Rijmen and Joan Daemen, was selected as the AES after evaluation of 15 candidate algorithms. It uses 128/192/256-bit keys and 128-bit blocks.
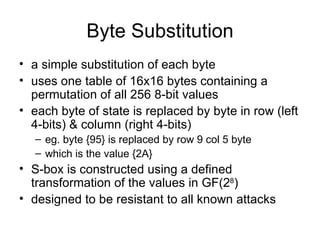
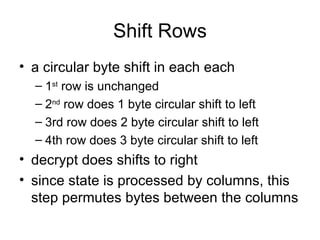
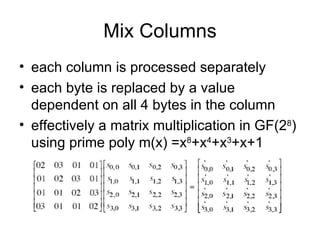
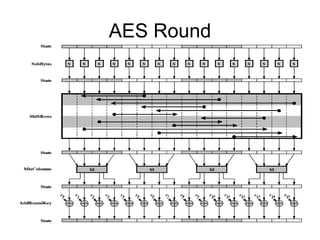
- The AES cipher, based on Rijndael, consists of 10-14 rounds depending on key size. Each round performs byte substitution, shift rows, mix columns, and adds a round key. It can be efficiently implemented in both software and hardware.