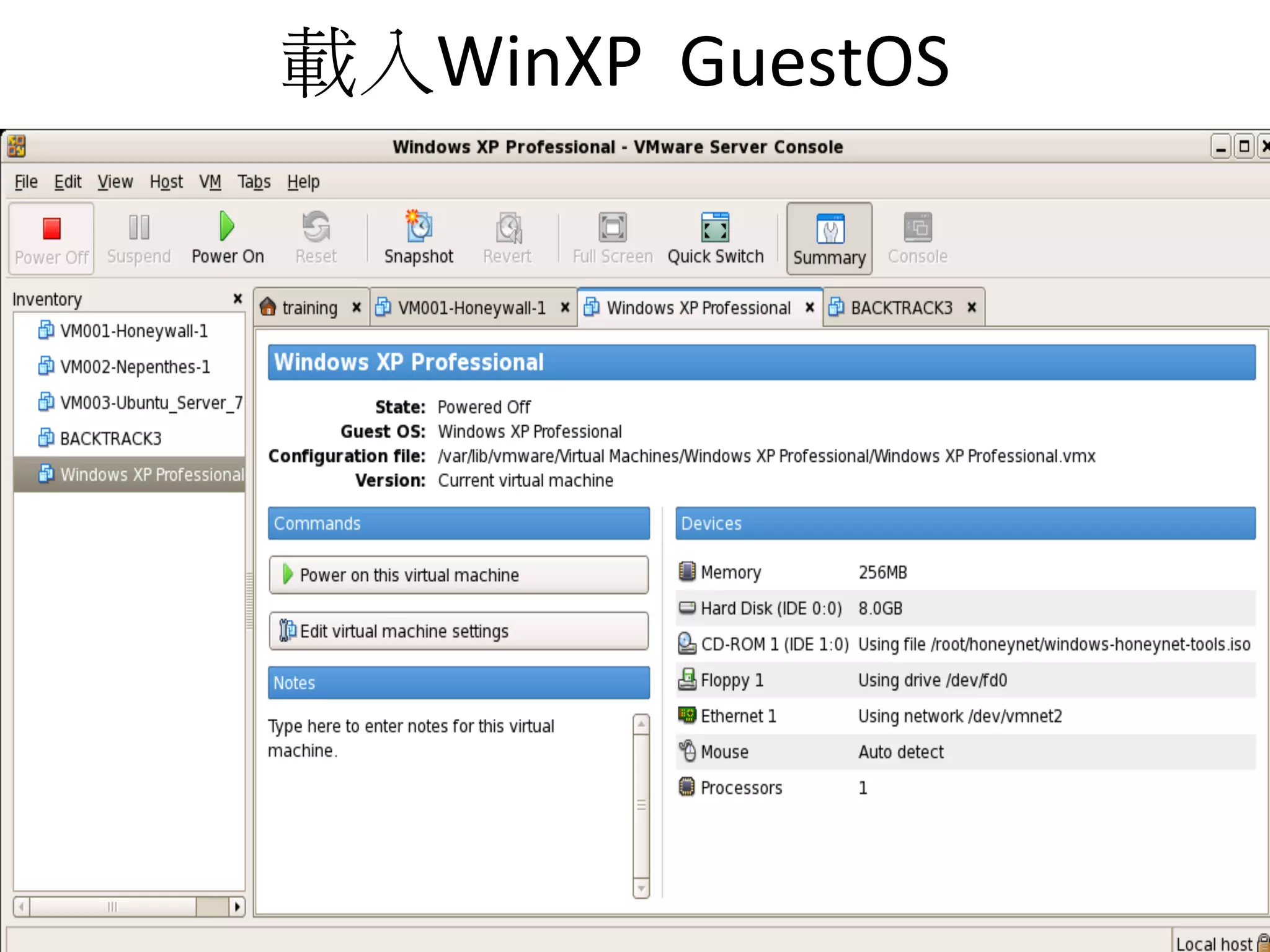
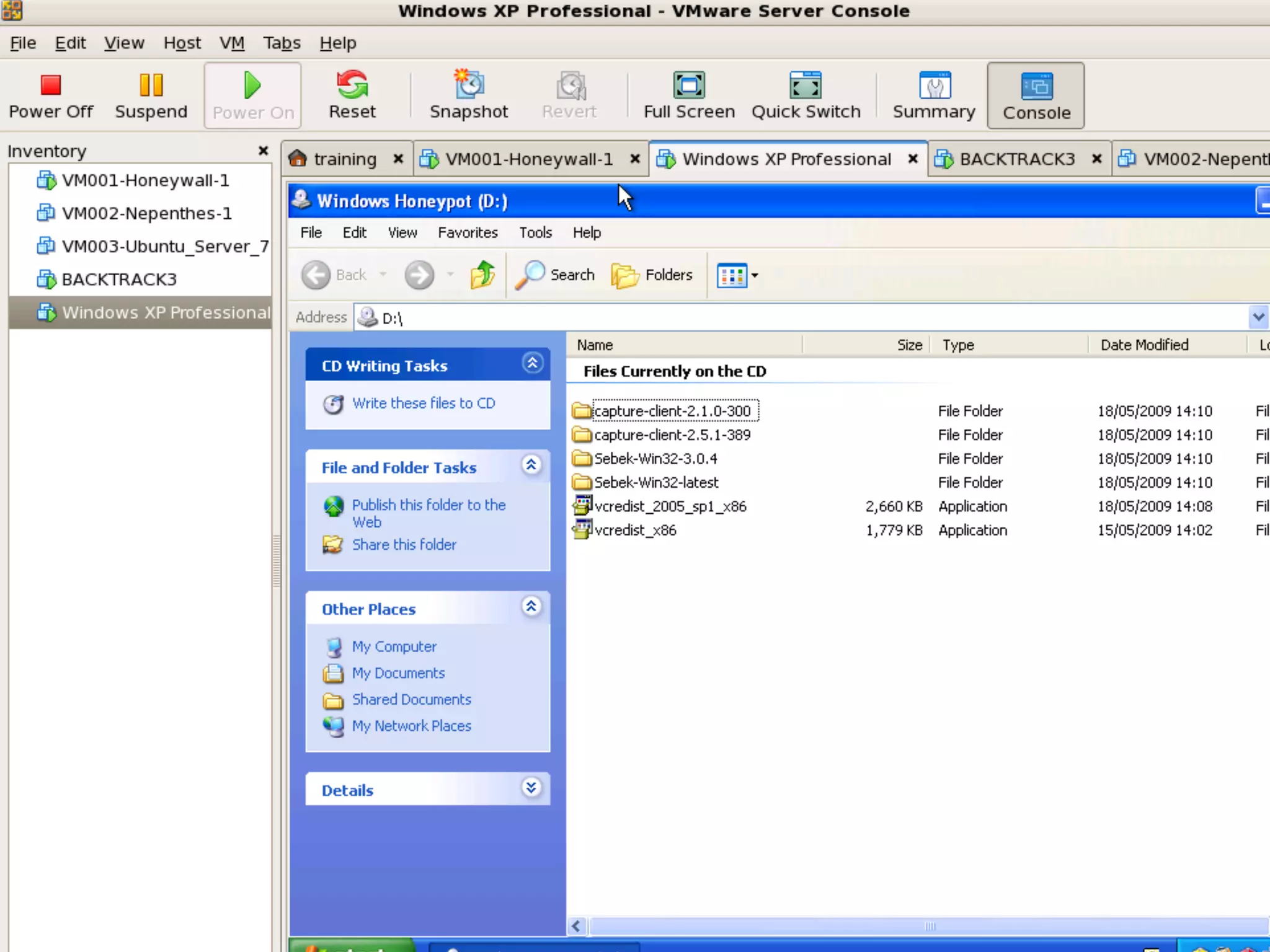
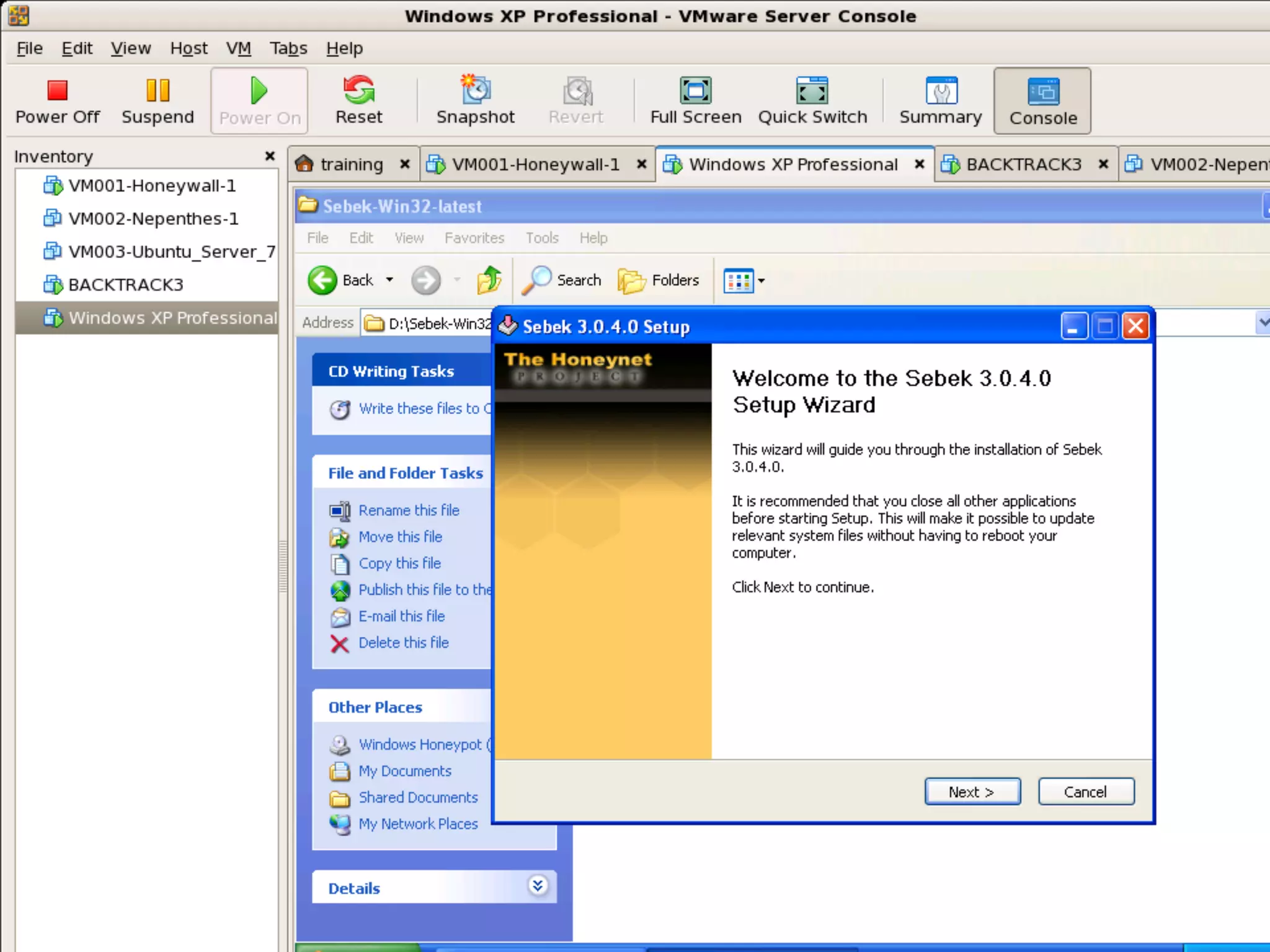
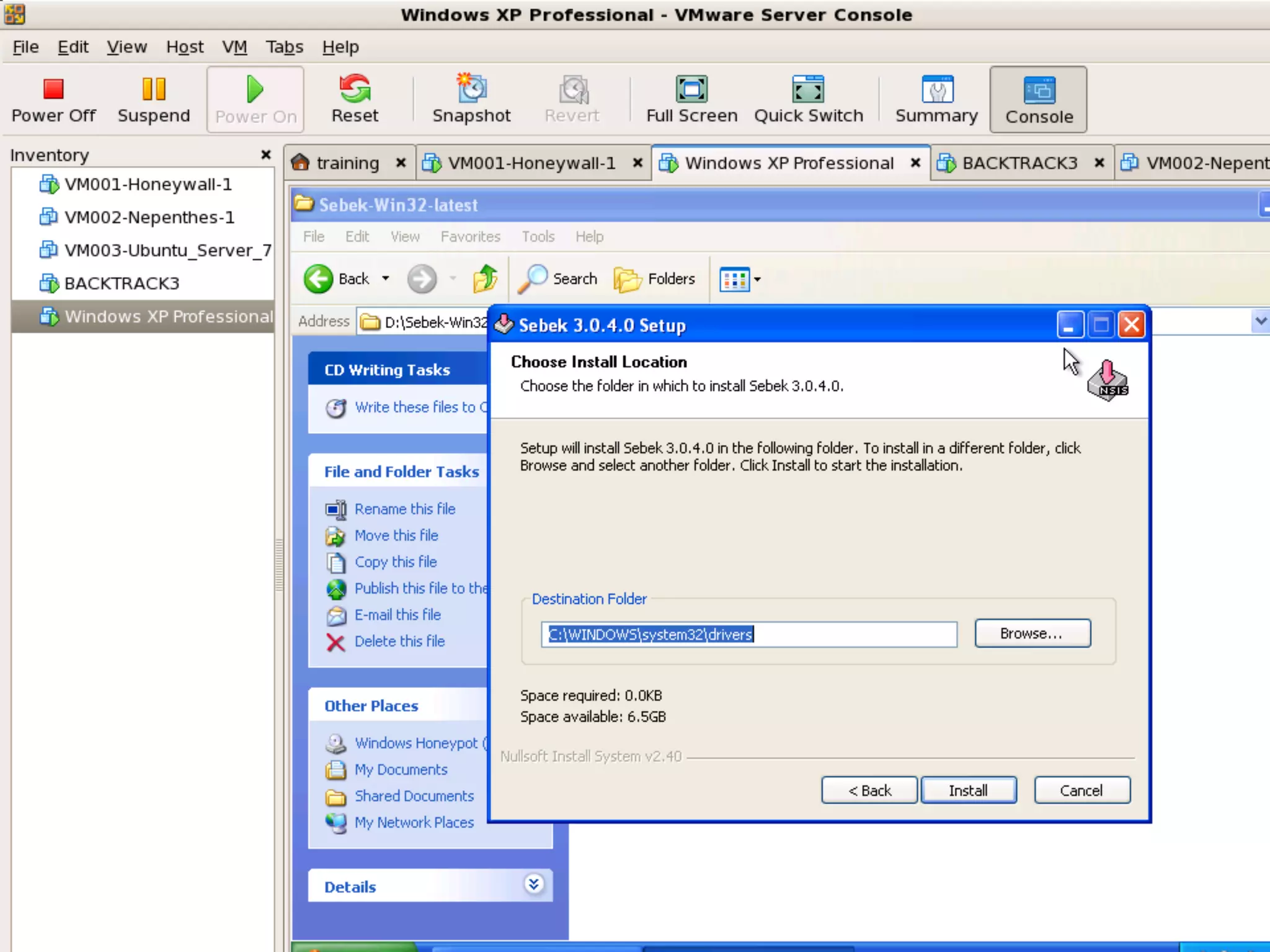
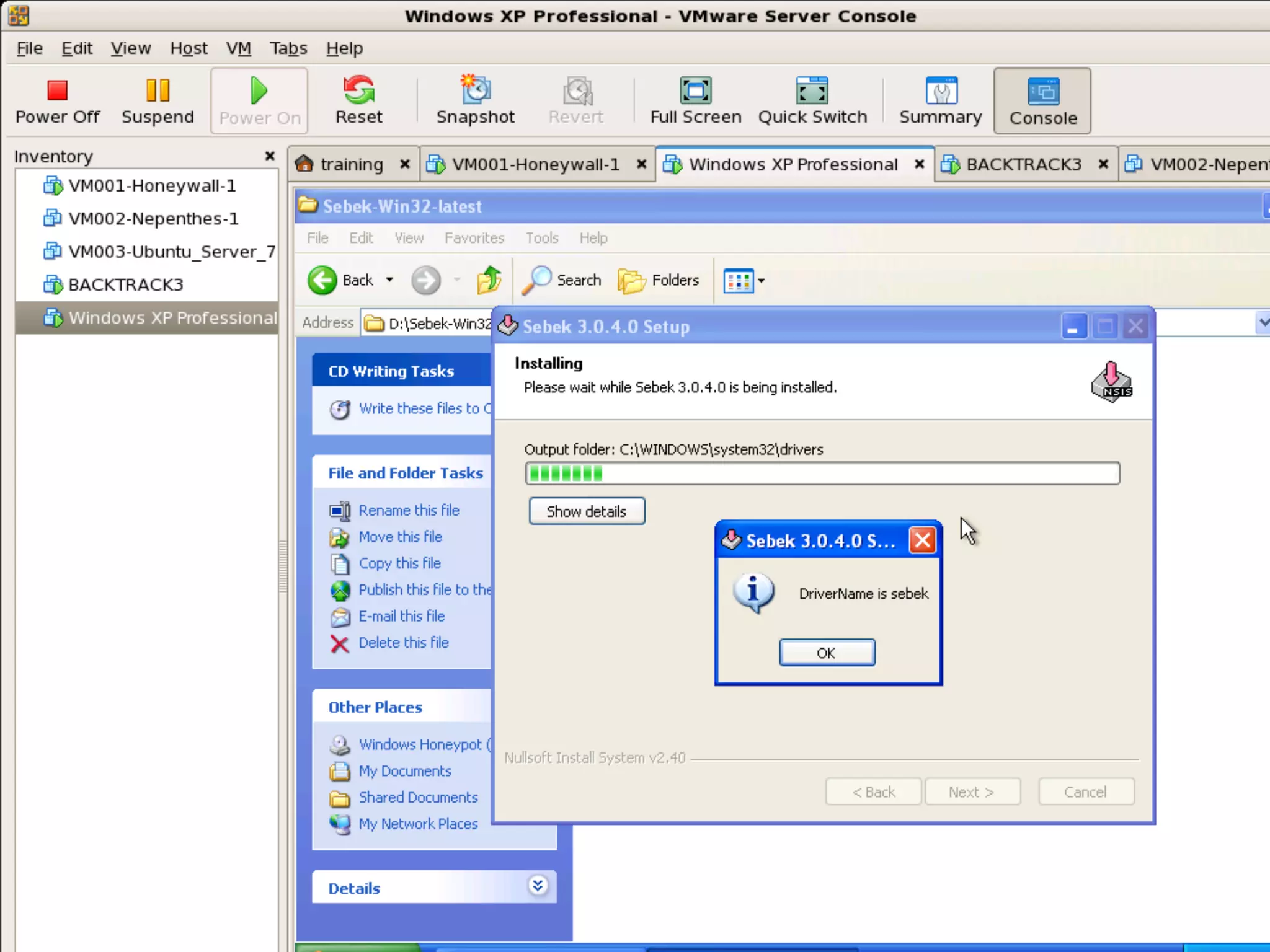
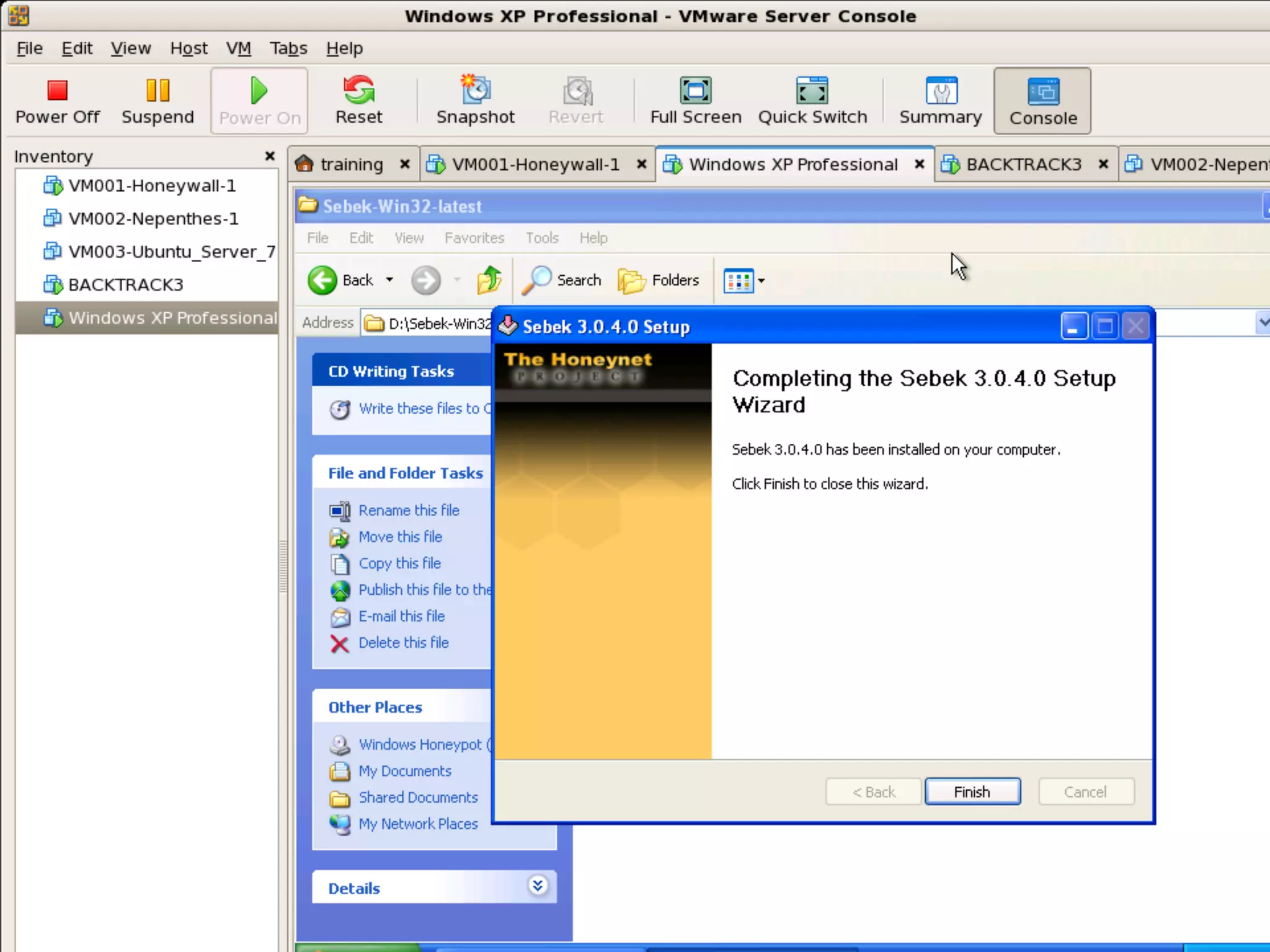
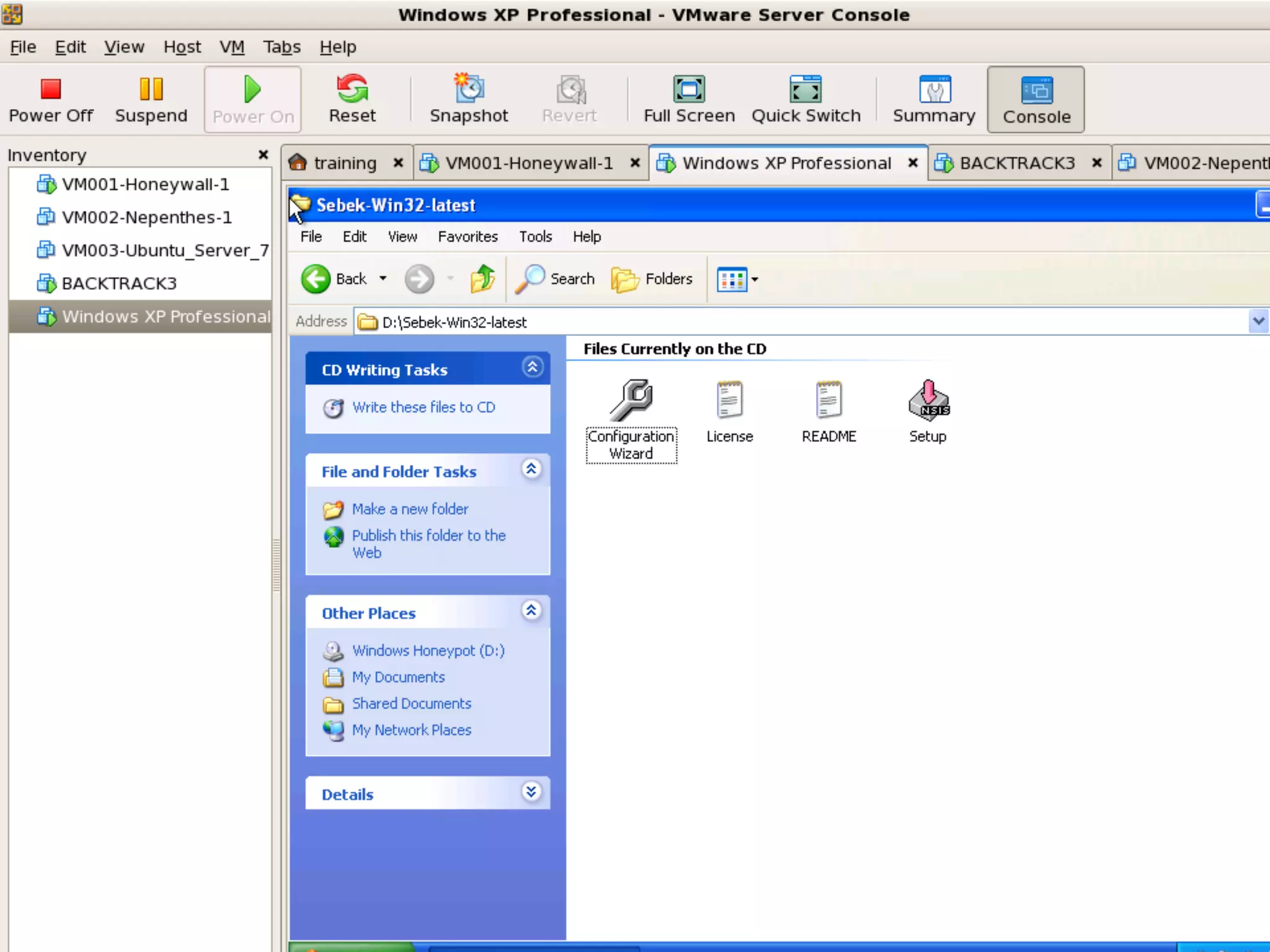
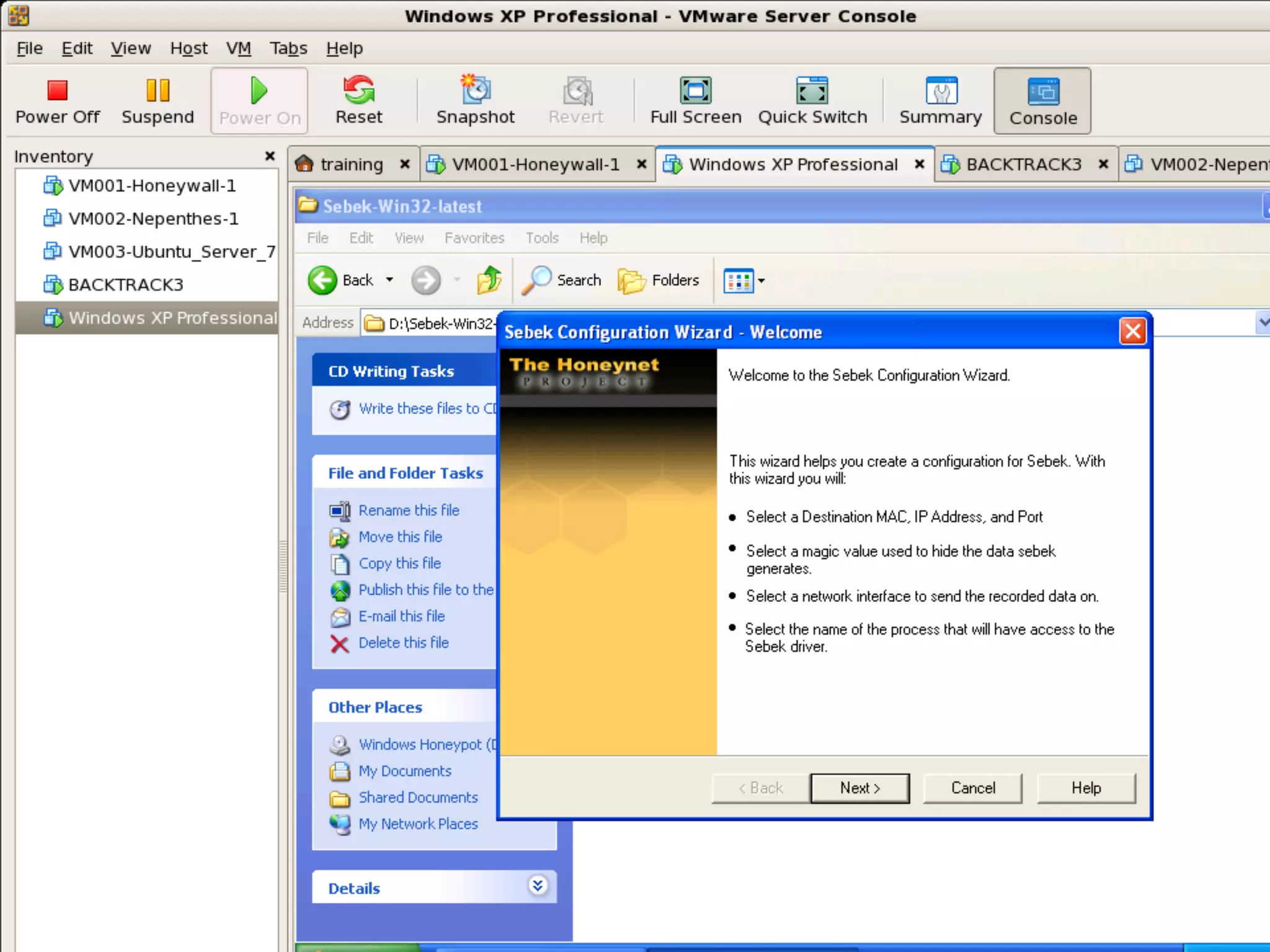
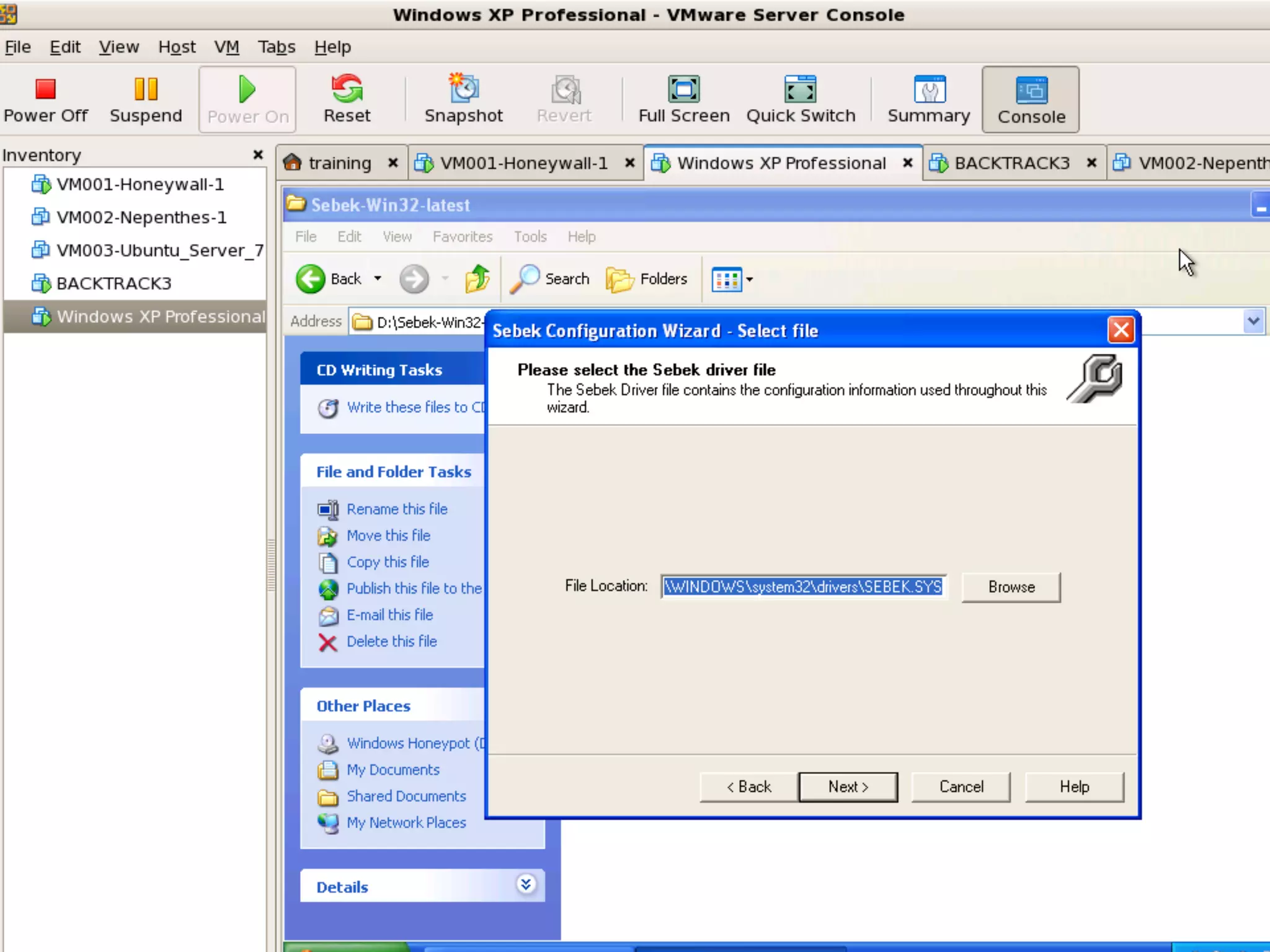
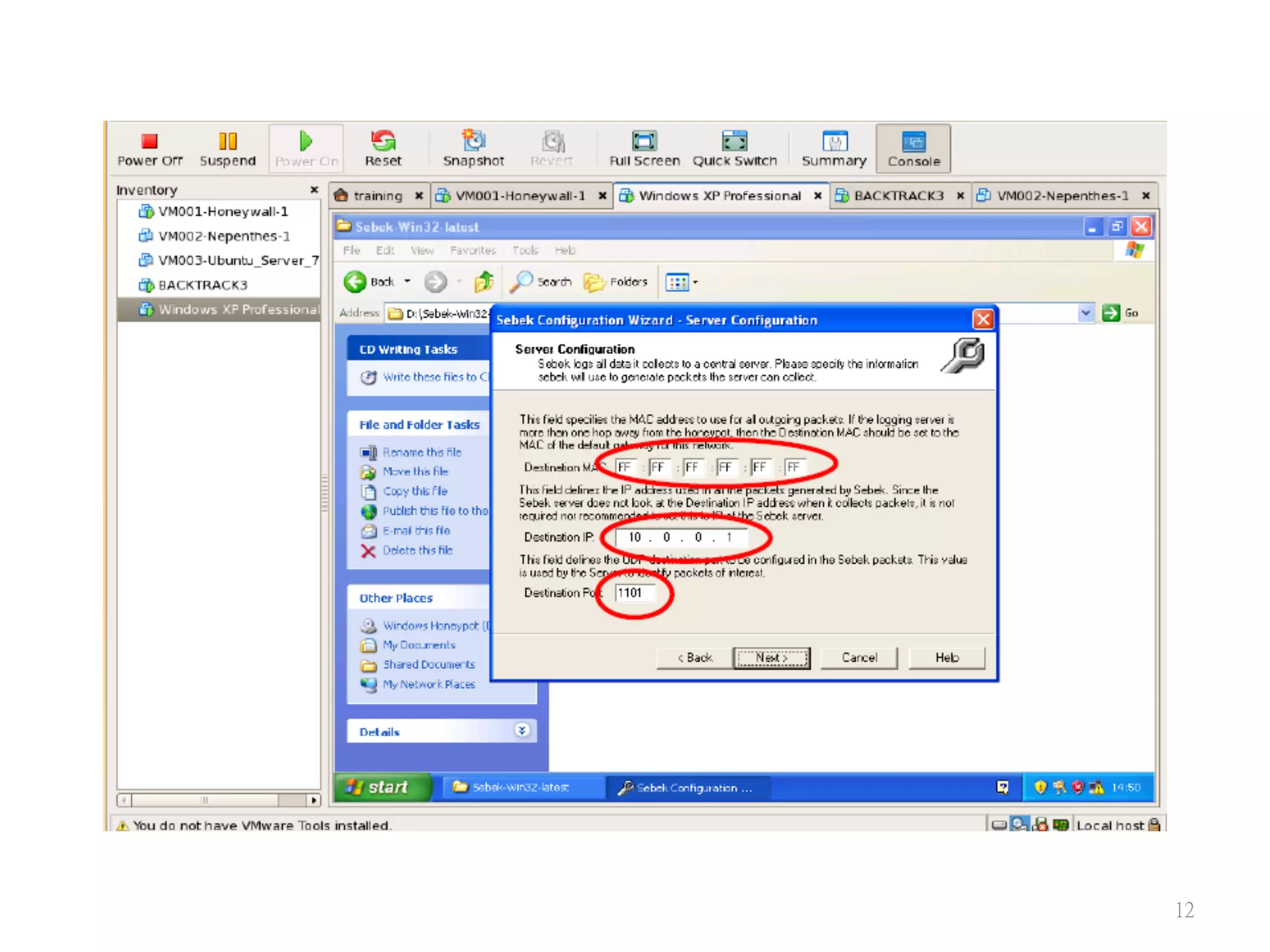
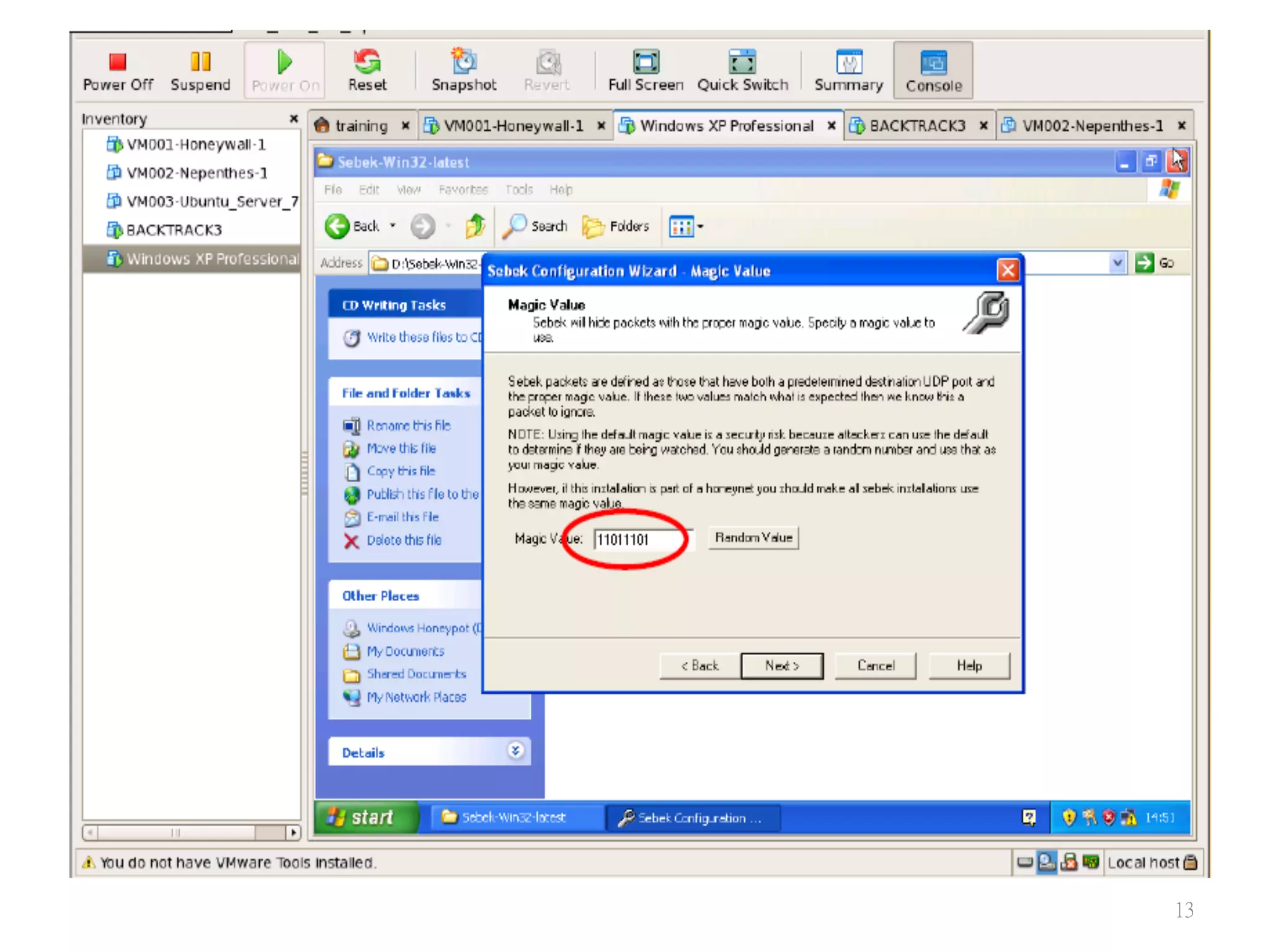
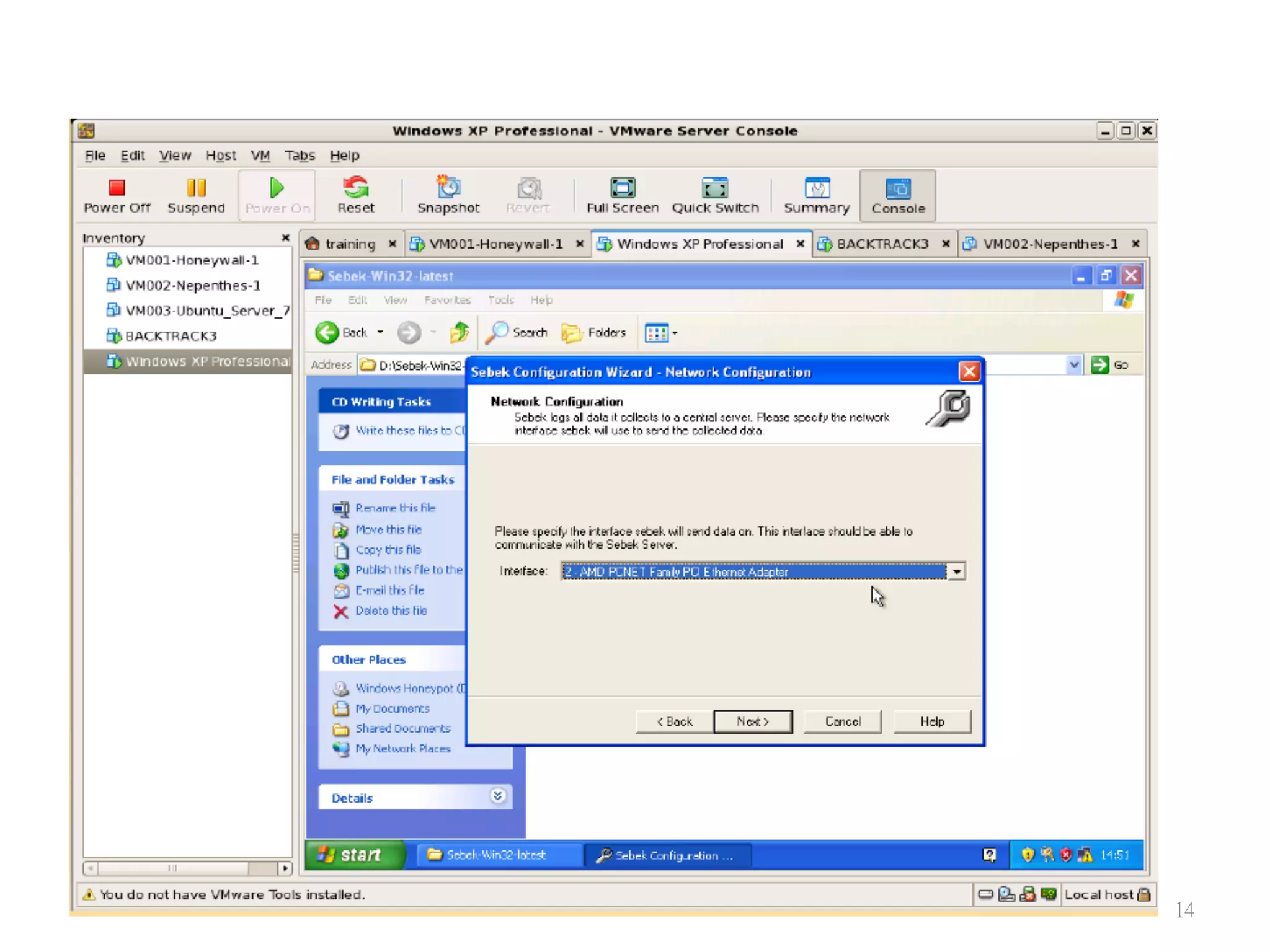
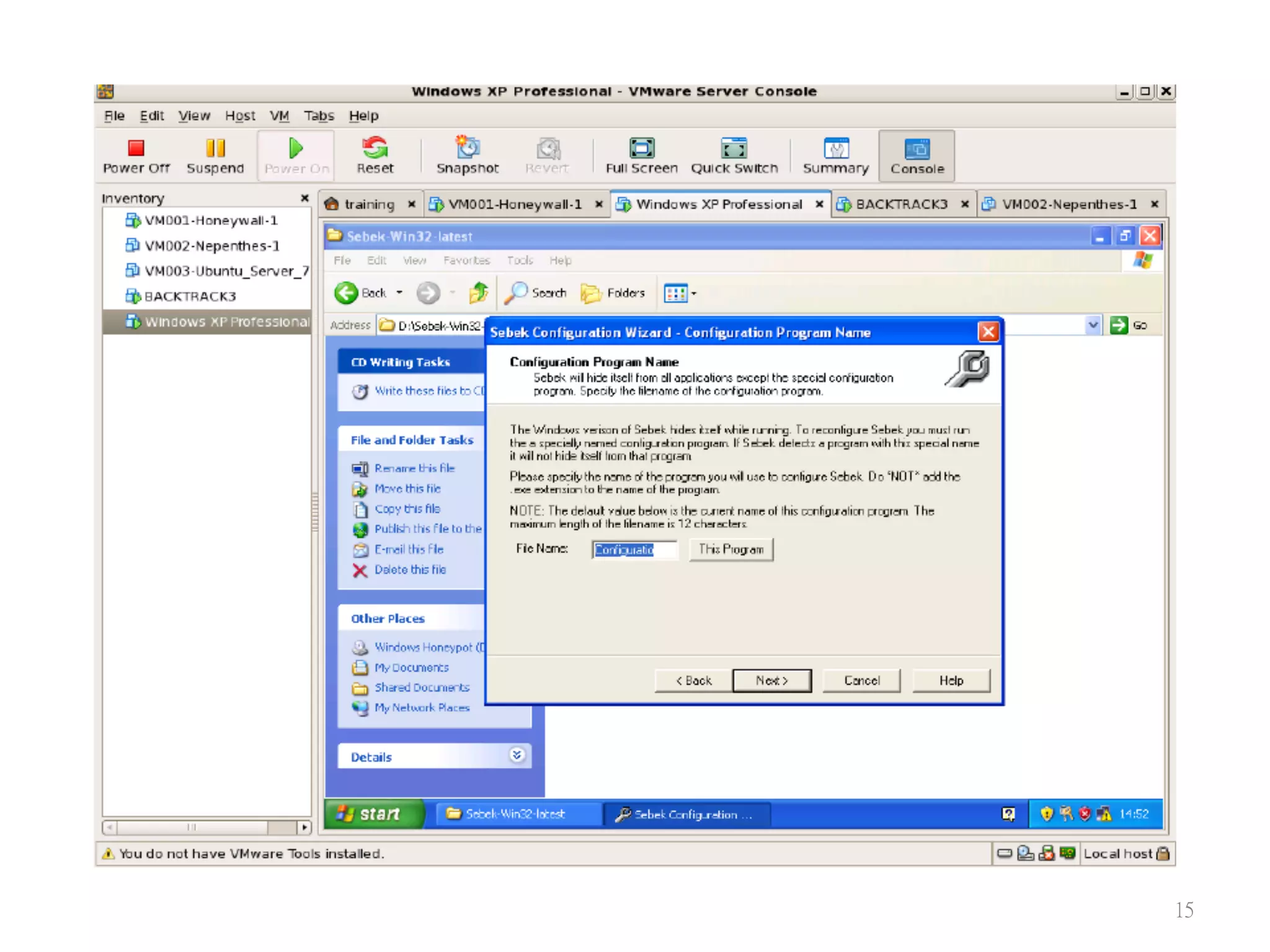
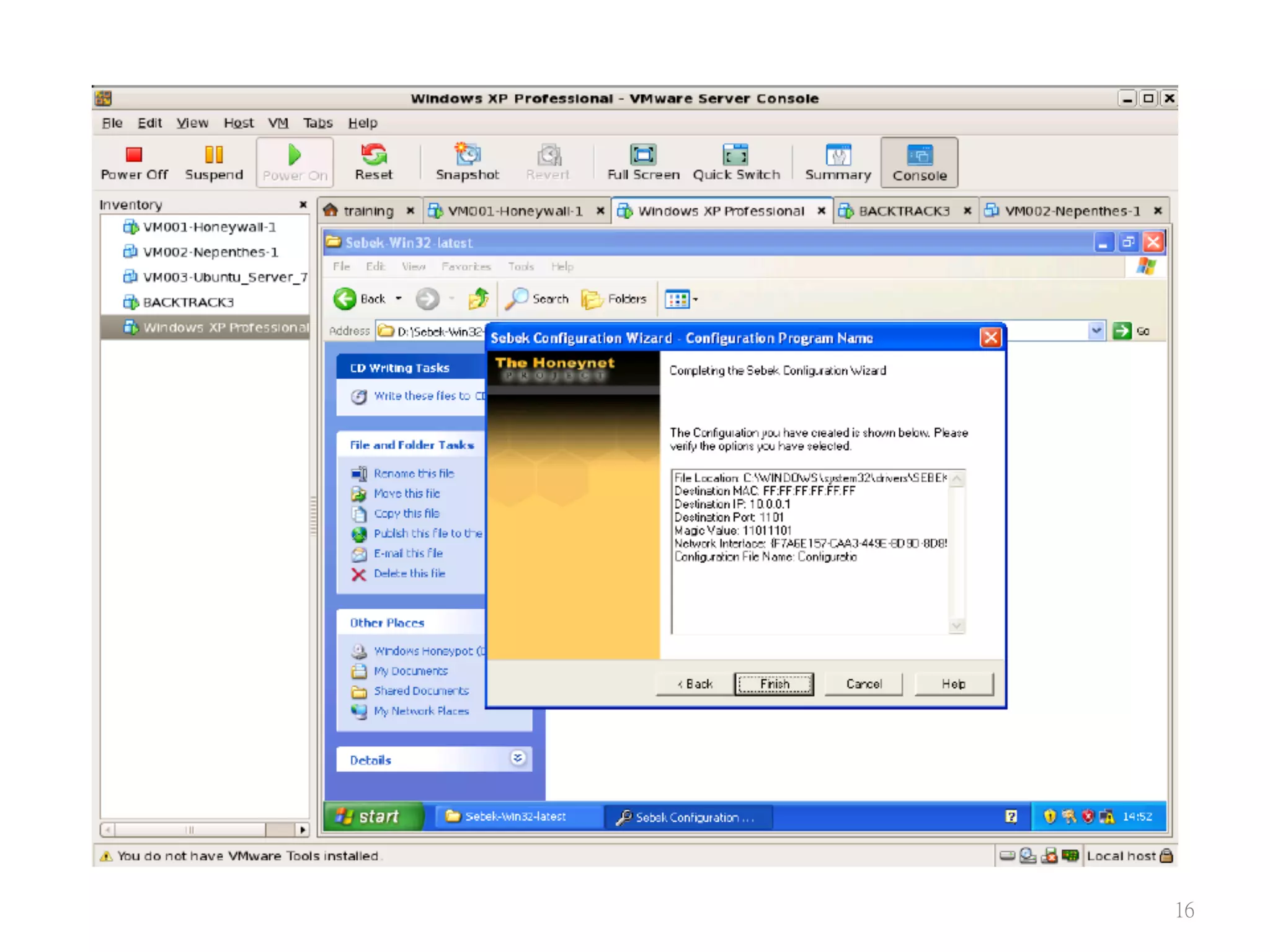
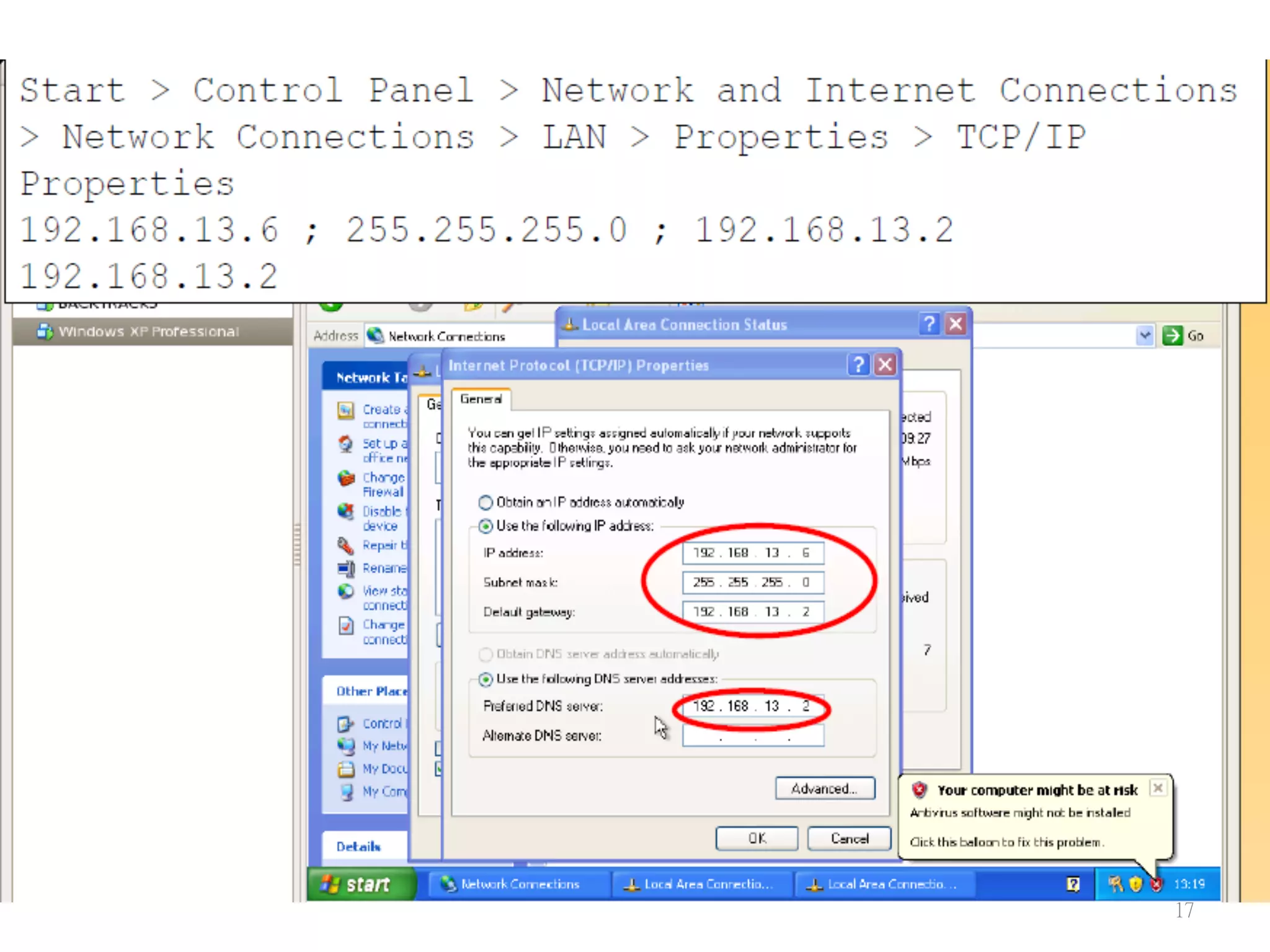
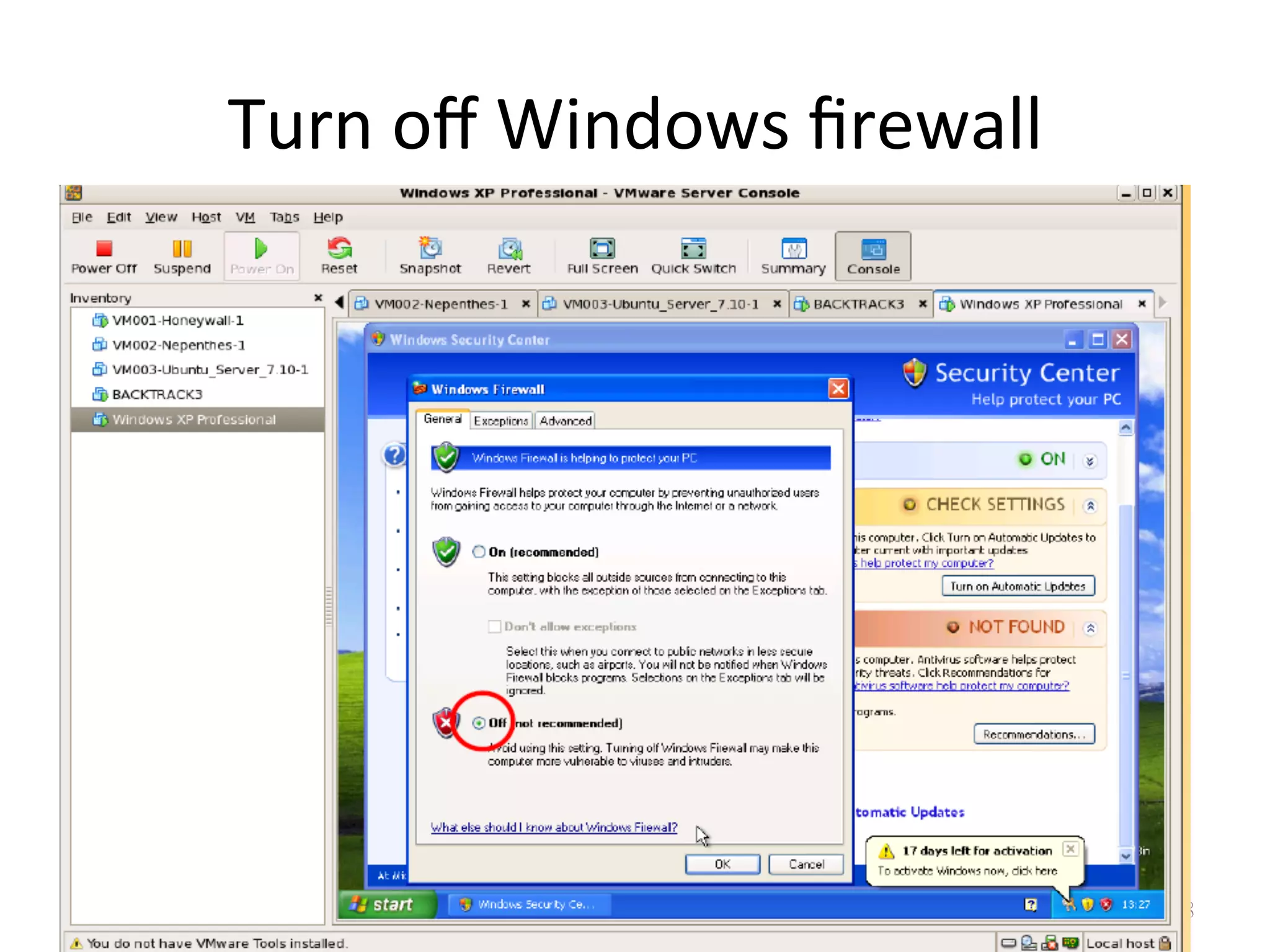
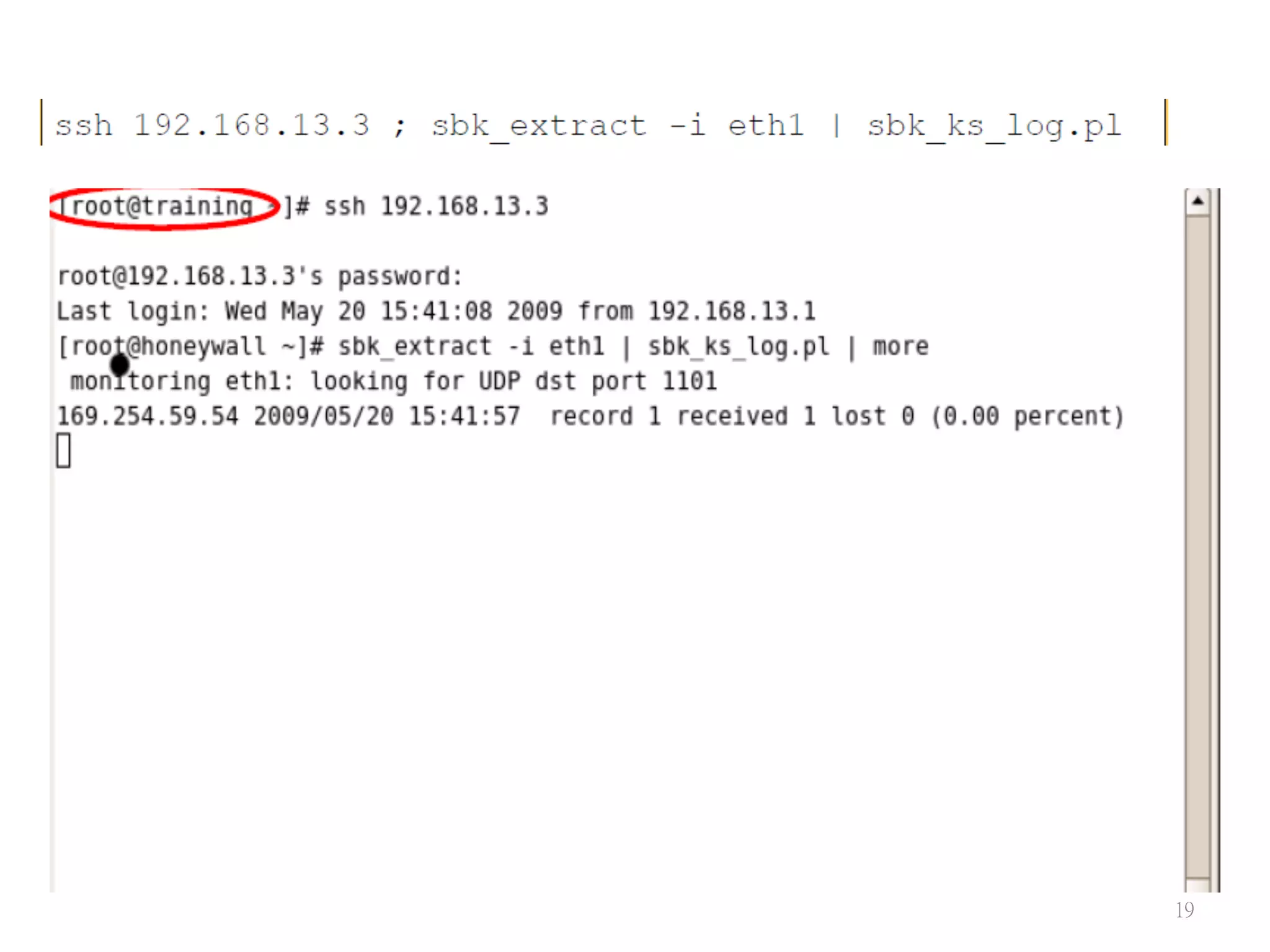
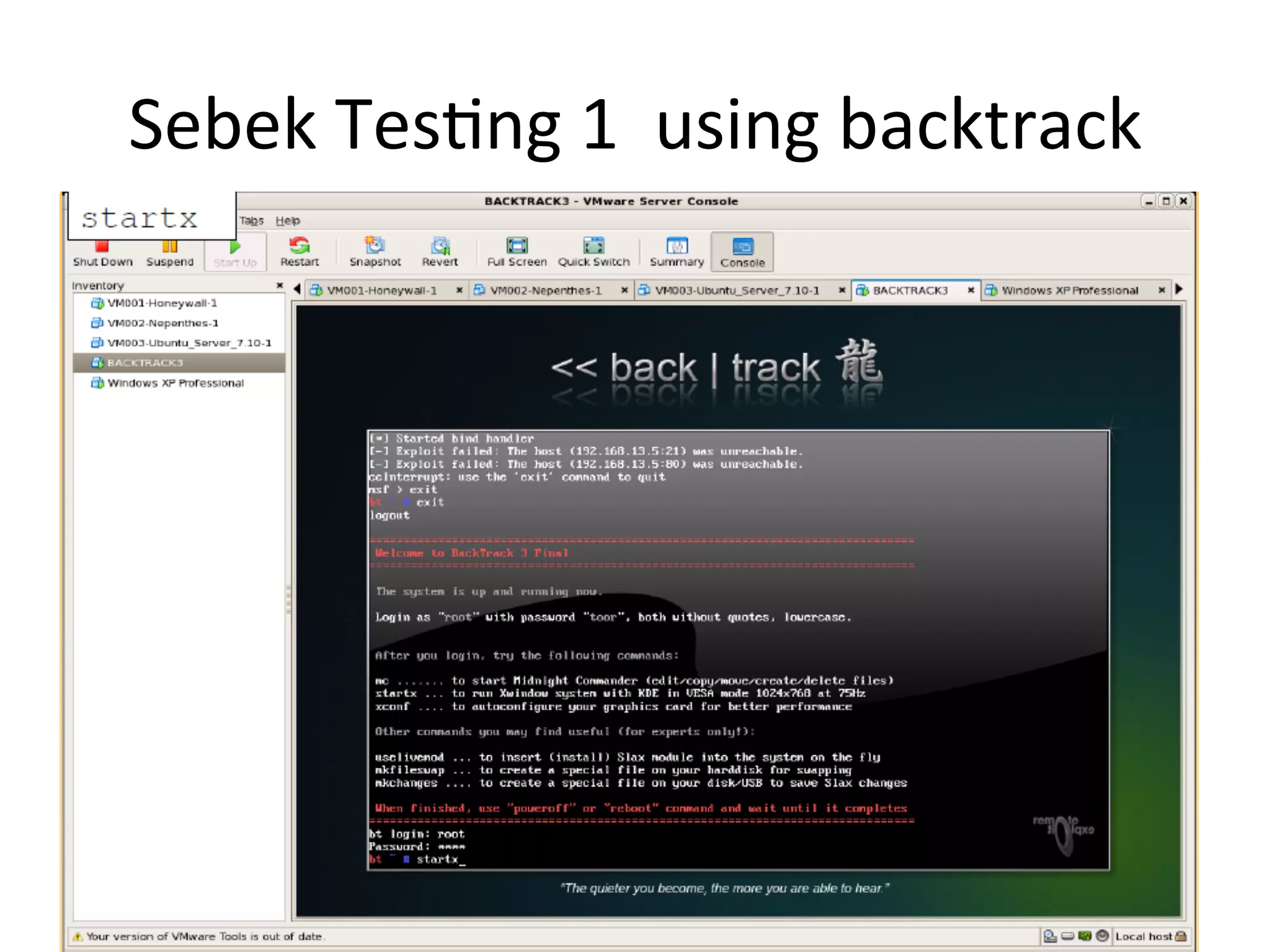
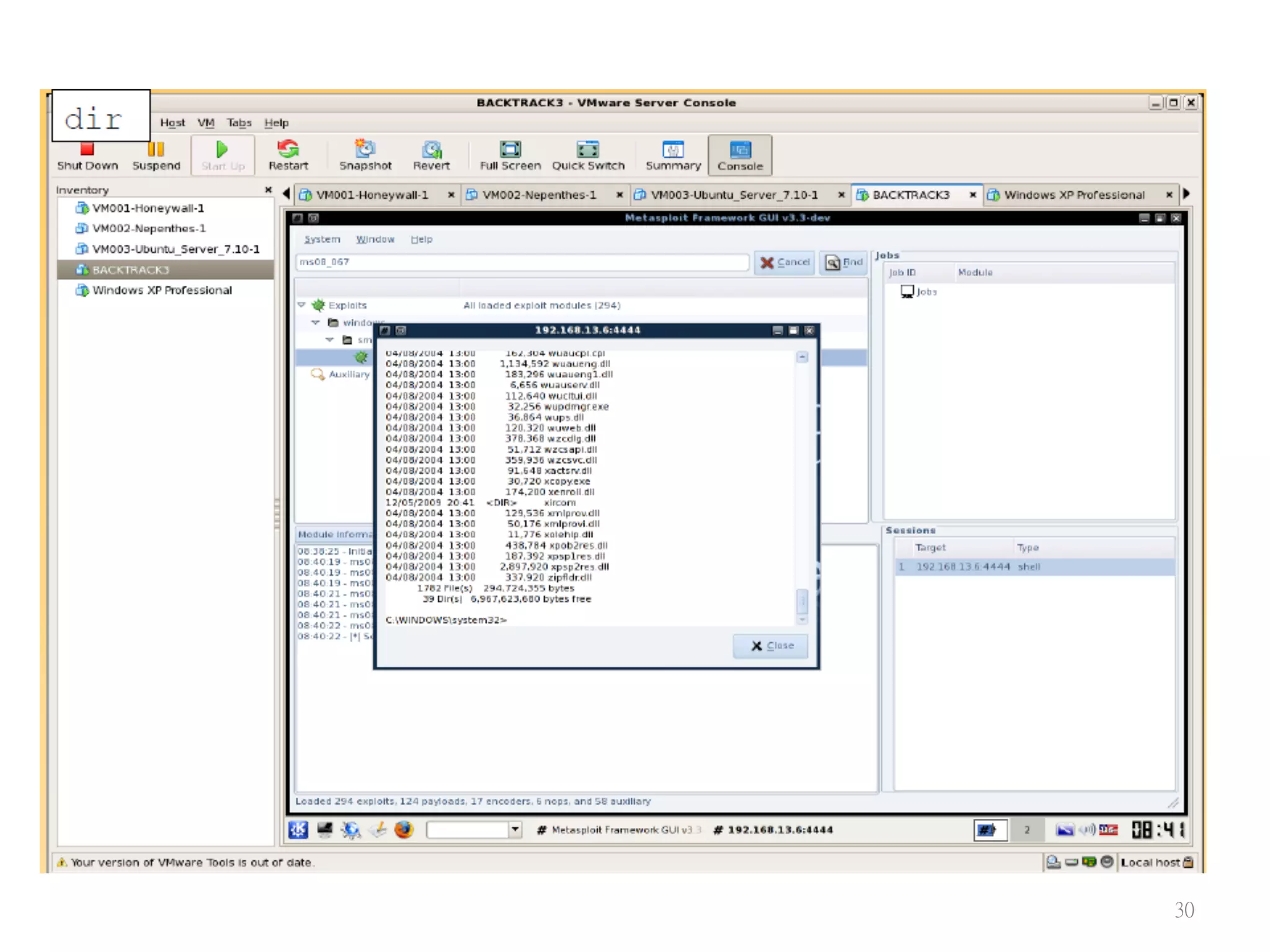
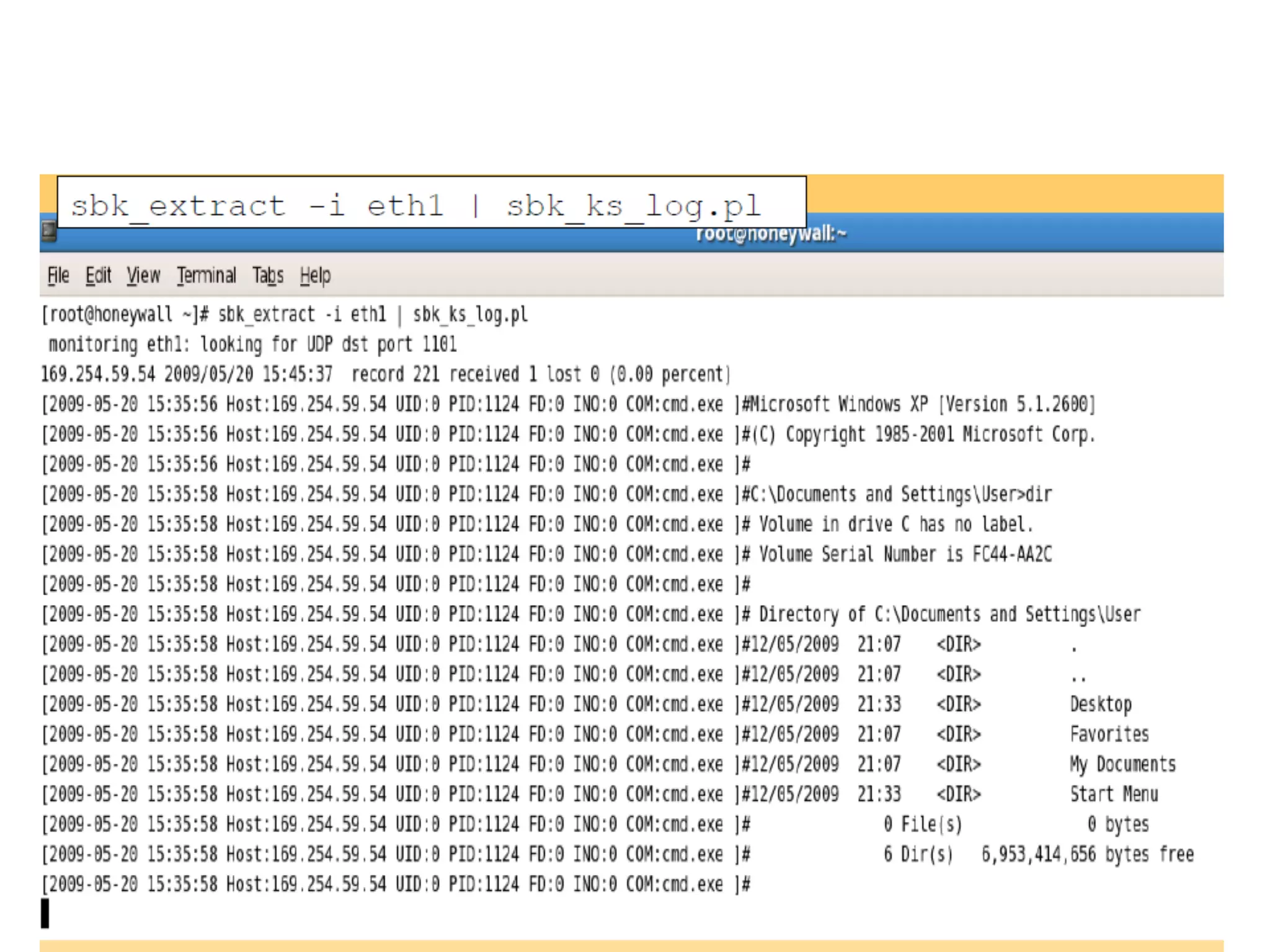
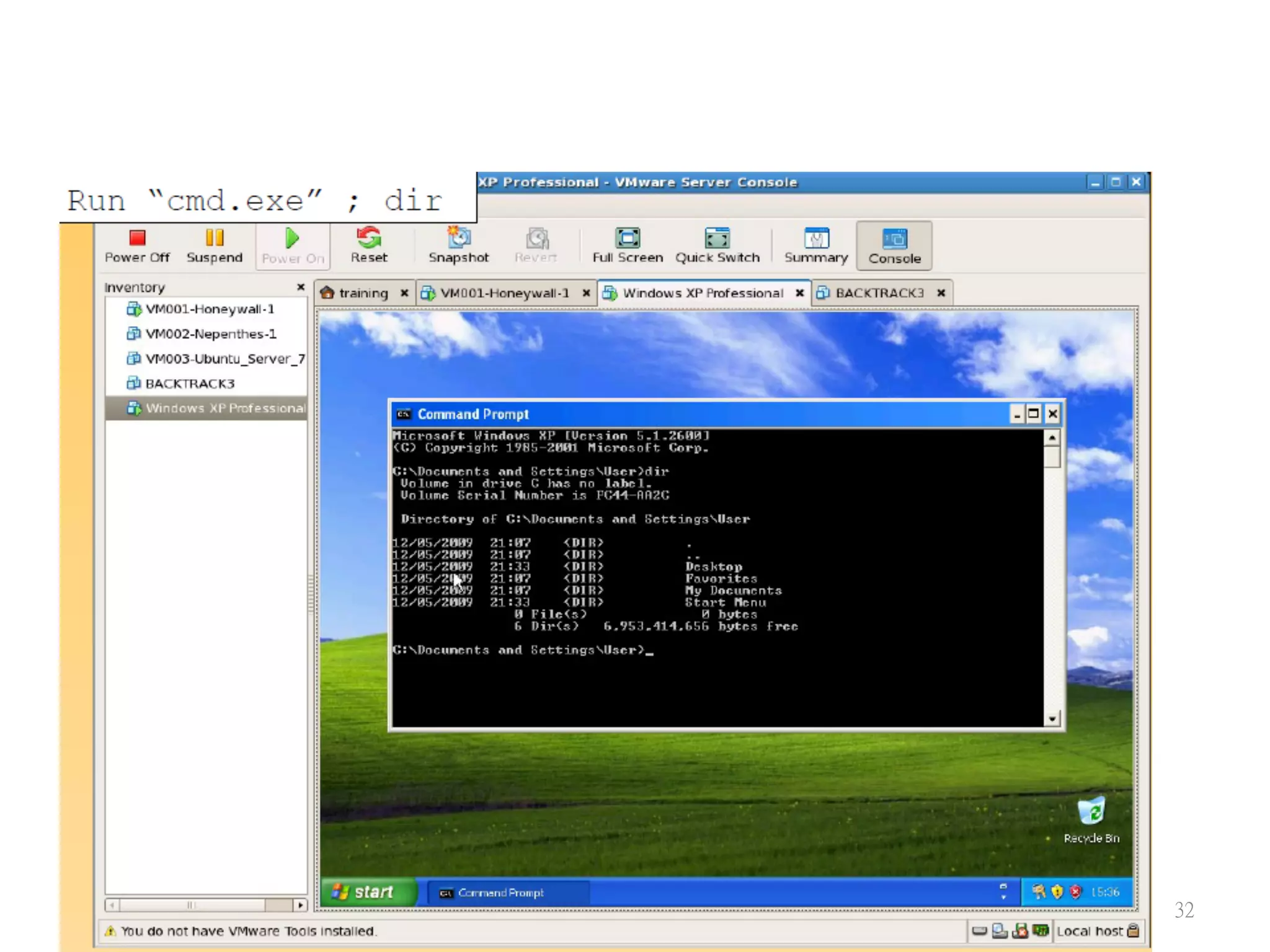
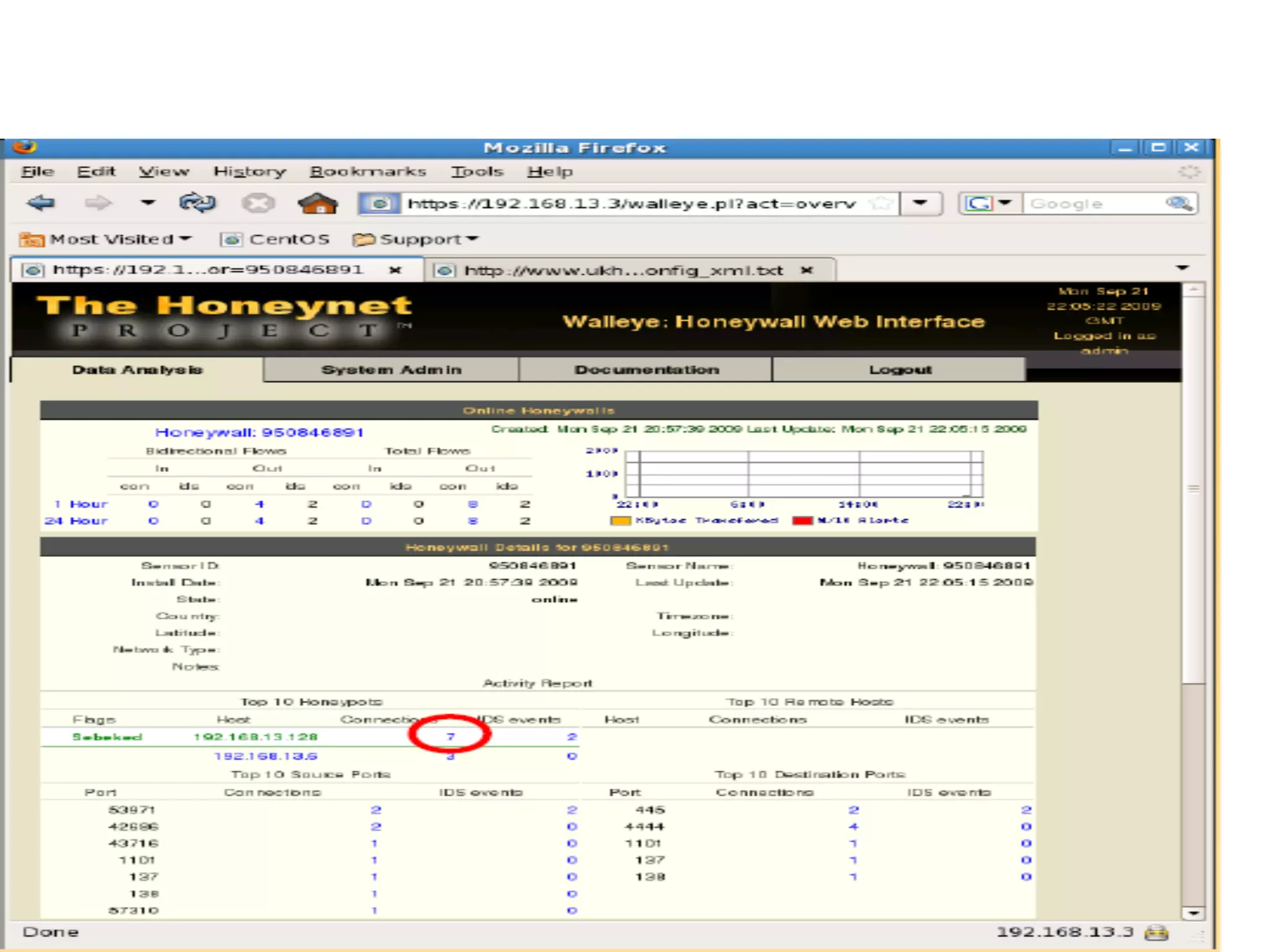
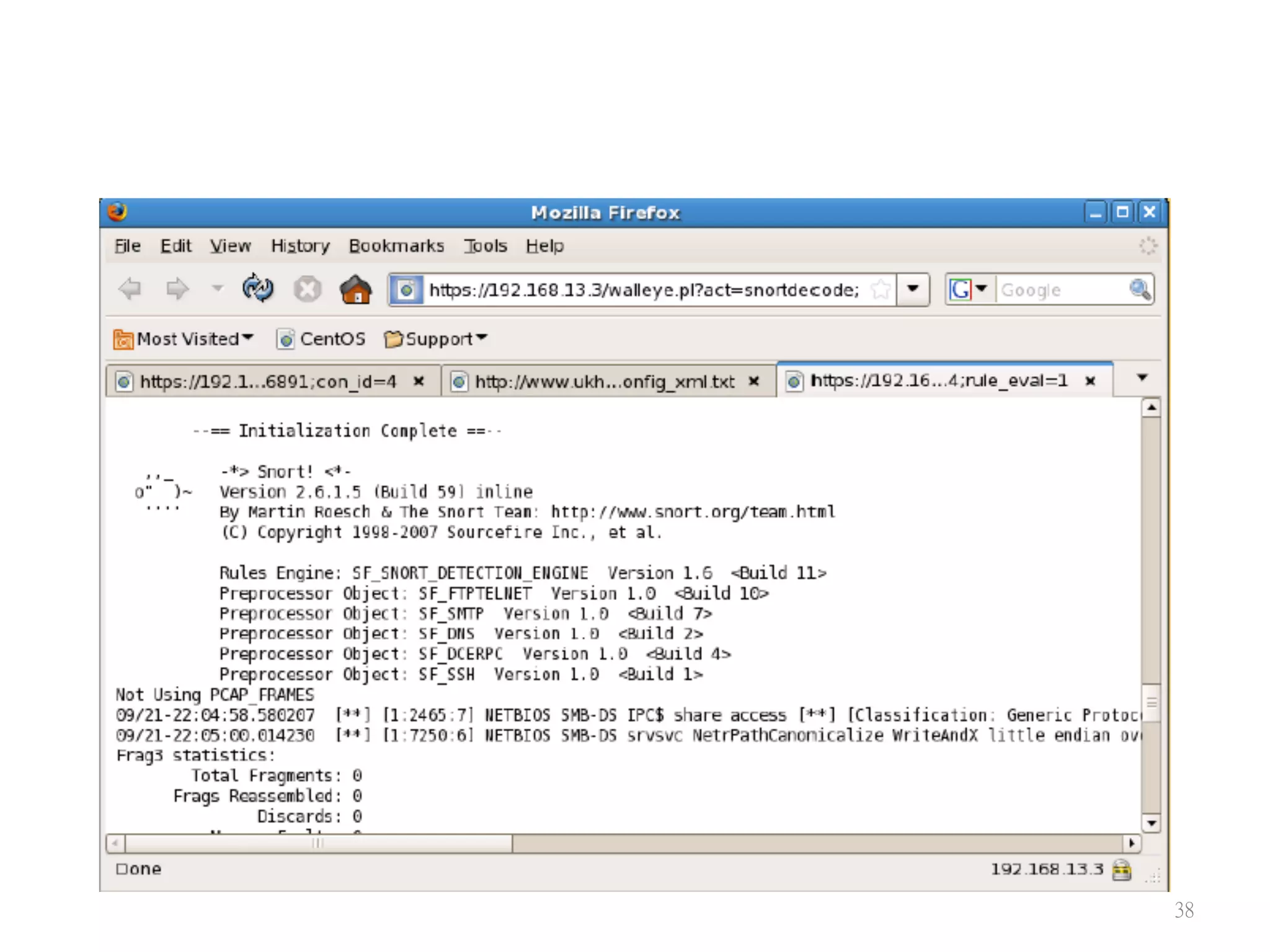
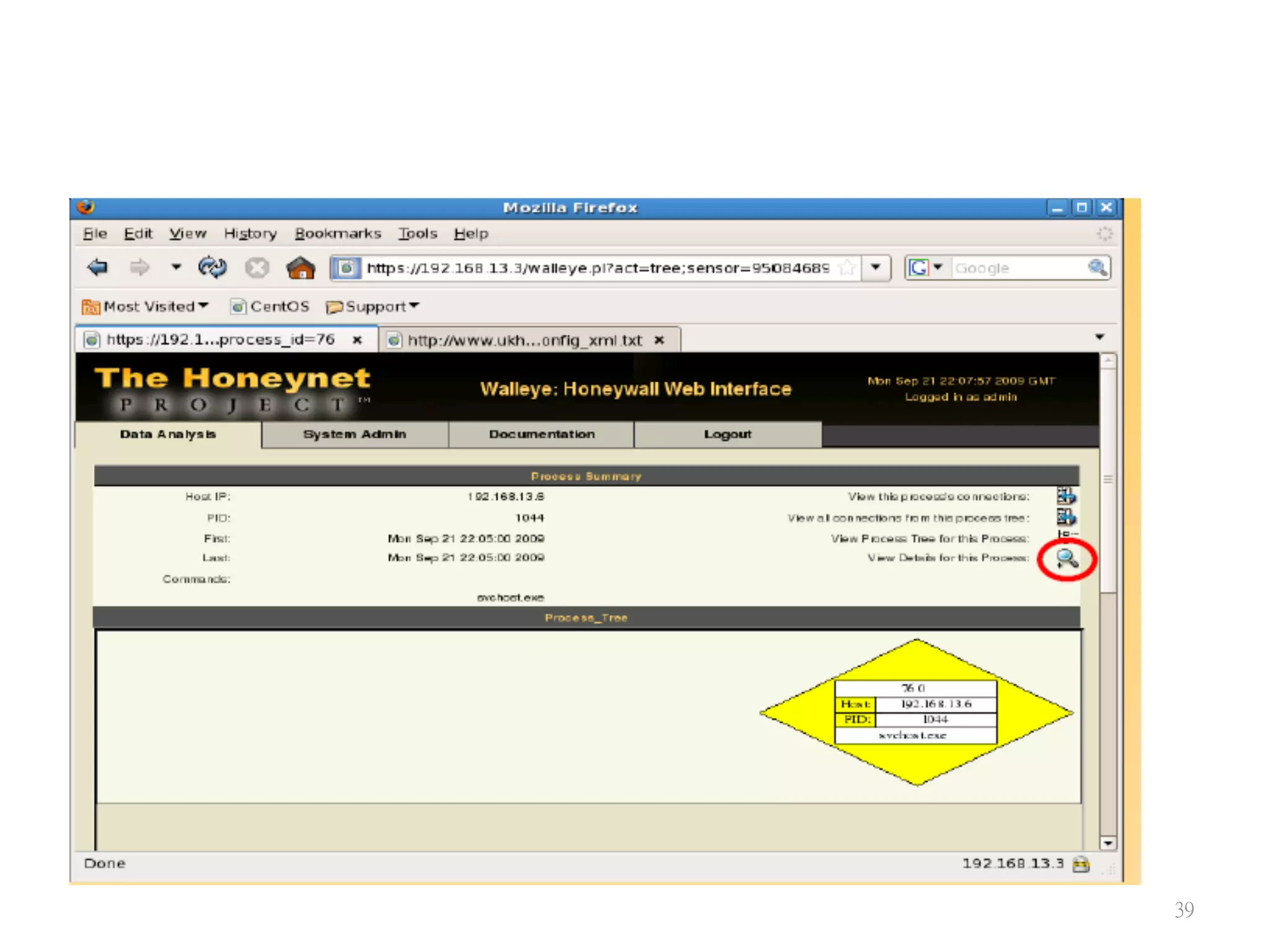
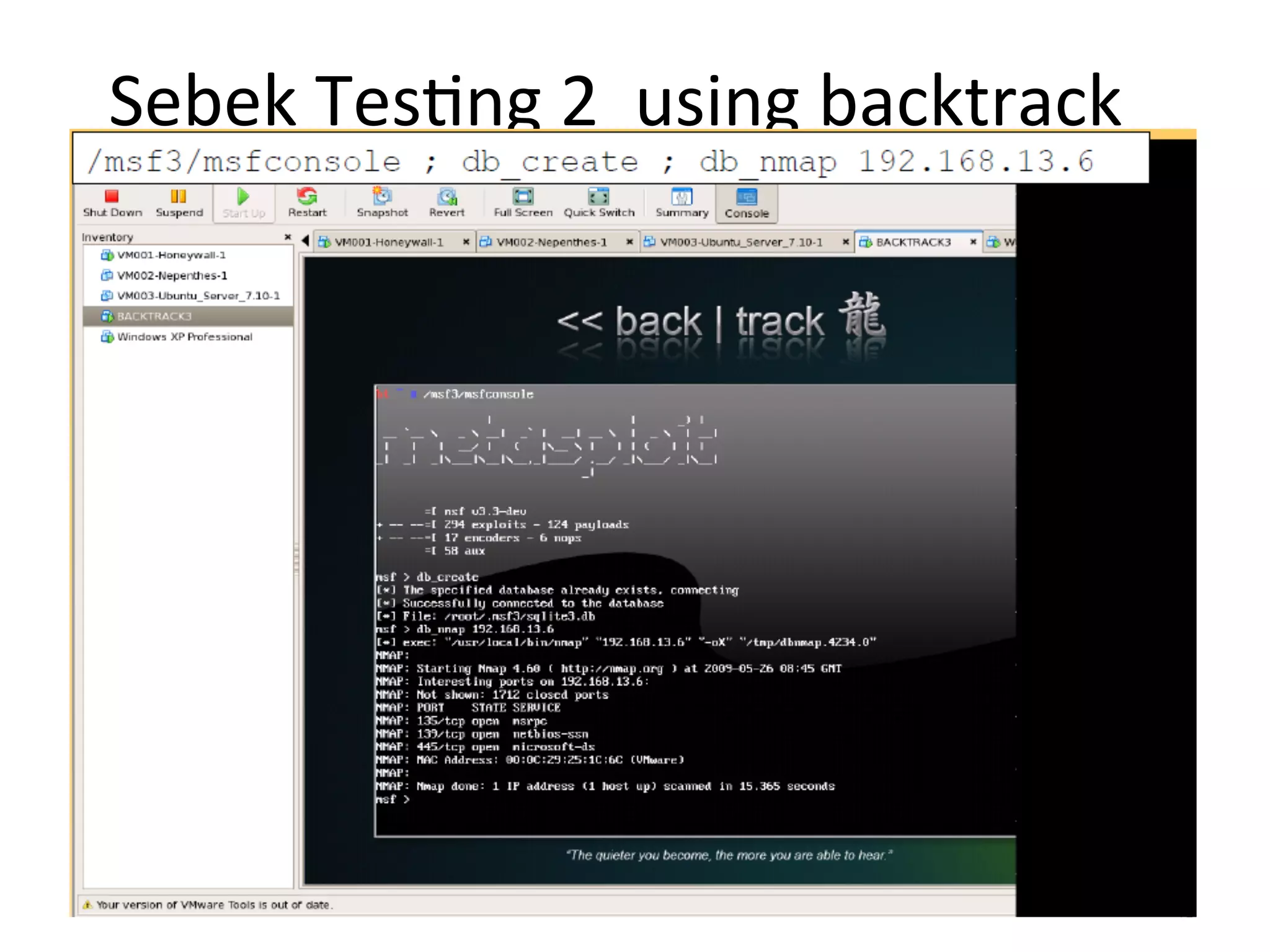
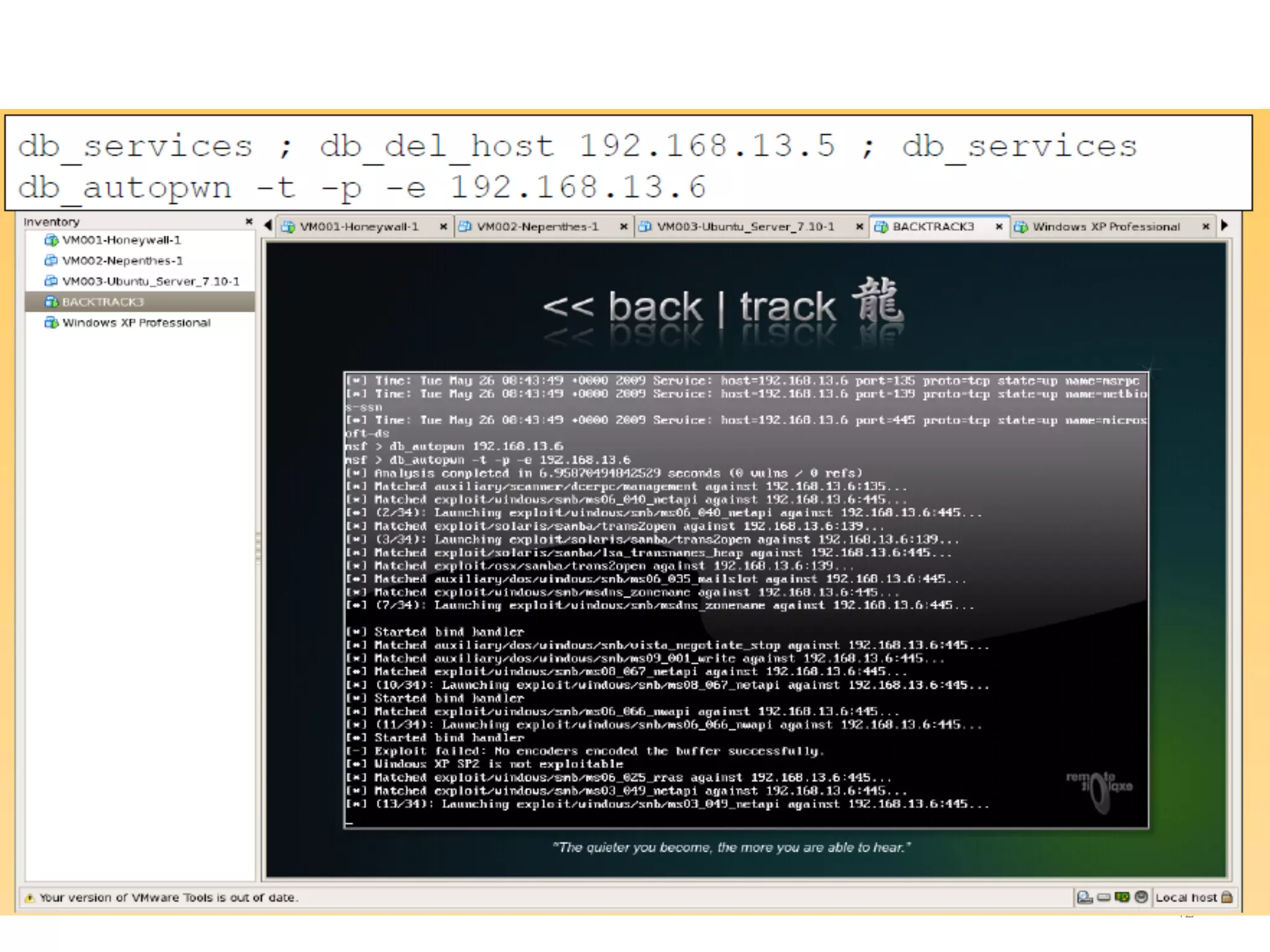
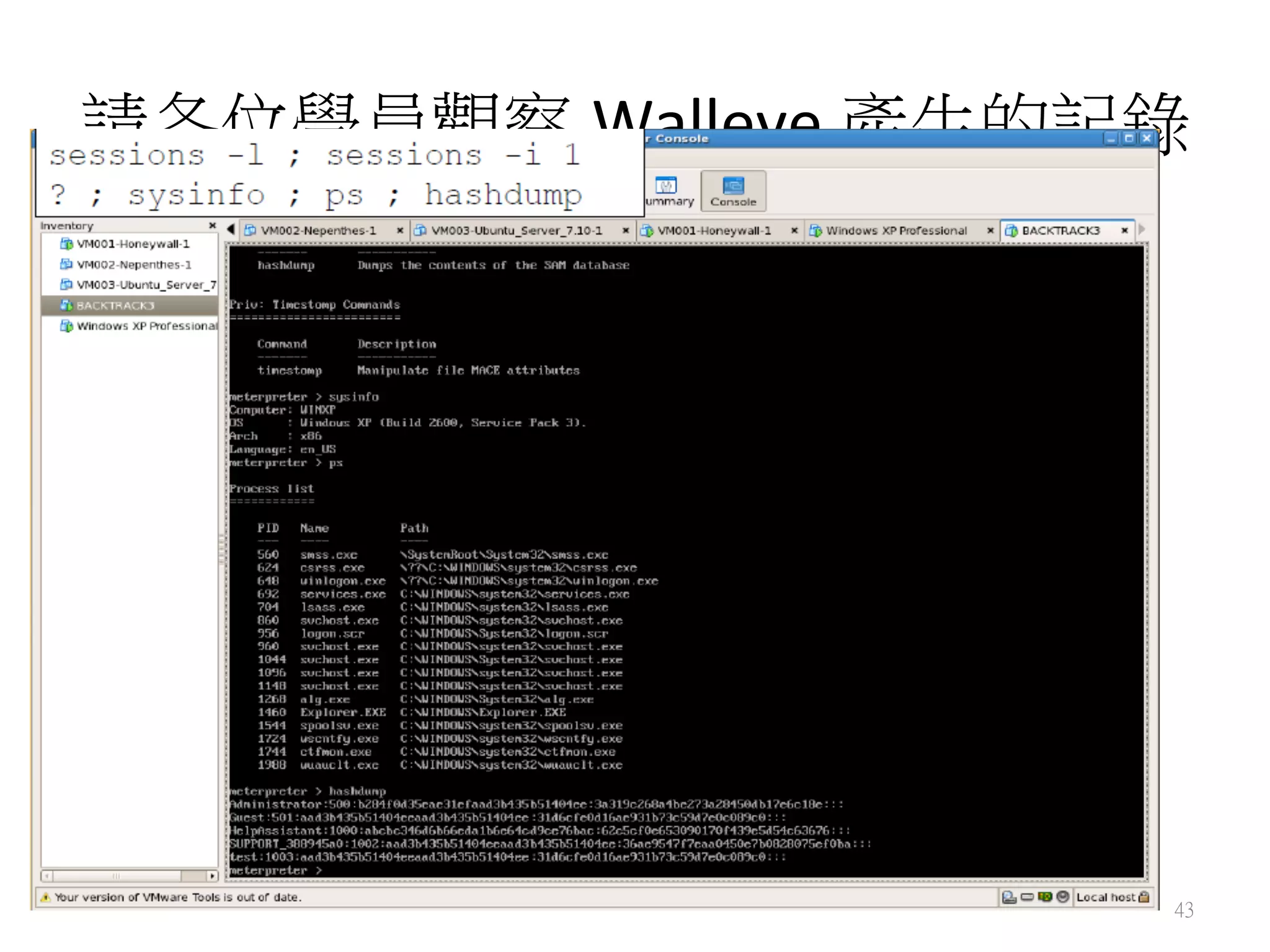
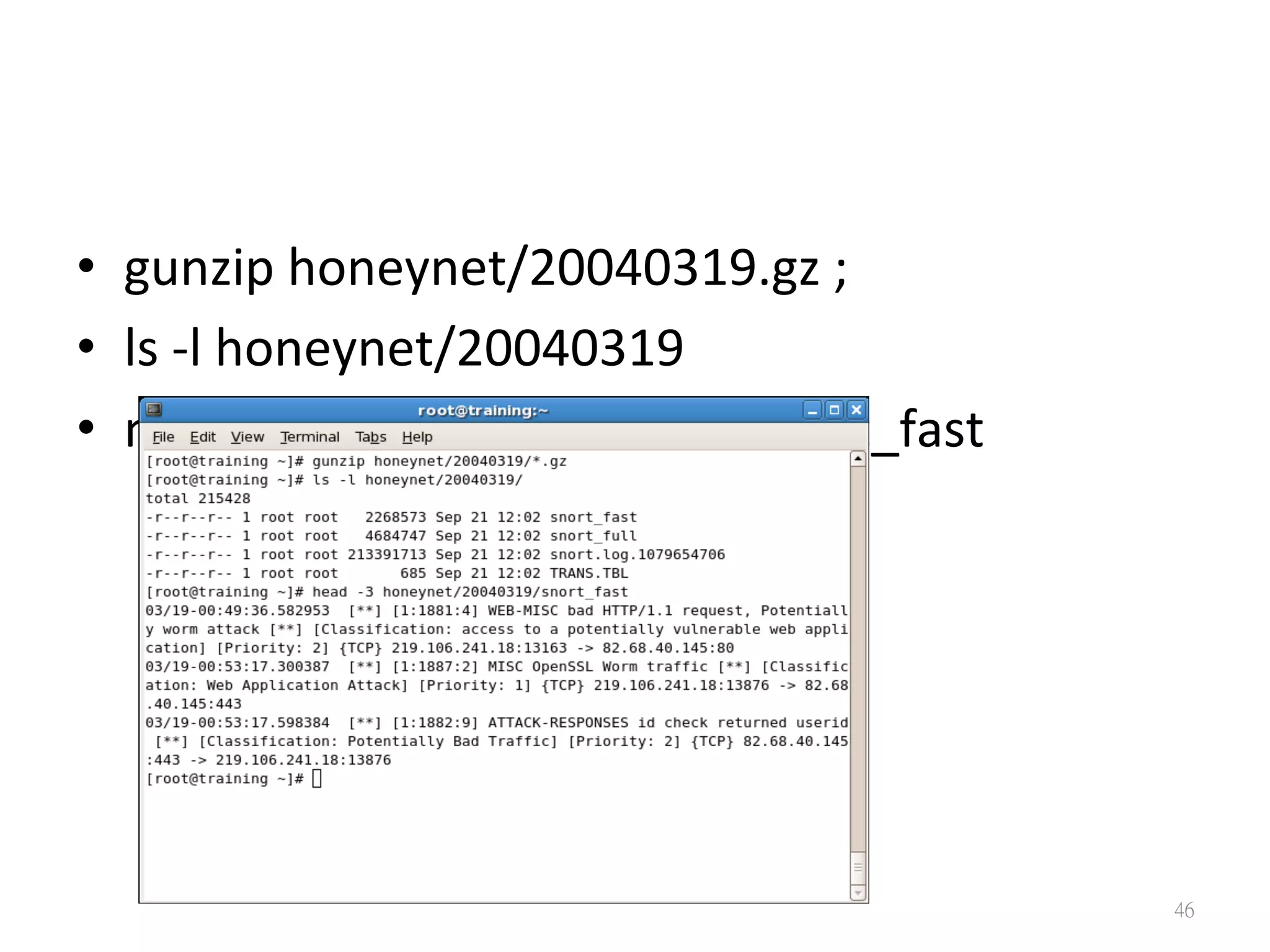
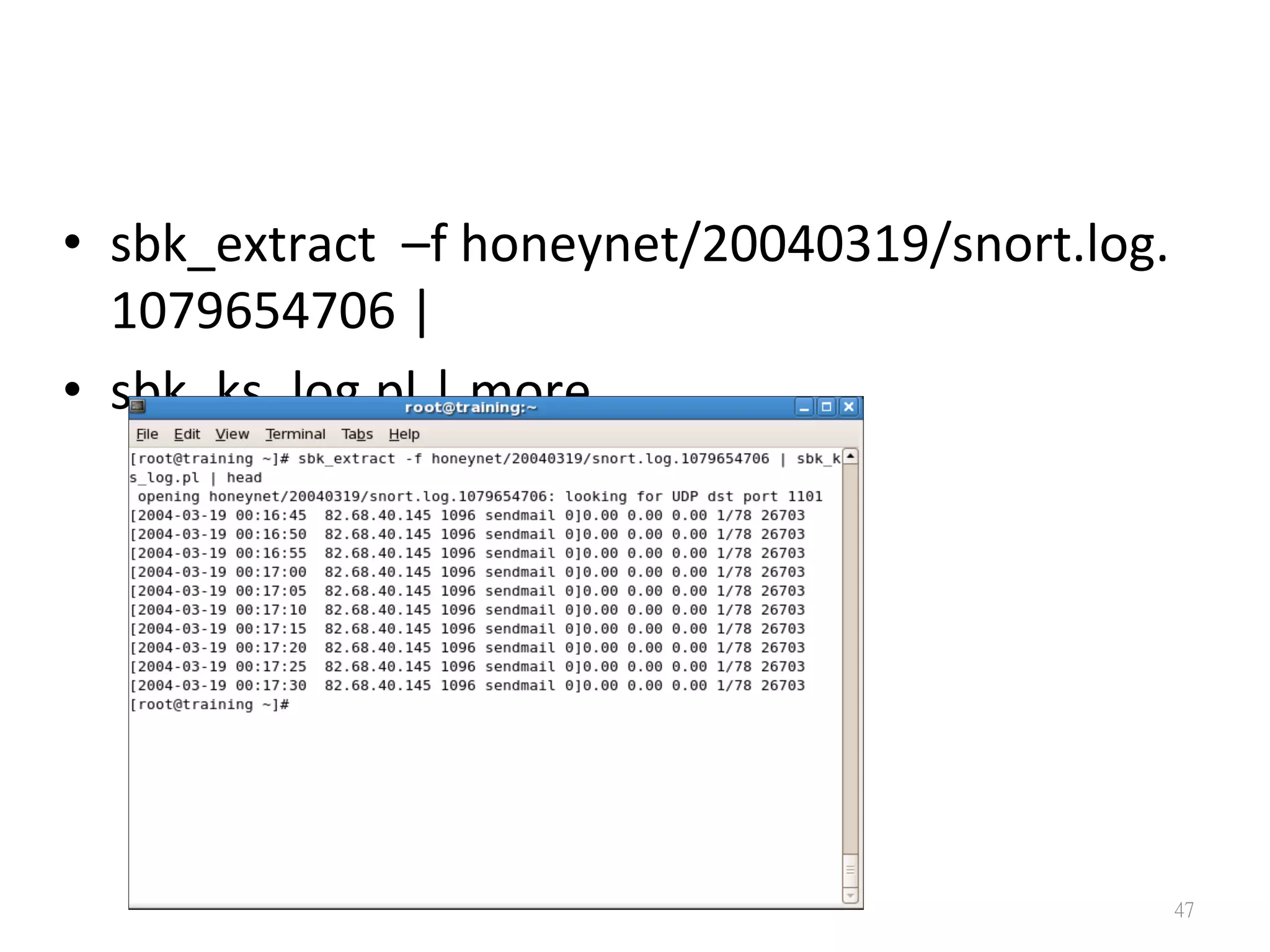
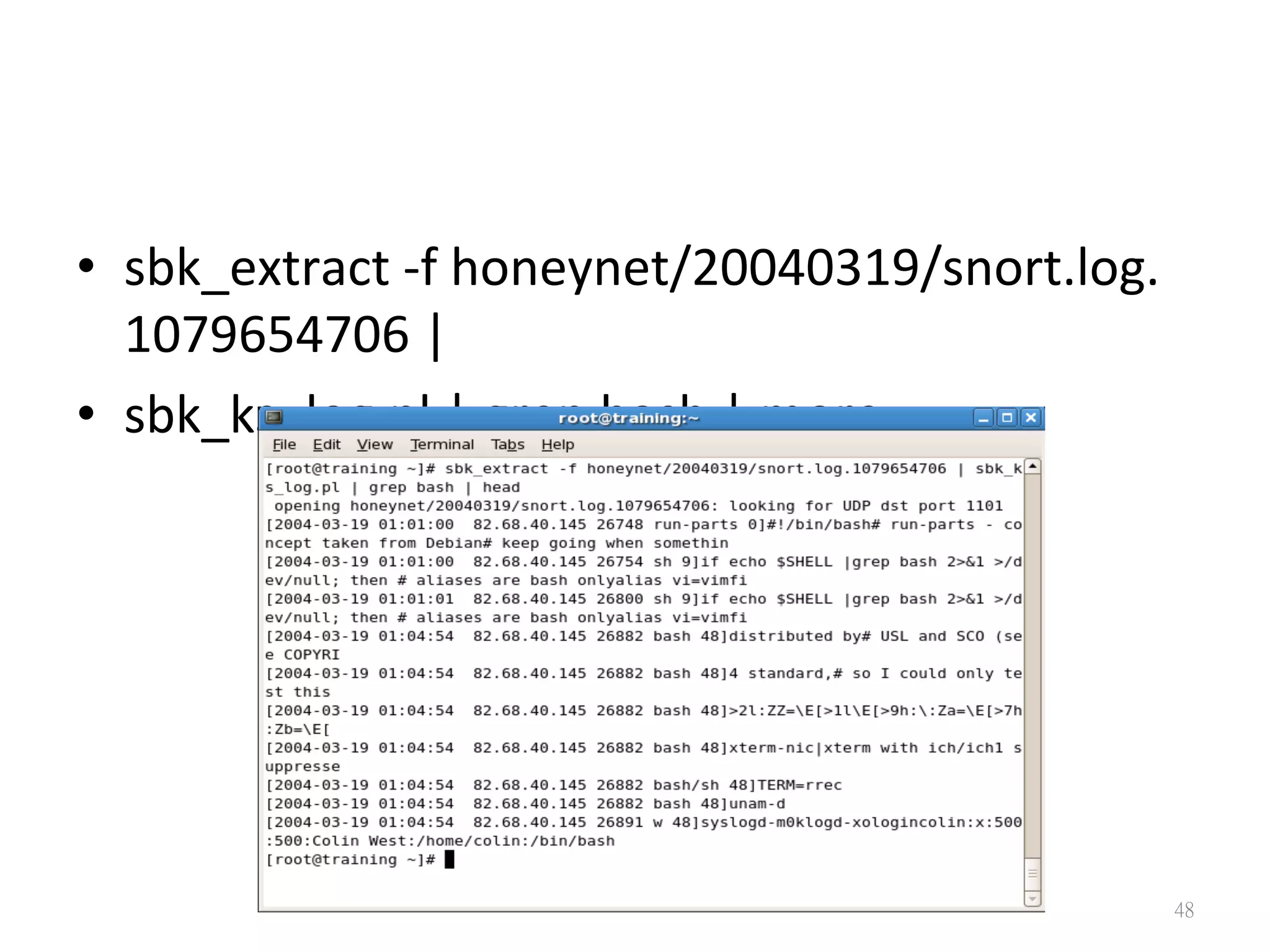
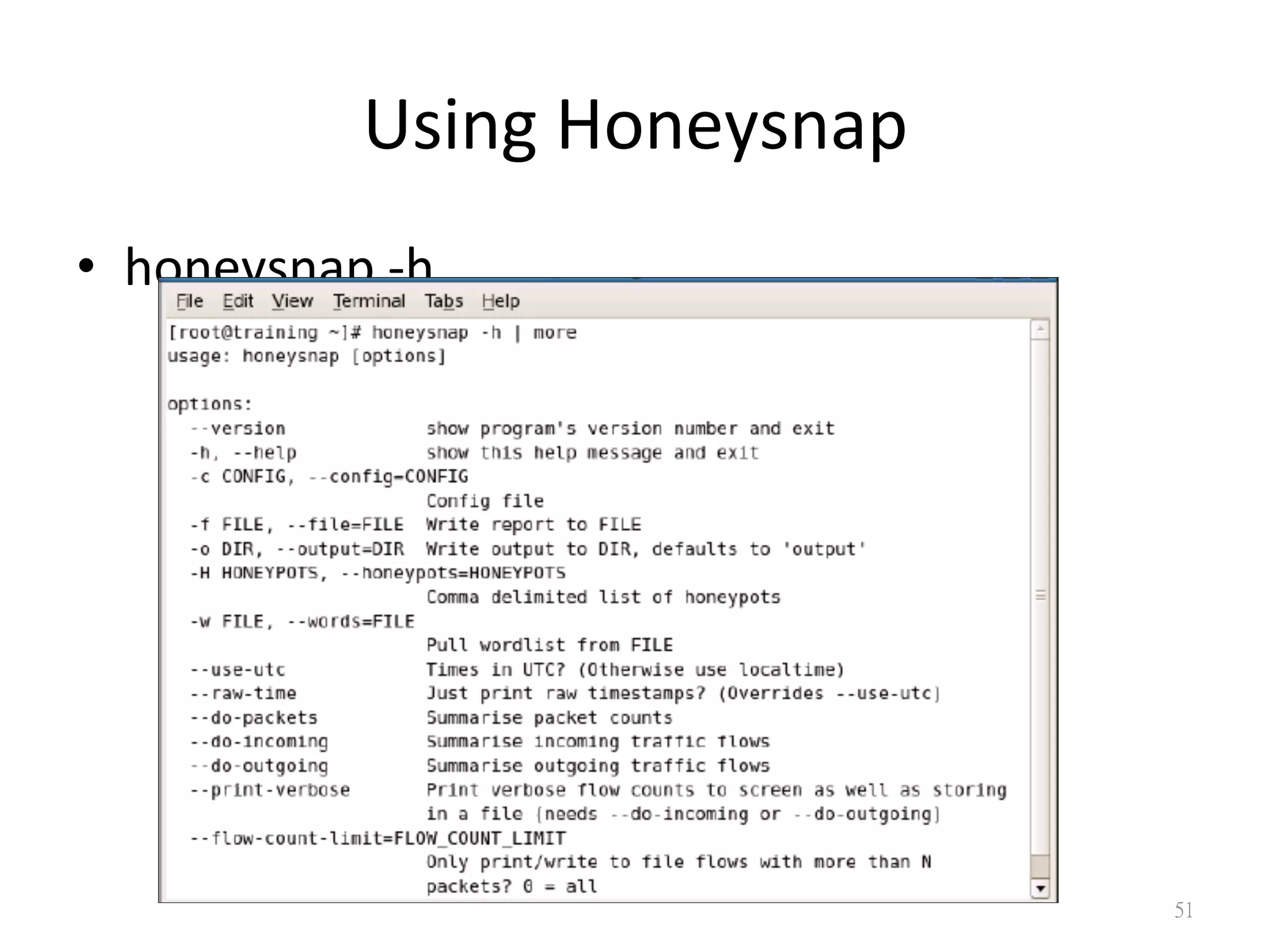
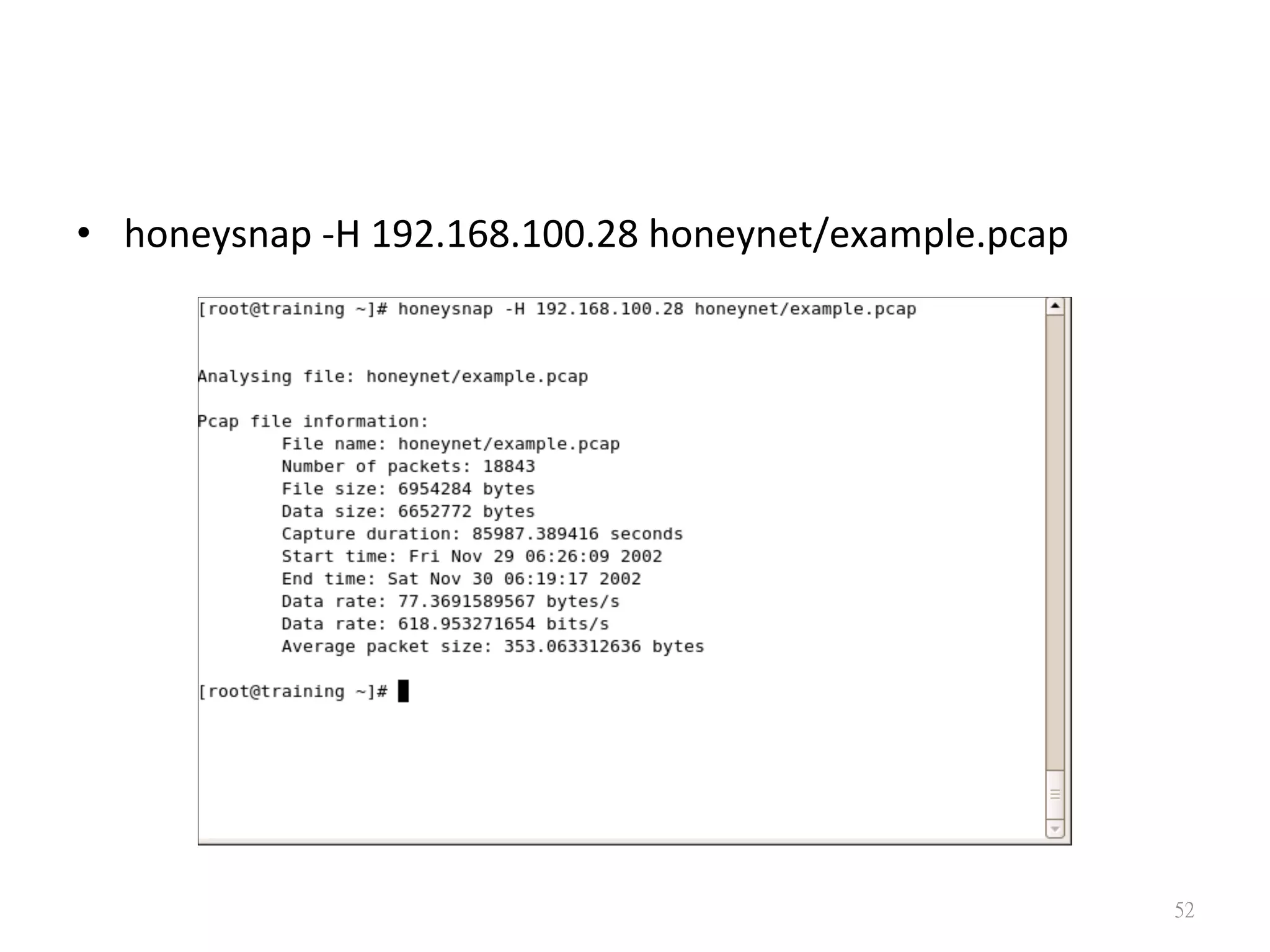
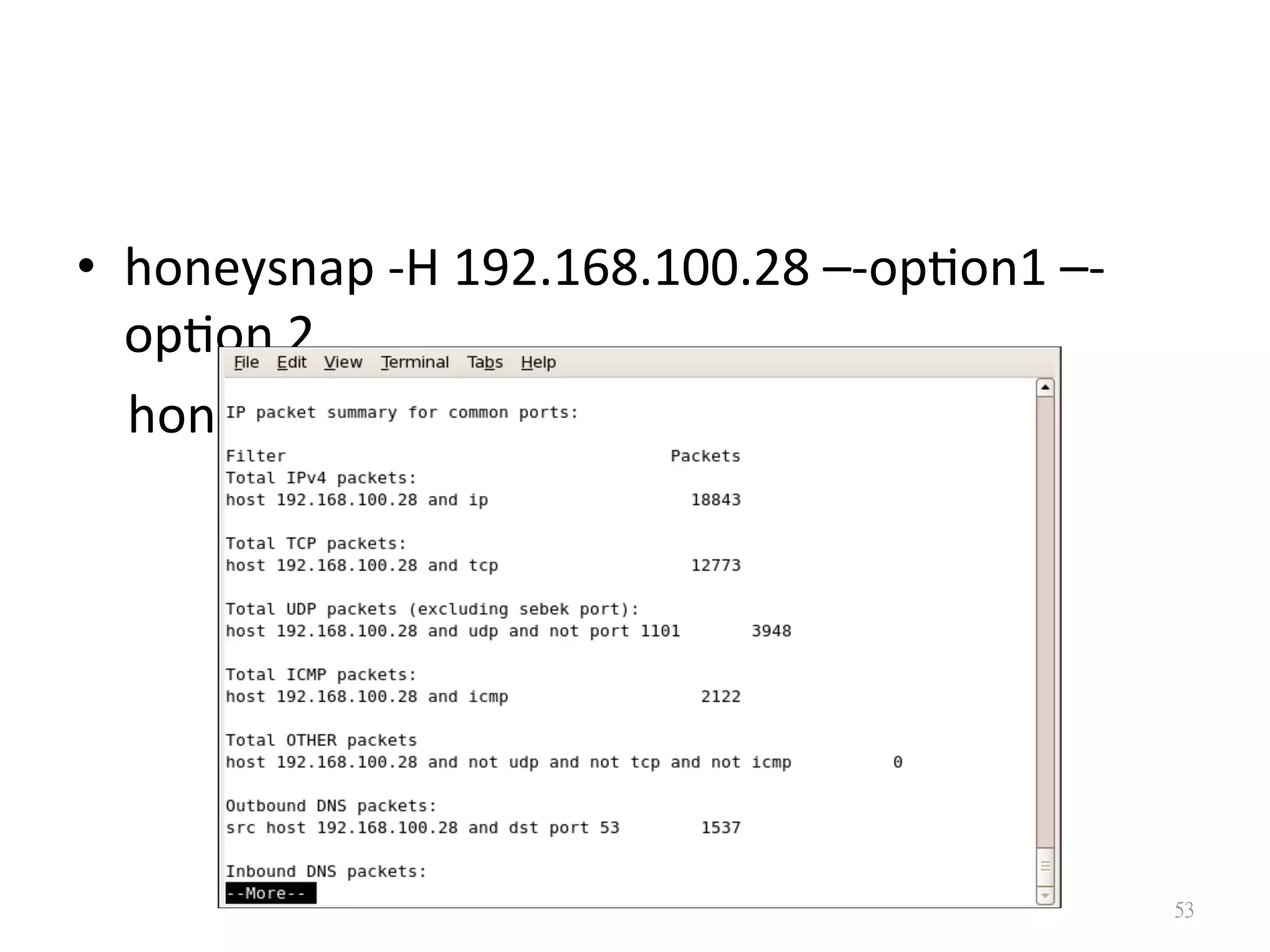
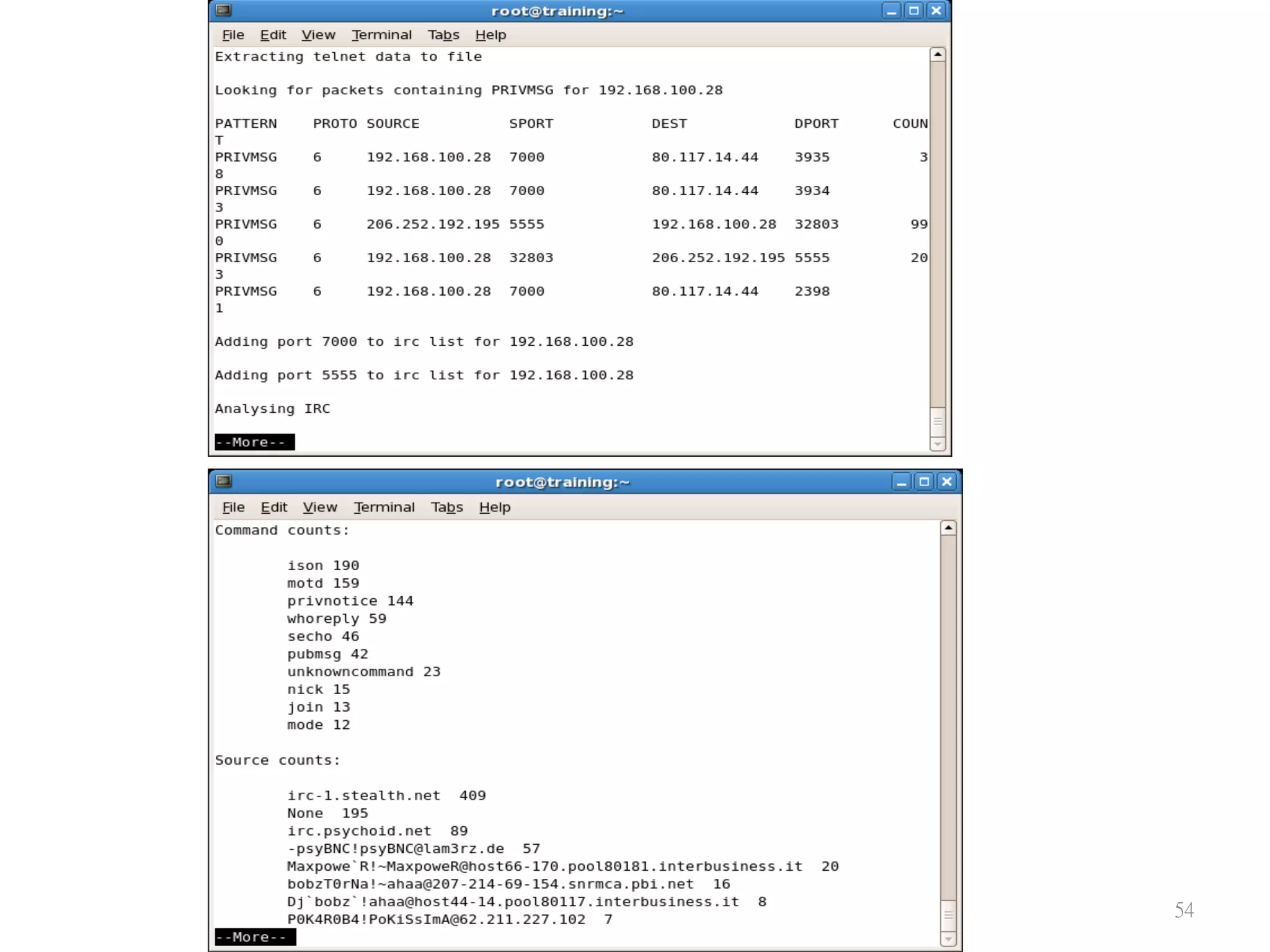
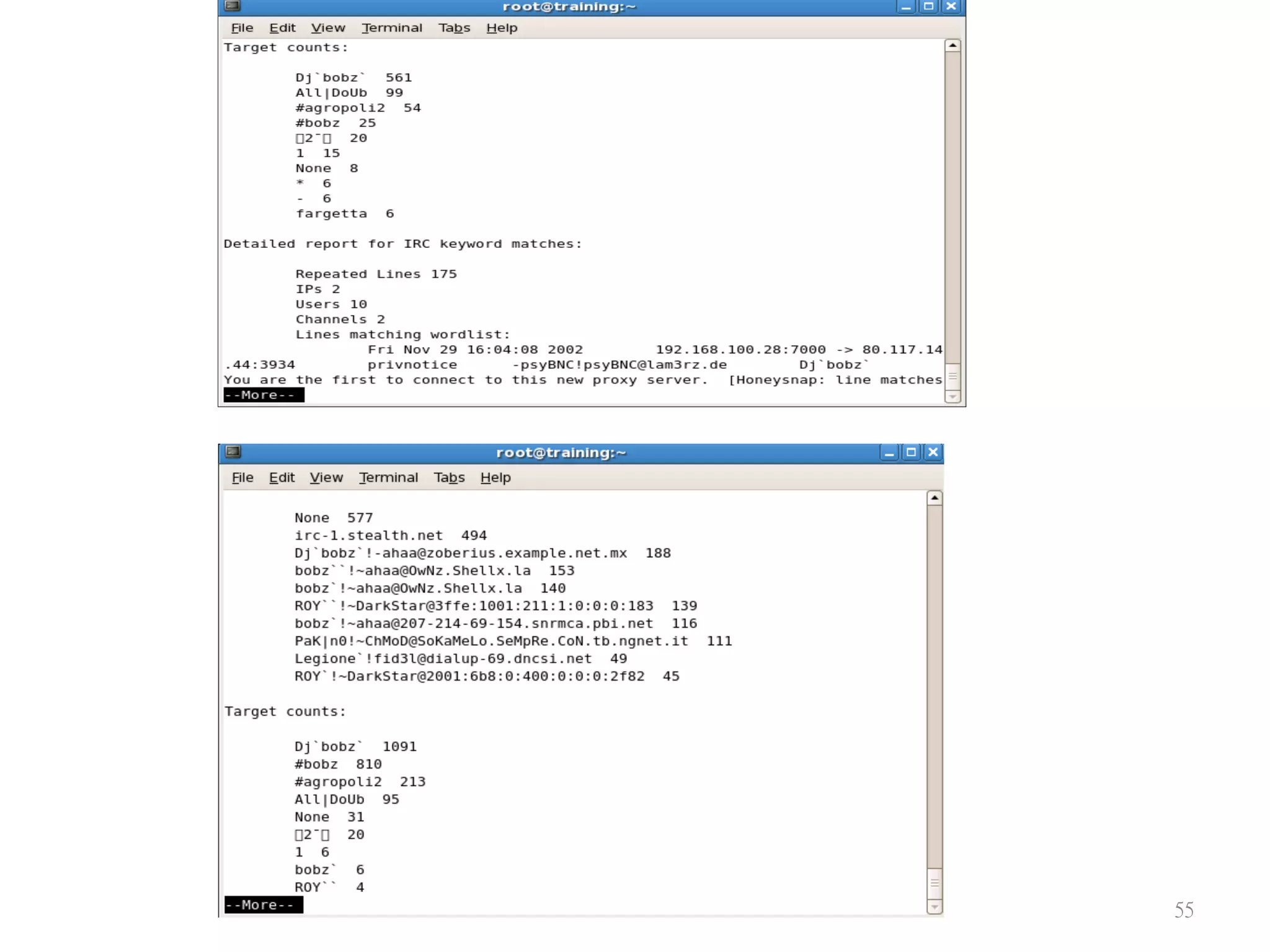
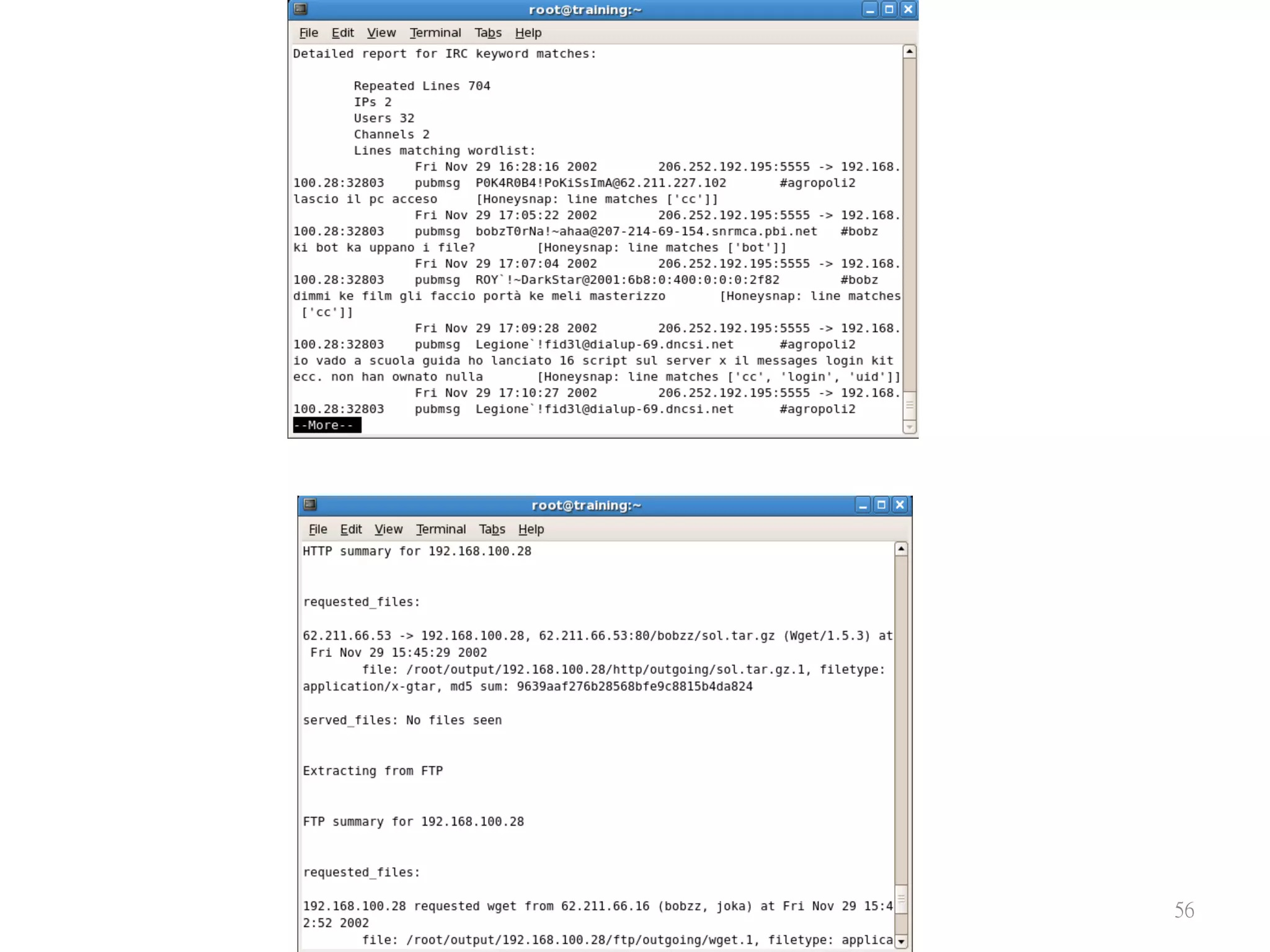
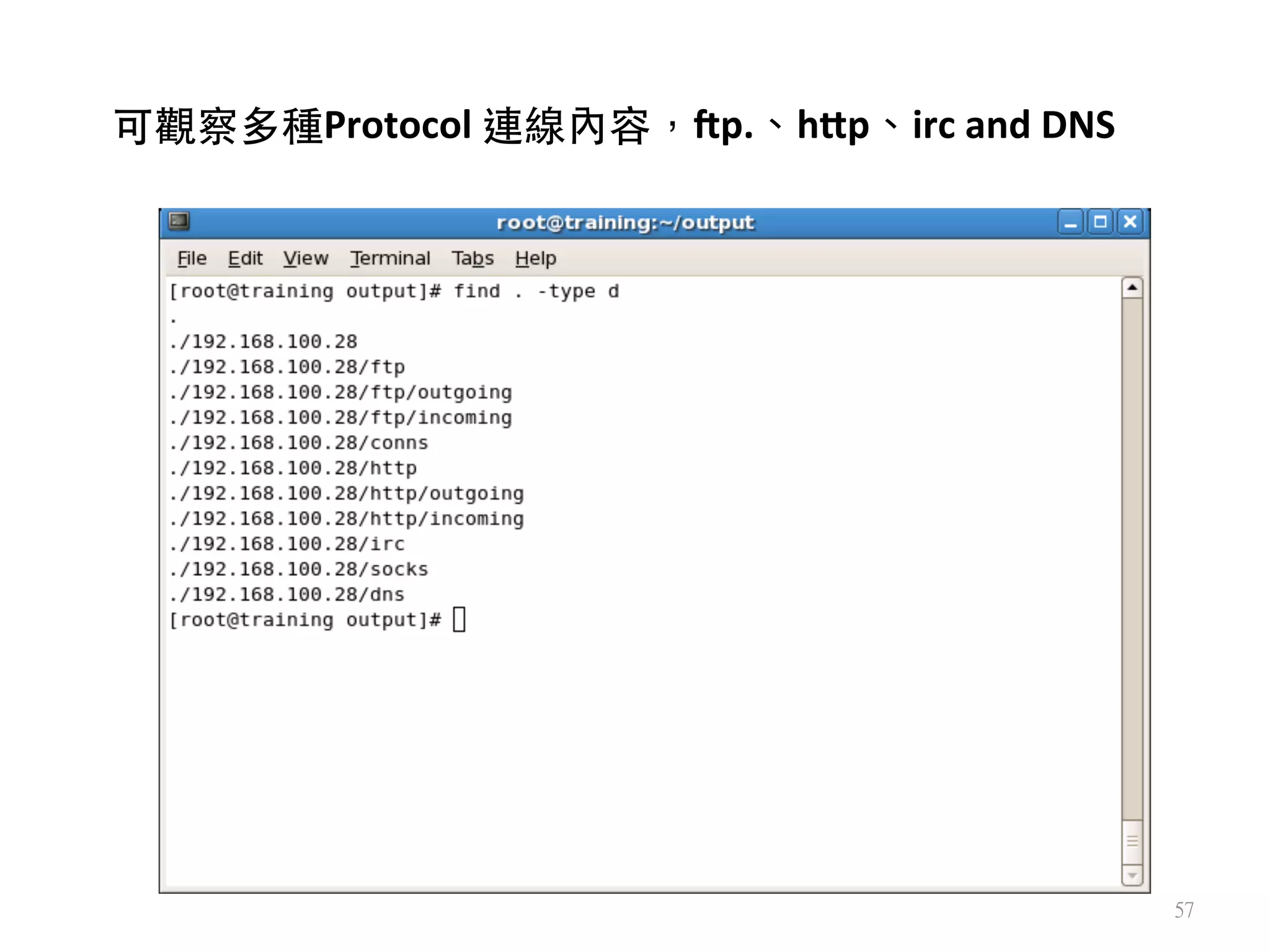
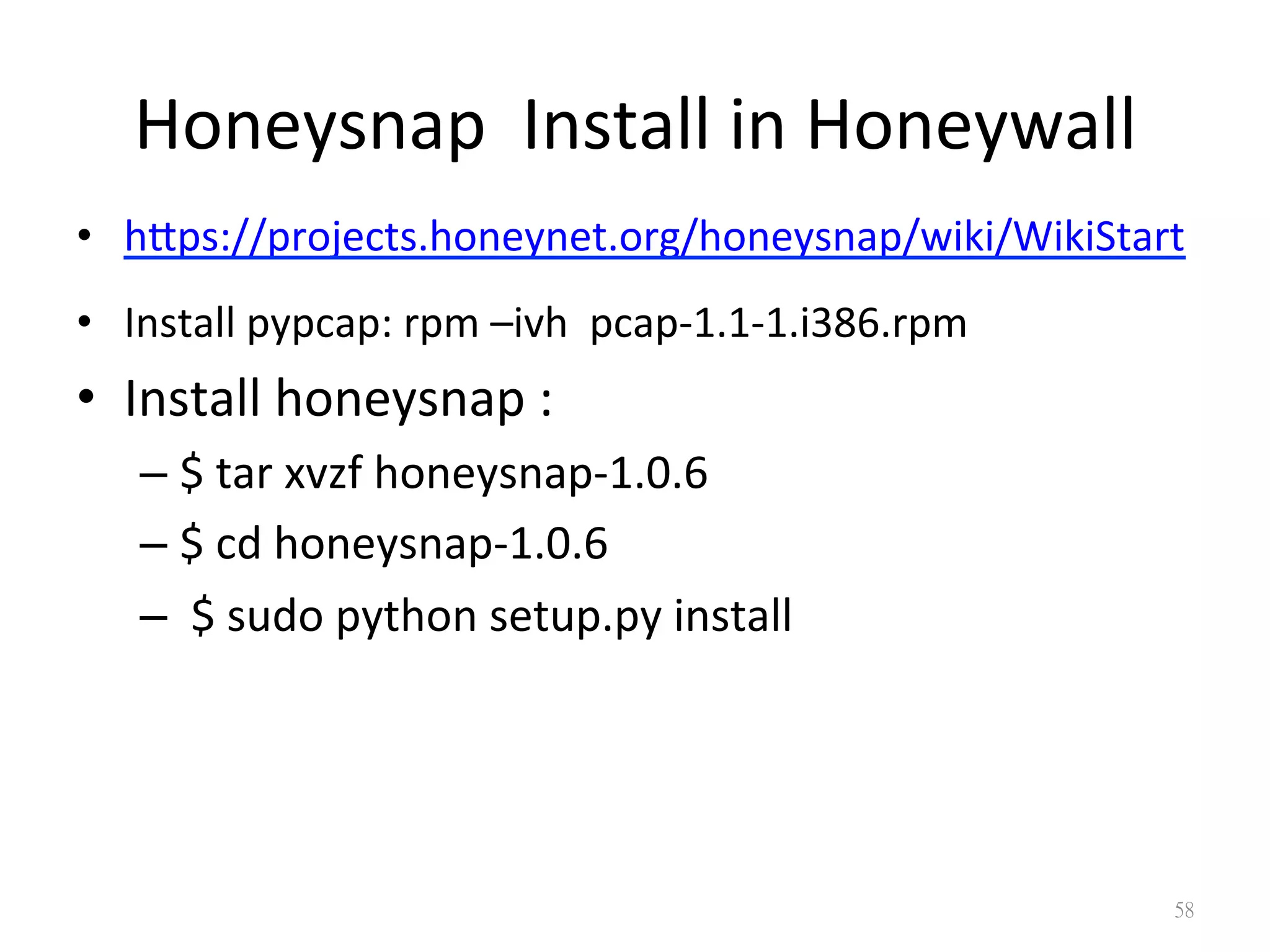
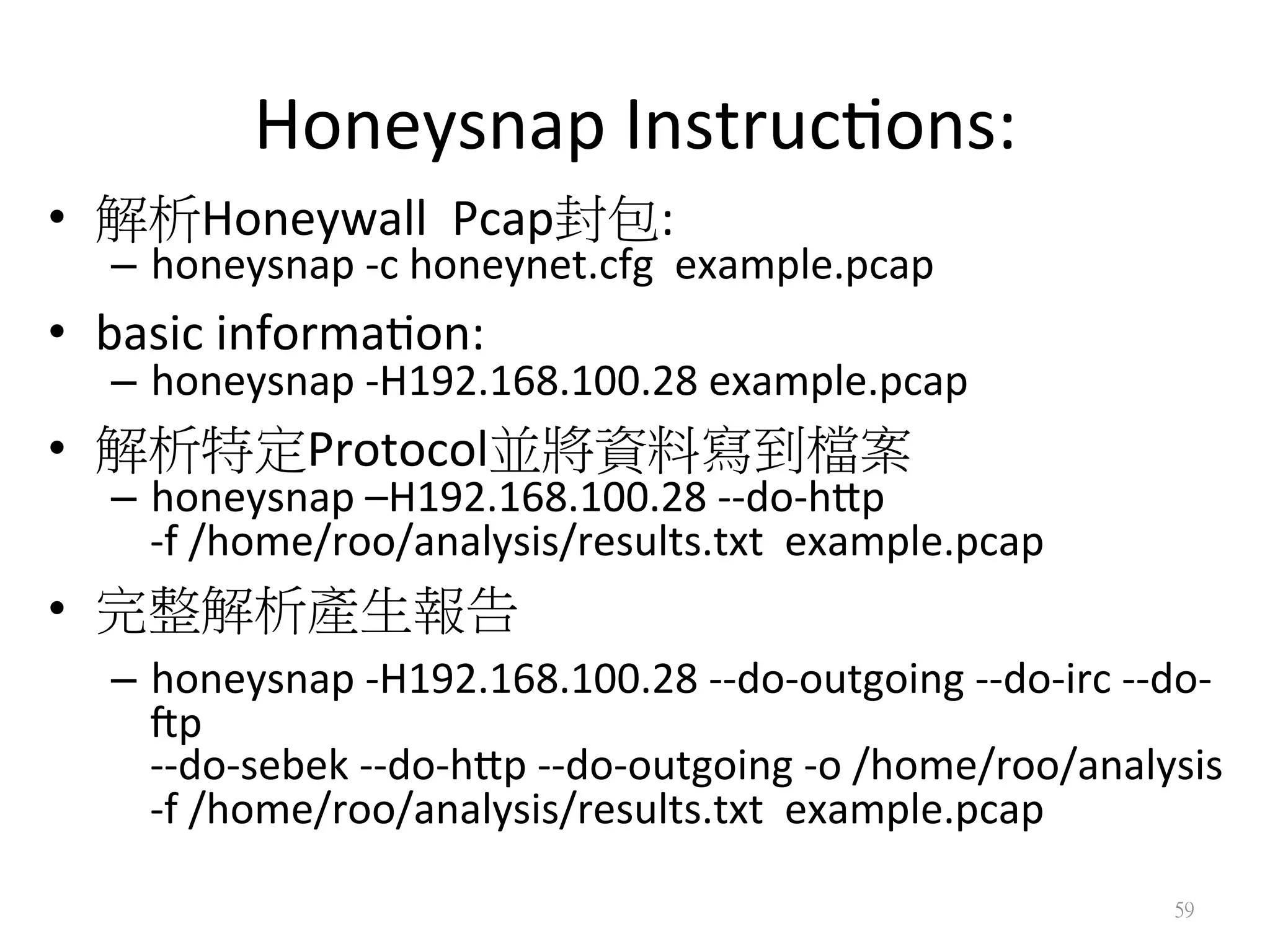
This document provides instructions for installing and using the Sebek and Honeysnap tools to analyze Windows XP guest operating systems and offline PCAP files from honeypots. It explains how to extract keysroke logs and network traffic using Sebek tools, and generate first-cut analysis reports of events using Honeysnap by parsing PCAP files offline. Specific commands are provided to view different protocol activity captured in PCAP files with these tools.