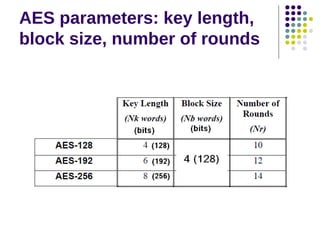
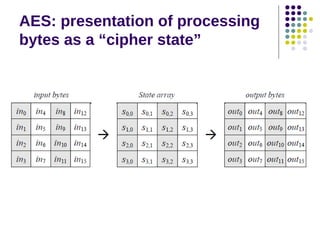
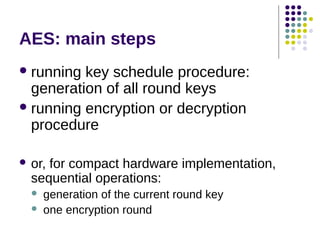
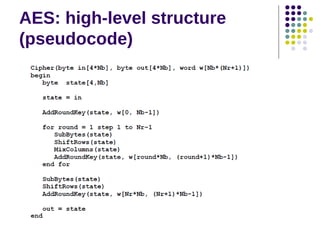
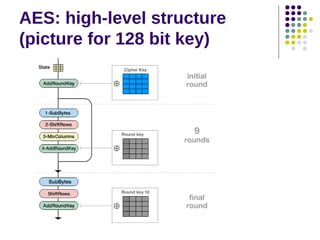
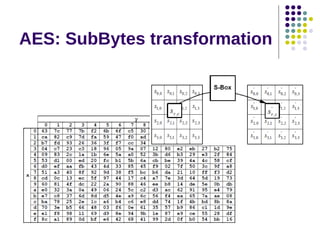
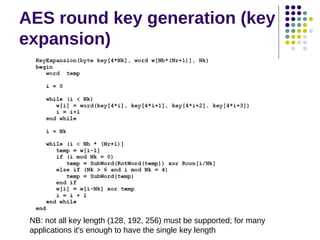
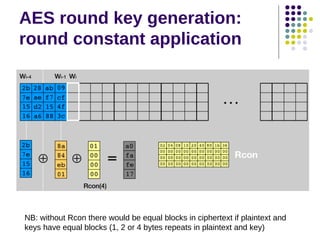
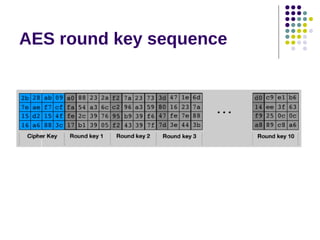
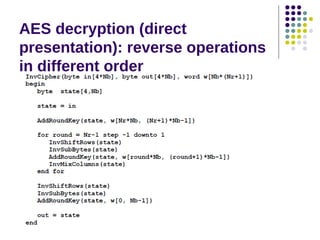
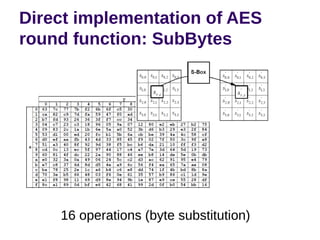
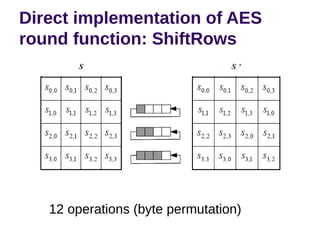
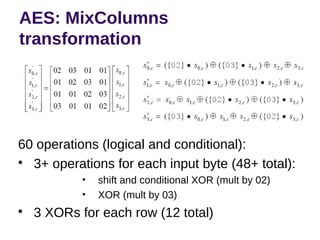
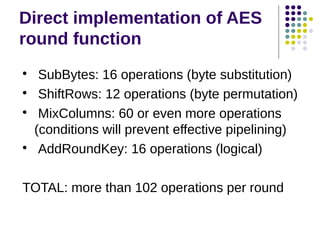
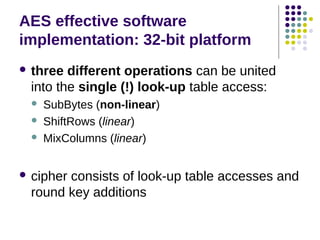
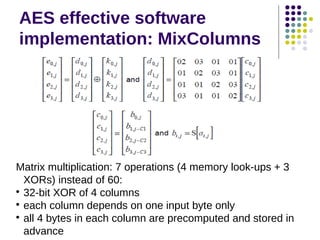
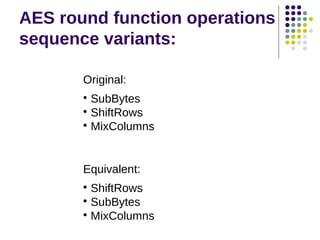
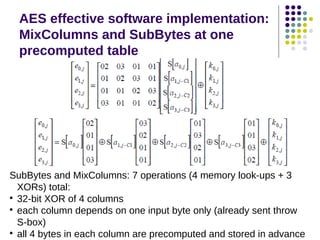
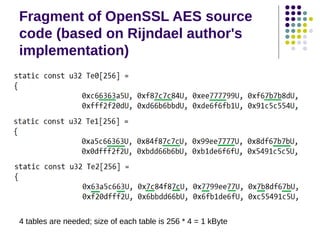
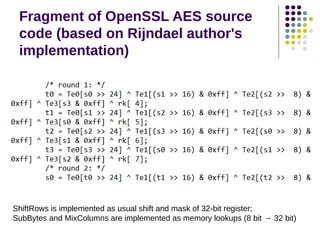
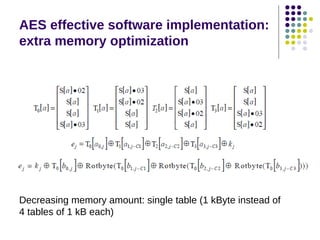
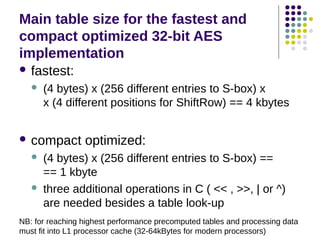
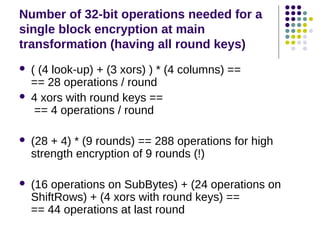
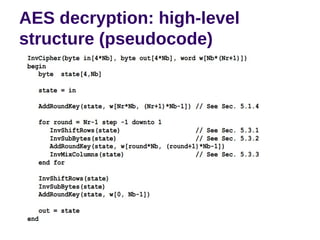
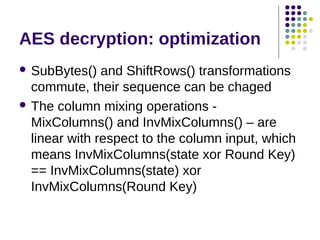
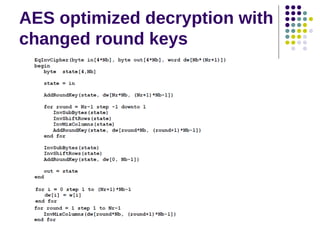
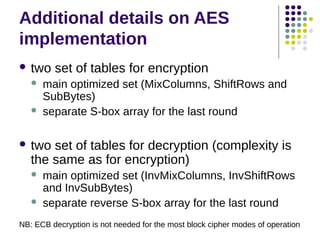
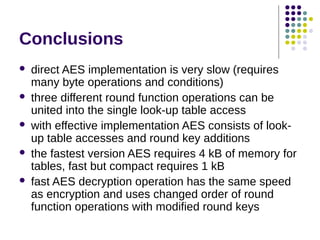
The document discusses effective software implementation of the Advanced Encryption Standard (AES), developed from the Rijndael cipher and selected in a cryptographic competition between 1997 and 2000. It covers AES properties, direct implementation challenges, optimization methods, and its efficiency on 32-bit platforms. The text concludes that effective AES implementation can significantly reduce processing time through look-up table accesses while maintaining cryptographic security.