1. The document discusses the Advanced Encryption Standard (AES) cipher, which was selected from the Rijndael algorithm in 2000 to replace the Data Encryption Standard (DES).
2. AES has a block size of 128 bits, with key sizes of 128, 192, or 256 bits. It operates on a 4x4 column-byte state and consists of 10-14 rounds depending on the key size.
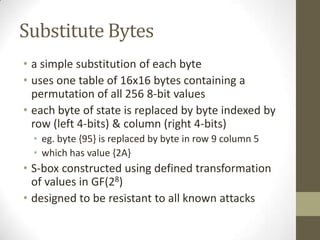
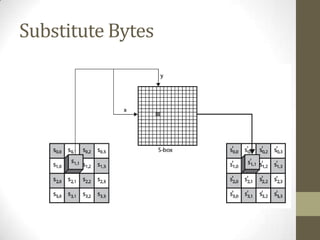
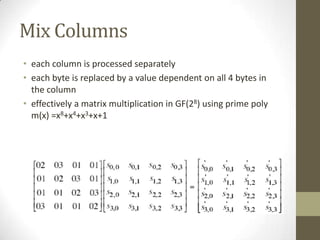
3. Each round performs byte substitution, shifting rows of the state, mixing columns using matrix multiplication, and adding the round key using XOR. The key is expanded using XOR and S-boxes to generate round keys.